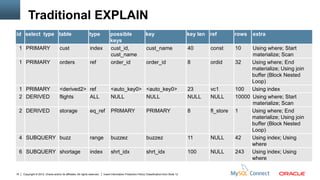
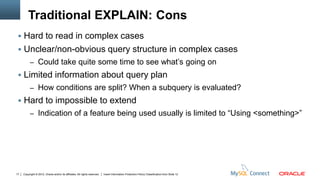
The document discusses the EXPLAIN statement in MySQL. It provides examples of using the traditional EXPLAIN output and the new JSON format for EXPLAIN. The JSON format provides more detailed information about the query plan and execution in a structured format. It allows seeing things like how conditions are split and when subqueries are evaluated.



![Optimizer trace: quick start
mysql> SET optimizer_trace= “enabled=on“,
end_markers_in_json=on;
mysql> SELECT * FROM orders WHERE customer_id <> 6;
mysql> SELECT trace FROM
information_schema.OPTIMIZER_TRACE;
mysql> SET optimizer_trace="enabled=off";
QUERY SELECT * FROM orders WHERE customer_id <> 6
TRACE “steps”: [ { "join_preparation": { "select#": 1,… } … } …]
MISSING_BYTES_BEYOND_MAX_MEM_SIZE 0
INSUFFICIENT_PRIVILEGES 0
6 Copyright © 2012, Oracle and/or its affiliates. All rights reserved. Insert Information Protection Policy Classification from Slide 12](https://image.slidesharecdn.com/powerfulexplainmysql56-130322100527-phpapp02/85/Powerful-Explain-in-MySQL-5-6-6-320.jpg)
![Optimizer trace: example
join_optimization / steps / condition_processing
"condition": "WHERE",
"original_condition": "((`t1`.`f1` = 1) and (`t1`.`f1` = `t2`.`f2`) and (`t2`.`f2` > 0))",
"steps": [
{
"transformation": "equality_propagation",
"resulting_condition": "((`t2`.`f2` > 0) and multiple equal(1, `t1`.`f1`, `t2`.`f2`))"
}, {
"transformation": "constant_propagation",
"resulting_condition": "((1 > 0) and multiple equal(1, `t1`.`f1`, `t2`.`f2`))"
}, {
"transformation": "trivial_condition_removal",
"resulting_condition": "multiple equal(1, `t1`.`f1`, `t2`.`f2`)"
}
] /* steps */
9 Copyright © 2012, Oracle and/or its affiliates. All rights reserved. Insert Information Protection Policy Classification from Slide 12](https://image.slidesharecdn.com/powerfulexplainmysql56-130322100527-phpapp02/85/Powerful-Explain-in-MySQL-5-6-9-320.jpg)
![Optimizer trace: example
join_optimization / row_estimation / table : t1, range_analysis
"table_scan": { "analyzing_range_alternatives": {
"rows": 5, "range_scan_alternatives": [ {
"cost": 5.1085 "index": "f1",
} /* table_scan */, "ranges": [ "1 <= f1 <= 1“ ] /* ranges */,
"potential_range_indices": [ { "index_dives_for_eq_ranges": true,
"index": "f1", "usable": true, "rows": 2, "cost": 3.41,
"key_parts": [ "f1“ ] /* key_parts */ } "chosen": false,
] /* potential_range_indices */, "cause": "cost"
"best_covering_index_scan": { }
"index": "f1", "cost": 2.093, "chosen": true ] /* range_scan_alternatives */,
} /* best_covering_index_scan */, "analyzing_roworder_intersect": {
"group_index_range": { "usable": false, "cause": "too_few_roworder_scans"
"chosen": false, "cause": "not_single_table" } /* analyzing_roworder_intersect */
} /* group_index_range */, } /* analyzing_range_alternatives */
10 Copyright © 2012, Oracle and/or its affiliates. All rights reserved. Insert Information Protection Policy Classification from Slide 12](https://image.slidesharecdn.com/powerfulexplainmysql56-130322100527-phpapp02/85/Powerful-Explain-in-MySQL-5-6-10-320.jpg)
