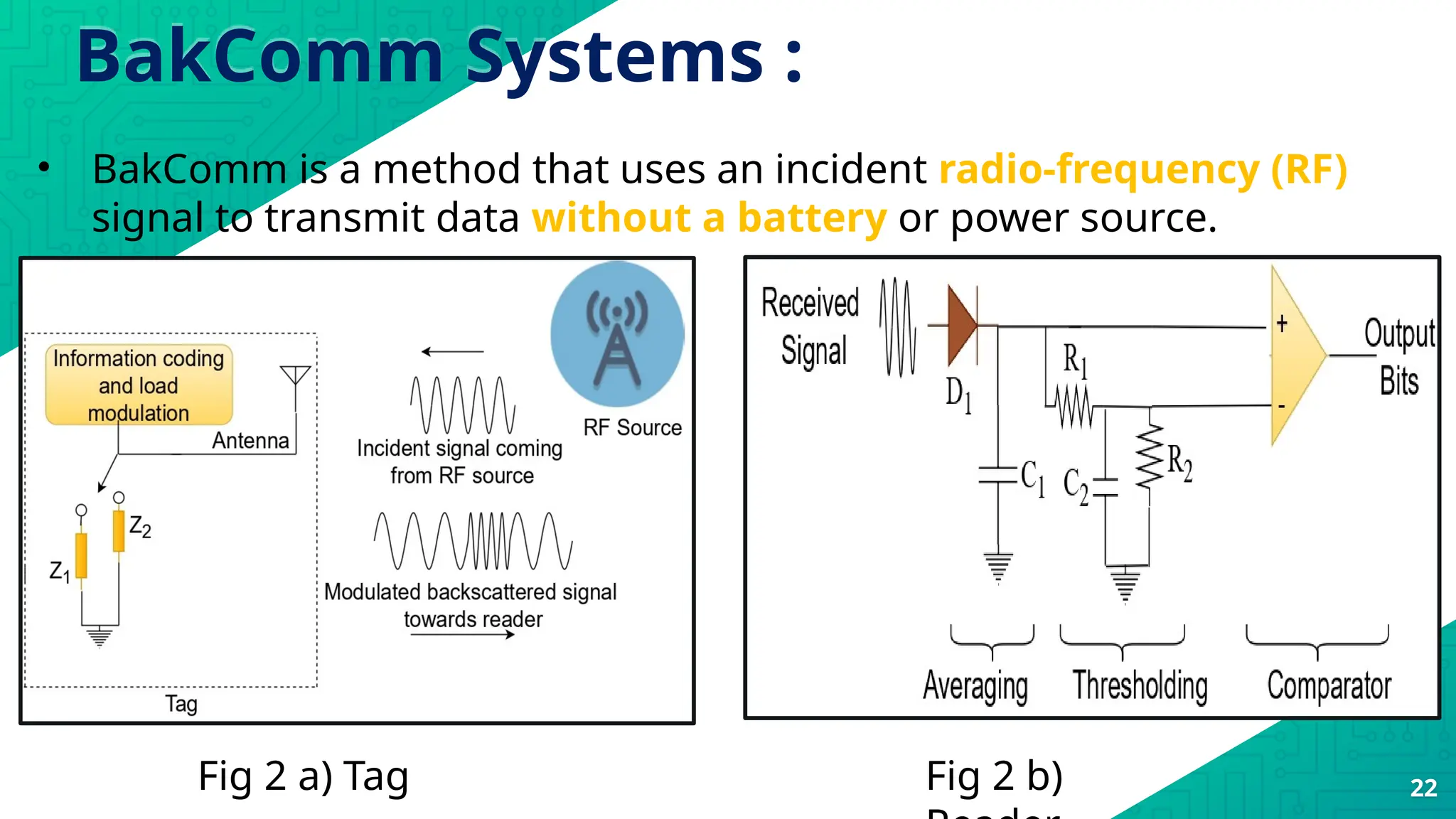
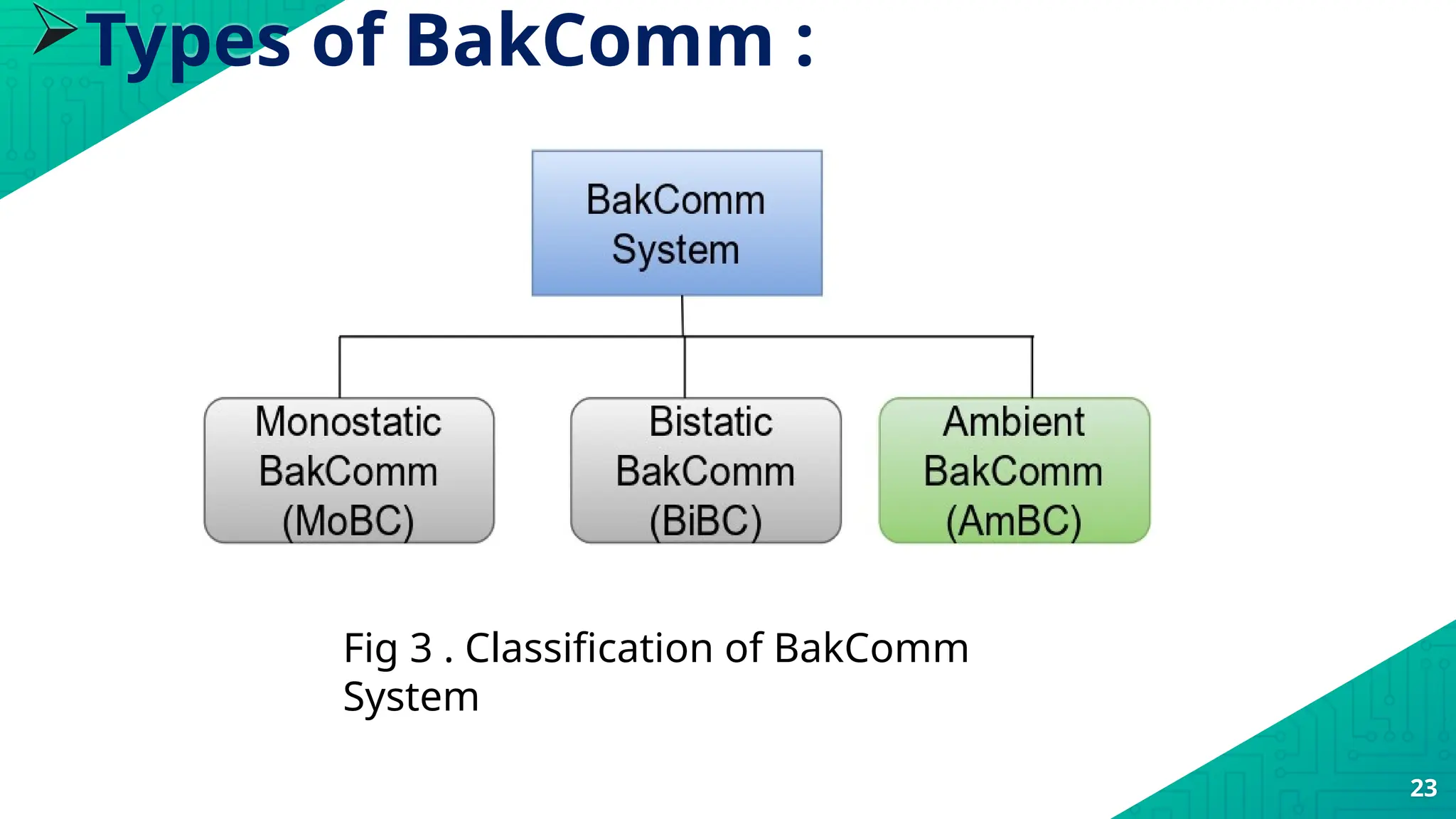
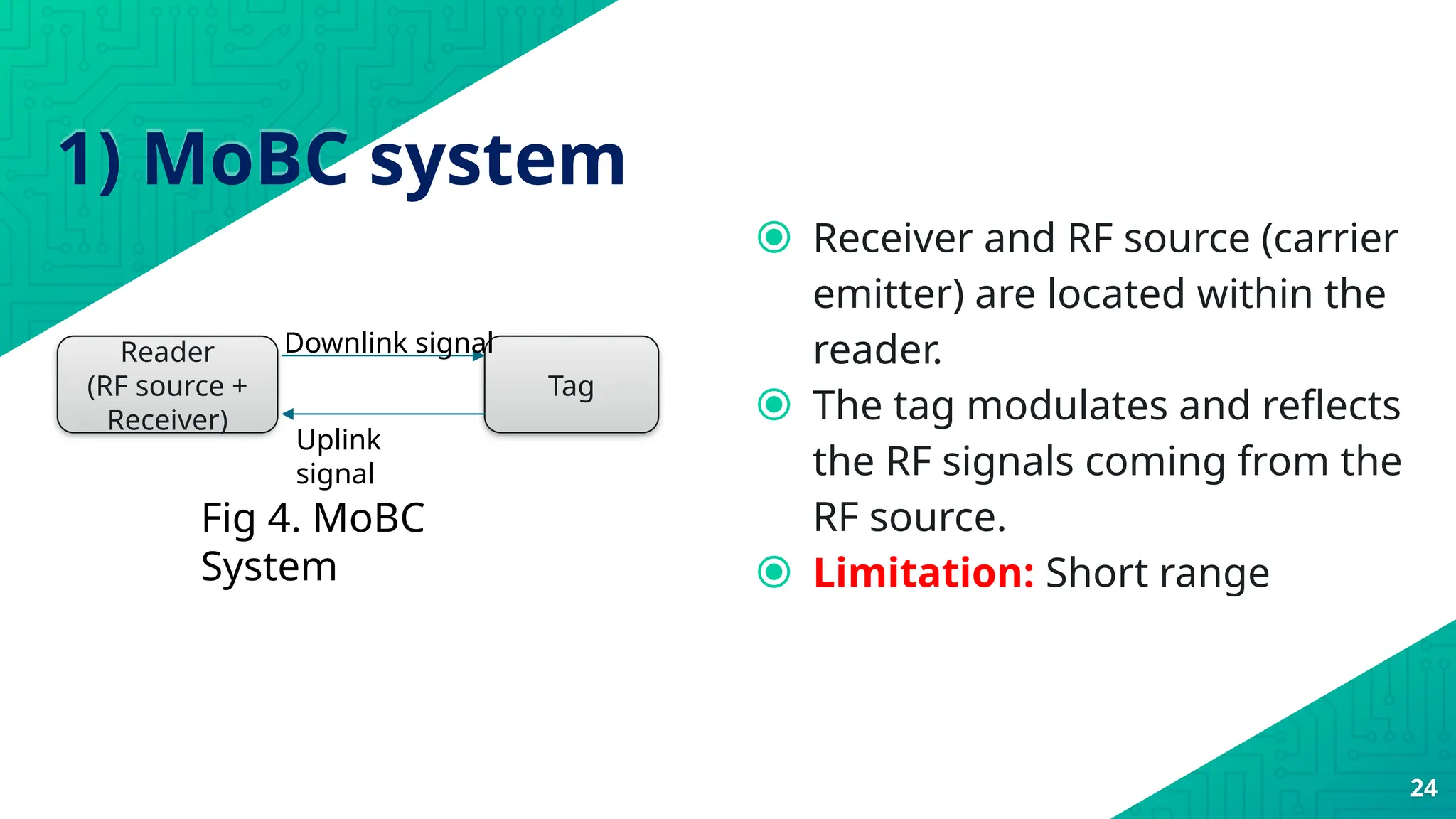
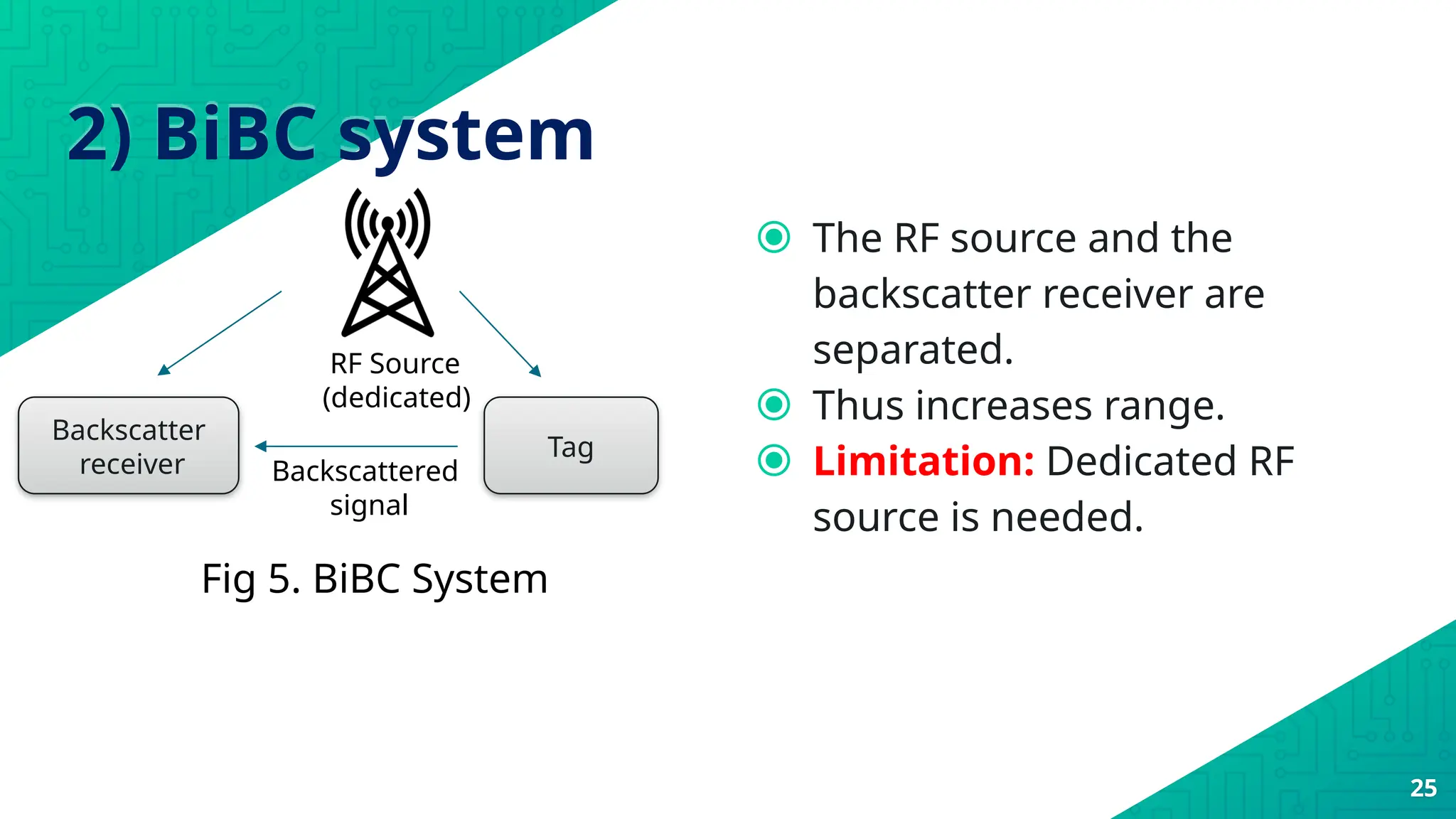
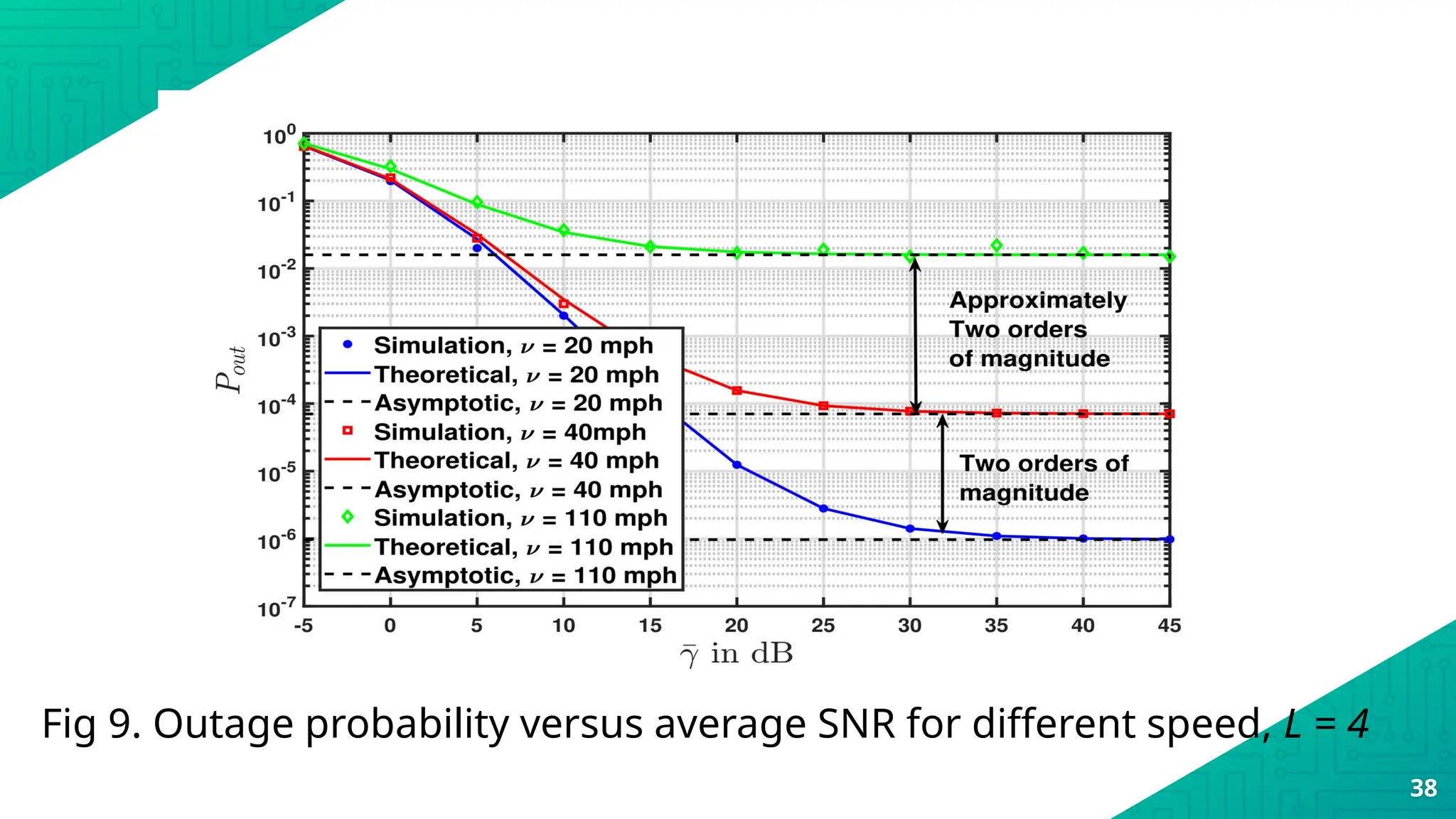
