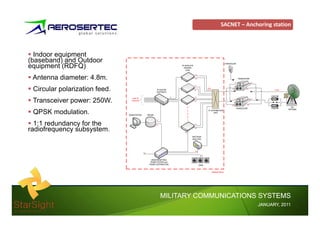
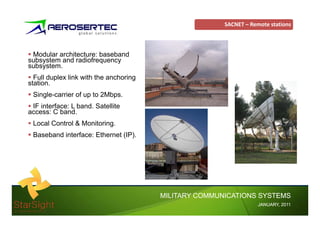
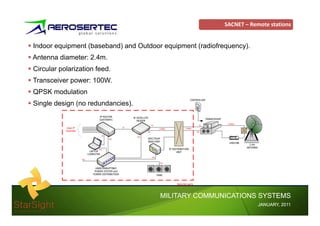
The document describes the SACNET secure satellite communications system, including its star topology network design with one anchoring station and 20 remote locations. It provides details on the technical specifications and components of the anchoring station and remote stations, as well as the centralized network management system and scope of supply. The document also discusses expertise in integrating networks and communications vehicles.