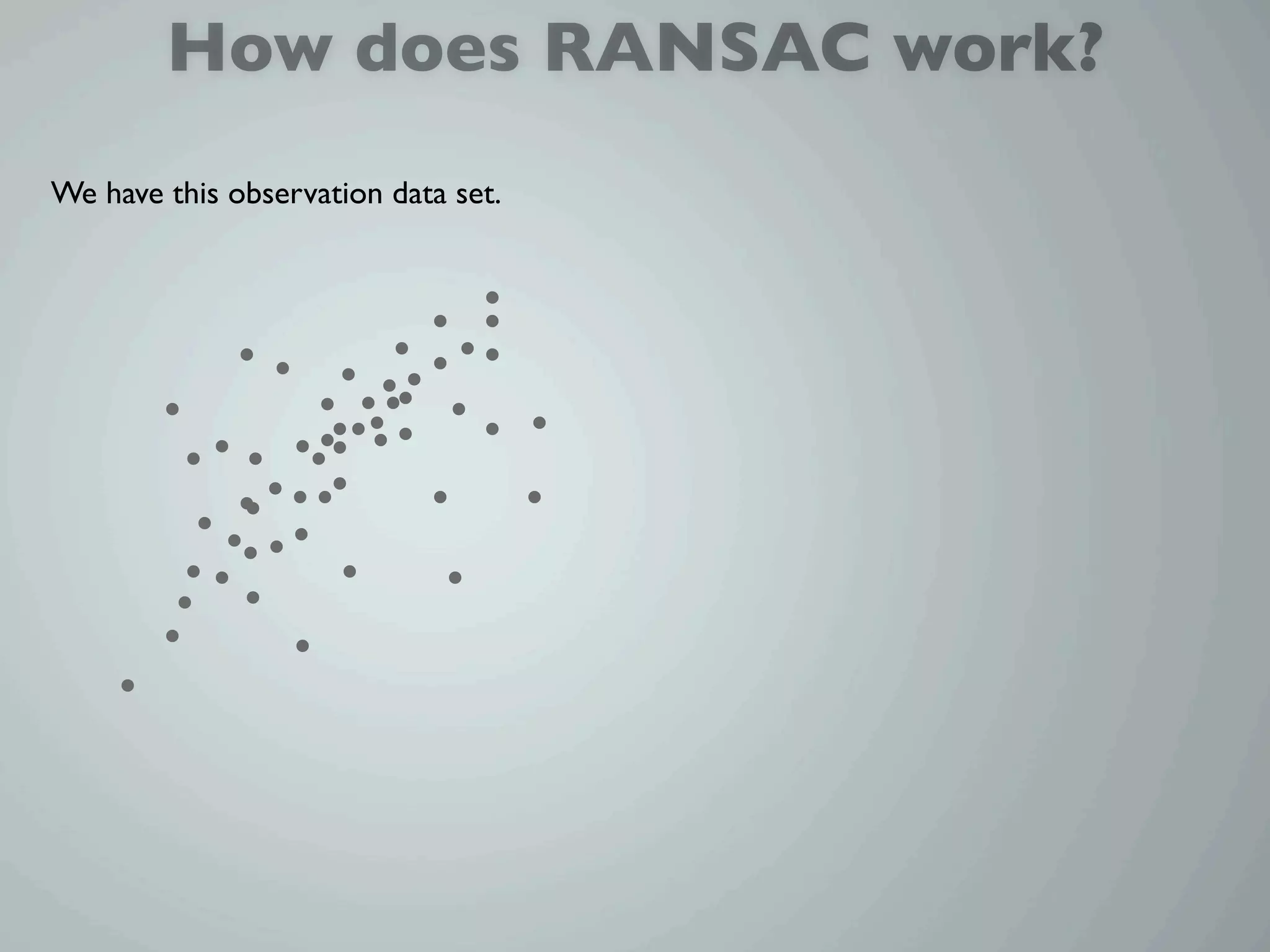
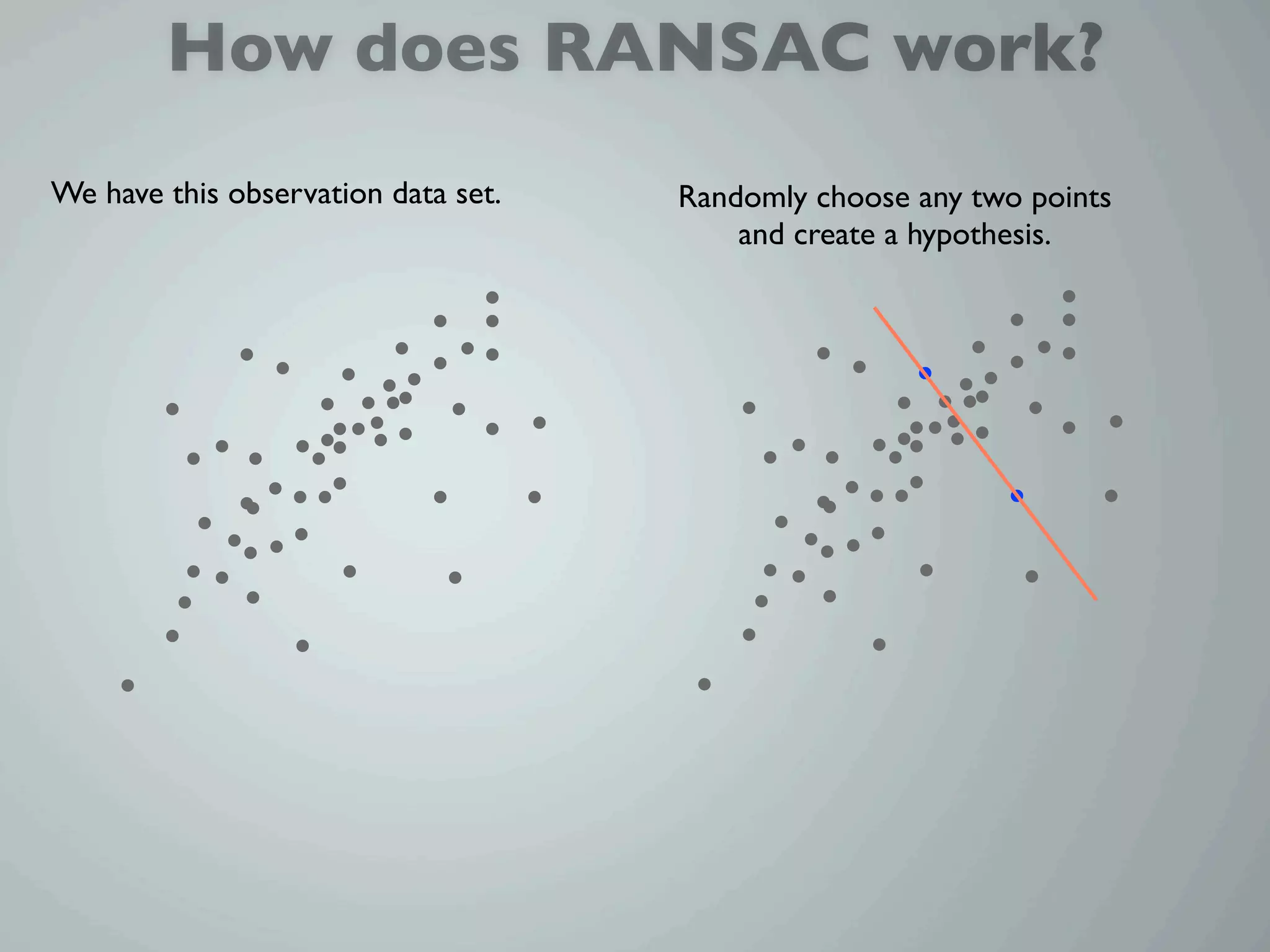
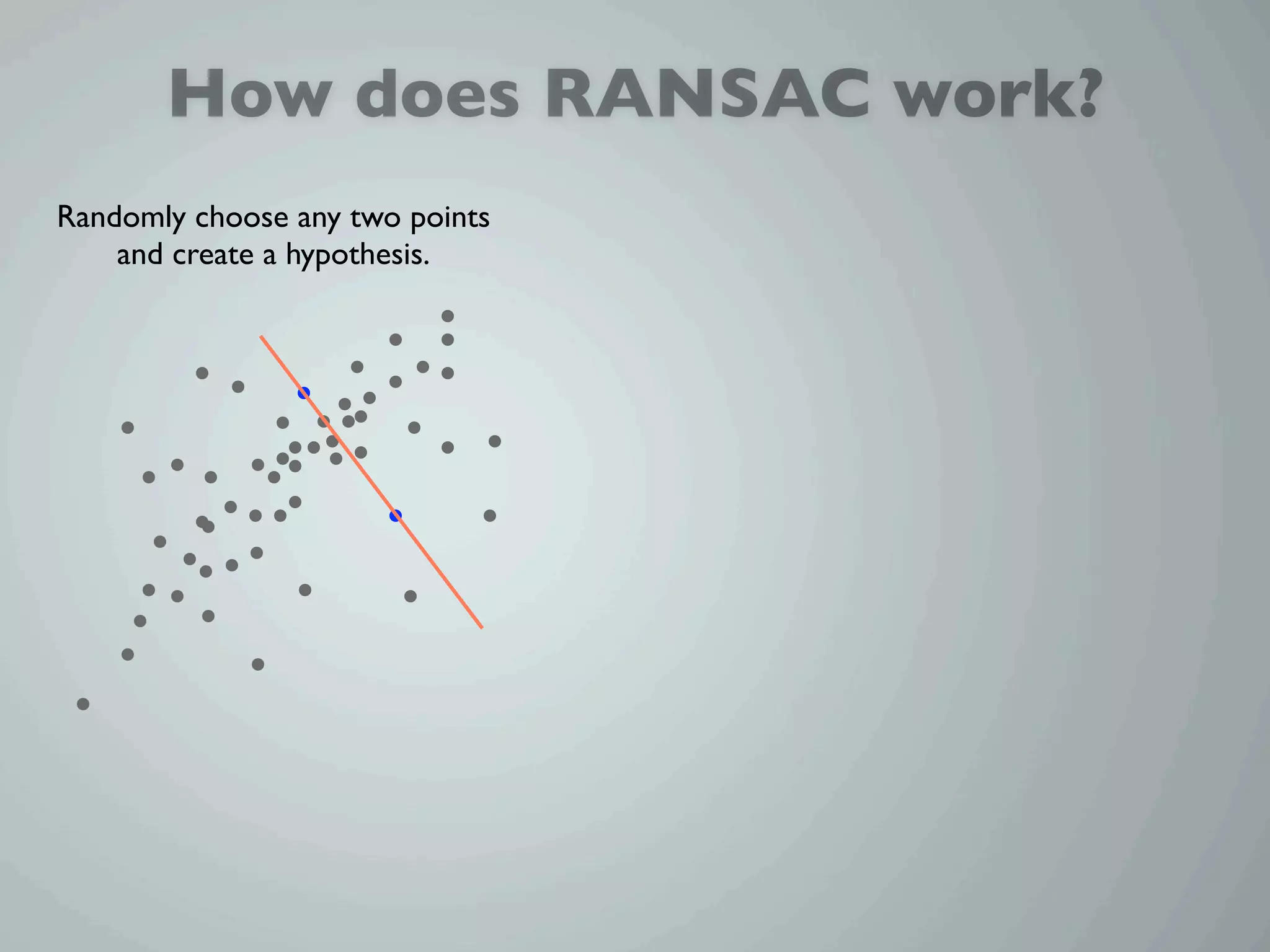
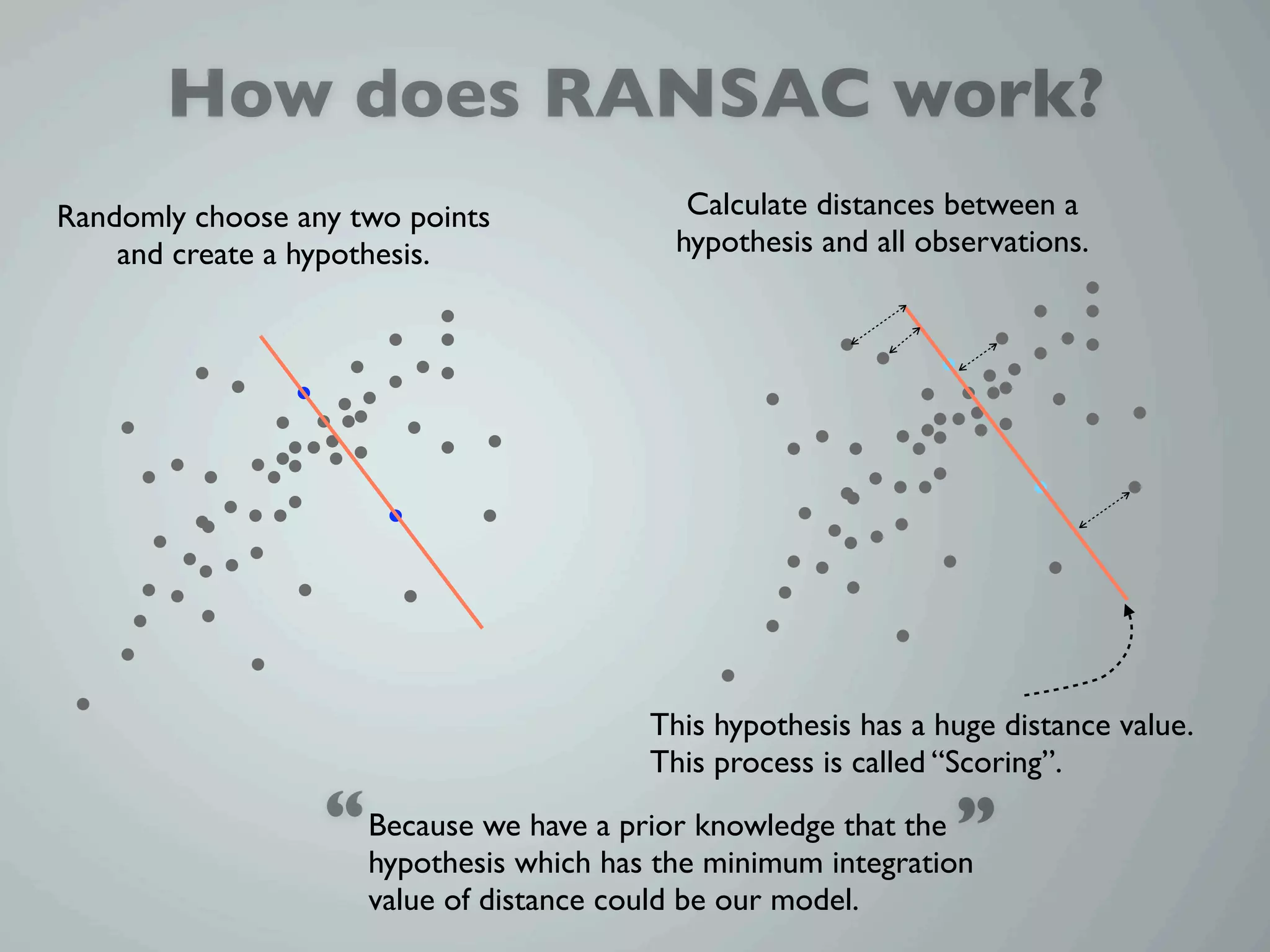
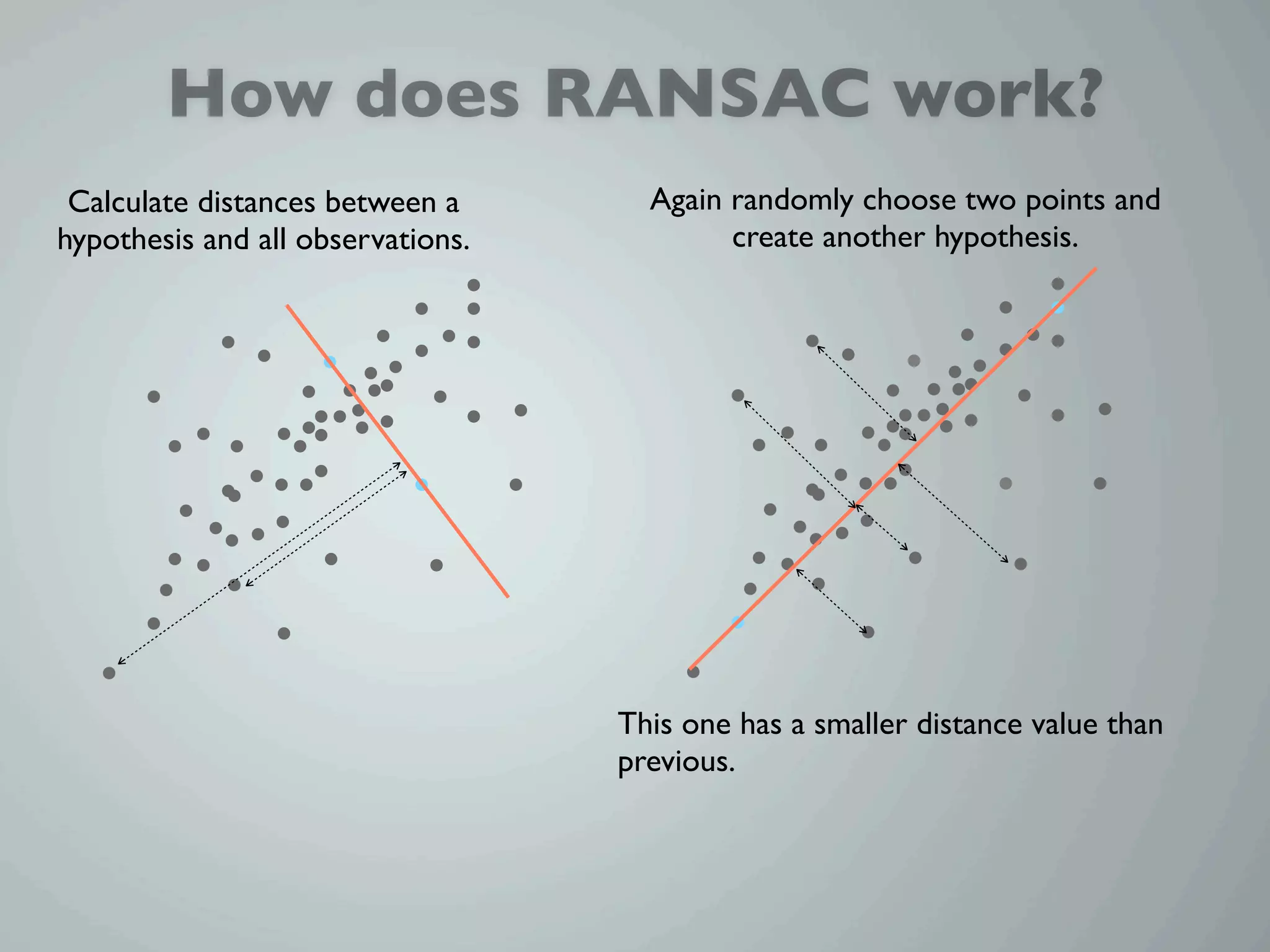
