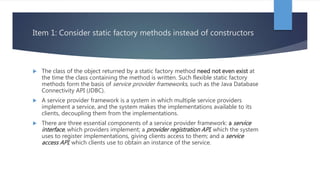
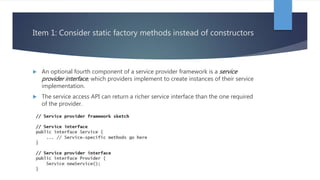
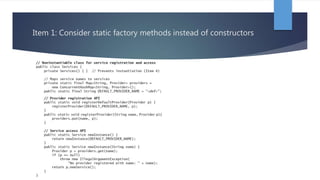
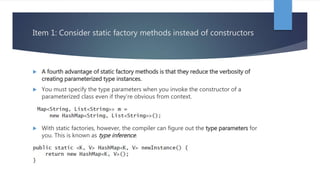
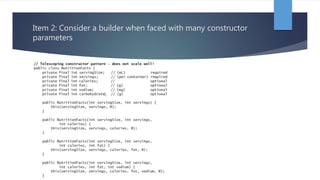
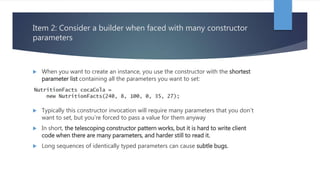
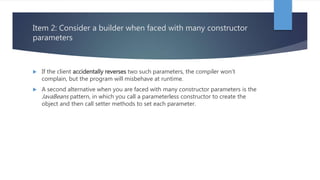
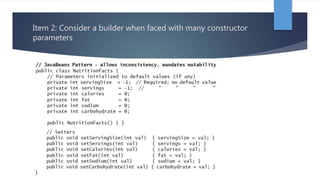
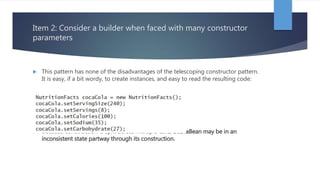
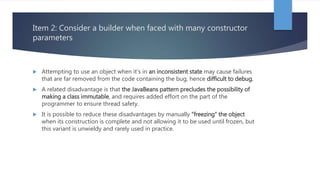
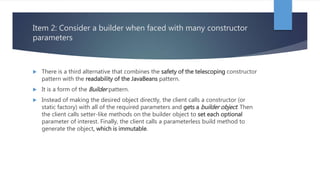
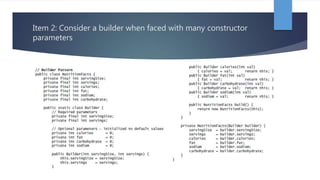
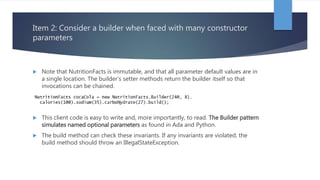
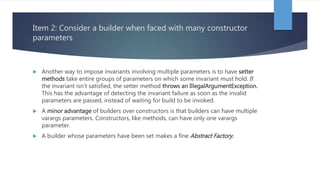
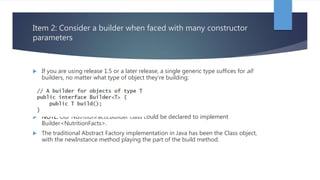
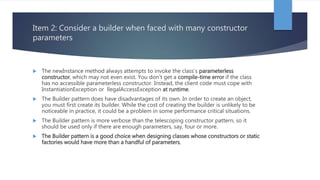
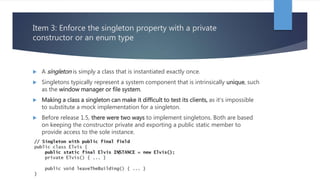
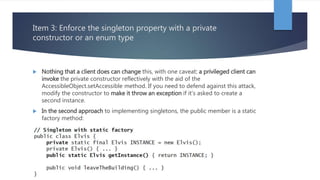
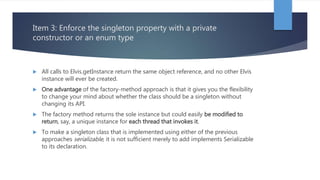
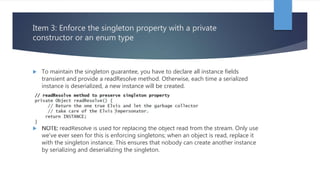
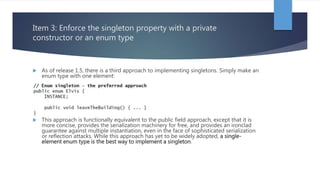
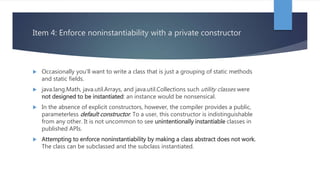
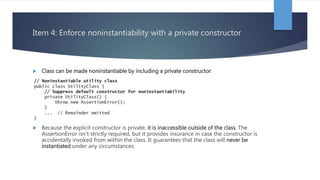
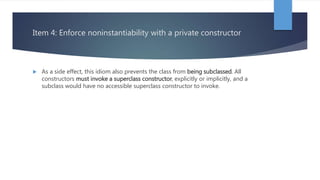
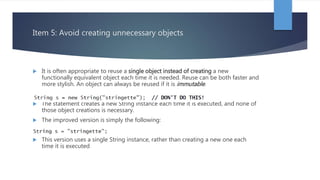
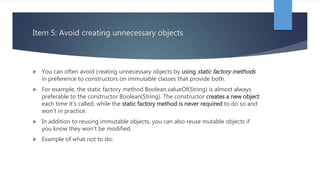
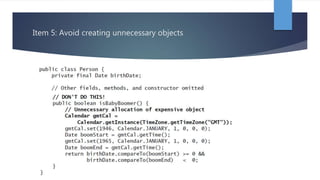
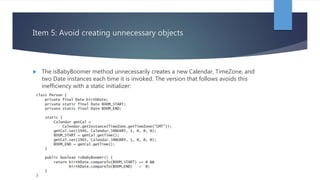
Chapter 2 of 'Effective Java' by Joshua Bloch discusses the creation and destruction of objects, emphasizing the use of static factory methods as an alternative to constructors, which offer advantages such as naming and instance control. It also suggests using the builder pattern for classes with multiple parameters and outlines how to properly implement singletons and noninstantiable classes. The chapter ultimately emphasizes efficient object management and the importance of readability and maintainability in code.