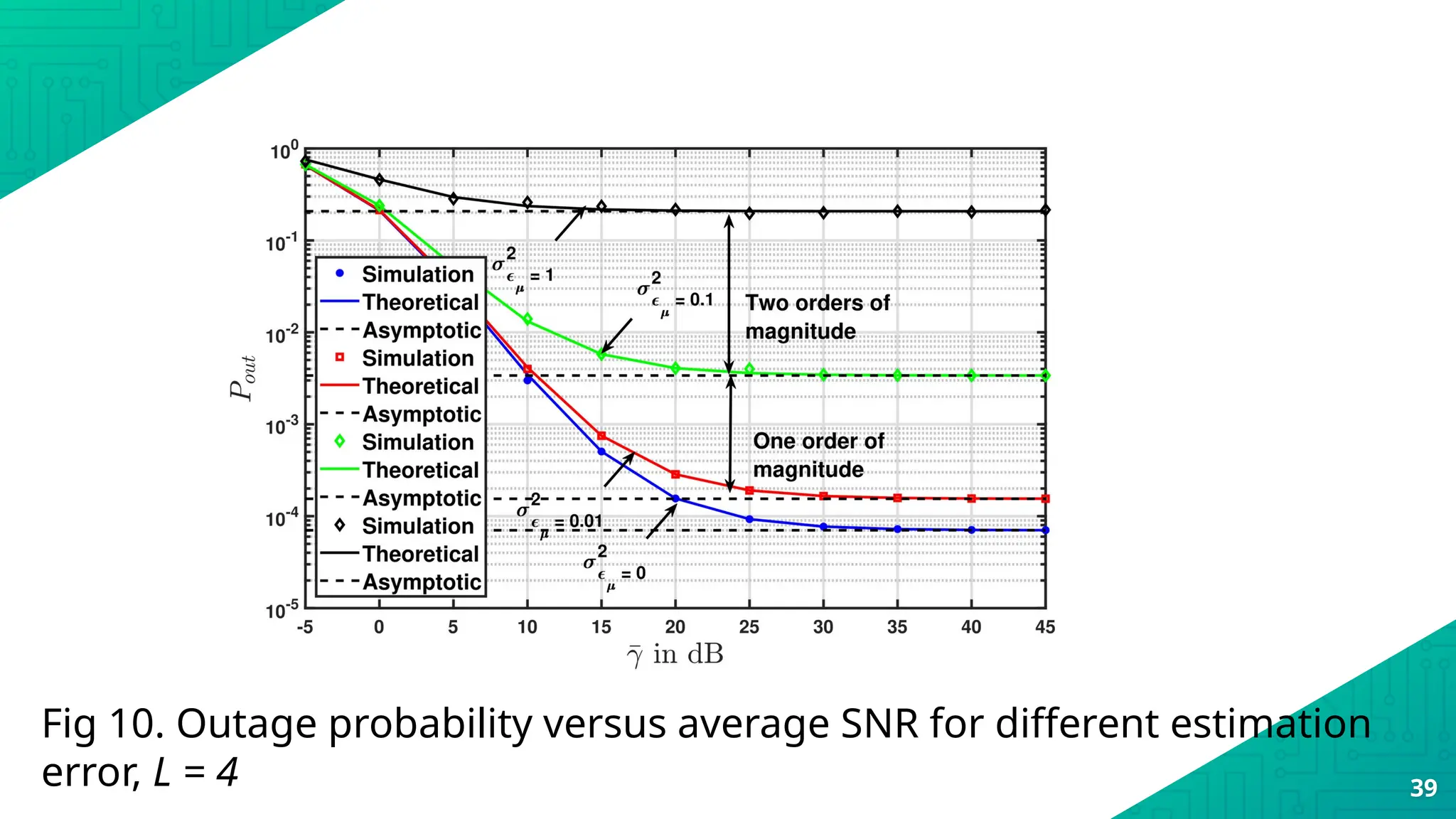
The document discusses the Global System for Mobile Communications (GSM), detailing its specifications, features, and advantages over analogue systems, including increased capacity, improved audio quality, and security measures. It outlines GSM's use of specific radio frequencies, cellular telephony structure, and various services such as voice and data connections, highlighting its importance in the mobilization of communication. Additionally, the document explores advanced concepts like backscatter communication, its types, and performance metrics in relation to future Internet of Things (IoT) scenarios.



