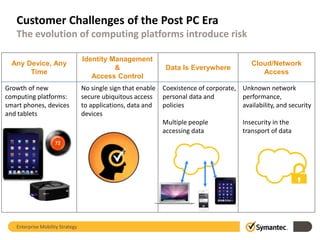
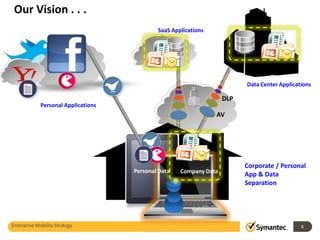
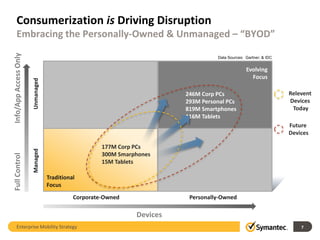
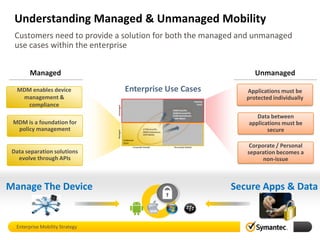
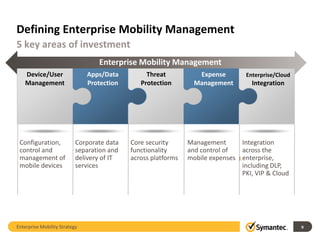
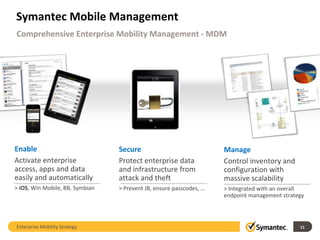
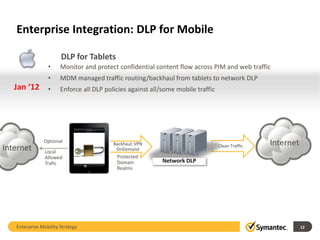
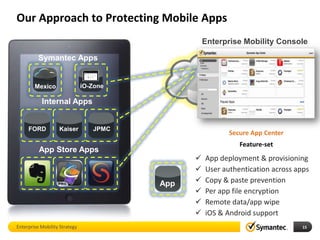
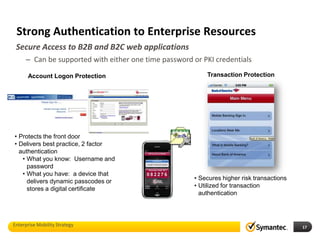
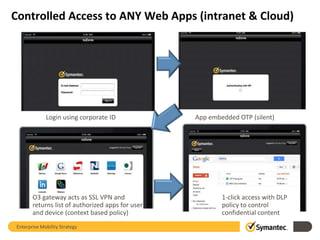
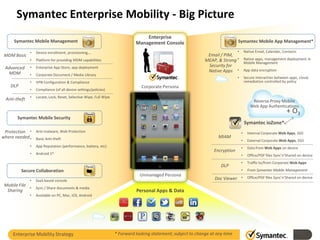
Enterprise mobility strategy involves managing both managed and unmanaged devices and data. It focuses on 5 key areas: device/user management, app/data protection, threat protection, expense management, and enterprise/cloud integration. Symantec's solution provides comprehensive enterprise mobility management through mobile device management, mobile security, and integration with other Symantec technologies to enable secure access and protect apps and data across managed and unmanaged devices.