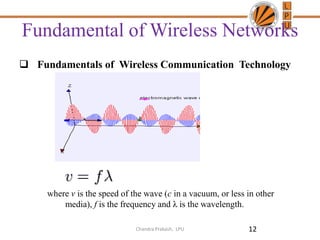
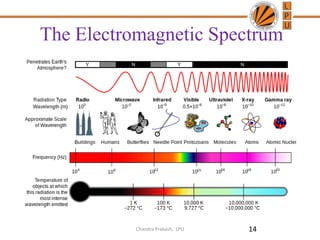
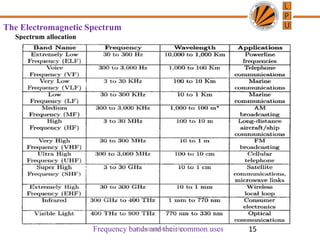
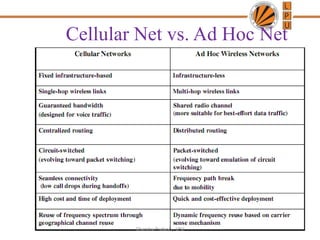
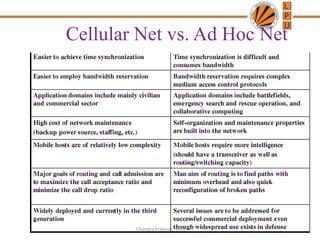
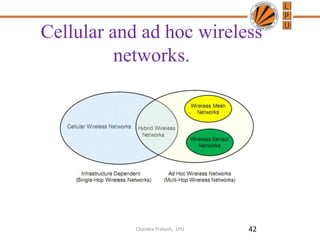
This document provides an overview of a course on mobile and ad hoc networks. It lists two textbooks that will be used and states that the goal is to cover fundamental design issues and solutions for network architecture and protocols. It also lists some related websites and outlines the objectives of chapters that will introduce wireless communication technologies, network standards, and multiple access techniques for ad hoc networks.
![Wireless Networks
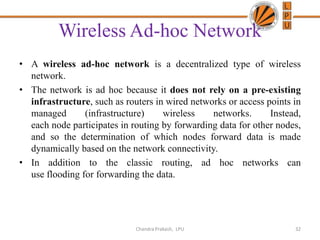
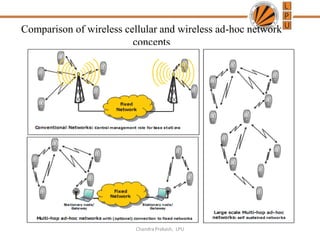
• Wireless Networks
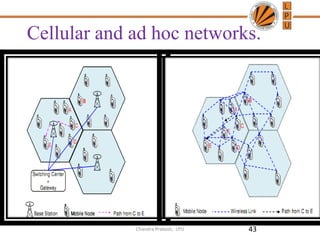
– Infrastructured Network
• Cellular Network (3GPP or 3GPP2)
• Wireless LAN (IEEE 802.11)
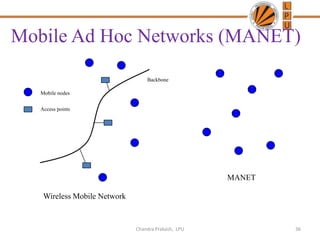
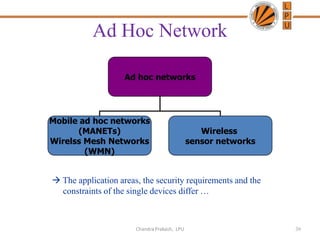
– Infrastructureless Network
• Ad Hoc Network
11
Internet
WLAN
Cellular
[Mobile/Wireless] Ad Hoc NetworksChandra Prakash, LPU](https://image.slidesharecdn.com/lecture1-mobileandadhocnetwork-introduction-130709073857-phpapp01/85/Lecture-1-mobile-and-adhoc-network-introduction-11-320.jpg)