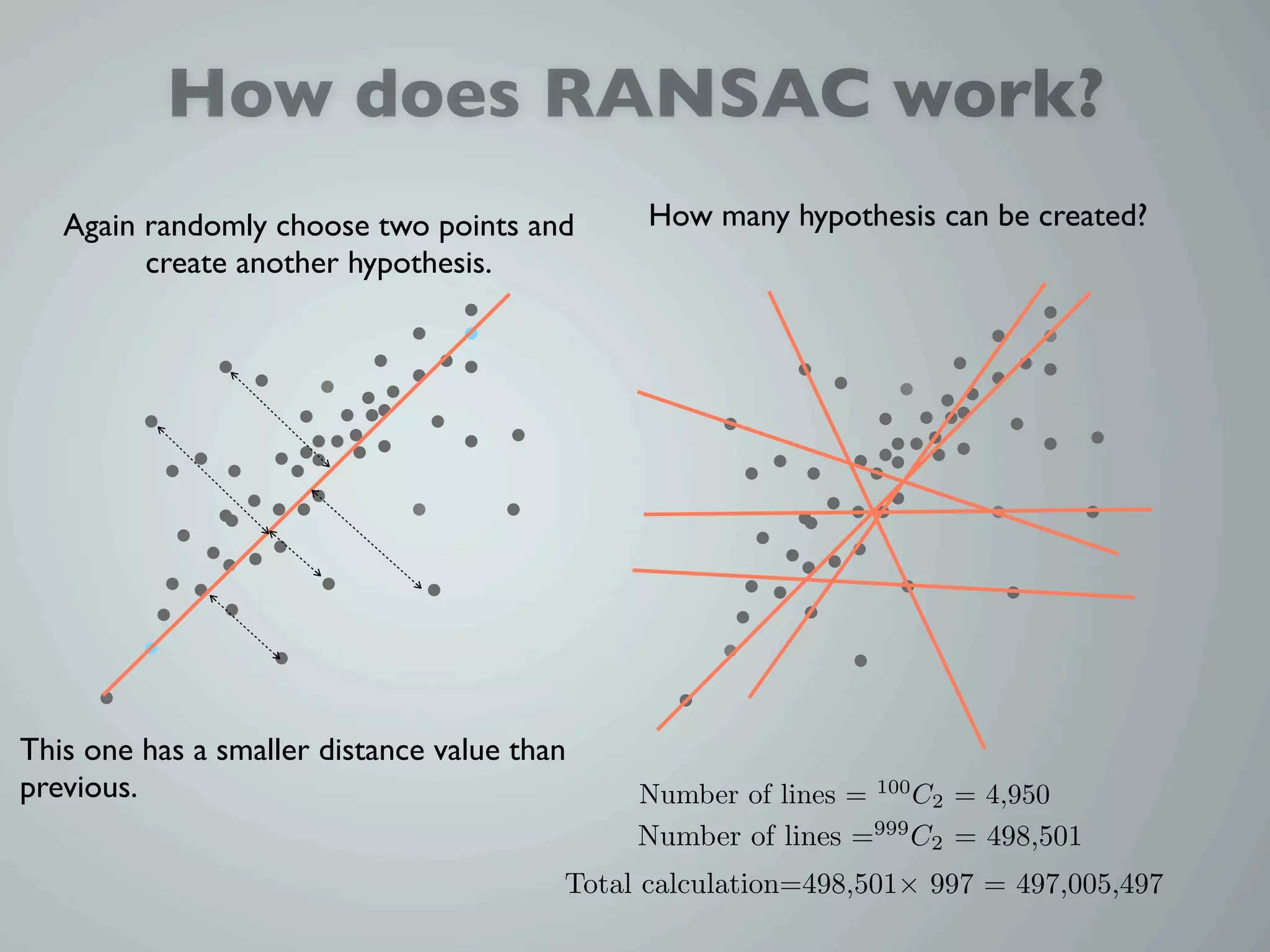
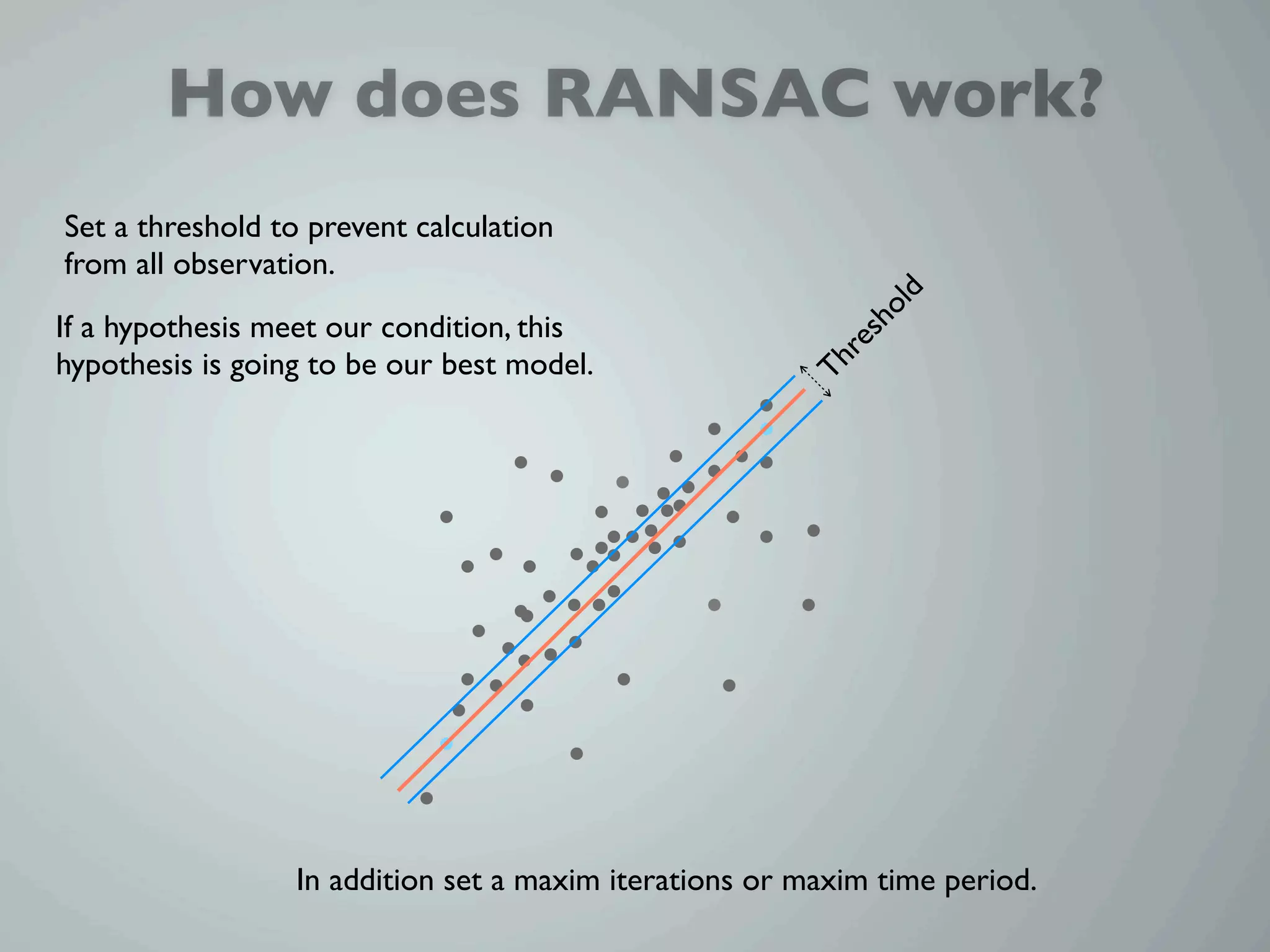
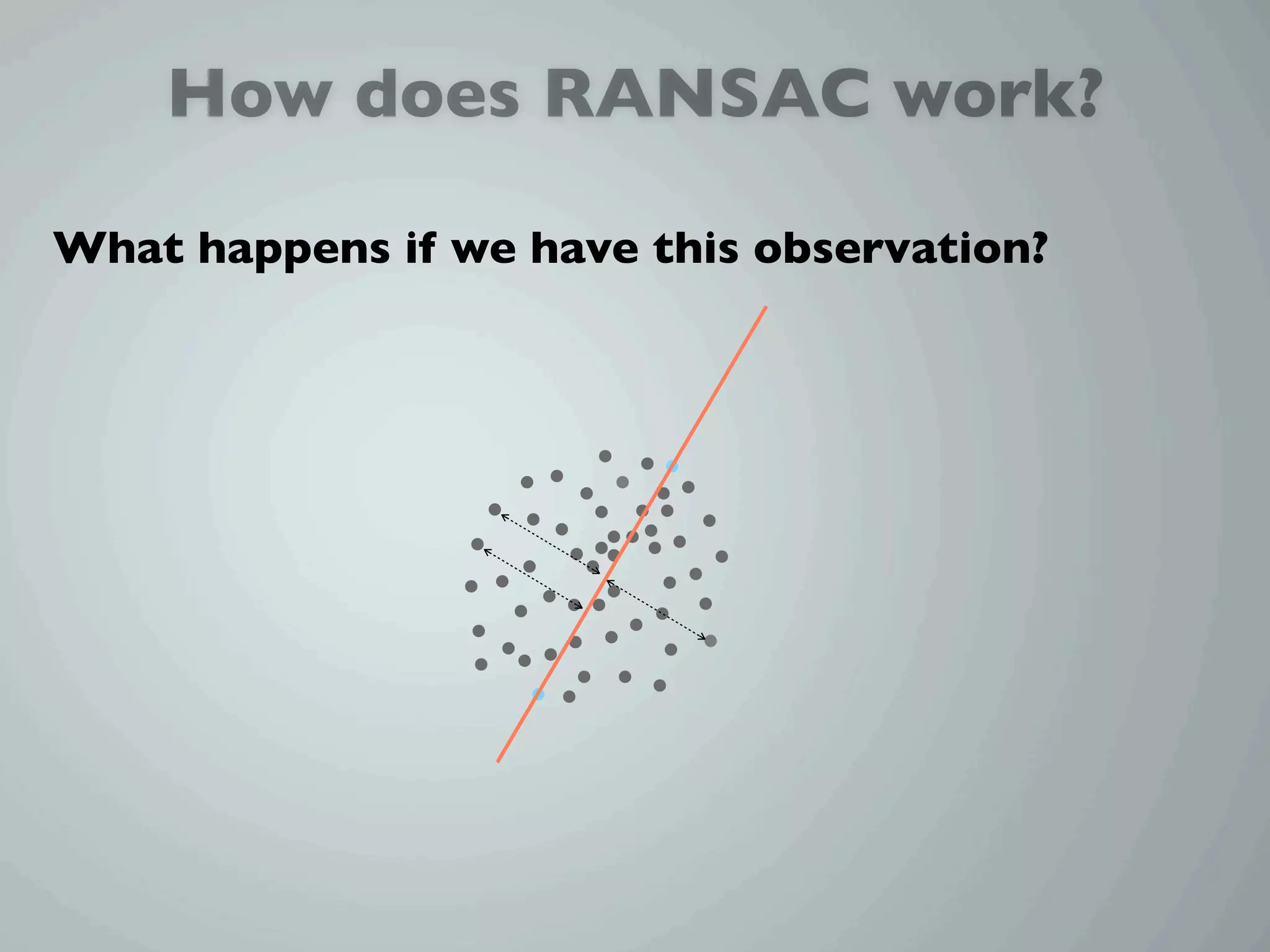
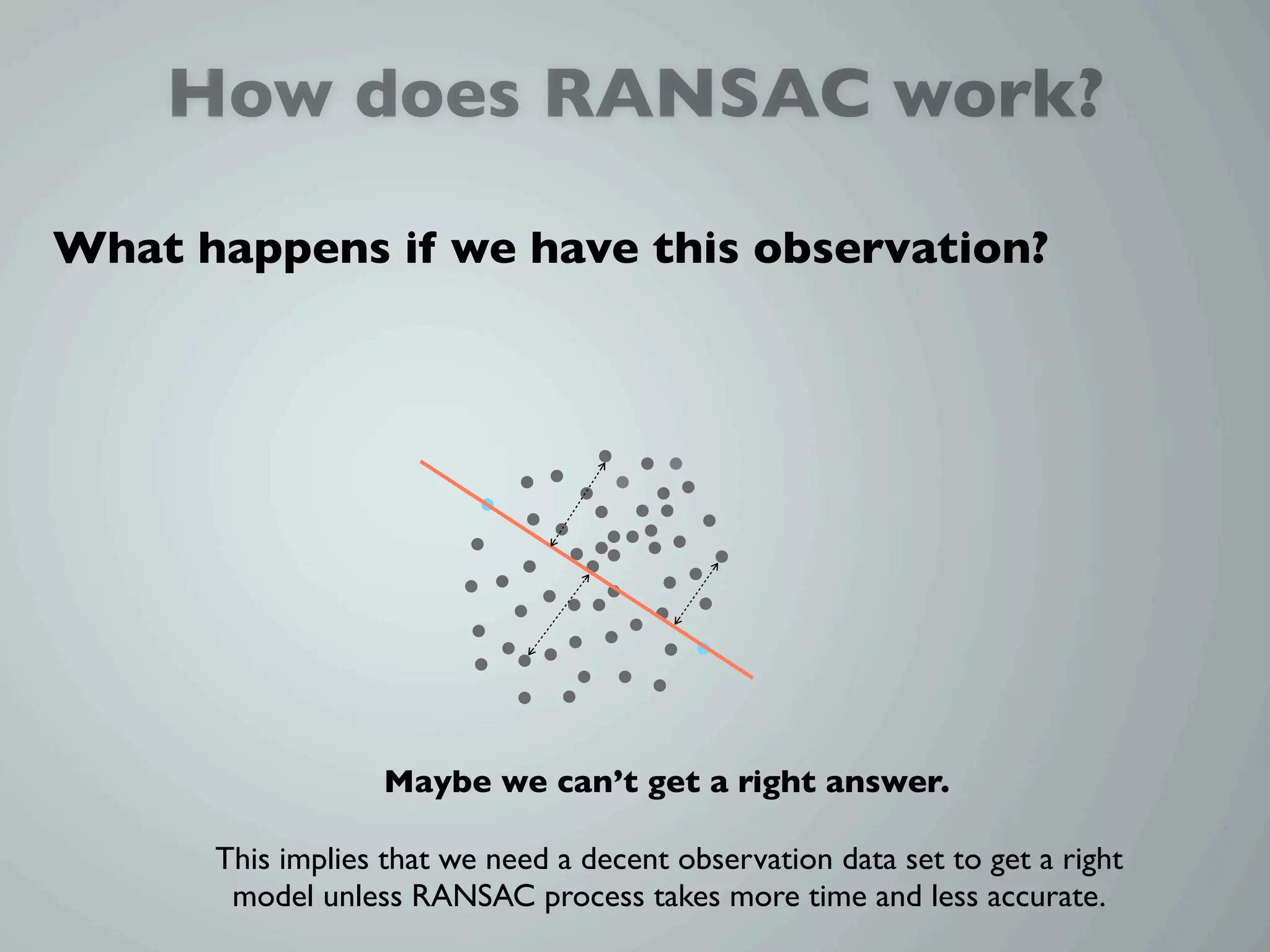
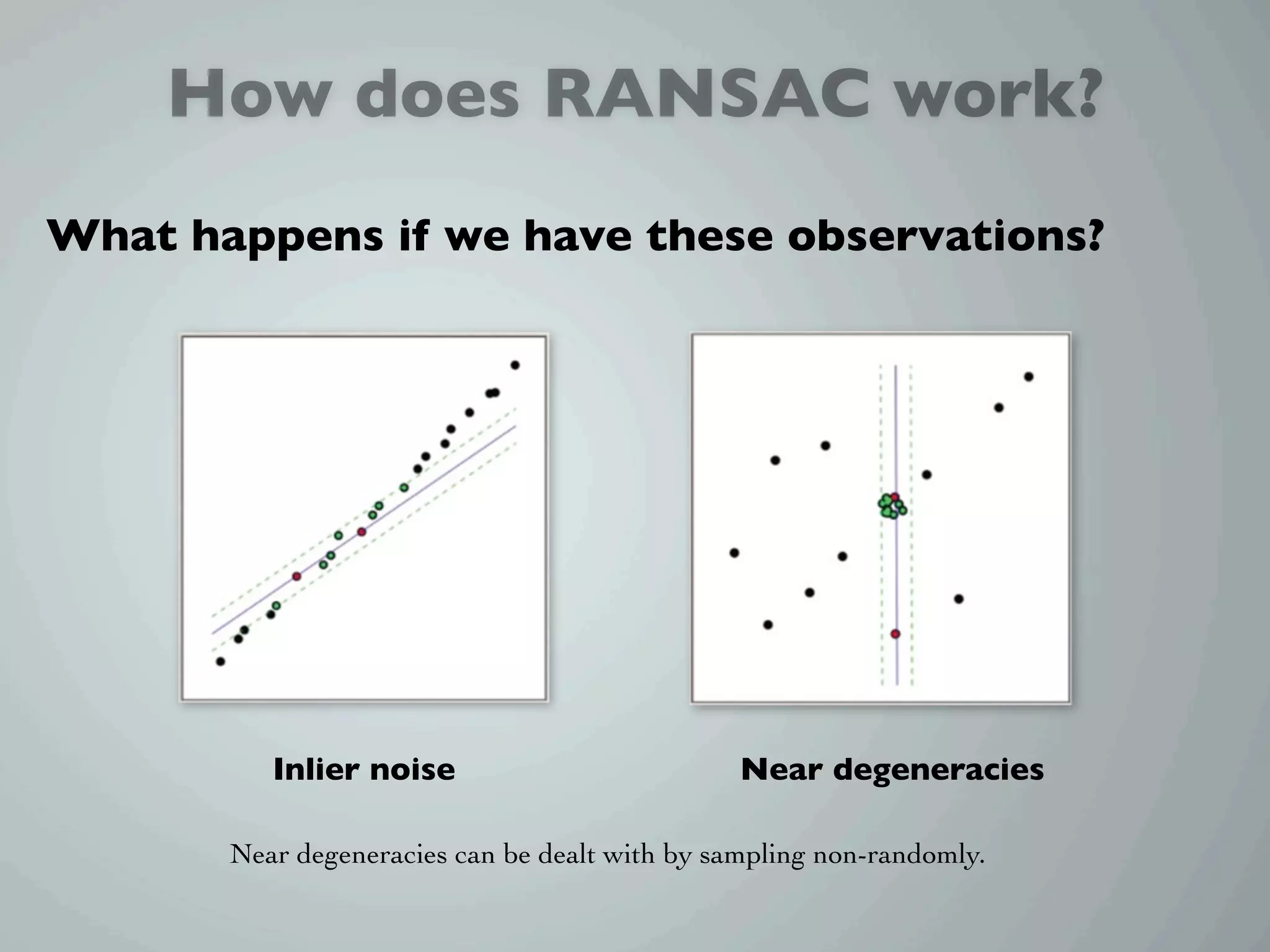
