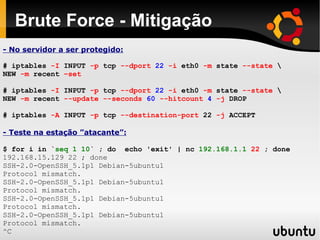
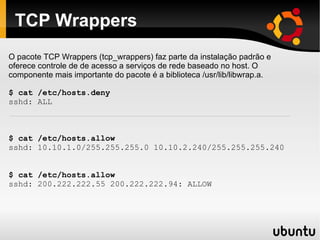
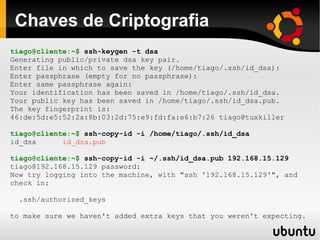
The document covers various topics related to remote access security, focusing on the use of SSH and vulnerabilities such as password sniffing and brute-force attacks. It discusses protective measures like firewalls, public/private key authentication, and securing SSH configurations. Additionally, it highlights advanced concepts like centralized public key management using LDAP and the potential dangers of denial-of-service attacks through fork bombs.

![SSH é sempre visado
...
Aug 31 23:21:28 localhost sshd[4560]: Illegal user admin from ::ffff:206.113.121.118
Aug 31 23:21:31 localhost sshd[4562]: Illegal user test from ::ffff:206.113.121.118
Aug 31 23:21:36 localhost sshd[4564]: Illegal user guest from ::ffff:206.113.121.118
Aug 31 23:21:39 localhost sshd[4566]: Illegal user webmaster from ::ffff:206.113.121.118
Aug 31 23:21:44 localhost sshd[4568]: Illegal user mysql from ::ffff:206.113.121.118
Aug 31 23:21:47 localhost sshd[4570]: Illegal user oracle from ::ffff:206.113.121.118
Aug 31 23:21:49 localhost sshd[4572]: Illegal user library from ::ffff:206.113.121.118
Aug 31 23:21:52 localhost sshd[4574]: Illegal user info from ::ffff:206.113.121.118
Aug 31 23:21:55 localhost sshd[4576]: Illegal user shell from ::ffff:206.113.121.118
Aug 31 23:21:59 localhost sshd[4578]: Illegal user linux from ::ffff:206.113.121.118
Aug 31 23:22:01 localhost sshd[4580]: Illegal user unix from ::ffff:206.113.121.118
Aug 31 23:22:05 localhost sshd[4582]: Illegal user webadmin from ::ffff:206.113.121.118
Aug 31 23:22:08 localhost sshd[4584]: Illegal user ftp from ::ffff:206.113.121.118
Aug 31 23:22:12 localhost sshd[4586]: Illegal user test from ::ffff:206.113.121.118
Aug 31 23:22:18 localhost sshd[4590]: Illegal user admin from ::ffff:206.113.121.118
Aug 31 23:22:21 localhost sshd[4592]: Illegal user guest from ::ffff:206.113.121.118
Aug 31 23:22:25 localhost sshd[4594]: Illegal user master from ::ffff:206.113.121.118
Aug 31 23:22:28 localhost sshd[4596]: Illegal user apache from ::ffff:206.113.121.118
Aug 31 23:22:33 localhost sshd[4598]: User root not allowed because not listed in AllowUsers
Aug 31 23:22:37 localhost sshd[4600]: User root not allowed because not listed in AllowUsers
...](https://image.slidesharecdn.com/segurancaacessoremotossh-090702220757-phpapp02/85/SSH-Seguranca-no-Acesso-Remoto-8-320.jpg)
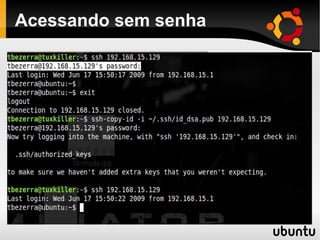
![Logs de acesso
# Log Antes:
Jun 17 15:06:15 ubuntu sshd[2938]:
Accepted password for tiago from
192.168.15.1 port 32813 ssh2
# Log Depois:
Jun 17 15:28:26 ubuntu sshd[3184]:
Accepted publickey for tiago from
192.168.15.1 port 60079 ssh2](https://image.slidesharecdn.com/segurancaacessoremotossh-090702220757-phpapp02/85/SSH-Seguranca-no-Acesso-Remoto-19-320.jpg)
![Busca no LDAP de exemplo
[root@testmachine ~]# ldapsearch -x uid=tcruz
# tcruz, People, empresa.com.br
dn: uid=tcruz,ou=People,dc=empresa,dc=com,dc=br
gecos: Tiago Cruz
loginShell: /bin/bash
objectClass: account
objectClass: posixAccount
objectClass: top
objectClass: shadowAccount
objectClass: ldapPublicKey
uid: tcruz
uidNumber: 1002
cn: tcruz
homeDirectory: /home/tcruz
SshPublicKey:: ssh-dss
c3NoLWRzcyBBQUFBQjNOemFDMWtjM01BQUFDQkFPTDF0alppRmdXdEdtMkJ2UWx
9DOHJKNVYwaE90R3J3QUFBSUJIZVlzWnJGR2xITG4xblVGUTBTSXB6bzlnNG90RmFje
gidNumber: 1010
shadowLastChange: 14196
# search result
search: 2
result: 0 Success](https://image.slidesharecdn.com/segurancaacessoremotossh-090702220757-phpapp02/85/SSH-Seguranca-no-Acesso-Remoto-23-320.jpg)
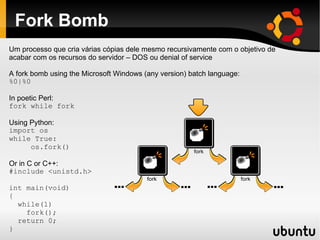
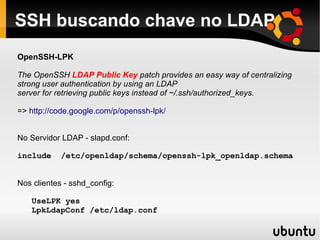
![Fork Bomb
tcruz@ubuntu:~$ ulimit -a | grep proce
max user processes (-u) unlimited
tcruz@ubuntu:~$ ulimit -u 1024
tcruz@ubuntu:~$ ulimit -a | grep proce
max user processes (-u) 1024
tcruz@ubuntu:~$ :(){ :|:& };:
[1] 3755
tcruz@ubuntu:~$ -bash: fork: Resource temporarily unavailable
-bash: fork: Resource temporarily unavailable
-bash: fork: Resource temporarily unavailable
-bash: fork: Resource temporarily unavailable
-bash: fork: Resource temporarily unavailable
-bash: fork: Resource temporarily unavailable
[1]+ Terminated : | :
Nota: Utilizado nesse teste uma VM com 512 GB de RAM](https://image.slidesharecdn.com/segurancaacessoremotossh-090702220757-phpapp02/85/SSH-Seguranca-no-Acesso-Remoto-26-320.jpg)