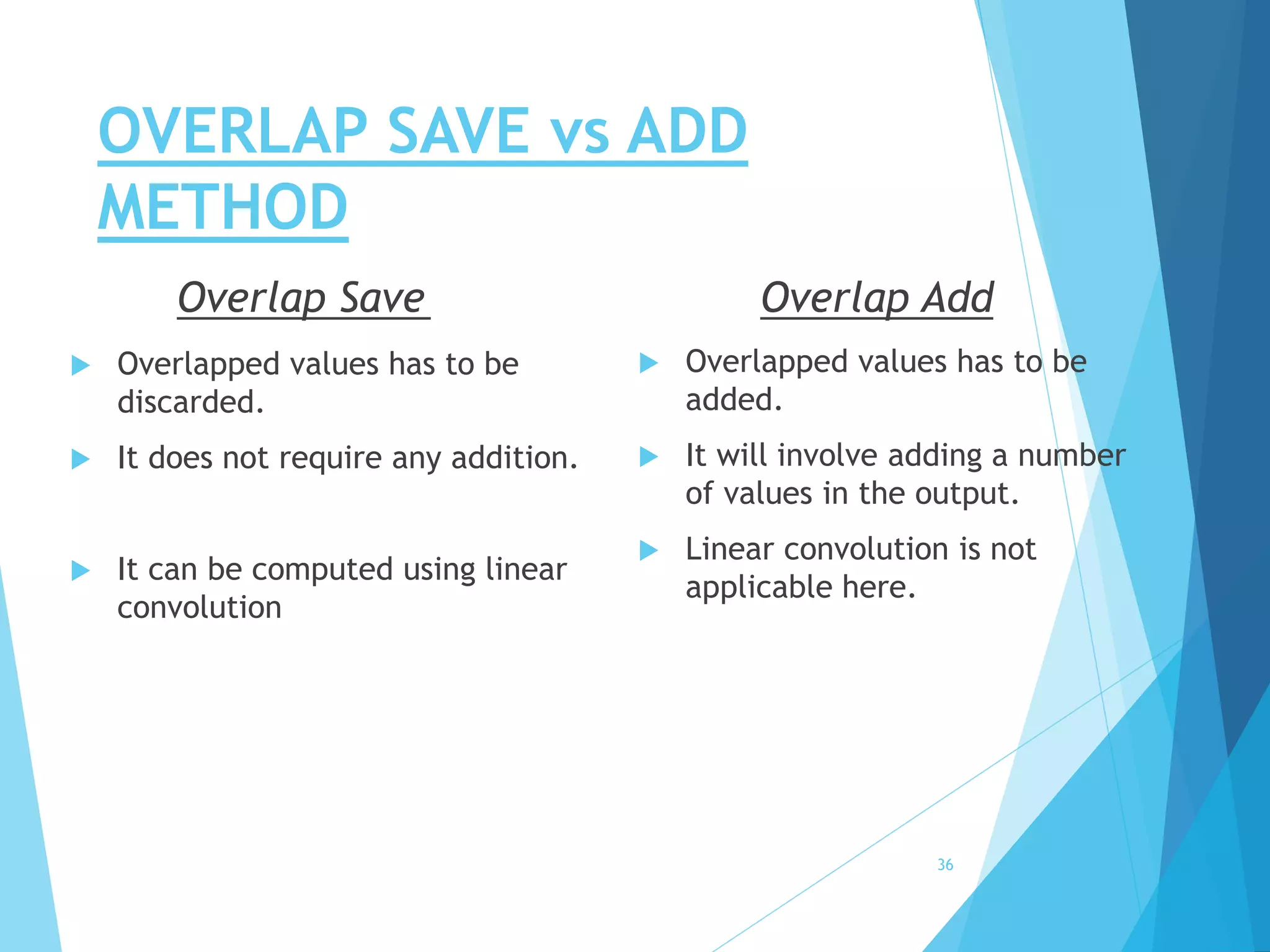
The document provides an overview of the overlap save and overlap add methods used in digital signal processing for filtering long data sequences. It outlines the steps for implementing each method, including examples, and discusses the differences between the two techniques. Both methods are explained in relation to their operations on blocks of data and their applicability, concluding that the choice between methods can be based on specific needs.