![Optimizer trace: example
join_optimization / considered_execution_plan
"plan_prefix": [ ] /* plan_prefix */, "plan_prefix": [ "`t2`“ ] /* plan_prefix */,
"table": "`t2`", "table": "`t1`",
"best_access_path": { "best_access_path": {
"considered_access_paths": [ { "considered_access_paths": [ {
"access_type": "scan", "rows": 3, "access_type": "ref", "index": "f1",
"cost": 2.6051, "chosen": true "rows": 2, "cost": 3.4698, "chosen": true
} ] /* considered_access_paths */ }, {
} /* best_access_path */, "access_type": "scan", "using_join_cache": true,
"cost_for_plan": 2.6051, "rows": 2, "cost": 3.8087,
"rows_for_plan": 3, "chosen": true
"rest_of_plan": [ { } ] } /* best_access_path */,
… next iteration … => "cost_for_plan": 6.4138,
} ] /* rest_of_plan */ "rows_for_plan": 6,
"chosen": true
11 Copyright © 2012, Oracle and/or its affiliates. All rights reserved. Insert Information Protection Policy Classification from Slide 12](https://image.slidesharecdn.com/powerfulexplainmysql56-130322100527-phpapp02/85/Powerful-Explain-in-MySQL-5-6-11-320.jpg)
![Optimizer trace: example
join_optimization / plan refinement
{ {
"attaching_conditions_to_tables": { "refine_plan": [
"original_condition": {
"((`t1`.`f1` = 1) and (`t2`.`f2` = 1))", "table": "`t1`"
"attached_conditions_summary": [ { },
"table": "`t1`", "attached": null {
}, { "table": "`t2`",
"table": "`t2`", "attached": "(`t2`.`f2` = 1)" "access_type": "table_scan"
} }
] /* attached_conditions_summary */ ] /* refine_plan */
} /* attaching_conditions_to_tables */ }
},
12 Copyright © 2012, Oracle and/or its affiliates. All rights reserved. Insert Information Protection Policy Classification from Slide 12](https://image.slidesharecdn.com/powerfulexplainmysql56-130322100527-phpapp02/85/Powerful-Explain-in-MySQL-5-6-12-320.jpg)

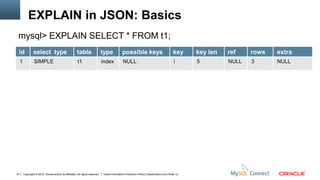
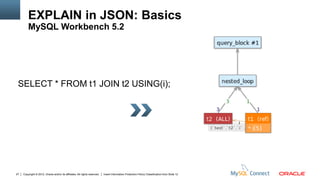
![EXPLAIN in JSON: Basics
mysql> set end_markers_in_json = on;
end_markers_in_json = off end_markers_in_json = on
} } /* table */
} } /* query_block */
} }
] ] /* query_specifications */
} } /* union_result */
} } /* query_block */
} } /* materialized_from_subquery */
} } /* table */
} } /* grouping_operation */
} } /* ordering_operation */
} } /* query_block */
20 Copyright © 2012, Oracle and/or its affiliates. All rights reserved. Insert Information Protection Policy Classification from Slide 12](https://image.slidesharecdn.com/powerfulexplainmysql56-130322100527-phpapp02/85/Powerful-Explain-in-MySQL-5-6-20-320.jpg)
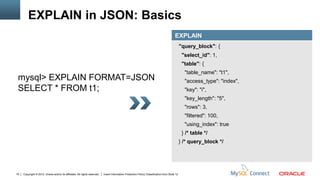
![EXPLAIN in JSON: Basics
EXPLAIN
"query_block": {
"select_id": 1,
"table": {
"table_name": "t1",
mysql> EXPLAIN FORMAT=JSON "access_type": "ref",
SELECT * FROM t1 WHERE str IS "possible_keys": [ "str“ ],
"key": "str", "key_length": "11",
NULL AND id > 0;
"ref": [ "const"],
"rows": 1, "filtered": 100,
"index_condition": "isnull(`test`.`t1`.`str`)“
"attached_condition": "(`test`.`t1`.`id` > 0)"
} /* table */
} /* query_block */
22 Copyright © 2012, Oracle and/or its affiliates. All rights reserved. Insert Information Protection Policy Classification from Slide 12](https://image.slidesharecdn.com/powerfulexplainmysql56-130322100527-phpapp02/85/Powerful-Explain-in-MySQL-5-6-22-320.jpg)