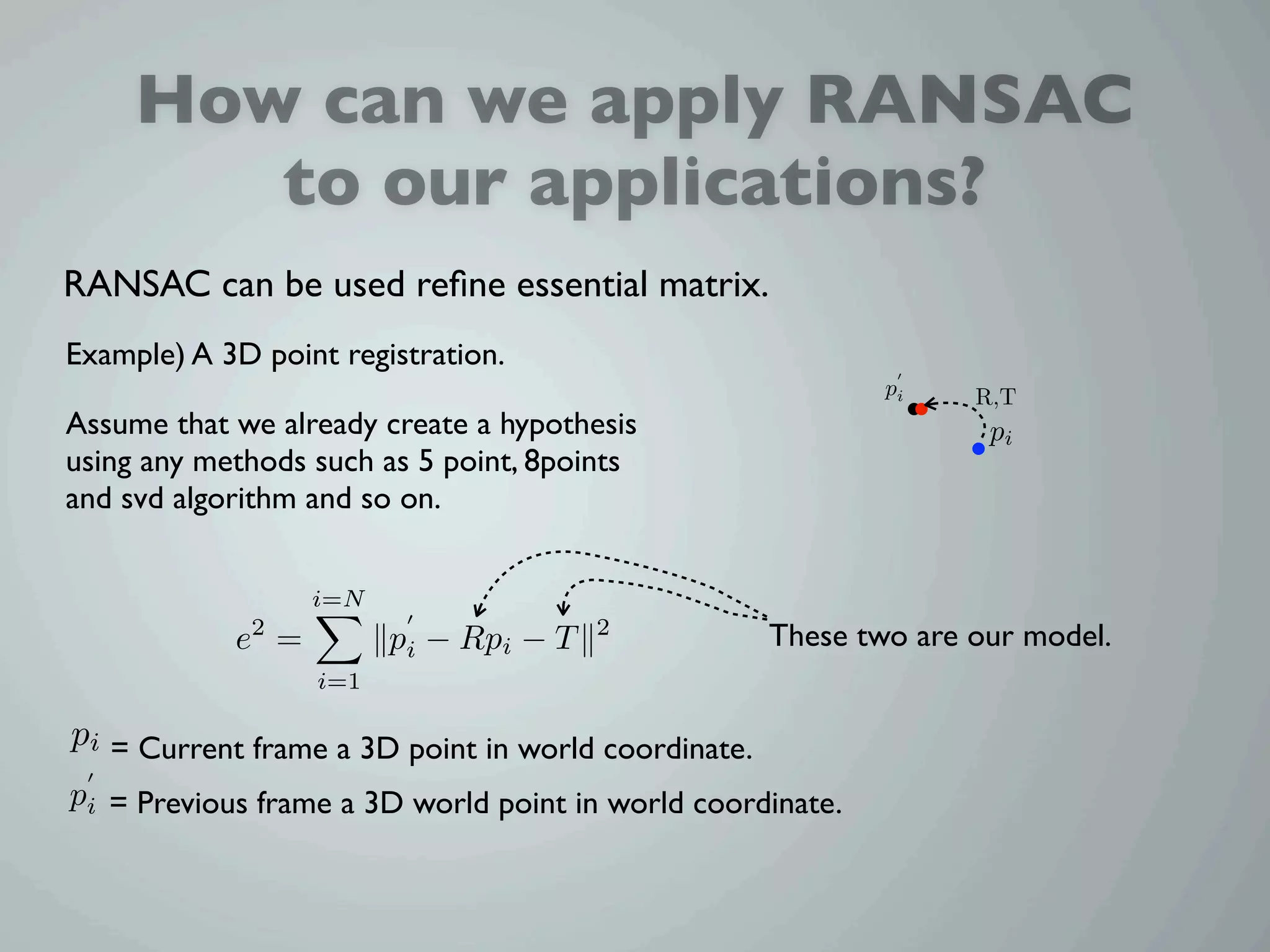
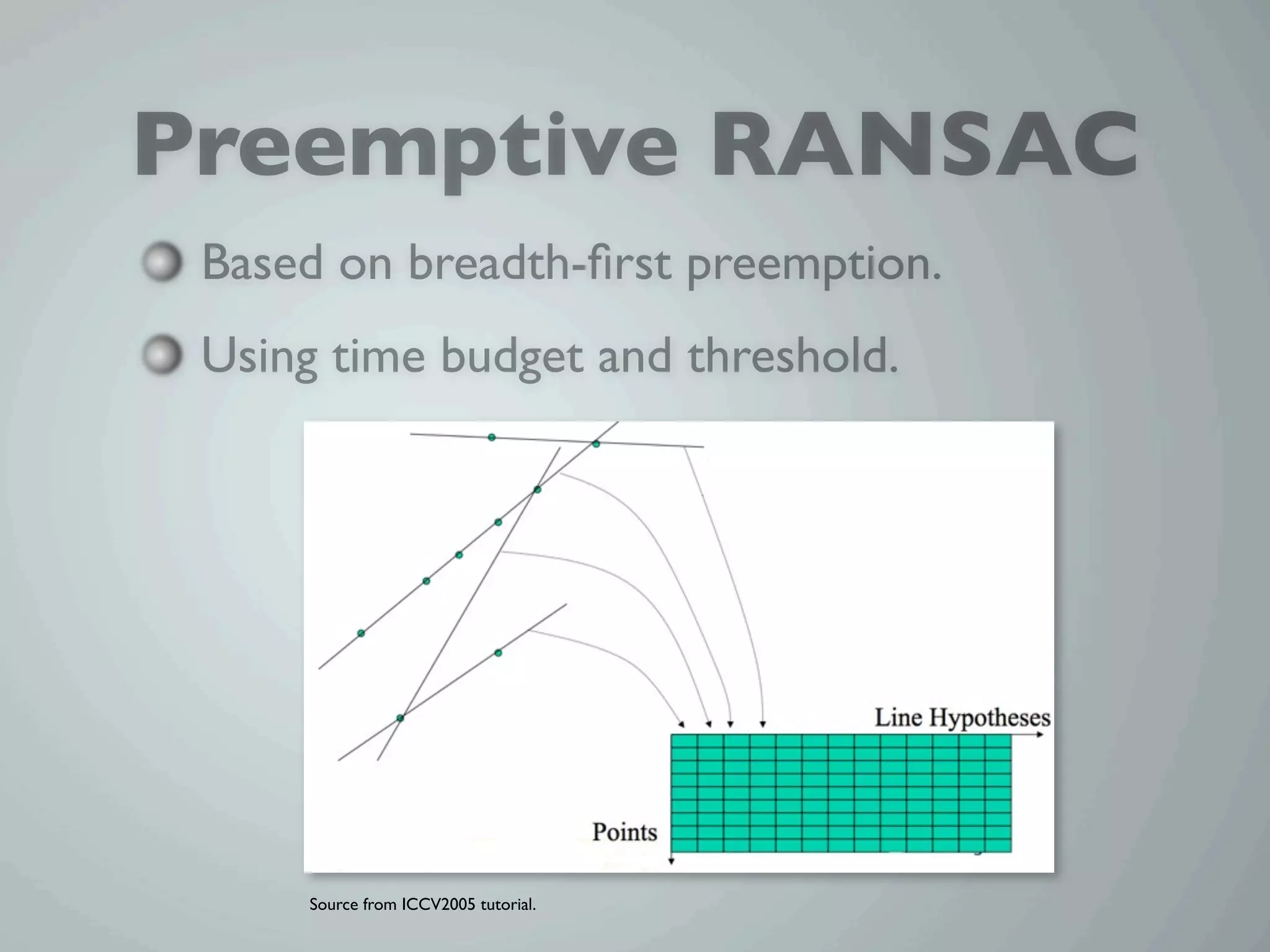
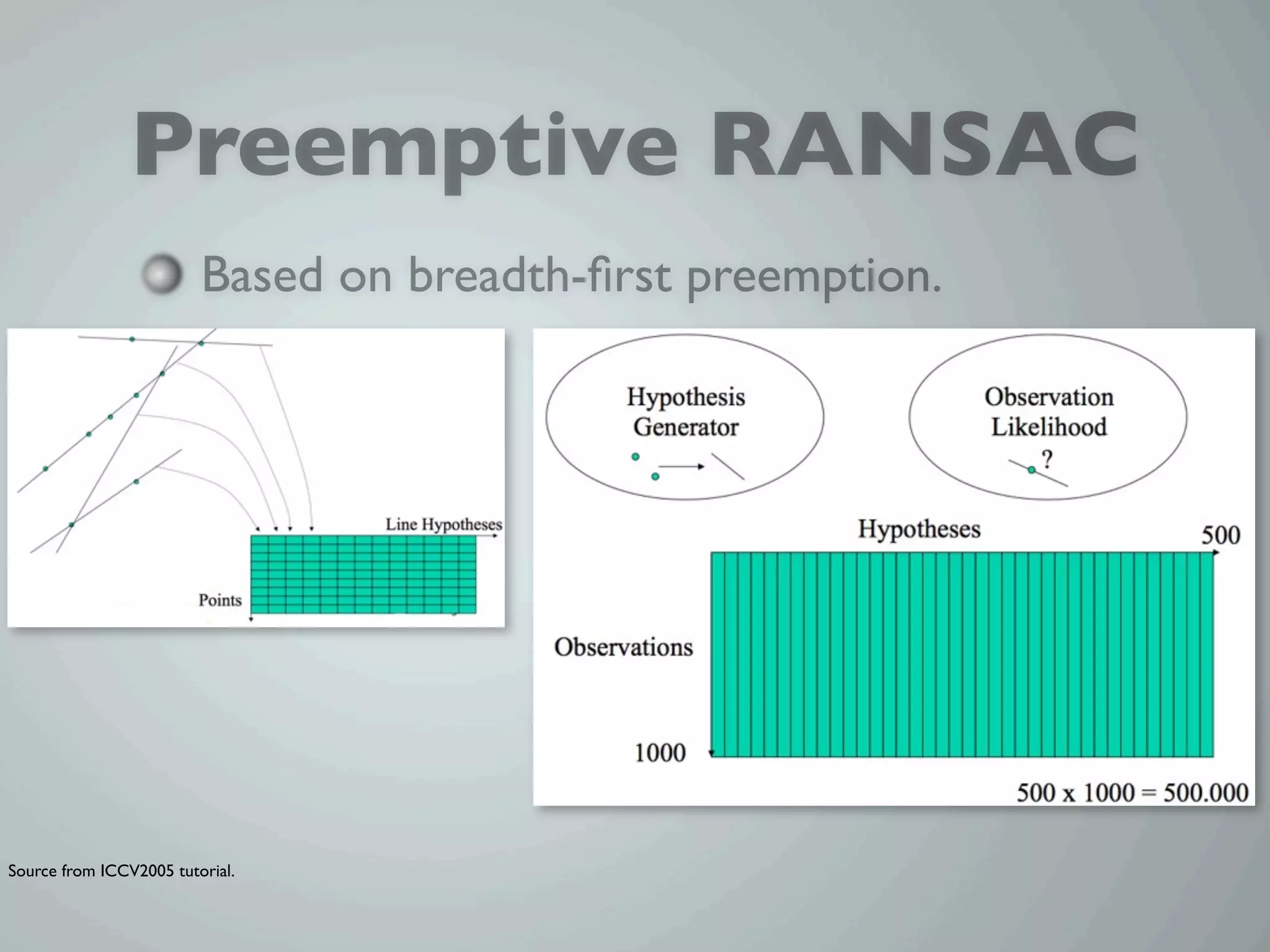
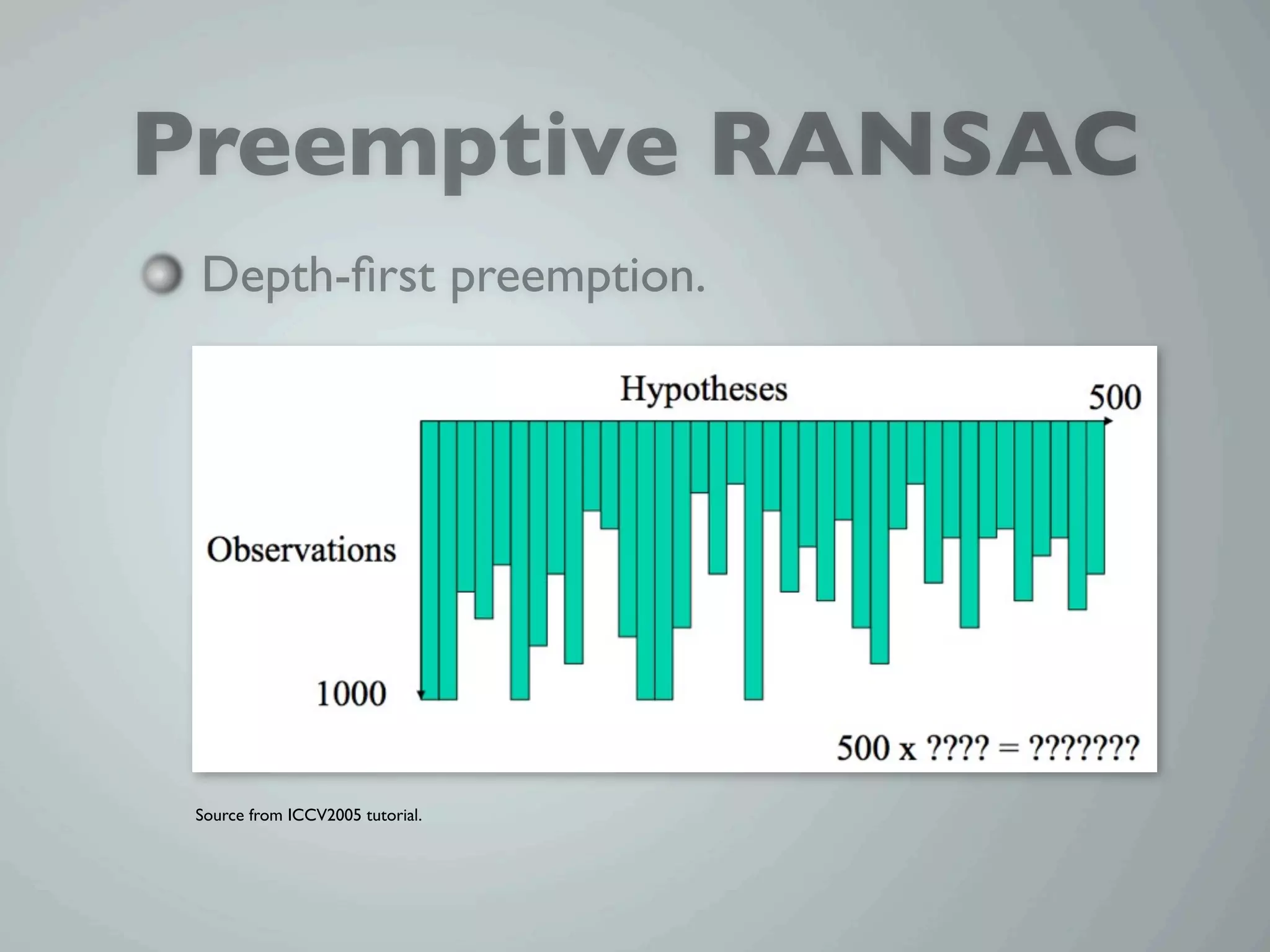
