Mobile telecommunication systems use cellular networks with multiple low-power base stations that divide coverage areas into cells. Each cell is served by a base station transmitting frequencies allocated to that cell. Neighboring cells use different frequencies to avoid interference. This allows frequency reuse for higher network capacity. Mobile devices connect to the nearest base station and can handover connections between base stations as they move between cells. The GSM system implements this cellular concept and provides voice calls, data services, and supplementary services through its radio subsystem, network switching subsystem, and operations subsystem.










![ behaving mobile
Congested network
Immediate service termination (IST)(E.g. Bills are not paid)
Load new parameters (Configuration has been changed and they should be taken into
use)
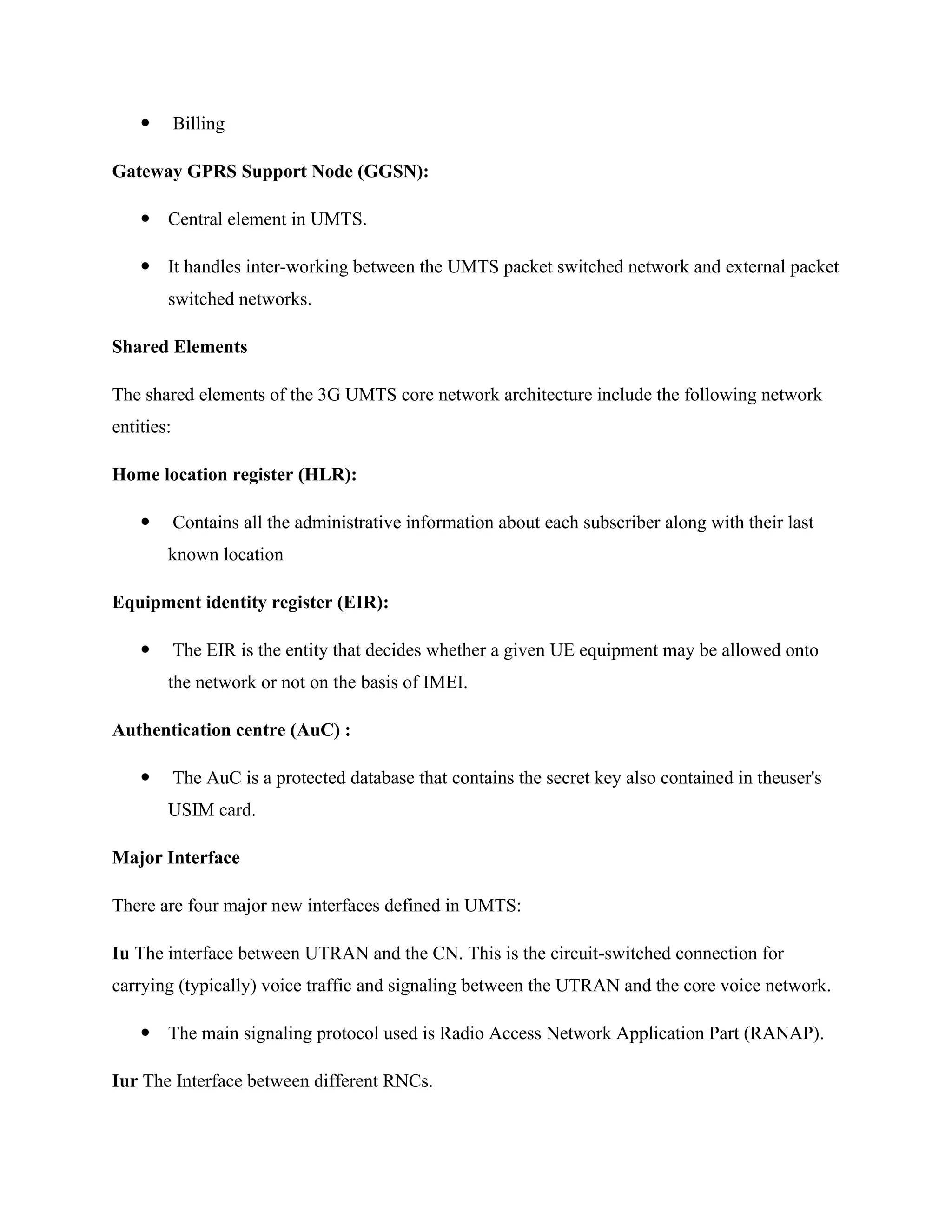
GPRS - PDP Context
PDP stands for Packet Data Protocol. The PDP addresses are network layer addresses
(Open Standards Interconnect [OSI] model Layer 3). GPRS systems support both X.25
and IP network layer protocols. Therefore, PDP addresses can be X.25, IP, or both.
Each PDP address is anchored at a Gateway GPRS Support Node (GGSN), as shown in
figure below. All packet data traffic sent from the public packet data network for the PDP
address goes through the gateway (GGSN).](https://image.slidesharecdn.com/mobiletelecommunicationsystem-converted-211110101011/75/Mobile-telecommunication-system-converted-20-2048.jpg)