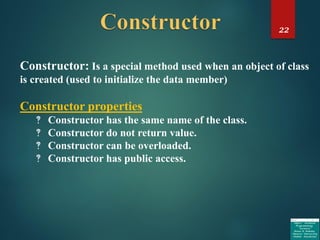
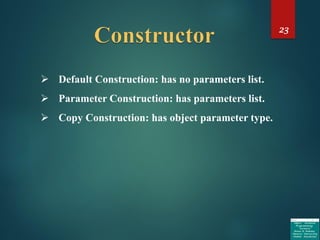
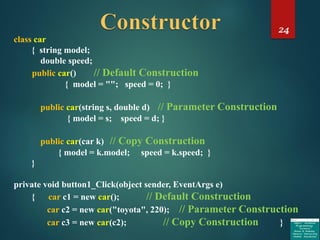
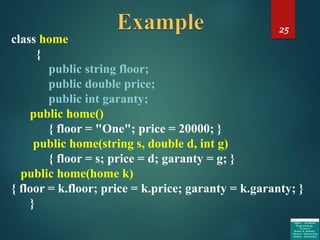
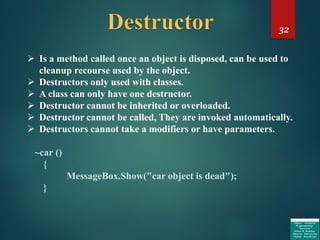
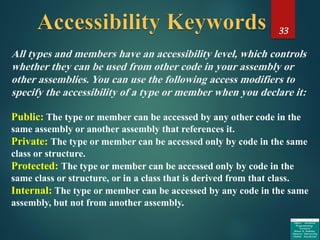
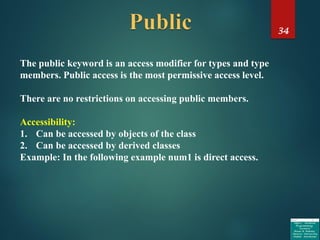
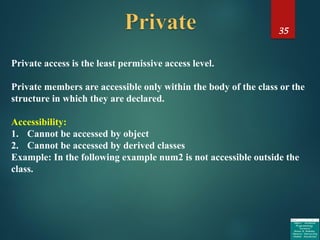
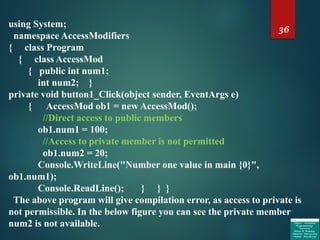
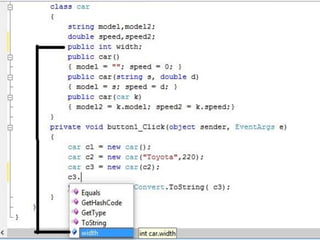
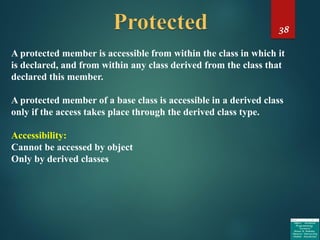
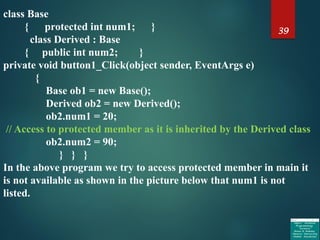
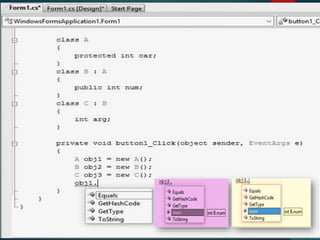
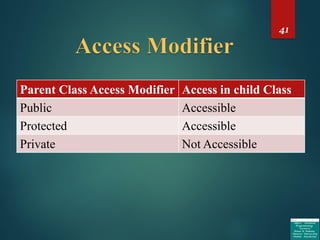
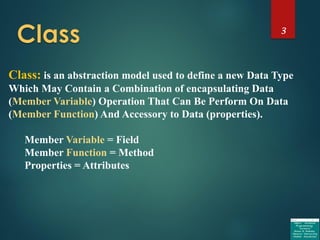
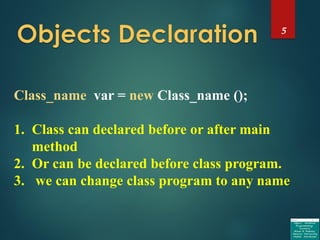
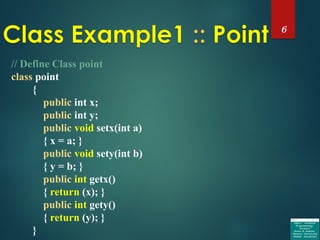
The document discusses object-oriented programming concepts in C#, including classes, constructors, destructors, and access modifiers. It provides examples of how to define classes with properties, methods, and constructors. It also explains the differences between public, private, and protected access modifiers and how they control accessibility of class members both within and outside of a class. The document contains code examples demonstrating the usage of classes, constructors, and access modifiers in C#.

