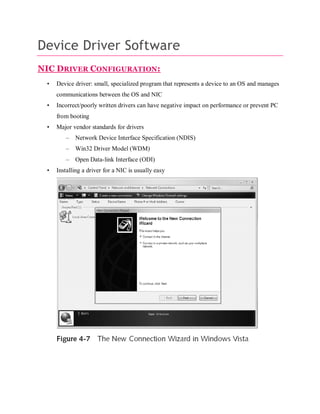
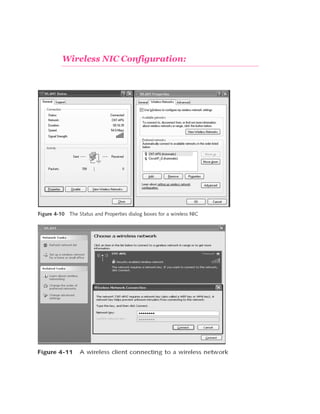
This document provides an overview of networking devices, focusing primarily on the network interface card (NIC) and its operations, configurations, and specialized types such as wireless adapters and remote boot adapters. It discusses various networking equipment including repeaters, bridges, routers, gateways, multiplexers, and switches, highlighting their roles and functionalities within data communication networks. Additionally, it addresses device driver software necessary for managing NIC communications and offers insights into troubleshooting and network management strategies.