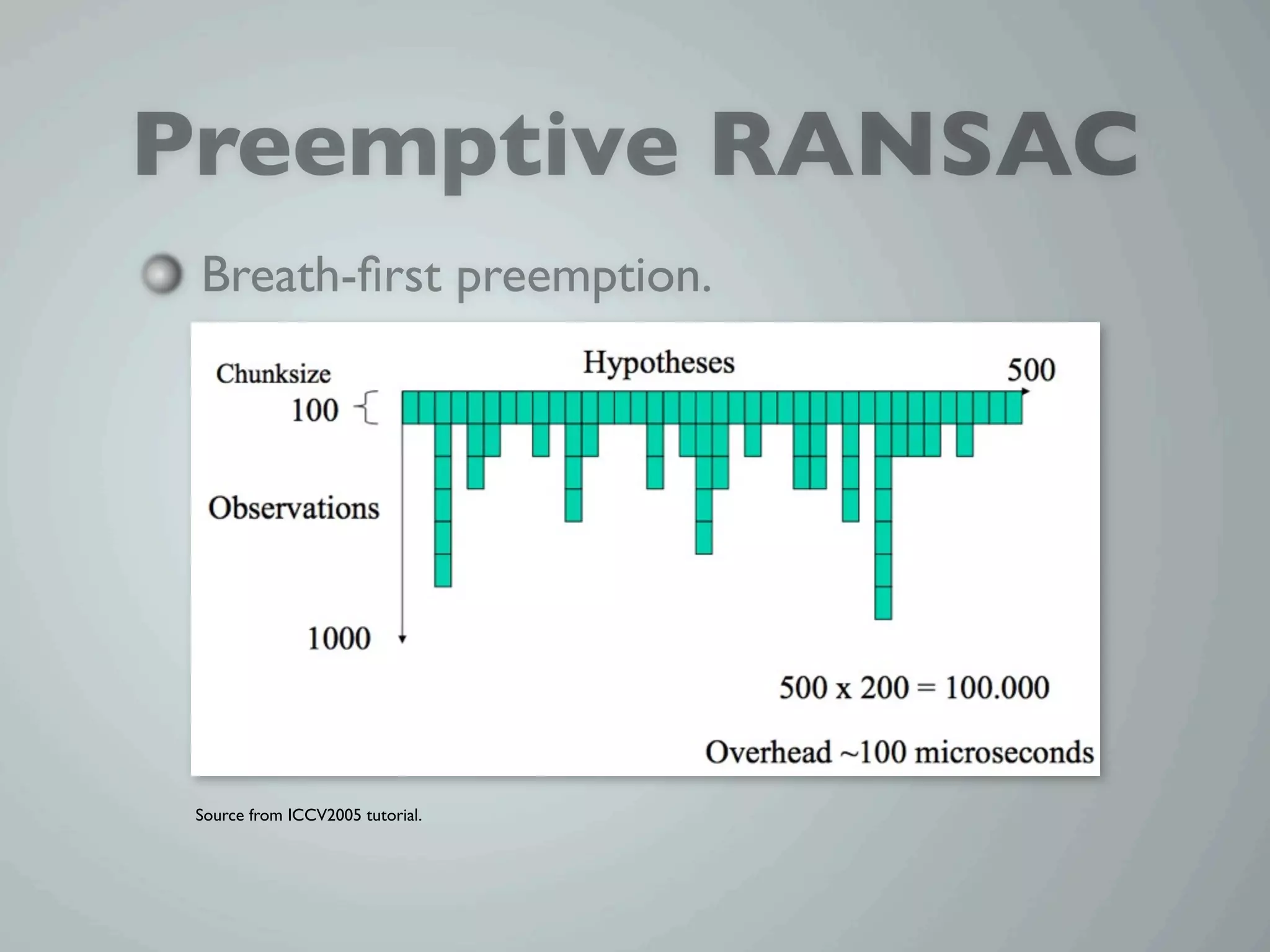
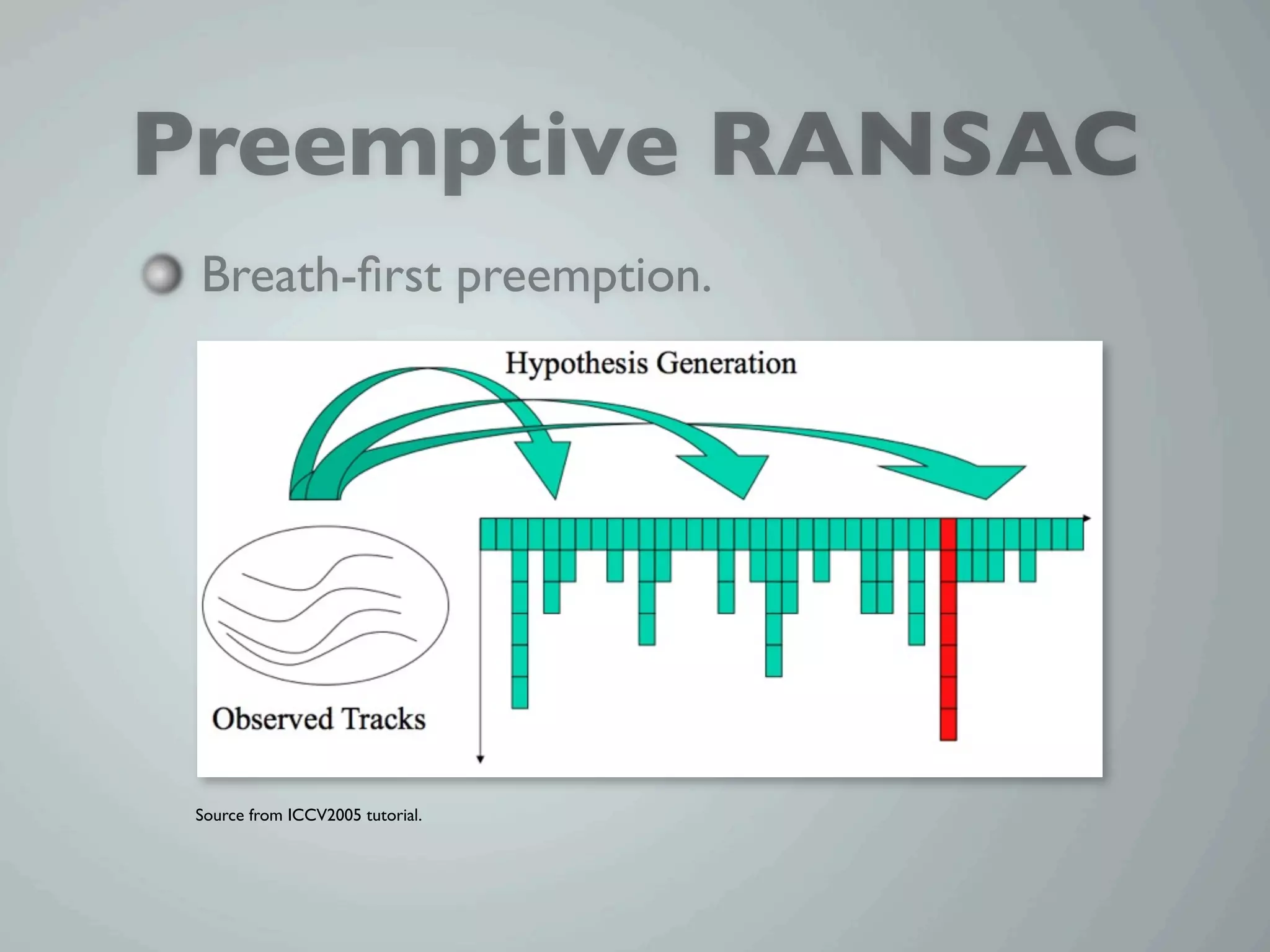
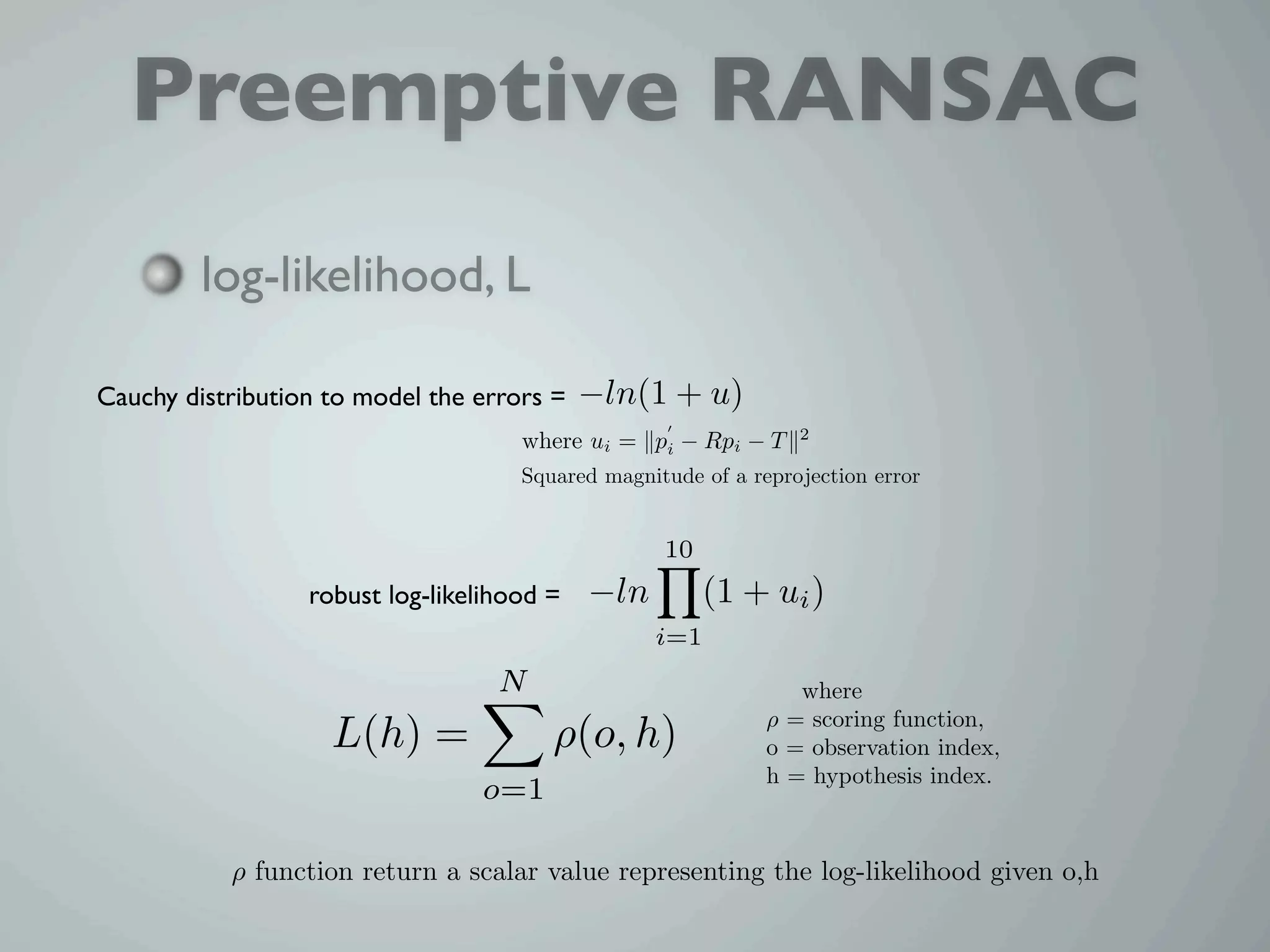
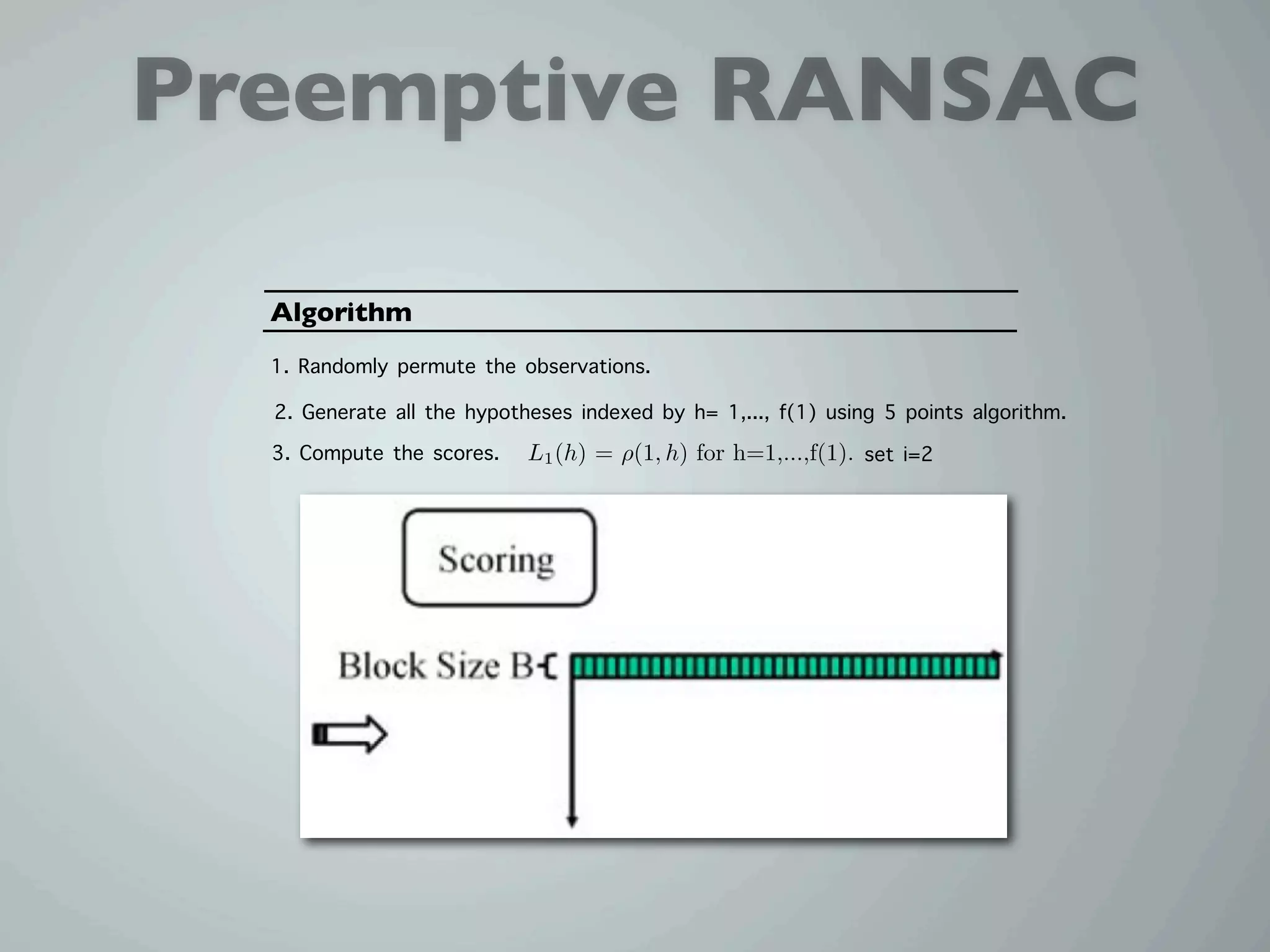
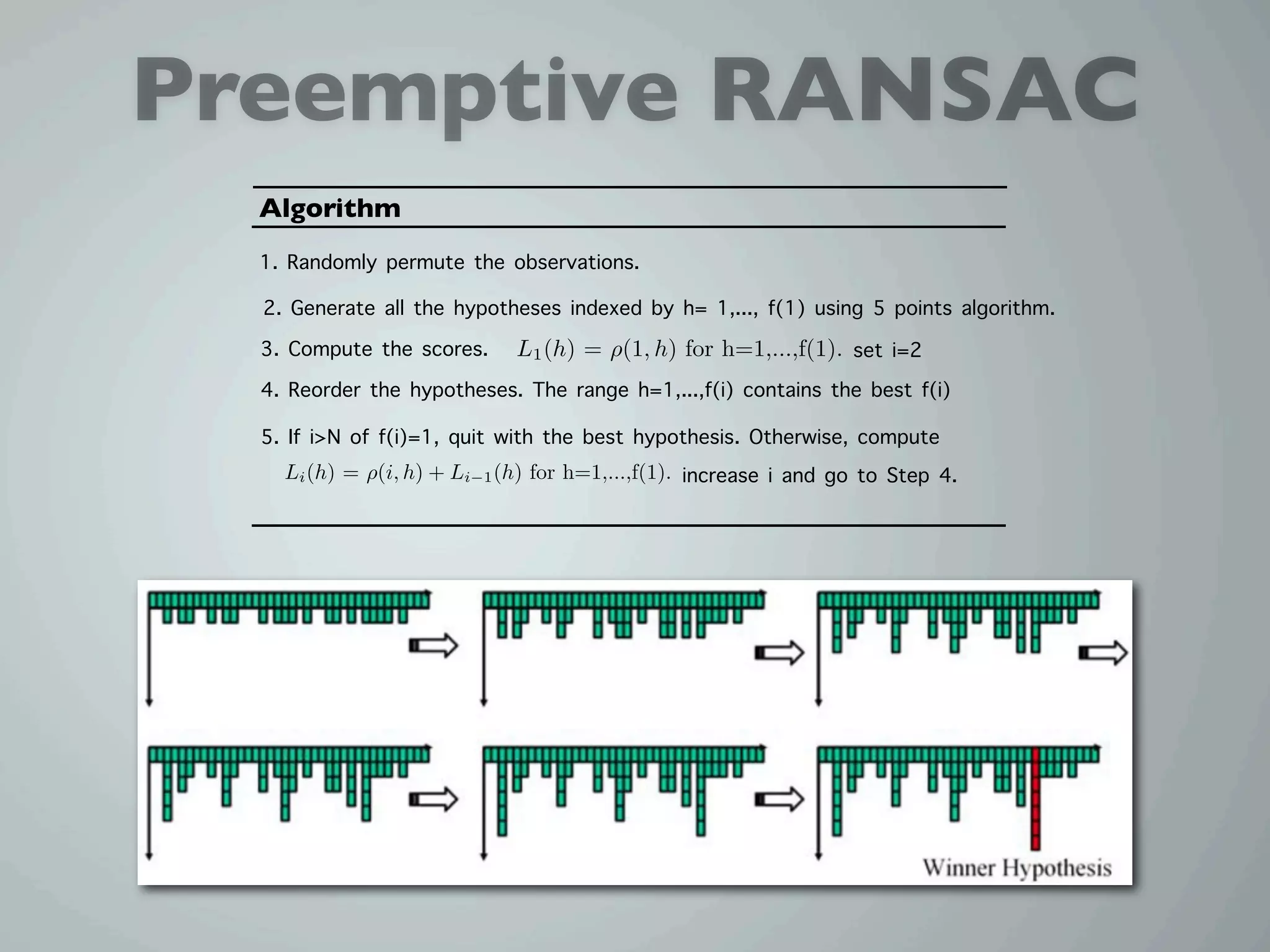