![OVERLAP SAVE METHOD
STEP-1:
Determine length ‘M’, which is the length of the impulse
response data sequences i.e. h[n] & determine ‘M-1’.
STEP-2:
Given input sequence x[n] size of DFT is ‘N’.
let assume, N=5
6](https://image.slidesharecdn.com/overlapaddoverlapsavedigitalsignalprocessing-180616102156/75/Overlap-Add-Overlap-Save-digital-signal-processing-6-2048.jpg)
![OVERLAP SAVE METHOD
STEP-3:
Determine the length of the new data, ‘L’
=> N=(L+M-1)
STEP-4:
Pad ‘L-1’ zeros to h[n]
7](https://image.slidesharecdn.com/overlapaddoverlapsavedigitalsignalprocessing-180616102156/75/Overlap-Add-Overlap-Save-digital-signal-processing-7-2048.jpg)
![OVERLAP SAVE METHOD
STEP-3:
Determine the length of the blocks, ‘L’
STEP-4:
Pad ‘L-1’ zeros to h[n]
8
h[n] ‘L-1’ zeros (padded)](https://image.slidesharecdn.com/overlapaddoverlapsavedigitalsignalprocessing-180616102156/75/Overlap-Add-Overlap-Save-digital-signal-processing-8-2048.jpg)
![OVERLAP SAVE METHOD
Input Data Sequence x[n]
9
x1[n]
x2[n]
x4[n]
x3[n]
M-1 zeros
M-1 data
M-1 data
M-1 data
L L LL](https://image.slidesharecdn.com/overlapaddoverlapsavedigitalsignalprocessing-180616102156/75/Overlap-Add-Overlap-Save-digital-signal-processing-9-2048.jpg)
![OVERLAP SAVE METHOD
STEP-4:
Perform Circular Convolution of h[n] & blocks of x[n]
i.e. y1[n]= x1[n] h[n]
y2[n]= x2[n] h[n]
y3[n]= x3[n] h[n]
y4[n]= x4[n] h[n]
10
N
N
N
N](https://image.slidesharecdn.com/overlapaddoverlapsavedigitalsignalprocessing-180616102156/75/Overlap-Add-Overlap-Save-digital-signal-processing-10-2048.jpg)
![OVERLAP SAVE METHOD
11
y1[n]
y2[n]
y4[n]
y3[n]
M-1 data
M-1 data
M-1 data
M-1 data
X
X
X
X
X=> discard](https://image.slidesharecdn.com/overlapaddoverlapsavedigitalsignalprocessing-180616102156/75/Overlap-Add-Overlap-Save-digital-signal-processing-11-2048.jpg)
![OVERLAP SAVE METHOD
12
y1[n]
y2[n]
y4[n]
y3[n]
M-1 data
M-1 data
M-1 data
Final Output Data Sequence y[n]
M-1 data
X
X
X
X
X=> discard](https://image.slidesharecdn.com/overlapaddoverlapsavedigitalsignalprocessing-180616102156/75/Overlap-Add-Overlap-Save-digital-signal-processing-12-2048.jpg)
![OVERLAP SAVE EXAMPLE
Ques. Given x[n]={3,-1,0,1,3,2,0,1,2,1} & h[n]={1,1,1}
Let, N=5
Length of h[n], M= 3
Therefore, M-1= 2
We know,
N=(L+M-1)
5=L+3-1
L=3
∴Pad L-1=2 zeros with h[n] i.e. h[n]={1,1,1,0,0}
13](https://image.slidesharecdn.com/overlapaddoverlapsavedigitalsignalprocessing-180616102156/75/Overlap-Add-Overlap-Save-digital-signal-processing-13-2048.jpg)