![4
Class Class_name
{
[Properties] Member Variable;
[Properties] Member Function;
.
.
.
}](https://image.slidesharecdn.com/objectorientedprogramming-171231213000/85/Object-oriented-programming-4-320.jpg)
![13
// Class array Define and Sort // Passing array
class sort
{
int[] ar = new int[10];
public void set_array(int[] a)
{
ar = a;
}
public int[] get_array()
{
Array.Sort(ar); return ((ar));
}
}](https://image.slidesharecdn.com/objectorientedprogramming-171231213000/85/Object-oriented-programming-13-320.jpg)
![14
// Calling the Class
private void button1_Click(object sender, EventArgs e)
{
sort s = new sort();
int[] b = new int[10] { 9, 8, 7, 6, 5, 4, 3, 2, 1, 0 };
s.set_array(b);
b=s.get_array();
for (int i = 0; i < 10; i++)
{
textBox1.Text = textBox1.Text + b[i];
}
}](https://image.slidesharecdn.com/objectorientedprogramming-171231213000/85/Object-oriented-programming-14-320.jpg)
![16
public string str_dn(string a)
{
return (a.ToLower());
}
public string get_s;
public string set_s;
public void find_array(string[,] s)
{
for (int j = 0; j < 5; j++)
if (get_s == s[0, j])
{
set_s =s[0,j]+":"+s[1,j]+" = "+ s[2, j];
break;
}
}
}](https://image.slidesharecdn.com/objectorientedprogramming-171231213000/85/Object-oriented-programming-16-320.jpg)
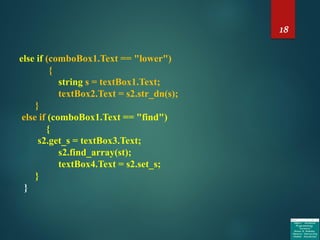
![17
private void button1_Click(object sender, EventArgs e)
{
string[,] st = new string[3, 5] { {ID},{NAME},{AVERAGE}};
stage2 s2 = new stage2();
if (comboBox1.Text == “round")
{
double x = Convert.ToDouble(textBox1.Text);
textBox2.Text = Convert.ToString(s2.rnd(x));
}
else if (comboBox1.Text == “floor")
{
double y = Convert.ToDouble(textBox1.Text);
textBox2.Text = Convert.ToString(s2.flor(y));
}
else if (comboBox1.Text == "upper")
{
string s = textBox1.Text;
textBox2.Text = s2.str_up(s);
}](https://image.slidesharecdn.com/objectorientedprogramming-171231213000/85/Object-oriented-programming-17-320.jpg)
![21
Homework :: ??? ???
1. Find summation in array[3,3] using class.
2. Print even numbers and odd numbers in array[3,3].
3. Find summation of even numbers and odd numbers
in array[3,3].
4. Exchange even numbers with odd numbers, keep
using same sequence.
5. Find power value of each elements of array[3,3].
6. Find factorial for each elements of array[10].
Hint: Use only one program to do the above questions.!!!](https://image.slidesharecdn.com/objectorientedprogramming-171231213000/85/Object-oriented-programming-21-320.jpg)