Mca3020 advanced database management system
•Download as DOCX, PDF•
0 likes•68 views
Dear students get fully solved assignments Send your semester & Specialization name to our mail id : help.mbaassignments@gmail.com or call us at : 08263069601
Report
Share
Report
Share
Recommended
Mca3020 advanced database management system

Dear students get fully solved assignments
Send your semester & Specialization name to our mail id :
help.mbaassignments@gmail.com
or
call us at : 08263069601
Mca3020 advanced database management system

Dear students get fully solved assignments
Send your semester & Specialization name to our mail id :
help.mbaassignments@gmail.com
or
call us at : 08263069601
Microsoft SQL Server 2016 

This document provides information about SQL Server and database management systems. It defines SQL Server, DBMS, and RDBMS. It lists features of database management including reducing redundancy and avoiding inconsistency, providing security, ensuring data integrity, and atomicity of transactions. It also lists examples of DBMS and RDBMS software and describes features like authentication, authorization, and ACID properties.
Mi0034 – database management system

Dear students get fully solved assignments
Send your semester & Specialization name to our mail id :
help.mbaassignments@gmail.com
or
call us at : 08263069601
Mi0034 database management system

The document provides information about an assignment for a Database Management Systems course. It includes 6 questions about key concepts in databases and DBMS. It provides the student's name, semester, course code, credit hours, and evaluation criteria. It asks the student to answer all questions, with 10-mark questions being approximately 400 words each. The questions cover topics like the definition of a DBMS, relational algebra operations, client-server models, SQL, locking protocols, distributed databases, and object-oriented data models. It provides contact information for students to get fully solved assignments.
Dbms

This document discusses key concepts related to databases and database management systems (DBMS). It defines metadata as data about data, such as information about a database's structure, that is stored in the data dictionary. It describes problems with traditional two-file processing systems and how the database approach integrates data and reduces data duplication. The core functions of a DBMS are presented, including its role in translating requests between users and the database. Advantages and common applications of DBMS are outlined.
Mi0034 – database management system

Dear students get fully solved assignments
Send your semester & Specialization name to our mail id :
help.mbaassignments@gmail.com
or
call us at : 08263069601
Database systems assignment 1

Database systems address several issues related to data storage and management:
1. Data redundancy and inconsistency are eliminated through database normalization which prevents duplicate data and ensures data remains consistent.
2. Difficulty in accessing data is resolved by providing application programs and interfaces to access and manage data through a database management system.
3. Data isolation and scattering across different files and formats is addressed by collecting all data into a centralized database.
Recommended
Mca3020 advanced database management system

Dear students get fully solved assignments
Send your semester & Specialization name to our mail id :
help.mbaassignments@gmail.com
or
call us at : 08263069601
Mca3020 advanced database management system

Dear students get fully solved assignments
Send your semester & Specialization name to our mail id :
help.mbaassignments@gmail.com
or
call us at : 08263069601
Microsoft SQL Server 2016 

This document provides information about SQL Server and database management systems. It defines SQL Server, DBMS, and RDBMS. It lists features of database management including reducing redundancy and avoiding inconsistency, providing security, ensuring data integrity, and atomicity of transactions. It also lists examples of DBMS and RDBMS software and describes features like authentication, authorization, and ACID properties.
Mi0034 – database management system

Dear students get fully solved assignments
Send your semester & Specialization name to our mail id :
help.mbaassignments@gmail.com
or
call us at : 08263069601
Mi0034 database management system

The document provides information about an assignment for a Database Management Systems course. It includes 6 questions about key concepts in databases and DBMS. It provides the student's name, semester, course code, credit hours, and evaluation criteria. It asks the student to answer all questions, with 10-mark questions being approximately 400 words each. The questions cover topics like the definition of a DBMS, relational algebra operations, client-server models, SQL, locking protocols, distributed databases, and object-oriented data models. It provides contact information for students to get fully solved assignments.
Dbms

This document discusses key concepts related to databases and database management systems (DBMS). It defines metadata as data about data, such as information about a database's structure, that is stored in the data dictionary. It describes problems with traditional two-file processing systems and how the database approach integrates data and reduces data duplication. The core functions of a DBMS are presented, including its role in translating requests between users and the database. Advantages and common applications of DBMS are outlined.
Mi0034 – database management system

Dear students get fully solved assignments
Send your semester & Specialization name to our mail id :
help.mbaassignments@gmail.com
or
call us at : 08263069601
Database systems assignment 1

