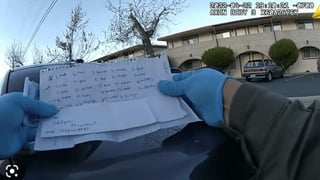
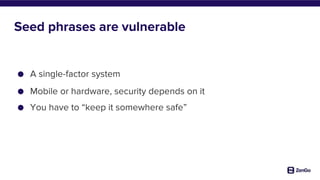
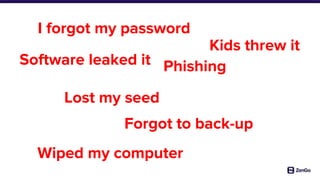
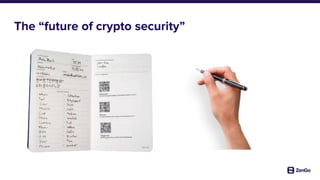
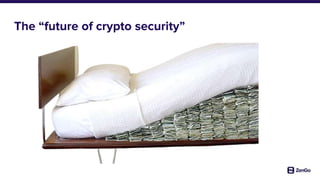
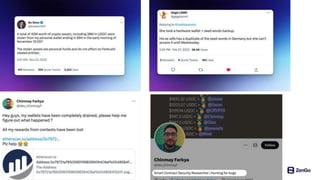
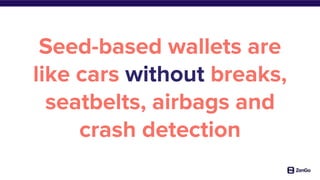
The document discusses the vulnerabilities of seed phrases in cryptocurrency wallet security, emphasizing that they can give a false sense of security and are prone to human error and external threats. It outlines the potential future of crypto security through multi-factor authentication, keyless systems, and advanced user protections. The author advocates for improved security measures to reduce the billions lost in theft and accidents related to seed-based wallets.