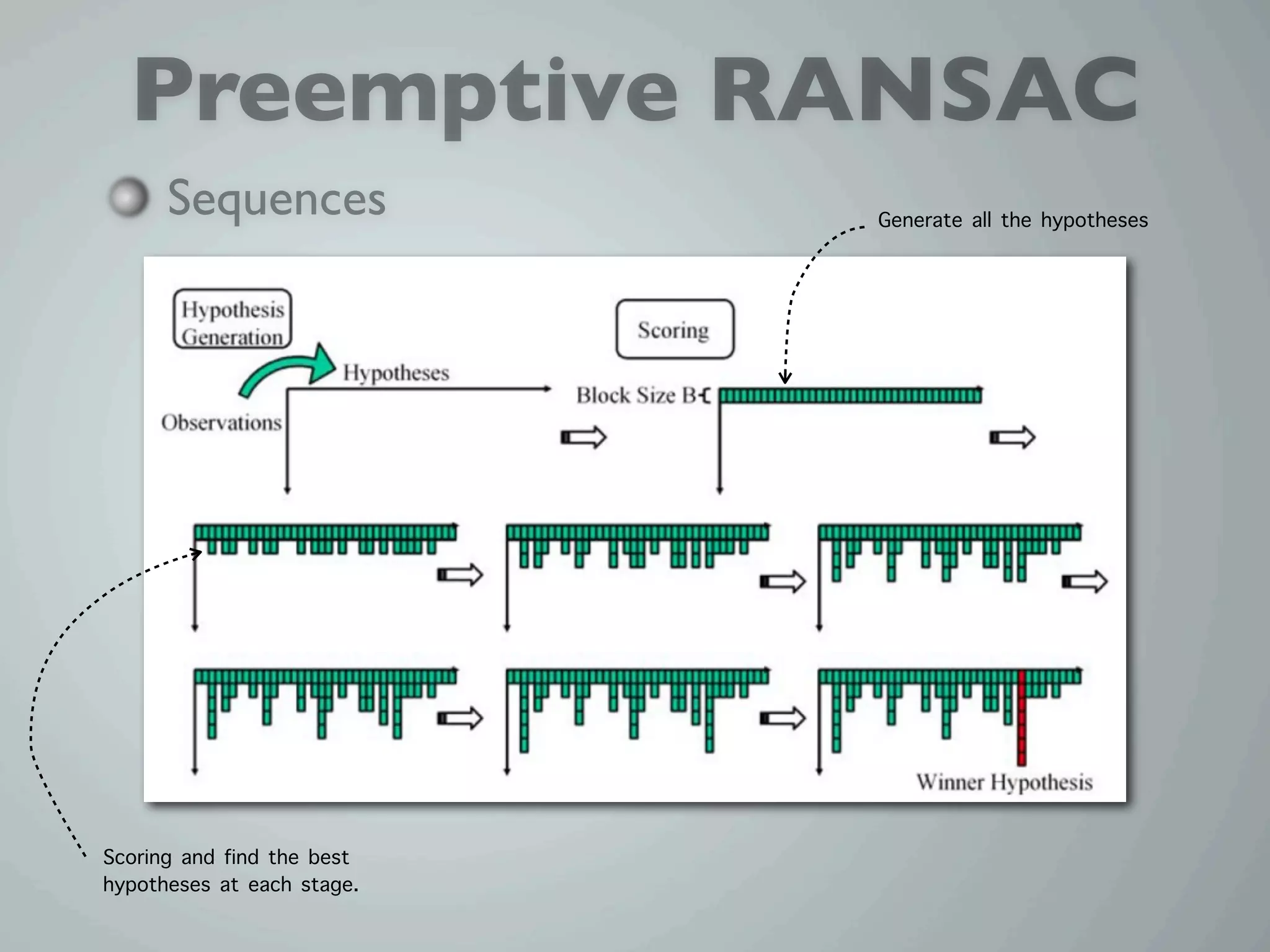
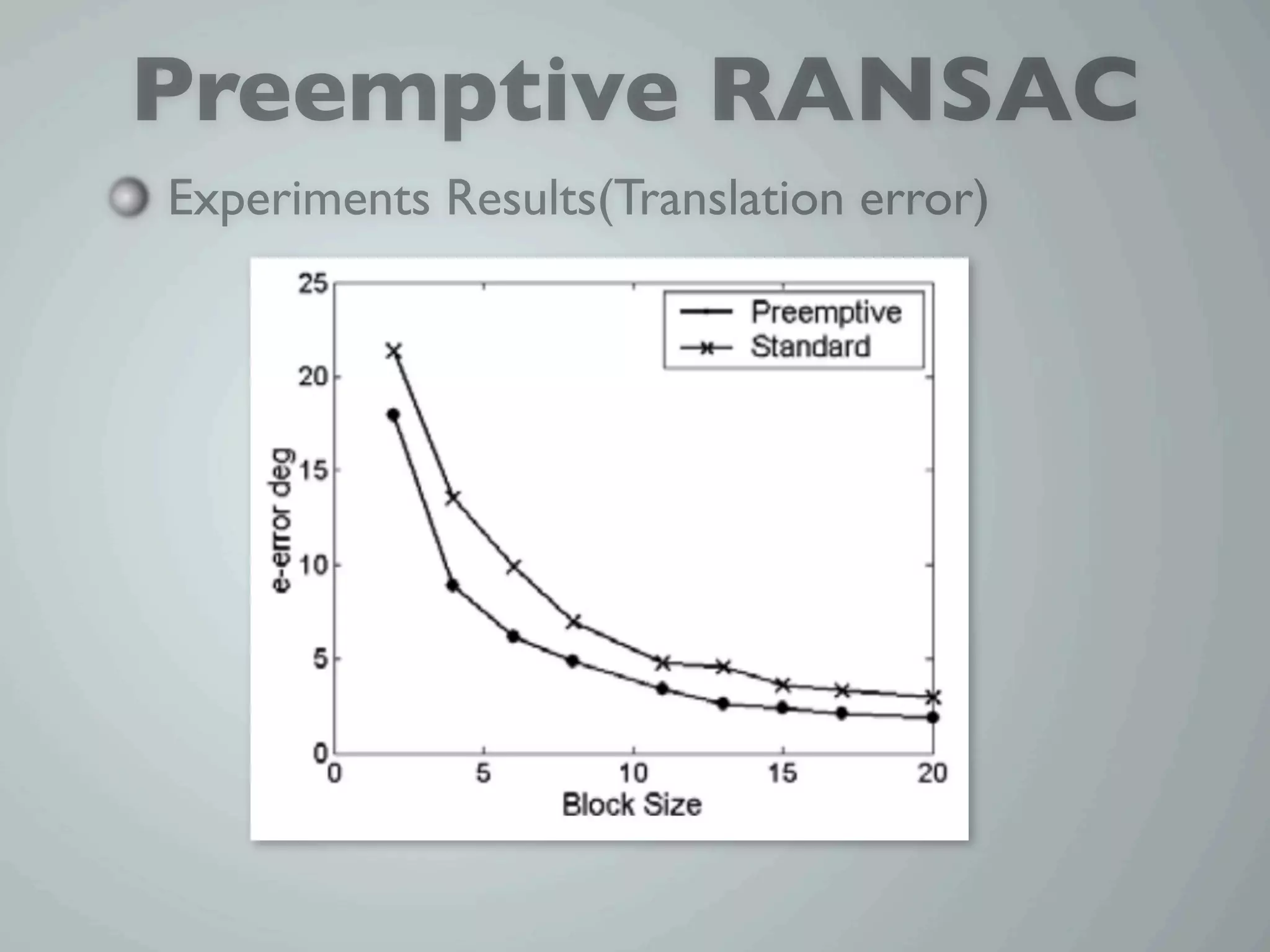
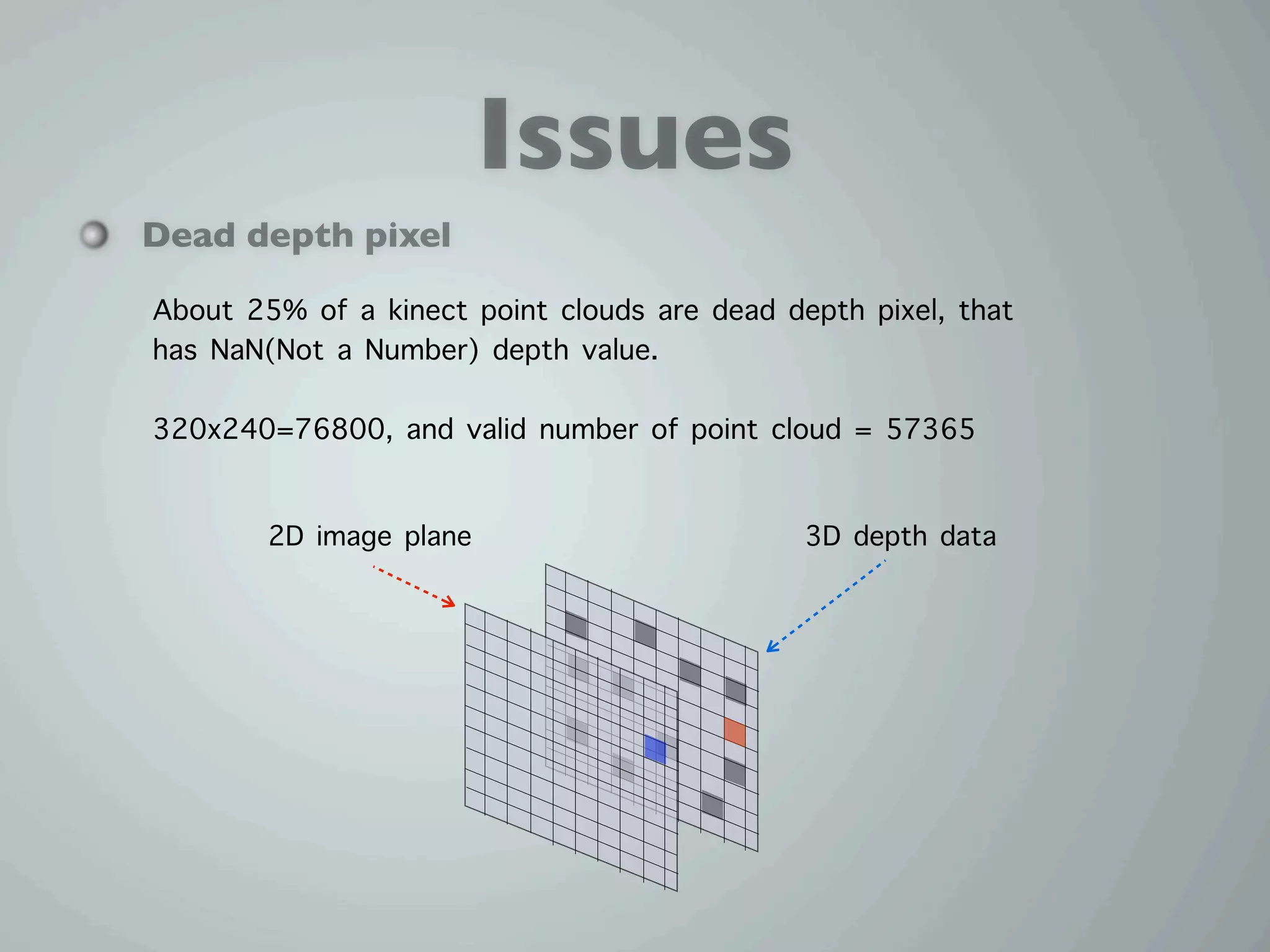
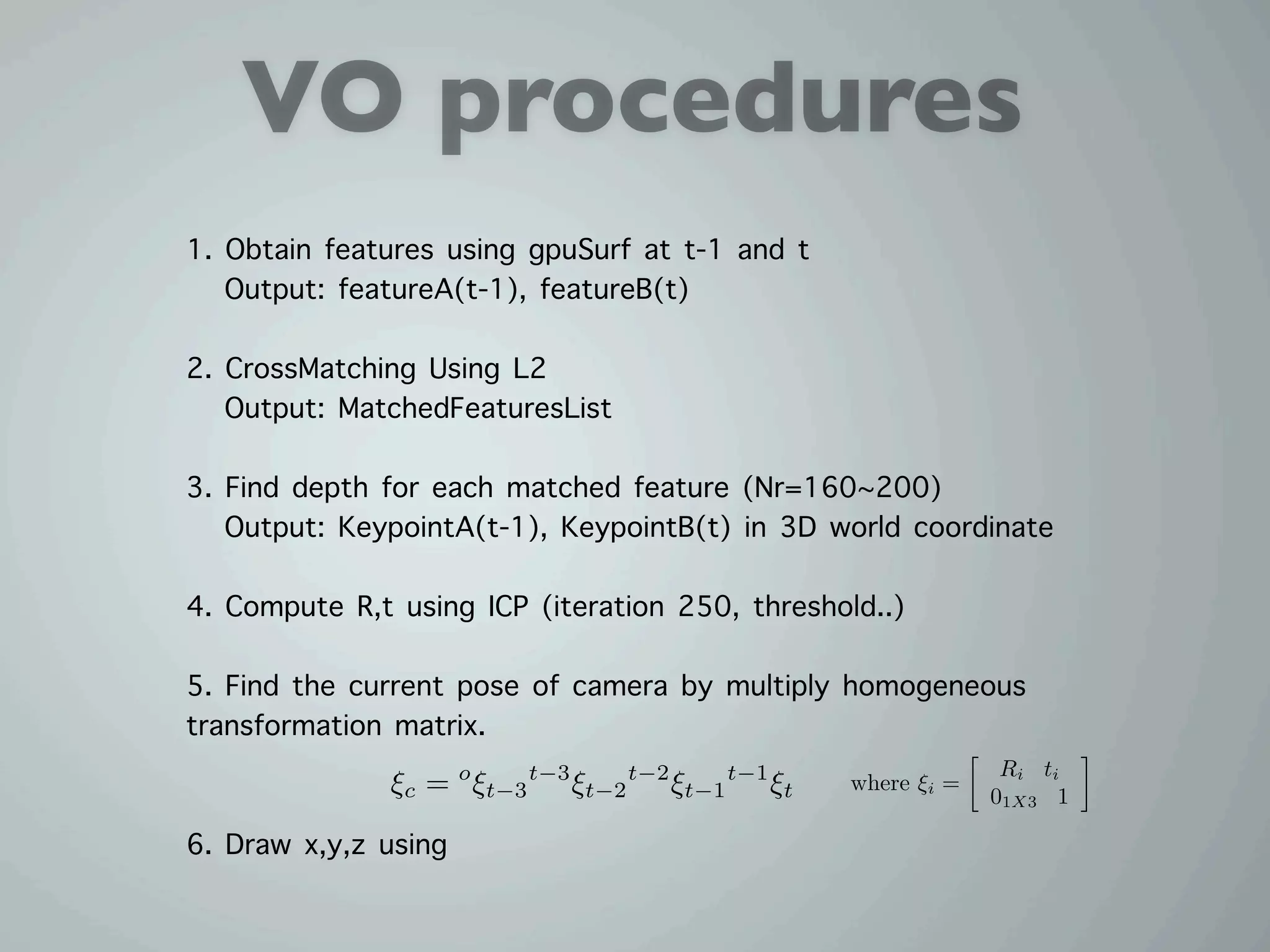
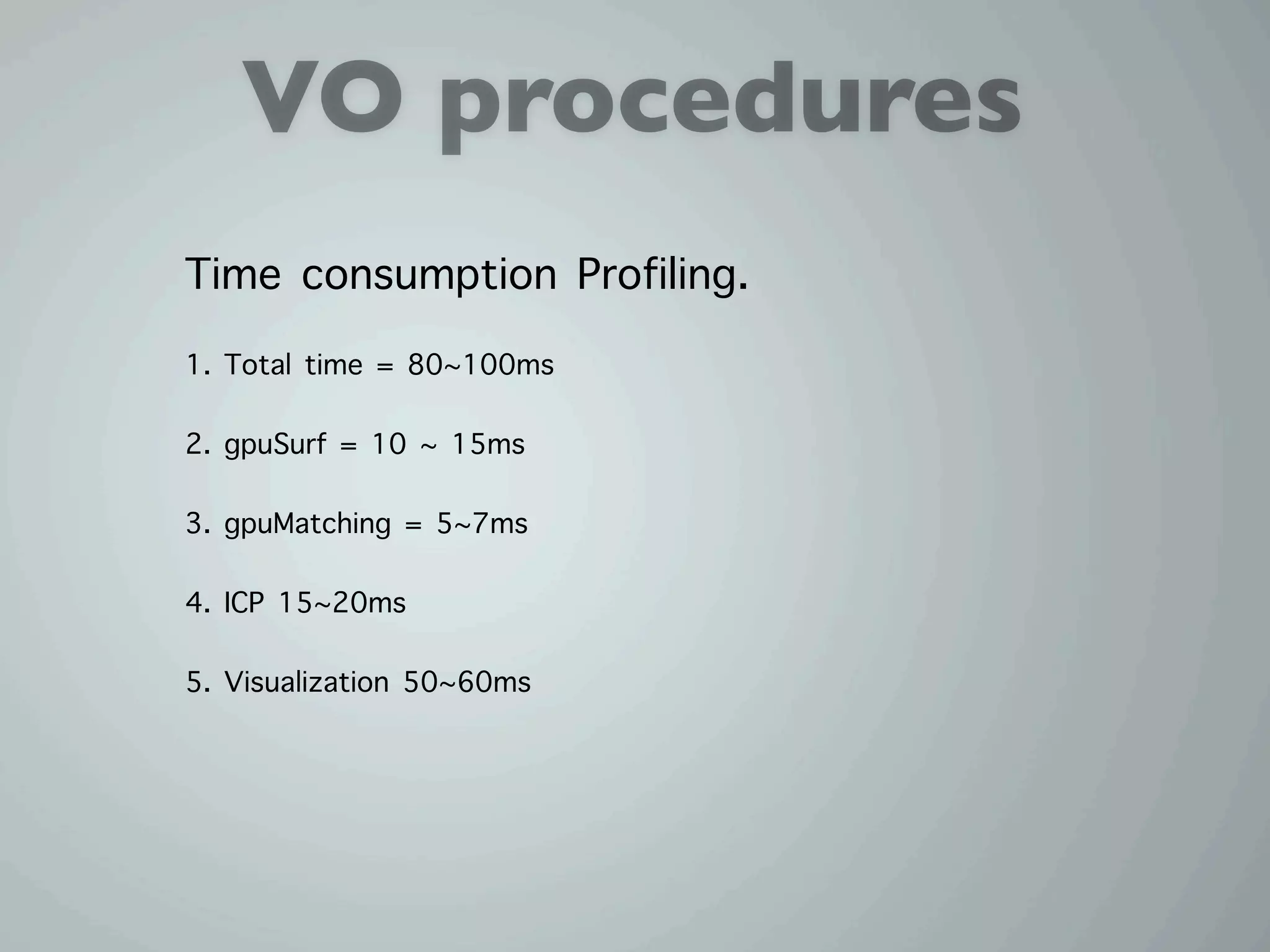