![OVERLAP SAVE EXAMPLE
3 -1 0 1 3 2 0 1 2 1
14
0 0 3 -1 0
-1 0 1 3 2
3 2 0 1 2
1 2 1 0 0
x1[n]
x2[n]
x4[n]
x3[n]
M-1(=2) no. of previous data
L(=3) no. of new data](https://image.slidesharecdn.com/overlapaddoverlapsavedigitalsignalprocessing-180616102156/75/Overlap-Add-Overlap-Save-digital-signal-processing-14-2048.jpg)
![OVERLAP SAVE EXAMPLE
Performing yk[n]= xk[n] h[n], where k=1,2,3,4
1. y1[n]= {-1,0,3,2,2}
2. y2[n]= {4,1,0,4,6}
3. y3[n]= {6,7,5,3,3}
4. y4[n]= {1,3,4,3,1}
15
N](https://image.slidesharecdn.com/overlapaddoverlapsavedigitalsignalprocessing-180616102156/75/Overlap-Add-Overlap-Save-digital-signal-processing-15-2048.jpg)
![OVERLAP SAVE EXAMPLE
-2 -1 0 1 2 3 4 5 6 7 8 9 10 11
16
3 2 2
0 4 6
5 3 3
4 3 1
-1 0
4 1
6 7
1 3
X=> discard
X
X
X
X
n-
y1[n]
y1[n]
y1[n]
y1[n]](https://image.slidesharecdn.com/overlapaddoverlapsavedigitalsignalprocessing-180616102156/75/Overlap-Add-Overlap-Save-digital-signal-processing-16-2048.jpg)
![OVERLAP SAVE EXAMPLE
-2 -1 0 1 2 3 4 5 6 7 8 9 10 11
17
3 2 2
0 4 6
5 3 3
4 3 1
-1 0
4 1
6 7
1 3
X=> discard
X
X
X
X
n-
y1[n]
y1[n]
y1[n]
y1[n]
y[n] 3 2 2](https://image.slidesharecdn.com/overlapaddoverlapsavedigitalsignalprocessing-180616102156/75/Overlap-Add-Overlap-Save-digital-signal-processing-17-2048.jpg)
![OVERLAP SAVE EXAMPLE
-2 -1 0 1 2 3 4 5 6 7 8 9 10 11
18
3 2 2
0 4 6
5 3 3
4 3 1
-1 0
4 1
6 7
1 3
X=> discard
X
X
X
X
n-
y1[n]
y1[n]
y1[n]
y1[n]
y[n] 3 2 2 0 4 6](https://image.slidesharecdn.com/overlapaddoverlapsavedigitalsignalprocessing-180616102156/75/Overlap-Add-Overlap-Save-digital-signal-processing-18-2048.jpg)
![OVERLAP SAVE EXAMPLE
-2 -1 0 1 2 3 4 5 6 7 8 9 10 11
19
3 2 2
0 4 6
5 3 3
4 3 1
-1 0
4 1
6 7
1 3
X=> discard
X
X
X
X
n-
y1[n]
y1[n]
y1[n]
y1[n]
y[n] 3 2 2 0 4 6 5 3 3](https://image.slidesharecdn.com/overlapaddoverlapsavedigitalsignalprocessing-180616102156/75/Overlap-Add-Overlap-Save-digital-signal-processing-19-2048.jpg)
![OVERLAP SAVE EXAMPLE
-2 -1 0 1 2 3 4 5 6 7 8 9 10 11
20
3 2 2
0 4 6
5 3 3
4 3 1
-1 0
4 1
6 7
1 3
X=> discard
X
X
X
X
n-
y1[n]
y1[n]
y1[n]
y1[n]
y[n] 3 2 2 0 4 6 5 3 3 4 3 1](https://image.slidesharecdn.com/overlapaddoverlapsavedigitalsignalprocessing-180616102156/75/Overlap-Add-Overlap-Save-digital-signal-processing-20-2048.jpg)
![OVERLAP ADD METHOD
STEP-1:
Determine length ‘M’, which is the length of the impulse
response data sequences i.e. h[n] & determine ‘M-1’.
