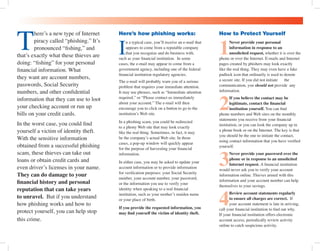
Phishing is a form of internet piracy where thieves attempt to acquire personal financial information through deceptive emails that appear legitimate. To protect yourself, never provide personal information in response to unsolicited requests and verify any communication directly with your financial institution. If you become a victim of phishing, immediately contact your financial institution and consider placing a fraud alert on your credit files.