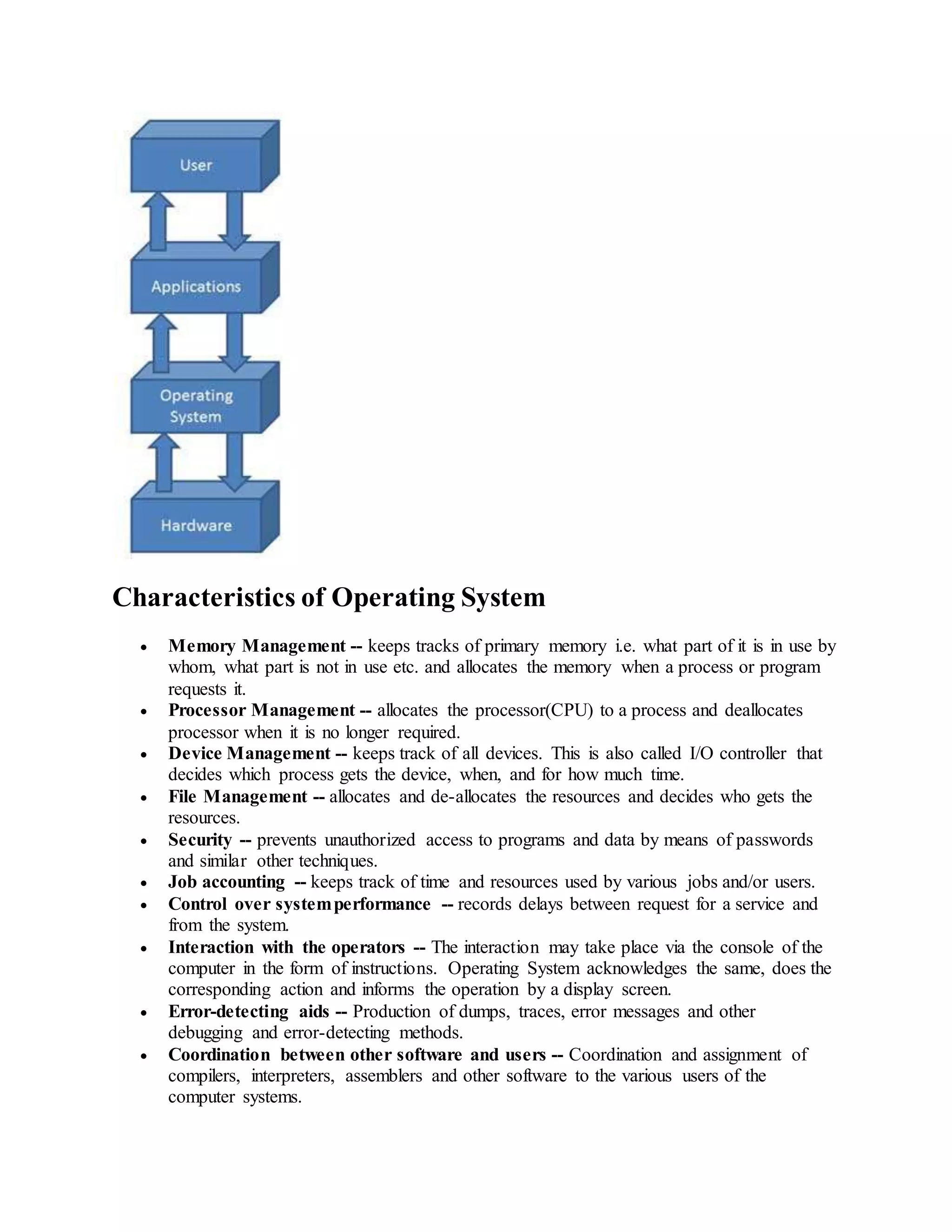
An operating system acts as an interface between computer hardware and software, managing computer resources and allowing users to run application programs. There are several types of operating systems including batch, time-sharing, distributed, network, and real-time systems. The five most common operating systems are Ubuntu, Android, Mac OS X, iOS, and Windows, each having their own unique features and compatibility with different hardware.