Database systems address several issues related to data storage and management:
1. Data redundancy and inconsistency are eliminated through database normalization which prevents duplicate data and ensures data remains consistent.
2. Difficulty in accessing data is resolved by providing application programs and interfaces to access and manage data through a database management system.
3. Data isolation and scattering across different files and formats is addressed by collecting all data into a centralized database.
Db lec 05_new

This document discusses data models and database management system architectures. It covers:
1) Categories of data models including conceptual, implementation, and physical models.
2) Classifications of DBMSs including the data model used (relational, network, etc.), number of users, number of sites, and cost.
3) Common multi-user DBMS architectures like teleprocessing, file-server, and client-server (two-tier and three-tier).
CQRS introduction

1. The document introduces CQRS and event sourcing architectures. It discusses how CQRS handles collaborations and staleness of data differently than conventional architectures.
2. Examples are provided to illustrate how CQRS would handle commands and events differently than updating a database directly. Commands are treated as verbs and handled asynchronously.
3. Benefits of CQRS include better scalability and performance when data reads are separated from writes. It also more accurately reflects how data becomes stale over time during collaborations. Cons include increased complexity to implement.
Locking in SQL Server

SQL Server uses different types of locks at varying levels of granularity to control access to resources by transactions. Locking resources at a finer-grained level, like individual rows, increases concurrency but requires more locks. Locking at a coarser level, like entire tables, reduces the number of required locks but also decreases concurrency by restricting access to the entire resource. SQL Server automatically determines the appropriate lock level needed based on the transaction's data access needs.
DATABASE FUNCTIONS

This document discusses database management systems (DBMS) and their functions. It begins by describing the functions of a DBMS, including data dictionary management, data storage management, data transformation and presentation, security management, and more. It then discusses how managing database systems has shifted the focus from programming to managing organizational resources. The document ends by explaining the three-schema architecture of databases, which includes external, conceptual, and physical schemas that separate the user application from the physical database.
Struts 2 – Architecture

This document provides an overview of the Struts 2 framework architecture and its request lifecycle. It explains that Struts 2 follows a pull-MVC pattern with five main components: actions, interceptors, the value stack, results, and view technologies. The request lifecycle involves a user request being routed through the filter dispatcher to an action, then any configured interceptors before the action is performed. Finally a result prepares the view to return to the user. It also provides an example of a basic "Hello World" Struts 2 application to demonstrate these concepts.
Mi0034 – database management system

Dear students get fully solved assignments
Send your semester & Specialization name to our mail id :
help.mbaassignments@gmail.com
or
call us at : 08263069601
Supporting Transactions

This document discusses database transactions and improving database performance. It defines transactions as operations on a database like create, retrieve, update and delete. Transactions can involve one or more of these operations on one or more tables. The document then provides examples of transactions for an appointment booking system and boat rental system. It discusses using indexes, views and denormalization to improve query performance by reducing the need to join tables. Permissions can be granted and revoked to users and roles to control database access.
Sql server concurrency

The document discusses concurrency and transactions in SQL Server databases. It covers topics such as locking basics, pessimistic and optimistic concurrency models, transaction isolation levels, and preventing issues like dirty reads, non-repeatable reads and phantom reads. The key aspects of transactions discussed are atomicity, consistency, isolation and durability (ACID).
Microsoft access powerpoint final

This document provides an overview and introduction to Microsoft Access. It discusses what Access is, when it should be used over Excel or SPSS, its advantages over other database management systems like Oracle, the structure of Access files, best practices for data storage and relationships, and how queries work. Resources for further learning about Access are also provided.
no sql presentation

This document provides an overview of NoSQL databases. It discusses why cloud data stores became popular due to the rise of social media sites and need for large data storage. NoSQL databases provide a mechanism for storage and retrieval of data that is not modeled in tabular relations. NoSQL databases are scalable, do not require fixed schemas, and lack ACID properties. The document also discusses the CAP theorem, which states that a distributed system cannot achieve consistency, availability, and partition tolerance simultaneously.
Databases in 30 minutes.