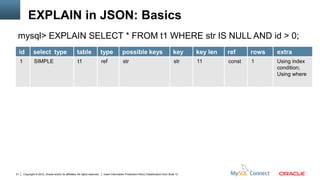
![EXPLAIN in JSON: Basics
EXPLAIN
"query_block": {
"select_id": 1,
"table": {
"table_name": "t1",
mysql> EXPLAIN FORMAT=JSON "partitions": [ "pNULL", "p0001-01-01",
SELECT * FROM t1 WHERE a "p1001-01-01"],
"access_type": "index",
BETWEEN '0000-00-00' AND '1001-
"possible_keys": [ "a" ],
01-01'; "key": "a", "key_length": "4",
"rows": 6, "filtered": 33.333,
"using_index": true,
"attached_condition": "(`test`.`t1`.`a` between
'0000-00-00' and '1001-01-01')"
}}
24 Copyright © 2012, Oracle and/or its affiliates. All rights reserved. Insert Information Protection Policy Classification from Slide 12](https://image.slidesharecdn.com/powerfulexplainmysql56-130322100527-phpapp02/85/Powerful-Explain-in-MySQL-5-6-24-320.jpg)
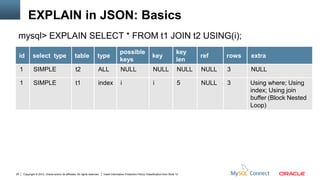
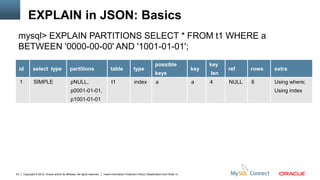
![EXPLAIN in JSON: Basics
EXPLAIN
{ {
"query_block": { "table": {
"select_id": 1, "table_name": "t1",
"nested_loop": [ "access_type": "index",
{ "possible_keys": [ "i" ],
"table": { "key": "i", "key_length": "5",
"table_name": "t2", "rows": 3, "filtered": 100,
"access_type": "ALL", "using_index": true,
"rows": 3, "using_join_buffer": "Block Nested Loop",
"filtered": 100 "attached_condition":
} /* table */ "(`test`.`t1`.`i` = `test`.`t2`.`i`)"
}, } /* table */
… next table … => }
] } /* nested_loop */ } /* query_block */
26 Copyright © 2012, Oracle and/or its affiliates. All rights reserved. Insert Information Protection Policy Classification from Slide 12](https://image.slidesharecdn.com/powerfulexplainmysql56-130322100527-phpapp02/85/Powerful-Explain-in-MySQL-5-6-26-320.jpg)
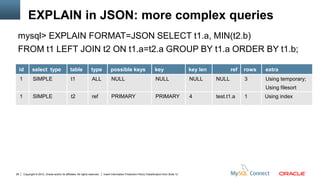
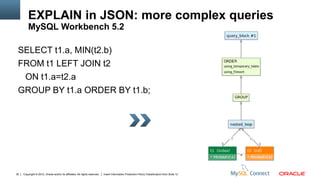
![EXPLAIN in JSON: more complex queries
EXPLAIN
"query_block": {
mysql> EXPLAIN FORMAT=JSON "select_id": 1,
SELECT t1.a, MIN(t2.b) "ordering_operation": {
"using_temporary_table": true,
FROM t1 LEFT JOIN t2 "using_filesort": true,
"grouping_operation": {
ON t1.a=t2.a
"using_filesort": true,
GROUP BY t1.a ORDER BY t1.b; "nested_loop": [
{ “table” : {…} },
{ “table” : {…} } ] /* nested_loop */
} /* grouping_operation */
} /* ordering_operation */
} /* query_block */
29 Copyright © 2012, Oracle and/or its affiliates. All rights reserved. Insert Information Protection Policy Classification from Slide 12](https://image.slidesharecdn.com/powerfulexplainmysql56-130322100527-phpapp02/85/Powerful-Explain-in-MySQL-5-6-29-320.jpg)
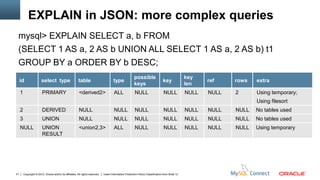
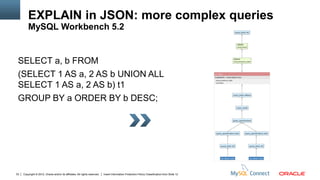
![EXPLAIN in JSON: more complex queries
EXPLAIN
"query_block": { "union_result": {
"ordering_operation": { "using_temporary_table": true,
"using_filesort": true, "table_name": "<union2,3>",
"grouping_operation": { "query_specifications": [ {
"using_temporary_table": true, "query_block": {
"using_filesort": false, "table": {
"table": { "message": "No tables used"
"table_name": "t1", } } }, {
"materialized_from_subquery": { "query_block": {
"using_temporary_table": true, "table": {
