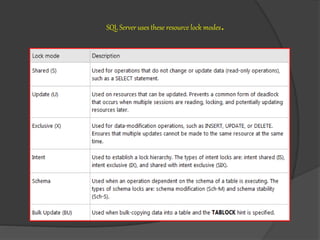
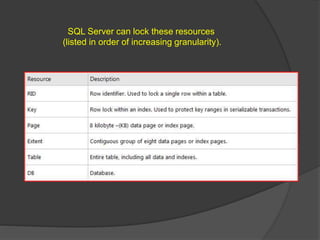
SQL Server uses different types of locks at varying levels of granularity to control access to resources by transactions. Locking resources at a finer-grained level, like individual rows, increases concurrency but requires more locks. Locking at a coarser level, like entire tables, reduces the number of required locks but also decreases concurrency by restricting access to the entire resource. SQL Server automatically determines the appropriate lock level needed based on the transaction's data access needs.