A quick run through of relational and noSql databases, ACID/BASE properties that govern them and also a quick look into the CAP theorem. It also discusses on the various points to consider while choosing a DB for any application
Mi0034 – database management system

Dear students get fully solved SMU MBA assignments
Send your semester & Specialization name to our mail id :
“ help.mbaassignments@gmail.com ”
or
Call us at : 08263069601
ADBMS 19MCA8125.pdf

This document contains 5 programs written in PL/SQL. Each program accepts user input, performs conditional logic based on the input, and outputs a result to the screen using dbms_output.put_line. The programs check if a year is a leap year, calculate the cost of an apple box based on weight, and determine if a user is a child, major, or adult based on their age.
Mi0034 database management systems

This document provides information about getting fully solved assignments. Students can send their semester and specialization details to the email address provided or call the phone number to get solved assignments. It is preferred to contact via email except in emergencies. The document then provides an example of an assignment question related to database management systems.
Bca3020 database management system

This document provides information about getting fully solved assignments for the SMU BBA Spring 2014 semester. It includes contact information to email or call for assistance, along with sample assignment questions on topics like databases, SQL, and object-relational mapping. Students are instructed to include their semester and specialization when contacting for help with assignments.
S18 das

This document describes LinkedIn's Databus, a distributed change data capture system that reliably captures and propagates changes from primary data stores. It has four main components - a fetcher that extracts changes from data sources, a log store that caches changes, a snapshot store that maintains a moving snapshot, and a subscription client that pulls changes. Databus uses a pull-based model where consumers pull changes based on a monotonically increasing system change number. It supports capturing transaction boundaries, commit order, and consistent states to preserve consistency from the data source.
Mi0034 database management systems

Dear students get fully solved assignments
Send your semester & Specialization name to our mail id :
help.mbaassignments@gmail.com
or
call us at : 08263069601
IP PROJECT FILE

This document contains information about a student project on a quiz application, including:
- The student's name and address along with the front-end and back-end tools used.
- An acknowledgement section thanking the teacher and principal for their support.
- An introduction describing the purpose of developing a software system to automate quiz functionalities.
- Details about the database design including tables to store questions, answers and student results.
- Description of the menu design and input/output forms with event coding to allow students to take tests and view results.
Building a SaaS Style Application

This document discusses patterns for building software applications using a Software as a Service (SaaS) model. It identifies 7 key challenges in architecting software to be delivered as a service:
1. Using a single database for multiple tenants while ensuring performance, extensibility, security and customization.
2. Enforcing data security at the architecture level to prevent unauthorized access to tenant data.
3. Handling configuration/metadata for tenants while minimizing data storage and enabling simplicity.
4. Orchestrating tenant workflows and navigation by integrating with metadata services.
5. Guaranteeing high scalability and availability while supporting tenant-specific requirements.
The document provides solutions to each challenge through
access.2021.3077680.pdf

This document proposes a novel distributed architecture for a NoSQL datastore that supports strong consistency while maintaining high scalability. It is based on the Scalable Distributed Two-Layer Data Store (SD2DS) model, which has proven efficient. The architecture considers concurrent and unfinished operations to ensure consistency. Algorithms for scheduling operations are presented and proven theoretically correct. An implementation is evaluated experimentally against MongoDB and MemCached, showing high performance compared to existing NoSQL systems. The architecture aims to augment SD2DS with consistency mechanisms without impacting scalability.
Workload Management with MicroStrategy Software and IBM DB2 9.5

This paper describes the best practices for configuring MicroStrategy software to use the workload management (WLM) features of IBM DB2 9.5 for Linux®, Unix®, and Windows. Source: ftp://ftp.software.ibm.com/software/data/sw-library/db2/papers/wlm_msi_db29.5.pdf
More Related Content
What's hot
Db lec 05_new

This document discusses data models and database management system architectures. It covers:
1) Categories of data models including conceptual, implementation, and physical models.
2) Classifications of DBMSs including the data model used (relational, network, etc.), number of users, number of sites, and cost.
3) Common multi-user DBMS architectures like teleprocessing, file-server, and client-server (two-tier and three-tier).
CQRS introduction

1. The document introduces CQRS and event sourcing architectures. It discusses how CQRS handles collaborations and staleness of data differently than conventional architectures.
2. Examples are provided to illustrate how CQRS would handle commands and events differently than updating a database directly. Commands are treated as verbs and handled asynchronously.
3. Benefits of CQRS include better scalability and performance when data reads are separated from writes. It also more accurately reflects how data becomes stale over time during collaborations. Cons include increased complexity to implement.
Locking in SQL Server

SQL Server uses different types of locks at varying levels of granularity to control access to resources by transactions. Locking resources at a finer-grained level, like individual rows, increases concurrency but requires more locks. Locking at a coarser level, like entire tables, reduces the number of required locks but also decreases concurrency by restricting access to the entire resource. SQL Server automatically determines the appropriate lock level needed based on the transaction's data access needs.
DATABASE FUNCTIONS

This document discusses database management systems (DBMS) and their functions. It begins by describing the functions of a DBMS, including data dictionary management, data storage management, data transformation and presentation, security management, and more. It then discusses how managing database systems has shifted the focus from programming to managing organizational resources. The document ends by explaining the three-schema architecture of databases, which includes external, conceptual, and physical schemas that separate the user application from the physical database.
Struts 2 – Architecture