![Trends in short range IoT
communication
19
• By 2027, the total number of short range IoT devices => 22.4 billion [1].
• Que. Could you please mention different short range IoT protocols ?
Short range IoT protocols
Bluetoot
h
Ultra
wide
band
(UWB)
Zigbee Wi-Fi](https://image.slidesharecdn.com/unit5gsm-241004092829-0071d572/75/Comprehensive-Overview-of-GSM-Technology-Architecture-and-Applications-19-2048.jpg)
![20
Fig 1. Power consumption by different short range wireless
communication standards [2]](https://image.slidesharecdn.com/unit5gsm-241004092829-0071d572/75/Comprehensive-Overview-of-GSM-Technology-Architecture-and-Applications-20-2048.jpg)
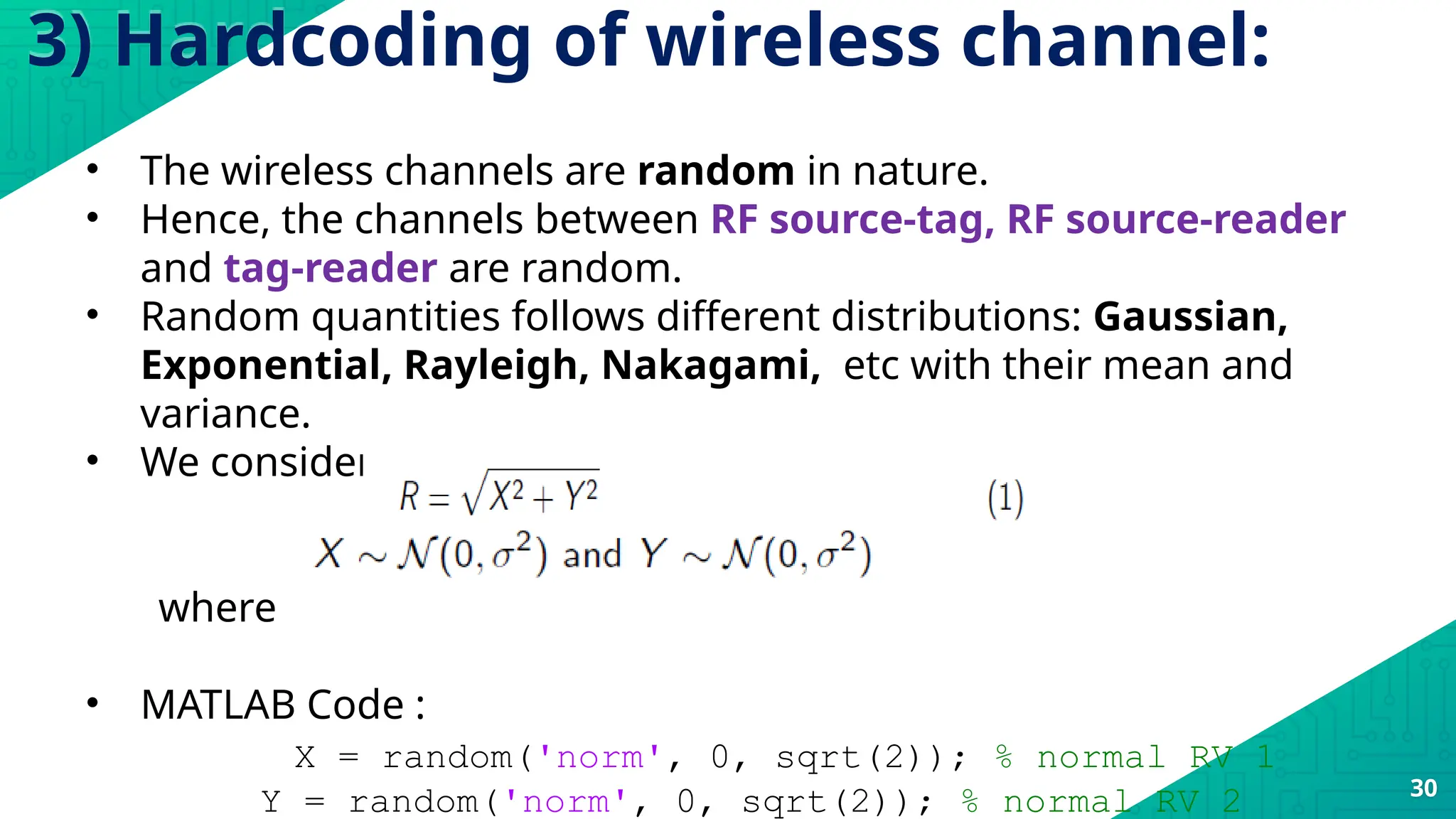

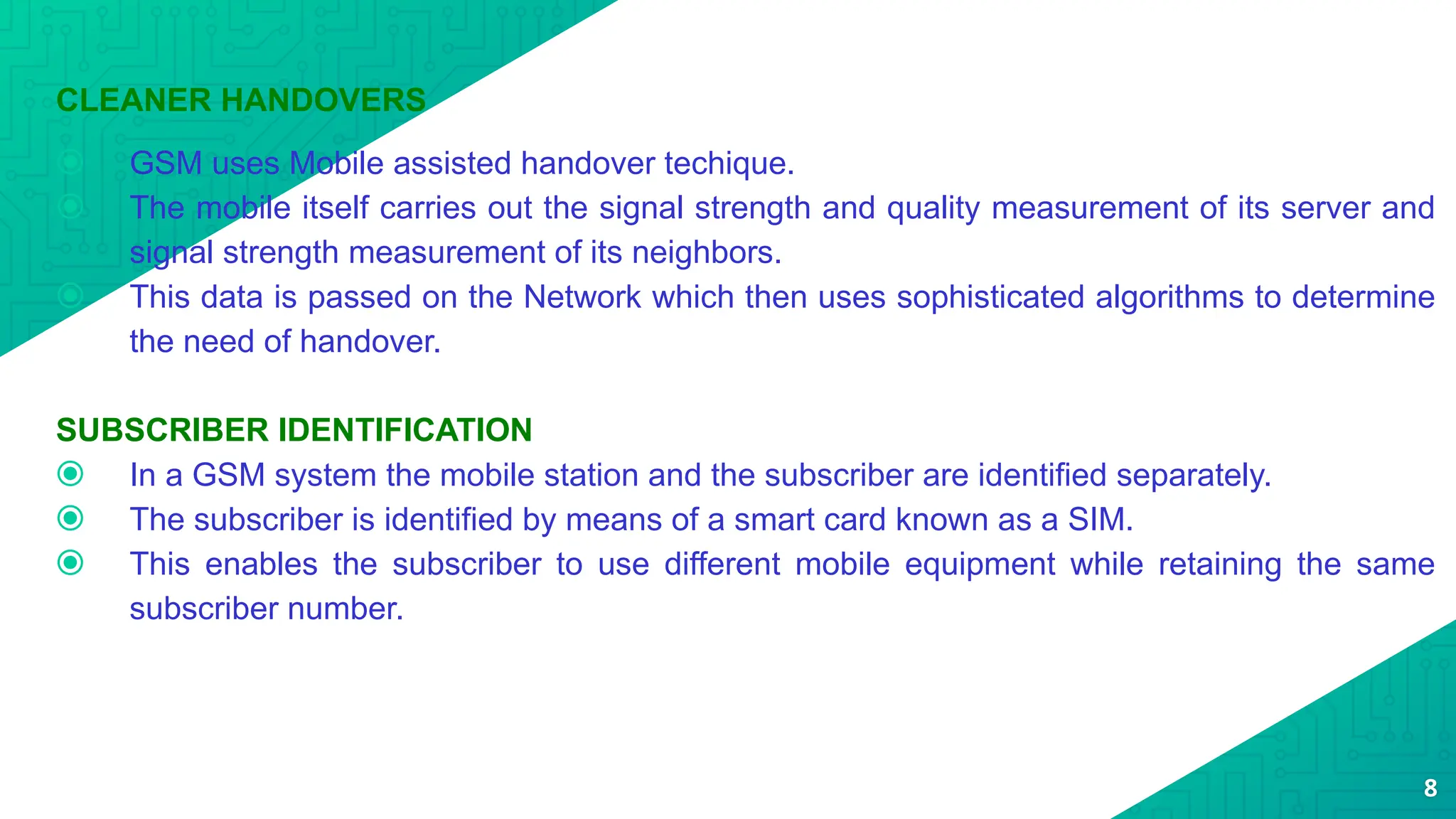
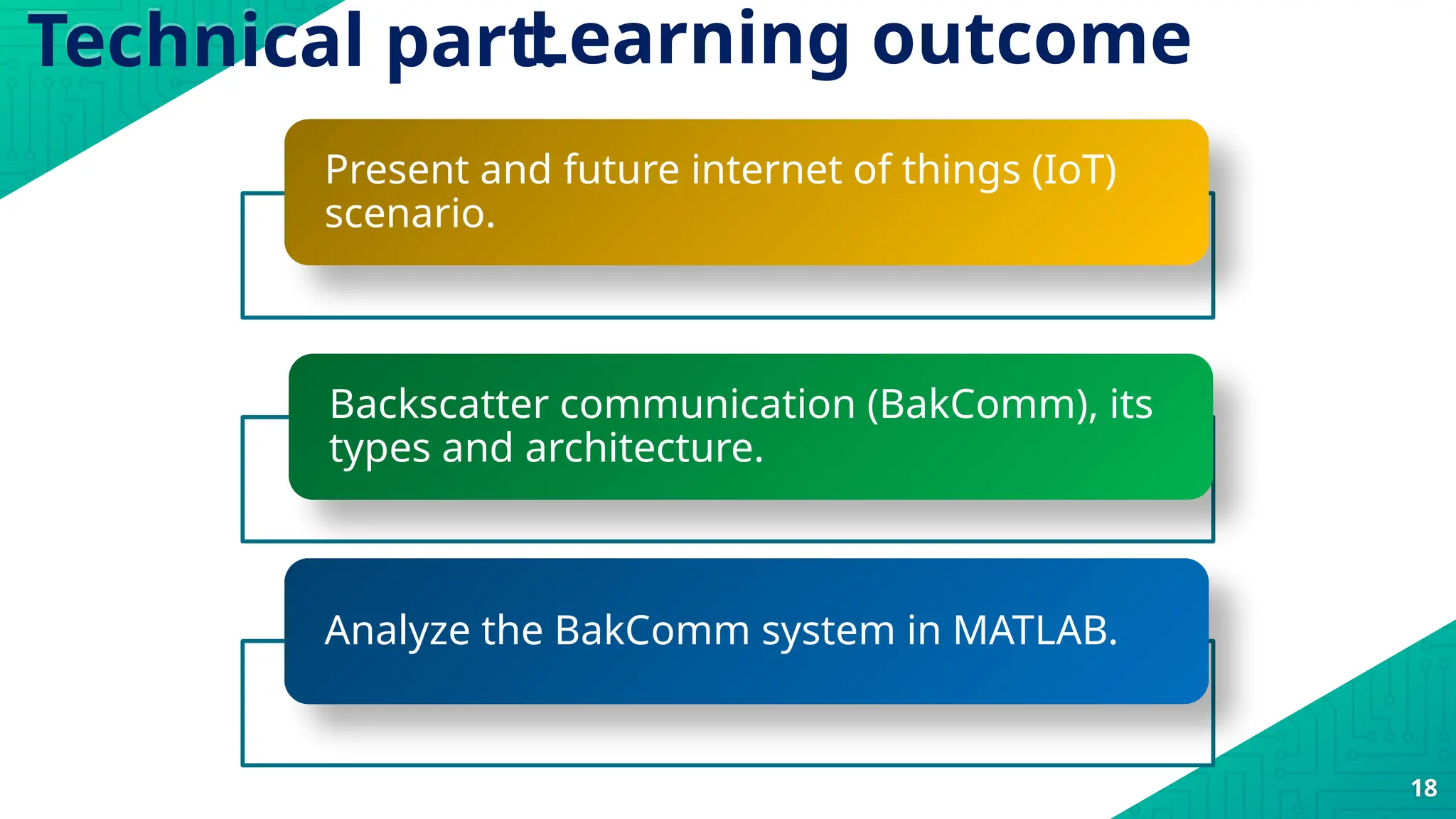
![%% Correlation Parameter Calculation
vel_r =10; % 20 miles per hour is speed of reader and it is 8.9408 mps.
