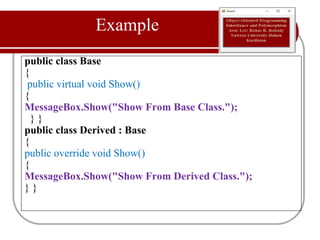
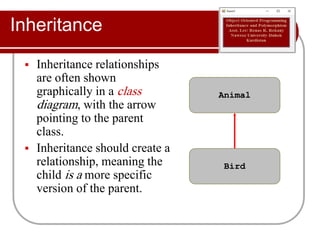
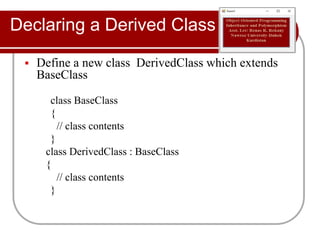
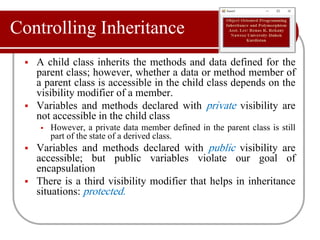
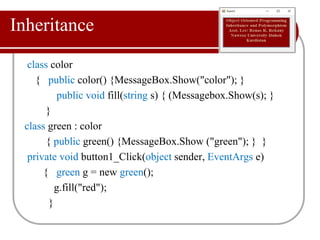
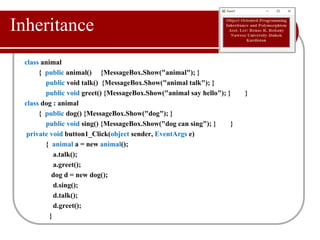
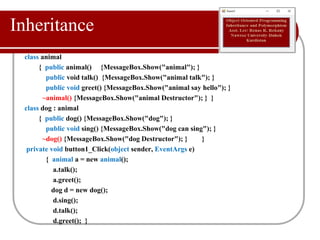
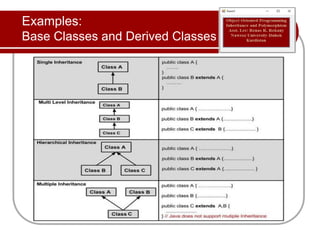
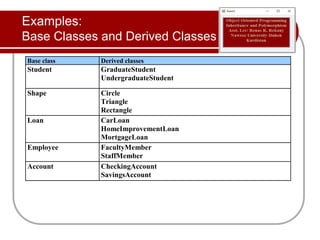
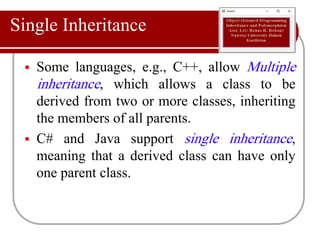
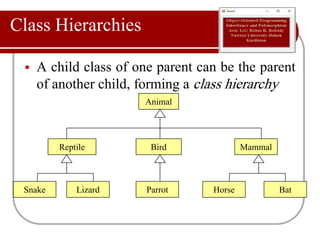
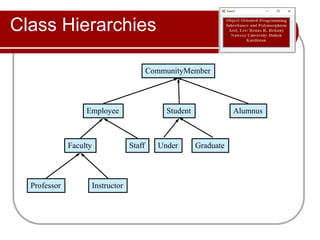
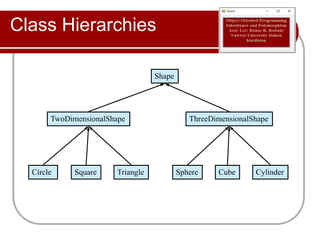
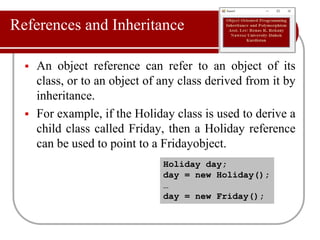
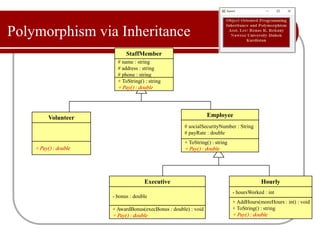
This document discusses inheritance and polymorphism in C#. It defines inheritance as allowing a derived class to inherit characteristics from a parent class. Methods and data from the parent class can be accessed differently depending on visibility modifiers like public, private, and protected. Inheritance allows class hierarchies to be formed. Polymorphism is enabled through inheritance and overriding methods in derived classes. Examples are provided to demonstrate inheritance, overriding methods, and class hierarchies.
![Overloading vs. Overriding
▪ Overloading deals with
multiple methods in the
same class with the same
name but different
signatures
▪ Overloading lets you
define a similar
operation in different
ways for different data
▪ Example:
▪ int foo(string[] bar);
▪ int foo(int bar1, float a);
▪ Overriding deals with two
methods, one in a parent
class and one in a child
class, that have the same
signature
▪ Overriding lets you define
a similar operation in
different ways for different
object types
▪ Example:
▪ class Base {
▪ public virtual int foo() {}
}
▪ class Derived {
▪ public override int foo()
{}}](https://image.slidesharecdn.com/objectorientedprogramminginheritance-171231213132/85/Object-oriented-programming-inheritance-24-320.jpg)