This document provides an overview of the Struts 2 framework architecture and its request lifecycle. It explains that Struts 2 follows a pull-MVC pattern with five main components: actions, interceptors, the value stack, results, and view technologies. The request lifecycle involves a user request being routed through the filter dispatcher to an action, then any configured interceptors before the action is performed. Finally a result prepares the view to return to the user. It also provides an example of a basic "Hello World" Struts 2 application to demonstrate these concepts.
Mi0034 – database management system

Dear students get fully solved assignments
Send your semester & Specialization name to our mail id :
help.mbaassignments@gmail.com
or
call us at : 08263069601
Supporting Transactions

This document discusses database transactions and improving database performance. It defines transactions as operations on a database like create, retrieve, update and delete. Transactions can involve one or more of these operations on one or more tables. The document then provides examples of transactions for an appointment booking system and boat rental system. It discusses using indexes, views and denormalization to improve query performance by reducing the need to join tables. Permissions can be granted and revoked to users and roles to control database access.
Sql server concurrency

The document discusses concurrency and transactions in SQL Server databases. It covers topics such as locking basics, pessimistic and optimistic concurrency models, transaction isolation levels, and preventing issues like dirty reads, non-repeatable reads and phantom reads. The key aspects of transactions discussed are atomicity, consistency, isolation and durability (ACID).
Microsoft access powerpoint final

This document provides an overview and introduction to Microsoft Access. It discusses what Access is, when it should be used over Excel or SPSS, its advantages over other database management systems like Oracle, the structure of Access files, best practices for data storage and relationships, and how queries work. Resources for further learning about Access are also provided.
no sql presentation

This document provides an overview of NoSQL databases. It discusses why cloud data stores became popular due to the rise of social media sites and need for large data storage. NoSQL databases provide a mechanism for storage and retrieval of data that is not modeled in tabular relations. NoSQL databases are scalable, do not require fixed schemas, and lack ACID properties. The document also discusses the CAP theorem, which states that a distributed system cannot achieve consistency, availability, and partition tolerance simultaneously.
Databases in 30 minutes.

A quick run through of relational and noSql databases, ACID/BASE properties that govern them and also a quick look into the CAP theorem. It also discusses on the various points to consider while choosing a DB for any application
What's hot (11)
Similar to Mca3020 advanced database management system
Mi0034 – database management system

Dear students get fully solved SMU MBA assignments
Send your semester & Specialization name to our mail id :
“ help.mbaassignments@gmail.com ”
or
Call us at : 08263069601
ADBMS 19MCA8125.pdf

This document contains 5 programs written in PL/SQL. Each program accepts user input, performs conditional logic based on the input, and outputs a result to the screen using dbms_output.put_line. The programs check if a year is a leap year, calculate the cost of an apple box based on weight, and determine if a user is a child, major, or adult based on their age.
Mi0034 database management systems

This document provides information about getting fully solved assignments. Students can send their semester and specialization details to the email address provided or call the phone number to get solved assignments. It is preferred to contact via email except in emergencies. The document then provides an example of an assignment question related to database management systems.
Bca3020 database management system

This document provides information about getting fully solved assignments for the SMU BBA Spring 2014 semester. It includes contact information to email or call for assistance, along with sample assignment questions on topics like databases, SQL, and object-relational mapping. Students are instructed to include their semester and specialization when contacting for help with assignments.
S18 das

This document describes LinkedIn's Databus, a distributed change data capture system that reliably captures and propagates changes from primary data stores. It has four main components - a fetcher that extracts changes from data sources, a log store that caches changes, a snapshot store that maintains a moving snapshot, and a subscription client that pulls changes. Databus uses a pull-based model where consumers pull changes based on a monotonically increasing system change number. It supports capturing transaction boundaries, commit order, and consistent states to preserve consistency from the data source.
Mi0034 database management systems

Dear students get fully solved assignments
Send your semester & Specialization name to our mail id :
help.mbaassignments@gmail.com
or
call us at : 08263069601
IP PROJECT FILE

This document contains information about a student project on a quiz application, including:
- The student's name and address along with the front-end and back-end tools used.
- An acknowledgement section thanking the teacher and principal for their support.
- An introduction describing the purpose of developing a software system to automate quiz functionalities.
- Details about the database design including tables to store questions, answers and student results.
- Description of the menu design and input/output forms with event coding to allow students to take tests and view results.
Building a SaaS Style Application