"query_block": { "message": "No tables used"
… here goes union_result… => } } } ] } /* union_result */
}}}}}}
32 Copyright © 2012, Oracle and/or its affiliates. All rights reserved. Insert Information Protection Policy Classification from Slide 12](https://image.slidesharecdn.com/powerfulexplainmysql56-130322100527-phpapp02/85/Powerful-Explain-in-MySQL-5-6-32-320.jpg)
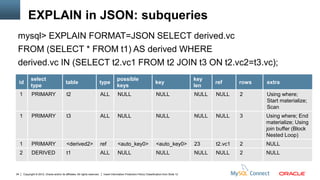
![EXPLAIN in JSON: subqueries
EXPLAIN
"query_block": { "table": {
"select_id": 1, "table_name": "derived",
"nested_loop": [ "materialized_from_subquery": {
{ "table": { "using_temporary_table": true,
"table_name": "<subquery3>", "query_block": {
"materialized_from_subquery": { "select_id": 2,
"query_block": { "table": {
"nested_loop": [ "table_name": "t1“,
{ "table": { "table_name": "t2“ } }, …
{ "table": { "table_name": "t3“ } } }
] } /* query_block */ } } /* table */ } /* query_block */
}, { … next table goes here … => } } /* materialized_from_subquery */
] /* nested_loop */ } /* query_block */ } /* table */
35 Copyright © 2012, Oracle and/or its affiliates. All rights reserved. Insert Information Protection Policy Classification from Slide 12](https://image.slidesharecdn.com/powerfulexplainmysql56-130322100527-phpapp02/85/Powerful-Explain-in-MySQL-5-6-35-320.jpg)
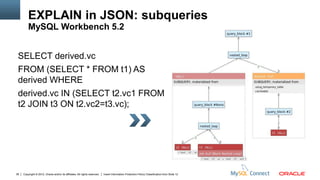
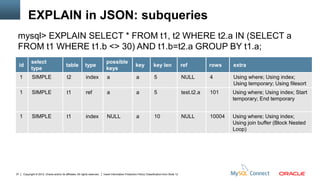
![EXPLAIN in JSON: subqueries
EXPLAIN
"query_block": { {
"select_id": 1, "duplicates_removal": {
"grouping_operation": { "using_temporary_table": true,
"using_temporary_table": true, "table": {
"nested_loop": [ "table_name": "t1",
{ "attached_condition": "(`test`.`t1`.`b` <> 30)"
"table": { } /* table */
"table_name": "t2", } /* duplicates_removal */
"attached_condition": "(`test`.`t2`.`a` is not null)" }, {
} /* table */ "table": {
}, "table_name": "t1",
… next 2 tables => … "attached_condition": "(`test`.`t1`.`b` = `test`.`t2`.`a`)"
] /* nested_loop */ } /* grouping_operation */ } /* table */
} /* query_block */ }
38 Copyright © 2012, Oracle and/or its affiliates. All rights reserved. Insert Information Protection Policy Classification from Slide 12](https://image.slidesharecdn.com/powerfulexplainmysql56-130322100527-phpapp02/85/Powerful-Explain-in-MySQL-5-6-38-320.jpg)
![EXPLAIN in JSON: subqueries
EXPLAIN
"query_block": { "query_block": {
"select_id": 1, "select_id": 1,
"nested_loop": [ "nested_loop": [
{ {
"table": { "table": {
"table_name": "t2", "table_name": "t1",
} /* table */ "access_type": "range", "loosescan": true,
}, { } /* table */
"table": { }, {
"table_name": "t1", "table": {
"first_match": "t2", "table_name": "t2",
"attached_condition": "(`test`.`t1`.`b` <> 30)" } /* table */
} /* table */ }
} ] /* nested_loop */ } /* query_block */ ] /* nested_loop */ } /* query_block */
40 Copyright © 2012, Oracle and/or its affiliates. All rights reserved. Insert Information Protection Policy Classification from Slide 12](https://image.slidesharecdn.com/powerfulexplainmysql56-130322100527-phpapp02/85/Powerful-Explain-in-MySQL-5-6-40-320.jpg)

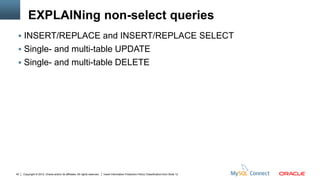
![EXPLAINing non-select queries
EXPLAIN
"query_block": {