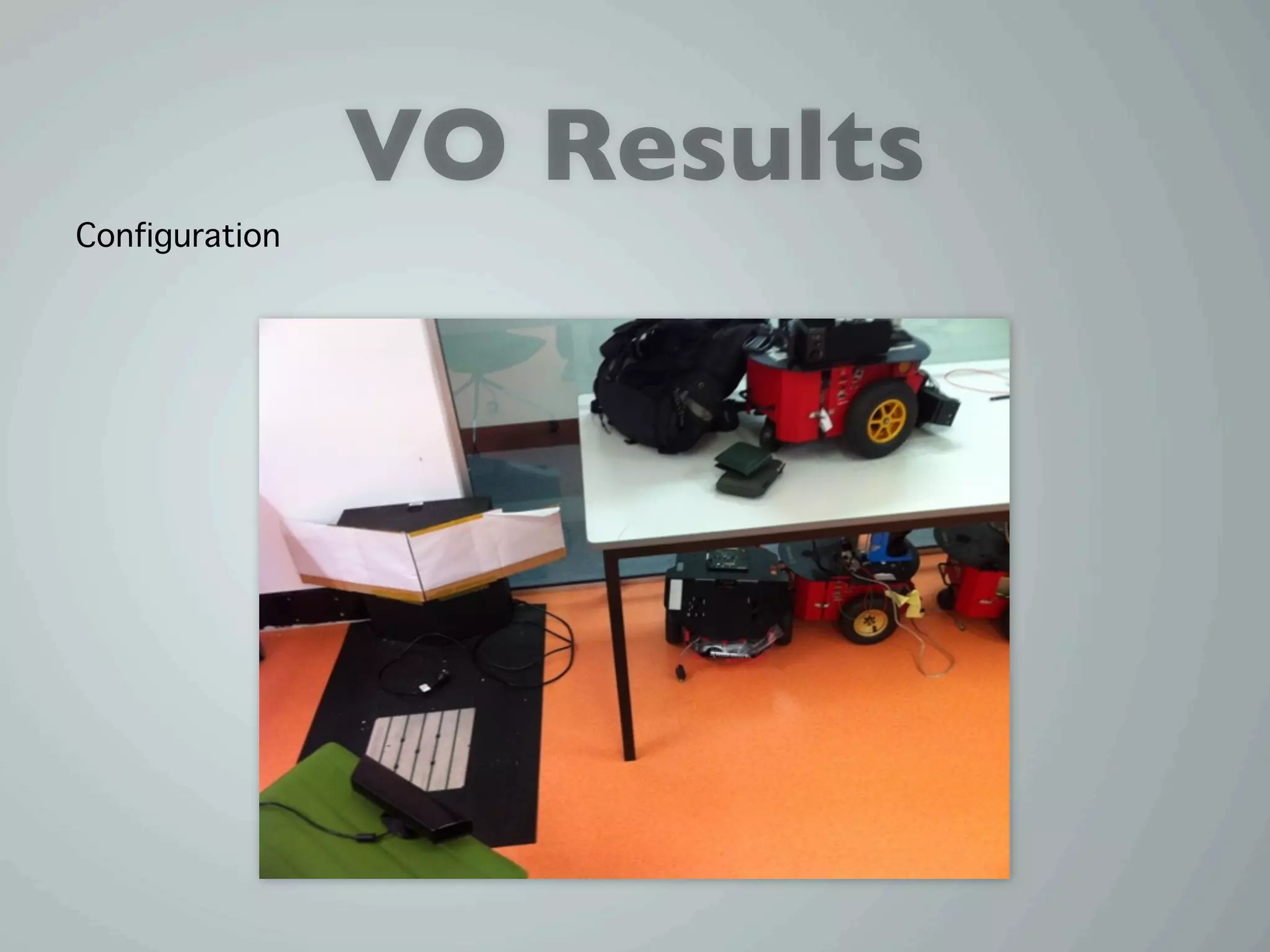
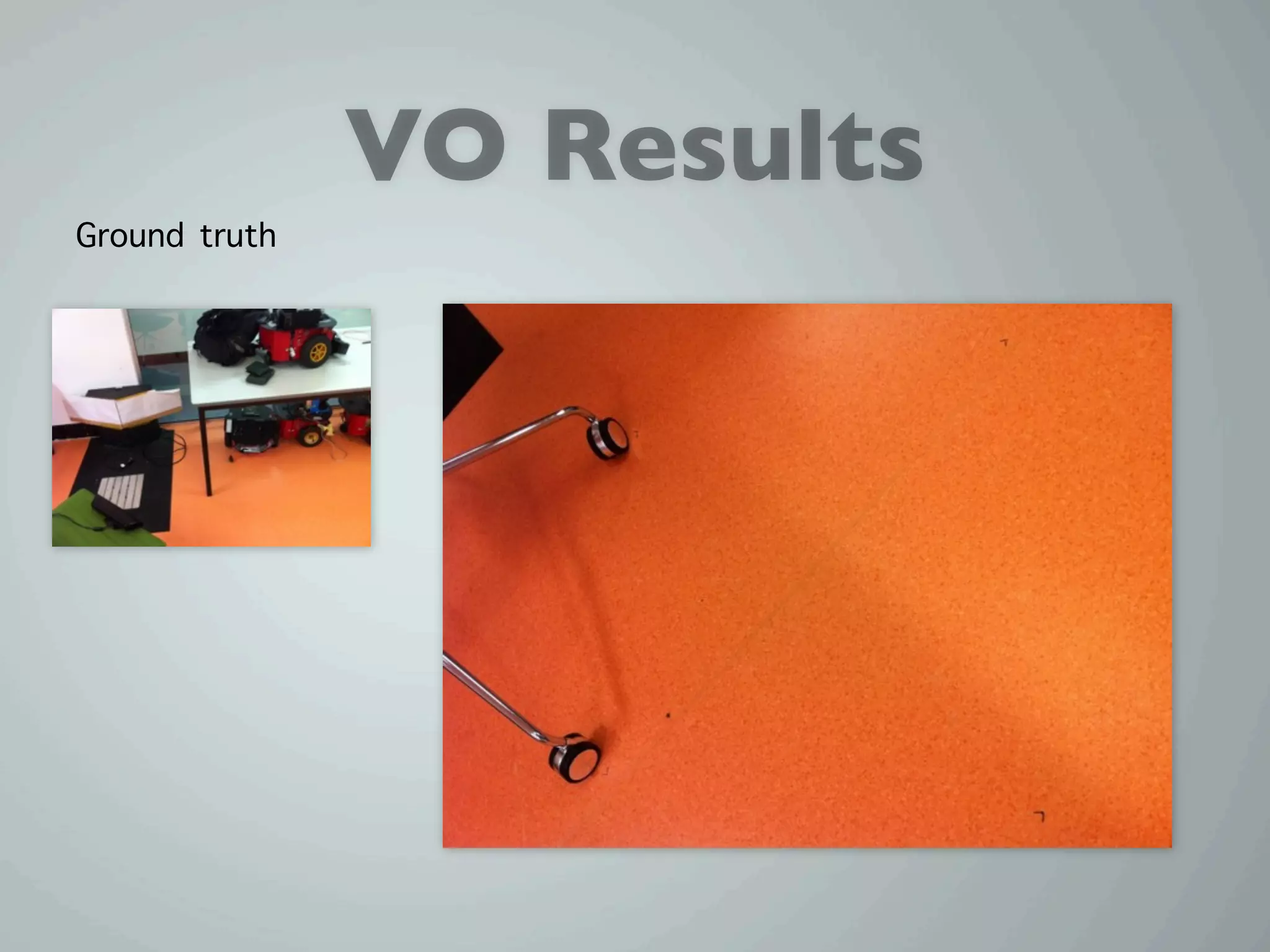
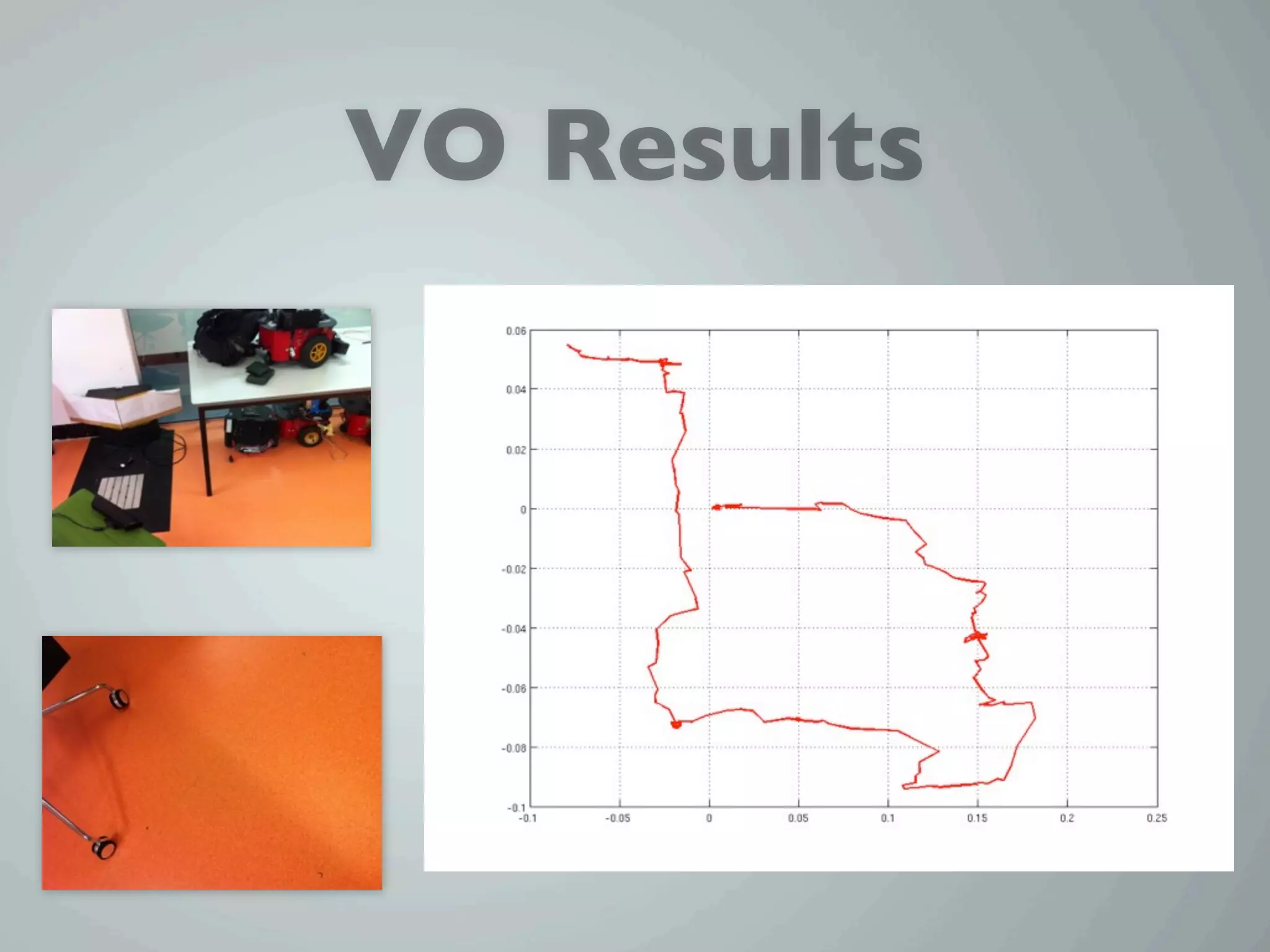
This document discusses the preemptive RANSAC (Random Sample Consensus) algorithm for live structure and motion estimation, outlining its methodology, advantages, and limitations. It emphasizes the importance of choosing robust hypotheses while managing observation data to mitigate errors caused by outliers and noise. Additionally, it describes experimental results related to implementing this algorithm in motion tracking applications using depth data from a Kinect sensor.