This document discusses patterns for building software applications using a Software as a Service (SaaS) model. It identifies 7 key challenges in architecting software to be delivered as a service:
1. Using a single database for multiple tenants while ensuring performance, extensibility, security and customization.
2. Enforcing data security at the architecture level to prevent unauthorized access to tenant data.
3. Handling configuration/metadata for tenants while minimizing data storage and enabling simplicity.
4. Orchestrating tenant workflows and navigation by integrating with metadata services.
5. Guaranteeing high scalability and availability while supporting tenant-specific requirements.
The document provides solutions to each challenge through
access.2021.3077680.pdf

This document proposes a novel distributed architecture for a NoSQL datastore that supports strong consistency while maintaining high scalability. It is based on the Scalable Distributed Two-Layer Data Store (SD2DS) model, which has proven efficient. The architecture considers concurrent and unfinished operations to ensure consistency. Algorithms for scheduling operations are presented and proven theoretically correct. An implementation is evaluated experimentally against MongoDB and MemCached, showing high performance compared to existing NoSQL systems. The architecture aims to augment SD2DS with consistency mechanisms without impacting scalability.
Workload Management with MicroStrategy Software and IBM DB2 9.5

This paper describes the best practices for configuring MicroStrategy software to use the workload management (WLM) features of IBM DB2 9.5 for Linux®, Unix®, and Windows. Source: ftp://ftp.software.ibm.com/software/data/sw-library/db2/papers/wlm_msi_db29.5.pdf
Mi0034 –database management systems

This document provides information about getting fully solved assignments from a company called Assignment Drive. It lists the contact details and instructions for students to send their semester and specialization to get assignments. It then provides details of subjects, codes, credits and marks for assignments in Database Management Systems for semester 3.
Build Application With MongoDB

MongoDB® is a matured NoSQL database product with an ever growing adoption. Many big enterprise and internet companies such as Cisco, EBay, Disney etc. are now running large scale mongoDB production deployments. With its increased adoption, mongoDB® has enabled developers to build new types of applications for cloud, mobile and social technologies. This makes mongoDB® developers an invaluable resource for companies looking to innovate in each of these areas.
Tech challenges in a large scale agile project

1. The document discusses three major technical challenges faced in a large-scale Java project that adopted Scrum methodology: modularization, testing environments, and declaratively representing domain knowledge.
2. For modularization, the project struggled with creating an optimal structure that balanced complexity, coupling, and cohesion across modules. Testing multiple environments provided benefits but also challenges in maintenance and automation.
3. Representing domain knowledge declaratively aimed to separate knowledge from implementation, but specific issues are not discussed in the summary due to a missing portion of the original text.
Espresso: LinkedIn's Distributed Data Serving Platform (Paper)

This paper, written by the LinkedIn Espresso Team, appeared at the ACM SIGMOD/PODS Conference (June 2013). To see the talk given by Swaroop Jagadish (Staff Software Engineer @ LinkedIn), go here:
http://www.slideshare.net/amywtang/li-espresso-sigmodtalk
Sigmod 2013 - On Brewing Fresh Espresso - LinkedIn's Distributed Data Serving...

Espresso is a document-oriented distributed data serving platform that has been built to address LinkedIn’s requirements for a scalable, performant, source-of-truth primary
store. It provides a hierarchical document model, transac-
tional support for modifications to related documents, real-
time secondary indexing, on-the-fly schema evolution and
provides a timeline consistent change capture stream. This
paper describes the motivation and design principles involved
in building Espresso, the data model and capabilities ex-
posed to clients, details of the replication and secondary
indexing implementation and presents a set of experimen-
tal results that characterize the performance of the system
along various dimensions.
ABC Architecture A New Approach To Build Reusable And Adaptable Business Tie...

1) The document proposes a new ABC Architecture for building reusable and adaptable business tier components based on static business interfaces.
2) The architecture uses Call Level Interfaces as a low-level API to communicate with databases, and implements type-safe interfaces to communicate with client applications based on SQL statement schemas.
3) ABC components can dynamically accept, remove, and update SQL statements at runtime from authorized entities, and execute the statements on behalf of client applications through the interfaces.
Data management in cloud study of existing systems and future opportunities

This document discusses data management in cloud computing and provides an overview of existing NoSQL database systems and their advantages over traditional SQL databases. It begins by defining cloud computing and the need for scalable data storage. It then discusses key goals for cloud data management systems including availability, scalability, elasticity and performance. Several popular NoSQL databases are described, including BigTable, MongoDB and Dynamo. The advantages of NoSQL systems like elastic scaling and easier administration are contrasted with some limitations like limited transaction support. The document concludes by discussing opportunities for future research to improve scalability and queries in cloud data management systems.
Developing multithreaded database application using java tools and oracle dat...

