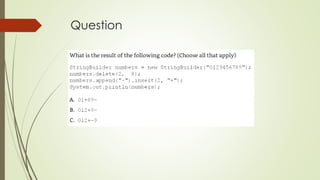
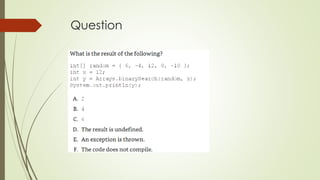
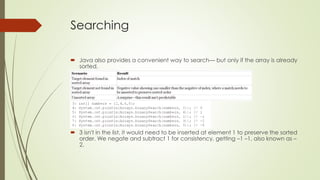
This document provides an overview of core Java APIs covered on the OCA exam, including Strings, StringBuilder, arrays, sorting, and searching. It discusses that Strings are immutable sequences of characters with useful methods like length(), charAt(), indexOf(), and substring(). StringBuilder is mutable and more efficient for string manipulation than concatenating Strings. Arrays are objects that hold primitives or references in indexed memory locations. The document covers creating, accessing, and searching arrays, as well as the Arrays utility class methods like sort().


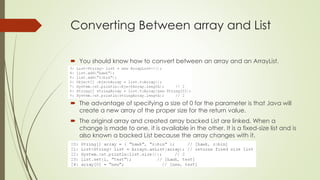
![Creating an Array of Primitives
int[] numbers1 = new int[ 3];](https://image.slidesharecdn.com/ocachapter3corejavaapis-151027194417-lva1-app6891/85/OCA-Java-SE-8-Exam-Chapter-3-Core-Java-APIs-22-320.jpg)
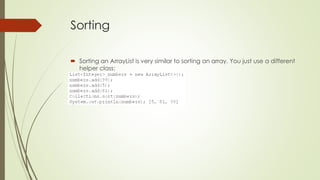
![Creating an Array of Primitives
All four of these statements do the exact same thing:
int[] ids, types; // two variables of type int[].
int ids[], types; // This time we get one variable of type int[] and one
variable of type int. Be careful on exam.](https://image.slidesharecdn.com/ocachapter3corejavaapis-151027194417-lva1-app6891/85/OCA-Java-SE-8-Exam-Chapter-3-Core-Java-APIs-23-320.jpg)
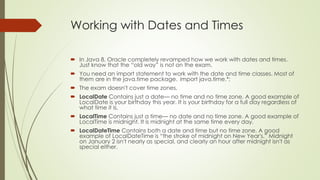
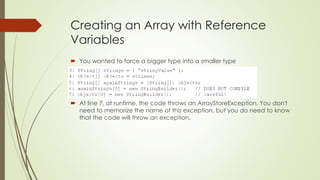
![Creating an Array with Reference
Variables
You can choose any Java type to be the type of the array.
We can call equals() because an array is an object. It returns true because
of reference equality.
int is a primitive; int[] is an object.
You don't have to know this for the exam, but [L means it is an array,
java.lang.String is the reference type, and 160bc7c0 is the hash code.
Note:Since Java 5, Java has provided a method that prints an array nicely:
java.util.Arrays.toString( bugs) would print [cricket, beetle, ladybug]. Not on
exam.](https://image.slidesharecdn.com/ocachapter3corejavaapis-151027194417-lva1-app6891/85/OCA-Java-SE-8-Exam-Chapter-3-Core-Java-APIs-24-320.jpg)
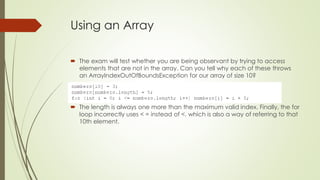

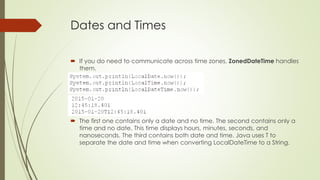
![Multidimensional Arrays
Arrays are objects, and of course array components can be objects.
String [][] rectangle = new String[ 3][ 2];](https://image.slidesharecdn.com/ocachapter3corejavaapis-151027194417-lva1-app6891/85/OCA-Java-SE-8-Exam-Chapter-3-Core-Java-APIs-29-320.jpg)
![Multidimensional Arrays
While that array happens to be rectangular in shape, an array doesn't
need to be. Consider this one:
int[][] differentSize = {{1, 4}, {3}, {9, 8, 7}};
Another way to create an asymmetric array is to initialize just an array's first
dimension, and define the size of each array component in a separate
statement:](https://image.slidesharecdn.com/ocachapter3corejavaapis-151027194417-lva1-app6891/85/OCA-Java-SE-8-Exam-Chapter-3-Core-Java-APIs-30-320.jpg)