STEP-2:
Given input sequence x[n] size of DFT is ‘N’.
let assume, N=5
22](https://image.slidesharecdn.com/overlapaddoverlapsavedigitalsignalprocessing-180616102156/75/Overlap-Add-Overlap-Save-digital-signal-processing-22-2048.jpg)
![OVERLAP ADD METHOD
STEP-3:
Determine the length of the new data, ‘L’
STEP-4:
Pad ‘M-1’ zeros to xk[n]
Pad ‘L-1’ zeros to h[n]
23
xk[n] ‘M-1’ zeros (padded)
h[n] ‘L-1’ zeros (padded)](https://image.slidesharecdn.com/overlapaddoverlapsavedigitalsignalprocessing-180616102156/75/Overlap-Add-Overlap-Save-digital-signal-processing-23-2048.jpg)
![OVERLAP ADD METHOD
Input Data Sequence x[n]
24
x1[n]
x2[n]
x4[n]
x3[n]
M-1 zeros
M-1 zeros
M-1 zeros
M-1 zeros
L L LL](https://image.slidesharecdn.com/overlapaddoverlapsavedigitalsignalprocessing-180616102156/75/Overlap-Add-Overlap-Save-digital-signal-processing-24-2048.jpg)
![OVERLAP ADD METHOD
STEP-4:
Perform Circular Convolution of h[n] & blocks of x[n]
i.e. y1[n]= x1[n] h[n]
y2[n]= x2[n] h[n]
y3[n]= x3[n] h[n]
y4[n]= x4[n] h[n]
25
N
N
N
N](https://image.slidesharecdn.com/overlapaddoverlapsavedigitalsignalprocessing-180616102156/75/Overlap-Add-Overlap-Save-digital-signal-processing-25-2048.jpg)
![OVERLAP ADD METHOD
26
y1[n]
y2[n]
y4[n]
y3[n]
M-1 data
M-1 data
M-1 data
Final Output Data Sequence y[n]
M-1 data
add
add
add](https://image.slidesharecdn.com/overlapaddoverlapsavedigitalsignalprocessing-180616102156/75/Overlap-Add-Overlap-Save-digital-signal-processing-26-2048.jpg)
![OVERLAP ADD EXAMPLE
Ques. Given x[n]={3,-1,0,1,3,2,0,1,2,1} & h[n]={1,1,1}
Let, N=5
Length of h[n], M= 3
Therefore, M-1= 2
We know,
N=(L+M-1)
5=L+3-1
L=3
∴Pad L-1=2 zeros with h[n] i.e. h[n]={1,1,1,0,0}
27](https://image.slidesharecdn.com/overlapaddoverlapsavedigitalsignalprocessing-180616102156/75/Overlap-Add-Overlap-Save-digital-signal-processing-27-2048.jpg)
![OVERLAP ADD EXAMPLE
3 -1 0 1 3 2 0 1 2 1
28
3 -1 0
1 3 2
0 1 2
1 0 0
x1[n]
x2[n]
x4[n]
x3[n]
M-1(=2) no. of zeros
L(=3) no. of new data
Input sequence x[n]
0 0
0 0
0 0
0 0](https://image.slidesharecdn.com/overlapaddoverlapsavedigitalsignalprocessing-180616102156/75/Overlap-Add-Overlap-Save-digital-signal-processing-28-2048.jpg)
![OVERLAP ADD EXAMPLE
Performing yk[n]= xk[n] h[n], where k=1,2,3,4
