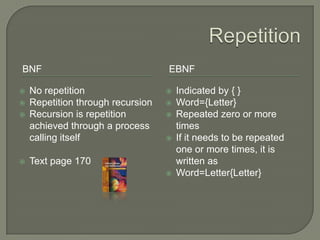
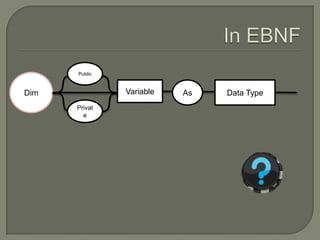
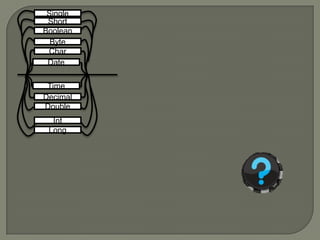
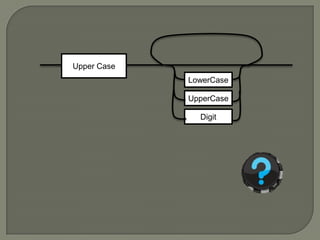
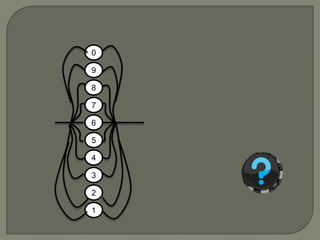
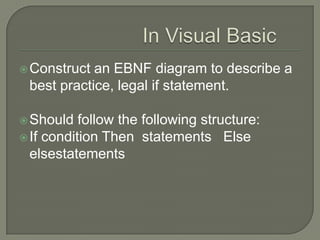
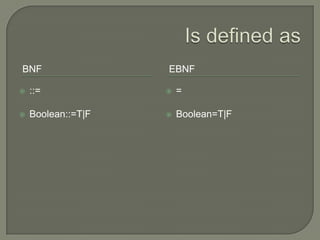
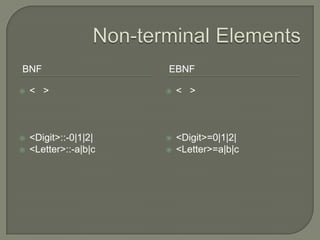
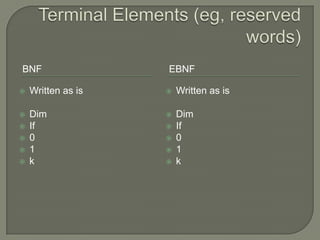
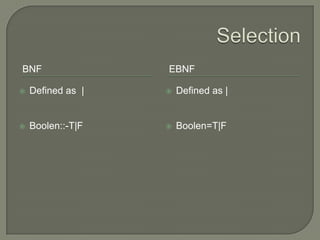
The document discusses metalanguages, specifically Backus-Naur Form (BNF) and Extended Backus-Naur Form (EBNF), highlighting their uses in representing syntax through text and diagrams. It explains the differences between BNF and EBNF, such as readability and handling of optional elements and repetition, and provides examples of EBNF syntax for legal statements in Visual Basic. The document serves as a guide for constructing EBNF diagrams for programming structures like 'if' statements.
![Optional ElementsBNFEBNFNo Optional Elements, so each option must be repeatedInteger::- - {<digit>} |{<digit>}[ ]Integer=[-] {<digit>}](https://image.slidesharecdn.com/metalanguagesbnfebnfstudentversion-090722002638-phpapp02/85/Meta-Languages-Bnf-Ebnf-Student-Version-12-320.jpg)