c = 3*10^8; % speed of light
fc = 1.9*10^9; % carrier frequency in GHz
Rs = 9.6 *10^3; % data rate
Z = ((2*pi*fc*vel_r)/(Rs*c));
P_mun = besselj(0,Z); % rho i.e., correlation parameter
c3 = (P_mun)^(2*(n-1));
v_phi_mun = (1-c3)*sig2_mun;% variance of nodes mobility noise
%% Looping
op = []; count = 0;
for j1 = -5:5:15 % Avg transmit snr i.e., gammabar in dB
jj1 = 10^(j1/10); dB to linear conversion
33](https://image.slidesharecdn.com/unit5gsm-241004092829-0071d572/75/Comprehensive-Overview-of-GSM-Technology-Architecture-and-Applications-33-2048.jpg)

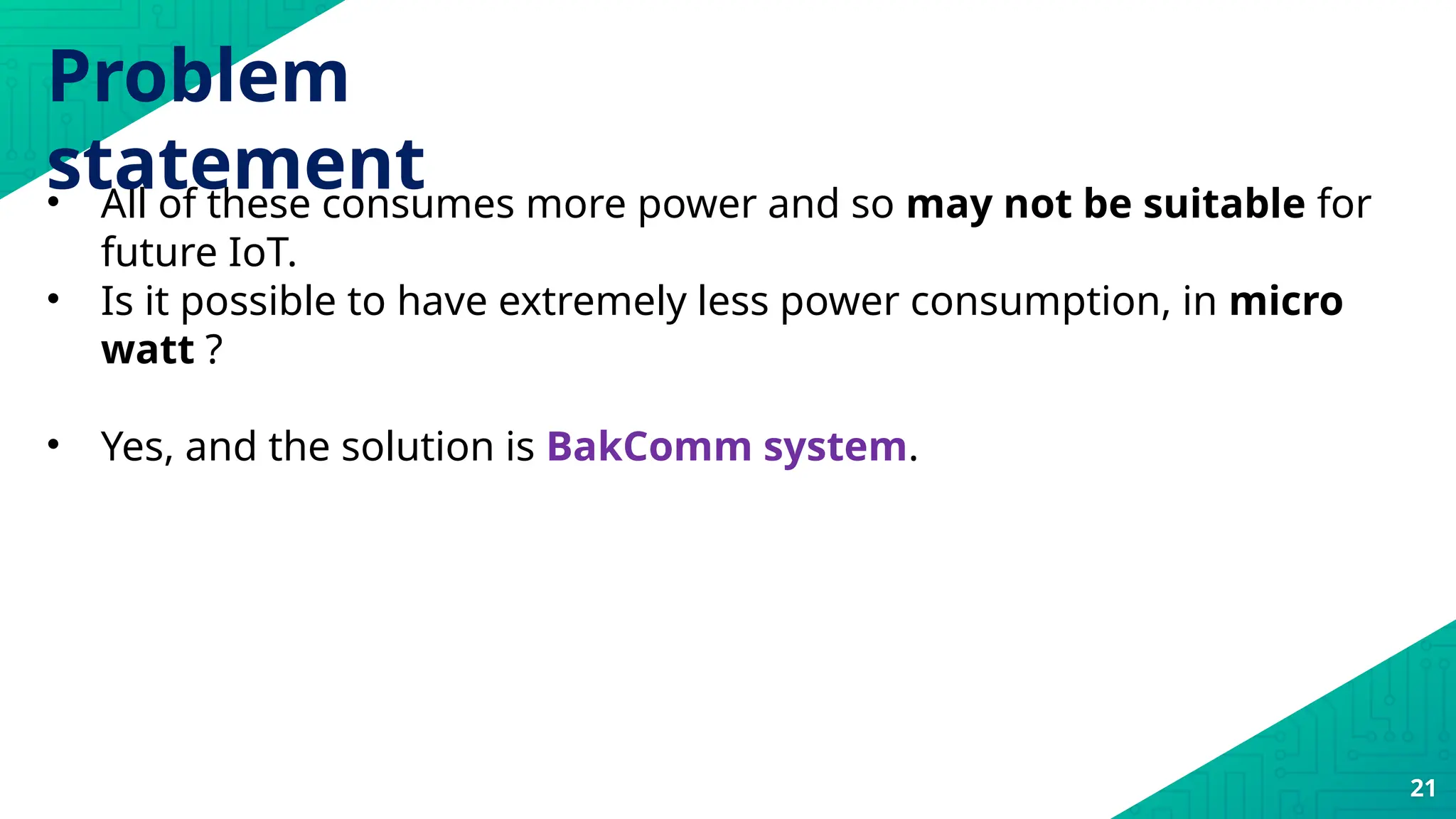
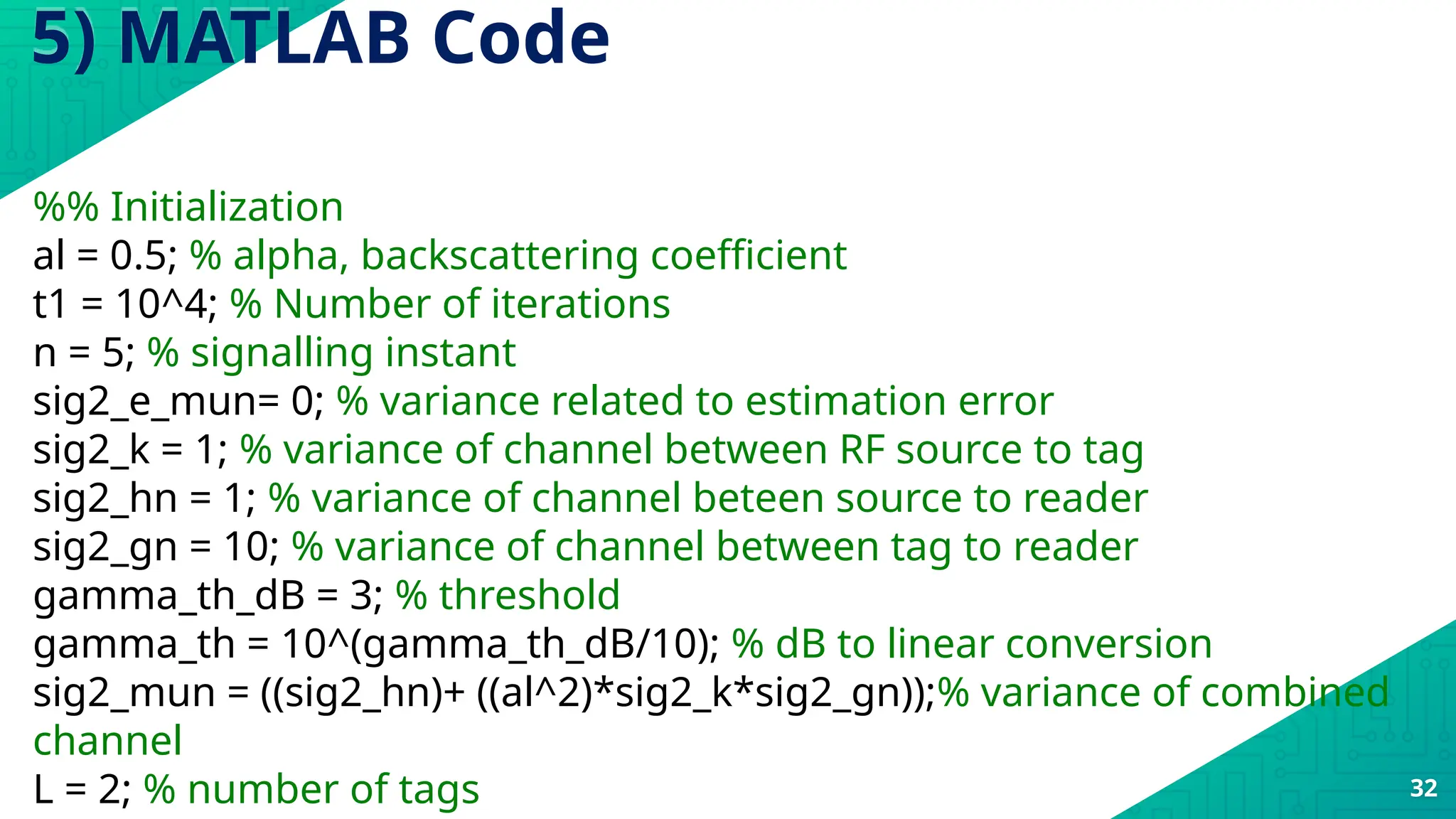
![SNRdB = -5:5:15; % Avg transmit snr i.e., gammabar
if gamma_s < gamma_th % Step 1: definition of outage probability
count = count+1;
end
end
op = [op,count/(t)]; % appending the calculated outage probability
count = 0;
end
%% plotting
grid on;
semilogy(SNRdB,op,'g-','LineWidth',1.1); % semilog plot on y axis
title('Outage Probability for changes in SNR'); % title of plot
ylabel('Outage Probabilty'); % y axis label
xlabel('average ytansmit SNR') % x axis label 35](https://image.slidesharecdn.com/unit5gsm-241004092829-0071d572/75/Comprehensive-Overview-of-GSM-Technology-Architecture-and-Applications-35-2048.jpg)
![References:
[1] S. O’Dea, “Number of wide-area and short-range iot devices worldwide
from 2014 to 2026,” https://www.statista.com/statistics/1016276/wide-
area-and-short-rangeiot-device-installed-base-worldwide/, accessed:
2022-01-28.
[2] R. Mubashar, M. A. B. Siddique, A. U. Rehman, A. Asad, and A. Rasool,
“Comparative performance analysis of short-range wireless protocols for
wireless personal area network,” Iran Journal of Computer Science, vol. 4,
no. 3, pp. 201–210, 2021.
41](https://image.slidesharecdn.com/unit5gsm-241004092829-0071d572/75/Comprehensive-Overview-of-GSM-Technology-Architecture-and-Applications-41-2048.jpg)