1. y1[n]= {3,2,2,-1,0}
2. y2[n]= {1,4,6,5,2}
3. y3[n]= {0,1,3,3,2}
4. y4[n]= {1,1,1,0,0}
29
N](https://image.slidesharecdn.com/overlapaddoverlapsavedigitalsignalprocessing-180616102156/75/Overlap-Add-Overlap-Save-digital-signal-processing-29-2048.jpg)
![OVERLAP ADD EXAMPLE
0 1 2 3 4 5 6 7 8 9 10 11 12 13
30
3 2 2
6 5 2
3 3 2
1 0 0
-1 0
1 4
0 1
1 1
+=> add
+
n-
y1[n]
y1[n]
y1[n]
y1[n]
+
++
++
3 2 2y[n]](https://image.slidesharecdn.com/overlapaddoverlapsavedigitalsignalprocessing-180616102156/75/Overlap-Add-Overlap-Save-digital-signal-processing-30-2048.jpg)
![OVERLAP ADD EXAMPLE
0 1 2 3 4 5 6 7 8 9 10 11 12 13
31
3 2 2
6 5 2
3 3 2
1 0 0
-1 0
1 4
0 1
1 1
+=> add
+
n-
y1[n]
y1[n]
y1[n]
y1[n]
+
++
++
3 2 2 0 4 6y[n]](https://image.slidesharecdn.com/overlapaddoverlapsavedigitalsignalprocessing-180616102156/75/Overlap-Add-Overlap-Save-digital-signal-processing-31-2048.jpg)
![OVERLAP ADD EXAMPLE
0 1 2 3 4 5 6 7 8 9 10 11 12 13
32
3 2 2
6 5 2
3 3 2
1 0 0
-1 0
1 4
0 1
1 1
+=> add
+
n-
y1[n]
y1[n]
y1[n]
y1[n]
+
++
++
3 2 2 0 4 6 5 3 3y[n]](https://image.slidesharecdn.com/overlapaddoverlapsavedigitalsignalprocessing-180616102156/75/Overlap-Add-Overlap-Save-digital-signal-processing-32-2048.jpg)
![OVERLAP ADD EXAMPLE
0 1 2 3 4 5 6 7 8 9 10 11 12 13
33
3 2 2
6 5 2
3 3 2
1 0 0
-1 0
1 4
0 1
1 1
+=> add
+
n-
y1[n]
y1[n]
y1[n]
y1[n]
+
++
++
3 2 2 0 4 6 5 3 3 4 3y[n]](https://image.slidesharecdn.com/overlapaddoverlapsavedigitalsignalprocessing-180616102156/75/Overlap-Add-Overlap-Save-digital-signal-processing-33-2048.jpg)
![OVERLAP ADD EXAMPLE
0 1 2 3 4 5 6 7 8 9 10 11 12 13
34
3 2 2
6 5 2
3 3 2
1 0 0
-1 0
1 4
0 1
1 1
+=> add
+
n-
y1[n]
y1[n]
y1[n]
y1[n]
+
++
++
3 2 2 0 4 6 5 3 3 4 3 1 0 0y[n]](https://image.slidesharecdn.com/overlapaddoverlapsavedigitalsignalprocessing-180616102156/75/Overlap-Add-Overlap-Save-digital-signal-processing-34-2048.jpg)
![OVERLAP ADD EXAMPLE
0 1 2 3 4 5 6 7 8 9 10 11 12 13
35
3 2 2
6 5 2
3 3 2
1 0 0
-1 0
1 4
0 1
1 1
+=> add
+
n-
y1[n]
y1[n]
y1[n]
y1[n]
+
++
++
3 2 2 0 4 6 5 3 3 4 3 1 0 0y[n]](https://image.slidesharecdn.com/overlapaddoverlapsavedigitalsignalprocessing-180616102156/75/Overlap-Add-Overlap-Save-digital-signal-processing-35-2048.jpg)