In many business organizations, database applicatio
ns are designed and implemented using
various DBMS and Programming Languages. These appli
cations are used to maintain
databases for the organizations. The organization
departments can be located at different
locations and can be connected by intranet environm
ent. In such environment maintenance of
database records become an assignment of complexity
which needs to be resolved. In this paper
an intranet application is designed and implemented
using Object-Oriented Programming
Language Java and Object-Relational Database Manage
ment System Oracle in multithreaded
Operating System environment.
DEVELOPING MULTITHREADED DATABASE APPLICATION USING JAVA TOOLS AND ORACLE DAT...

In many business organizations, database applications are designed and implemented using
various DBMS and Programming Languages. These applications are used to maintain
databases for the organizations. The organization departments can be located at different
locations and can be connected by intranet environment. In such environment maintenance of
database records become an assignment of complexity which needs to be resolved. In this paper
an intranet application is designed and implemented using Object-Oriented Programming
Language Java and Object-Relational Database Management System Oracle in multithreaded
Operating System environment
Similar to Mca3020 advanced database management system (20)
Advanced Database Management System MCQ with Answers_071802.pdf

Advanced Database Management System MCQ with Answers_071802.pdf
Workload Management with MicroStrategy Software and IBM DB2 9.5

Workload Management with MicroStrategy Software and IBM DB2 9.5
Espresso: LinkedIn's Distributed Data Serving Platform (Paper)

Espresso: LinkedIn's Distributed Data Serving Platform (Paper)
Sigmod 2013 - On Brewing Fresh Espresso - LinkedIn's Distributed Data Serving...

Sigmod 2013 - On Brewing Fresh Espresso - LinkedIn's Distributed Data Serving...
ABC Architecture A New Approach To Build Reusable And Adaptable Business Tie...

ABC Architecture A New Approach To Build Reusable And Adaptable Business Tie...
Data management in cloud study of existing systems and future opportunities

Data management in cloud study of existing systems and future opportunities
Developing multithreaded database application using java tools and oracle dat...

Developing multithreaded database application using java tools and oracle dat...
DEVELOPING MULTITHREADED DATABASE APPLICATION USING JAVA TOOLS AND ORACLE DAT...

DEVELOPING MULTITHREADED DATABASE APPLICATION USING JAVA TOOLS AND ORACLE DAT...
Recently uploaded
The History of Stoke Newington Street Names

Presented at the Stoke Newington Literary Festival on 9th June 2024
www.StokeNewingtonHistory.com
Benner "Expanding Pathways to Publishing Careers"

This presentation was provided by Rebecca Benner, Ph.D., of the American Society of Anesthesiologists, for the second session of NISO's 2024 Training Series "DEIA in the Scholarly Landscape." Session Two: 'Expanding Pathways to Publishing Careers,' was held June 13, 2024.
Gender and Mental Health - Counselling and Family Therapy Applications and In...

A proprietary approach developed by bringing together the best of learning theories from Psychology, design principles from the world of visualization, and pedagogical methods from over a decade of training experience, that enables you to: Learn better, faster!
ISO/IEC 27001, ISO/IEC 42001, and GDPR: Best Practices for Implementation and...

Denis is a dynamic and results-driven Chief Information Officer (CIO) with a distinguished career spanning information systems analysis and technical project management. With a proven track record of spearheading the design and delivery of cutting-edge Information Management solutions, he has consistently elevated business operations, streamlined reporting functions, and maximized process efficiency.
Certified as an ISO/IEC 27001: Information Security Management Systems (ISMS) Lead Implementer, Data Protection Officer, and Cyber Risks Analyst, Denis brings a heightened focus on data security, privacy, and cyber resilience to every endeavor.
His expertise extends across a diverse spectrum of reporting, database, and web development applications, underpinned by an exceptional grasp of data storage and virtualization technologies. His proficiency in application testing, database administration, and data cleansing ensures seamless execution of complex projects.
What sets Denis apart is his comprehensive understanding of Business and Systems Analysis technologies, honed through involvement in all phases of the Software Development Lifecycle (SDLC). From meticulous requirements gathering to precise analysis, innovative design, rigorous development, thorough testing, and successful implementation, he has consistently delivered exceptional results.
Throughout his career, he has taken on multifaceted roles, from leading technical project management teams to owning solutions that drive operational excellence. His conscientious and proactive approach is unwavering, whether he is working independently or collaboratively within a team. His ability to connect with colleagues on a personal level underscores his commitment to fostering a harmonious and productive workplace environment.
Date: May 29, 2024
Tags: Information Security, ISO/IEC 27001, ISO/IEC 42001, Artificial Intelligence, GDPR
-------------------------------------------------------------------------------
Find out more about ISO training and certification services
Training: ISO/IEC 27001 Information Security Management System - EN | PECB
ISO/IEC 42001 Artificial Intelligence Management System - EN | PECB
General Data Protection Regulation (GDPR) - Training Courses - EN | PECB
Webinars: https://pecb.com/webinars
Article: https://pecb.com/article
-------------------------------------------------------------------------------
For more information about PECB:
Website: https://pecb.com/
LinkedIn: https://www.linkedin.com/company/pecb/
Facebook: https://www.facebook.com/PECBInternational/
Slideshare: http://www.slideshare.net/PECBCERTIFICATION
BÀI TẬP BỔ TRỢ TIẾNG ANH 8 CẢ NĂM - GLOBAL SUCCESS - NĂM HỌC 2023-2024 (CÓ FI...