"select_id": 1,
"table": {
"update": true,
mysql> EXPLAIN FORMAT=JSON "table_name": "t1",
"access_type": "range",
UPDATE t1 SET a = 10 WHERE
"possible_keys": [ "a", "a_2" ],
a < 10; "key": "a", "key_length": "5",
"rows": 2, "filtered": 100,
"using_temporary_table": "for update",
"attached_condition": "(`test`.`t1`.`a` < 10)"
} /* table */
} /* query_block */
44 Copyright © 2012, Oracle and/or its affiliates. All rights reserved. Insert Information Protection Policy Classification from Slide 12](https://image.slidesharecdn.com/powerfulexplainmysql56-130322100527-phpapp02/85/Powerful-Explain-in-MySQL-5-6-44-320.jpg)
![EXPLAINing non-select queries
EXPLAIN
"query_block": {
"select_id": 1,
"table": {
"delete": true,
mysql> EXPLAIN FORMAT=JSON "table_name": "t1",
"access_type": "range",
DELETE FROM t1 WHERE a < 10;
"possible_keys": [ "a", "a_2“ ],
"key": "a", "key_length": "5",
"rows": 2, "filtered": 100,
"attached_condition": "(`test`.`t1`.`a` < 10)"
} /* table */
} /* query_block */
45 Copyright © 2012, Oracle and/or its affiliates. All rights reserved. Insert Information Protection Policy Classification from Slide 12](https://image.slidesharecdn.com/powerfulexplainmysql56-130322100527-phpapp02/85/Powerful-Explain-in-MySQL-5-6-45-320.jpg)
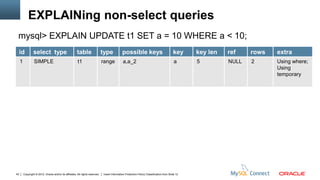
![EXPLAINing non-select queries
EXPLAIN
"query_block": { {
"select_id": 1, "table": {
"nested_loop": [ { "table_name": "t12",
"table": { "access_type": "ALL",
"update": true, "rows": 3, "filtered": 100,
"table_name": "t11", "using_join_buffer": "Block Nested Loop",
"access_type": "ref", "materialized_from_subquery": {
"possible_keys": [ "a", "a_2“ ], "using_temporary_table": true,
"key": "a", "key_length": "5", "query_block": {
"ref": ["const"] /* ref */, "select_id": 2,
"rows": 1, "filtered": 100 "table": { … } /* table */
} /* table */ }, } /* query_block */
… here goes 2nd table…=> } /* materialized_from_subquery */
] /* nested_loop */ } /* query_block */ } /* table */ }
47 Copyright © 2012, Oracle and/or its affiliates. All rights reserved. Insert Information Protection Policy Classification from Slide 12](https://image.slidesharecdn.com/powerfulexplainmysql56-130322100527-phpapp02/85/Powerful-Explain-in-MySQL-5-6-47-320.jpg)
![EXPLAINing non-select queries
EXPLAIN
"query_block": { [{
"select_id": 1, "dependent": true, "cacheable": false,
"table": { "query_block": {
"update": true, "select_id": 2,
"table_name": "t1", "table": {
"possible_keys": [ "a", "a_2“ ], "table_name": "t2",
"attached_condition": "access_type": "ALL",
"<in_optimizer>(`test`.`t1`.`a`, "rows": 3, "filtered": 100,
<exists>(select 1 from `test`.`t2` where "attached_condition":
(<cache>(`test`.`t1`.`a`) = "(<cache>(`test`.`t1`.`a`) = `test`.`t2`.`b`)"
`test`.`t1`.`a`)))", } /* table */
"attached_subqueries": [ … => …] } /* query_block */
} /* table */ }]
} /* query_block */
49 Copyright © 2012, Oracle and/or its affiliates. All rights reserved. Insert Information Protection Policy Classification from Slide 12](https://image.slidesharecdn.com/powerfulexplainmysql56-130322100527-phpapp02/85/Powerful-Explain-in-MySQL-5-6-49-320.jpg)
