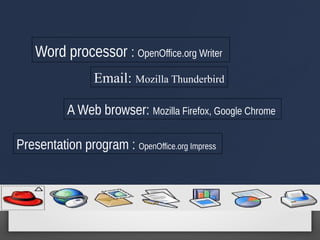
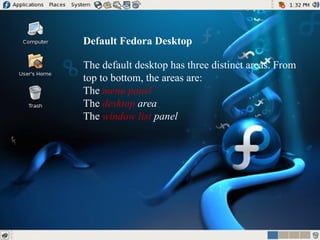
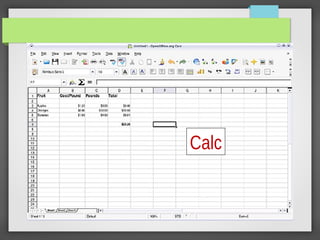
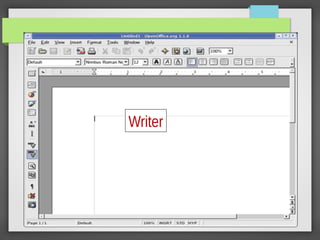
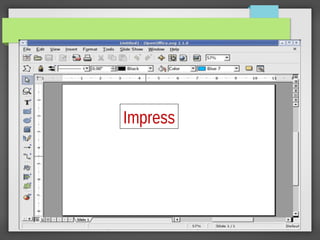
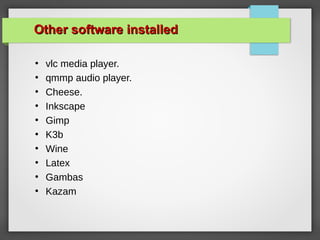
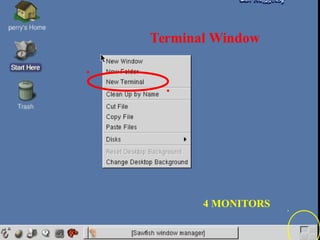
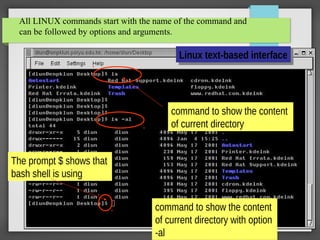
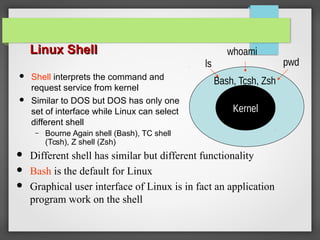
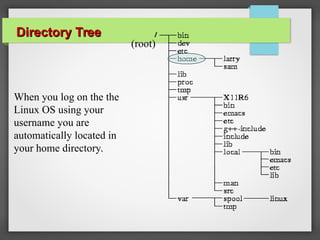
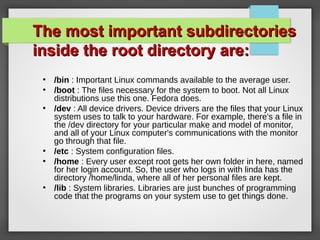
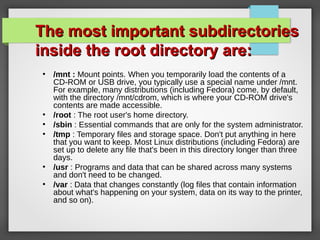
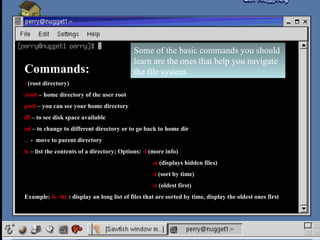
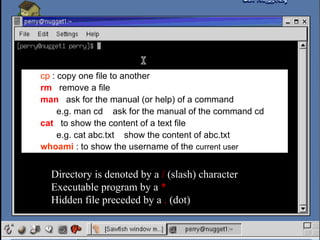
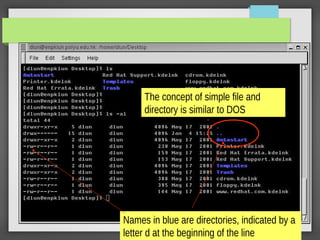
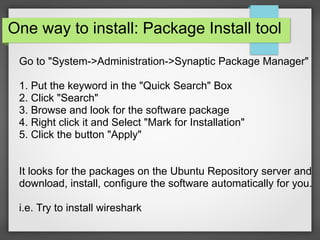
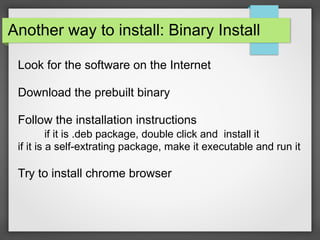
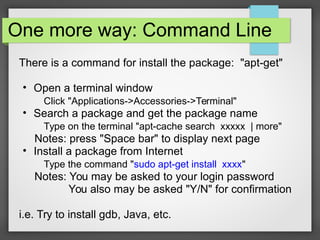
This document provides an overview of common Linux software and how to install additional software. It discusses the major desktop environments GNOME and KDE and default applications like Firefox, Thunderbird, and OpenOffice. It describes the file structure with directories like home, bin, etc. It also outlines several methods for installing software, including via package managers, downloading binaries or source code. The key difference between Linux and Windows is that Linux has a different file structure and installation process which can cause culture shock for new users.