BÀI TẬP BỔ TRỢ TIẾNG ANH 8 CẢ NĂM - GLOBAL SUCCESS - NĂM HỌC 2023-2024 (CÓ FI...Nguyen Thanh Tu Collection
https://app.box.com/s/y977uz6bpd3af4qsebv7r9b7s21935vdBBR 2024 Summer Sessions Interview Training

Qualitative research interview training by Professor Katrina Pritchard and Dr Helen Williams
How to Setup Warehouse & Location in Odoo 17 Inventory

In this slide, we'll explore how to set up warehouses and locations in Odoo 17 Inventory. This will help us manage our stock effectively, track inventory levels, and streamline warehouse operations.
A Visual Guide to 1 Samuel | A Tale of Two Hearts

These slides walk through the story of 1 Samuel. Samuel is the last judge of Israel. The people reject God and want a king. Saul is anointed as the first king, but he is not a good king. David, the shepherd boy is anointed and Saul is envious of him. David shows honor while Saul continues to self destruct.
Jemison, MacLaughlin, and Majumder "Broadening Pathways for Editors and Authors"

Jemison, MacLaughlin, and Majumder "Broadening Pathways for Editors and Authors"National Information Standards Organization (NISO)
This presentation was provided by Racquel Jemison, Ph.D., Christina MacLaughlin, Ph.D., and Paulomi Majumder. Ph.D., all of the American Chemical Society, for the second session of NISO's 2024 Training Series "DEIA in the Scholarly Landscape." Session Two: 'Expanding Pathways to Publishing Careers,' was held June 13, 2024.Leveraging Generative AI to Drive Nonprofit Innovation

In this webinar, participants learned how to utilize Generative AI to streamline operations and elevate member engagement. Amazon Web Service experts provided a customer specific use cases and dived into low/no-code tools that are quick and easy to deploy through Amazon Web Service (AWS.)
Mule event processing models | MuleSoft Mysore Meetup #47

Mule event processing models | MuleSoft Mysore Meetup #47
Event Link:- https://meetups.mulesoft.com/events/details/mulesoft-mysore-presents-mule-event-processing-models/
Agenda
● What is event processing in MuleSoft?
● Types of event processing models in Mule 4
● Distinction between the reactive, parallel, blocking & non-blocking processing
For Upcoming Meetups Join Mysore Meetup Group - https://meetups.mulesoft.com/mysore/YouTube:- youtube.com/@mulesoftmysore
Mysore WhatsApp group:- https://chat.whatsapp.com/EhqtHtCC75vCAX7gaO842N
Speaker:-
Shivani Yasaswi - https://www.linkedin.com/in/shivaniyasaswi/
Organizers:-
Shubham Chaurasia - https://www.linkedin.com/in/shubhamchaurasia1/
Giridhar Meka - https://www.linkedin.com/in/giridharmeka
Priya Shaw - https://www.linkedin.com/in/priya-shaw
Recently uploaded (20)
Gender and Mental Health - Counselling and Family Therapy Applications and In...

Gender and Mental Health - Counselling and Family Therapy Applications and In...
Film vocab for eal 3 students: Australia the movie

Film vocab for eal 3 students: Australia the movie
ISO/IEC 27001, ISO/IEC 42001, and GDPR: Best Practices for Implementation and...

ISO/IEC 27001, ISO/IEC 42001, and GDPR: Best Practices for Implementation and...
BÀI TẬP BỔ TRỢ TIẾNG ANH 8 CẢ NĂM - GLOBAL SUCCESS - NĂM HỌC 2023-2024 (CÓ FI...

BÀI TẬP BỔ TRỢ TIẾNG ANH 8 CẢ NĂM - GLOBAL SUCCESS - NĂM HỌC 2023-2024 (CÓ FI...
How to Setup Warehouse & Location in Odoo 17 Inventory

How to Setup Warehouse & Location in Odoo 17 Inventory
Jemison, MacLaughlin, and Majumder "Broadening Pathways for Editors and Authors"

Jemison, MacLaughlin, and Majumder "Broadening Pathways for Editors and Authors"
Leveraging Generative AI to Drive Nonprofit Innovation

Leveraging Generative AI to Drive Nonprofit Innovation
Mule event processing models | MuleSoft Mysore Meetup #47

Mule event processing models | MuleSoft Mysore Meetup #47
spot a liar (Haiqa 146).pptx Technical writhing and presentation skills

spot a liar (Haiqa 146).pptx Technical writhing and presentation skills
Mca3020 advanced database management system
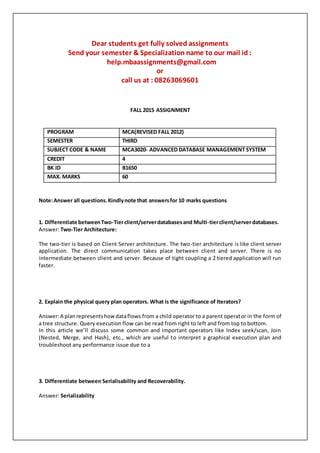
- 1. Dear students get fully solved assignments Send your semester & Specialization name to our mail id : help.mbaassignments@gmail.com or call us at : 08263069601 FALL 2015 ASSIGNMENT PROGRAM MCA(REVISED FALL 2012) SEMESTER THIRD SUBJECT CODE & NAME MCA3020- ADVANCED DATABASE MANAGEMENT SYSTEM CREDIT 4 BK ID B1650 MAX. MARKS 60 Note:Answer all questions.Kindlynote that answersfor 10 marks questions 1. Differentiate betweenTwo-Tierclient/serverdatabasesand Multi-tierclient/serverdatabases. Answer: Two-Tier Architecture: The two-tier is based on Client Server architecture. The two-tier architecture is like client server application. The direct communication takes place between client and server. There is no intermediate between client and server. Because of tight coupling a 2 tiered application will run faster. 2. Explain the physical query plan operators. What is the significance of Iterators? Answer:A planrepresentshowdataflows from a child operator to a parent operator in the form of a tree structure. Query execution flow can be read from right to left and from top to bottom. In this article we’ll discuss some common and important operators like Index seek/scan, Join (Nested, Merge, and Hash), etc., which are useful to interpret a graphical execution plan and troubleshoot any performance issue due to a 3. Differentiate between Serialisability and Recoverability. Answer: Serializability
- 2. Serializabilityisthe classical concurrencyscheme.This helps to ensures that a schedule with regard to performingexecutingconcurrenttransactionsisequivalenttoone that executes the transactions serially in some order. It assumes that all accesses 4. Discuss about Parallel query processing. How parallel-execution works? Answer: When Oracle runs SQL statements in parallel, multiple processes work together simultaneously to run a single SQL statement. By dividing the work necessary to run a statement amongmultiple processes, Oracle can run the statement more quickly than if only a single process ran it. This is called parallel execution or parallel processing. Parallel execution dramatically reduces response time for data-intensive operations on large databasestypicallyassociatedwithdecisionsupportsystems(DSS) anddatawarehouses.Symmetric multiprocessing (SMP), clustered systems, and 5. Differentiate between homogeneous and heterogeneous Database. Answer:A DDBMS maybe classifiedashomogeneousorheterogeneous.Ina homogeneous system, all sites use the same DBMS product. In a heterogeneous system, sites may run different DBMS products,whichneed not be based on the same underlying data model, and so the system may be composed of relational, network, hierarchical and object-oriented DBMSs. Homogeneous systems are much easier to design and 6. Write short notes on ODMG standards. What are the various components of ODMG-93? Answer: The ODMG standard builds upon the existing OMG, SQL-92, INCITS (formerly ANSI) programming language standards, and JavaSoft’s Java specification to define a framework for application portability between compliant data storage products. The standard’s functional components include an Object Model, an Object Definition Language, an Object Query Language, and Language Bindings to Java, C++, and Smalltalk. The two primary benefits of the ODMG Dear students get fully solved assignments Send your semester & Specialization name to our mail id : help.mbaassignments@gmail.com or call us at : 08263069601
