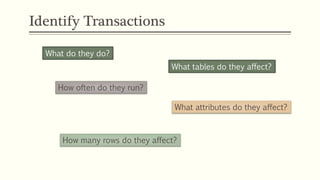
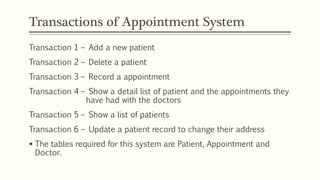
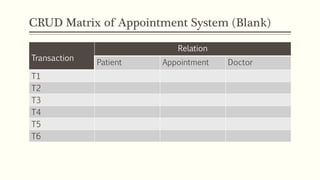
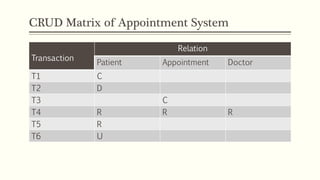
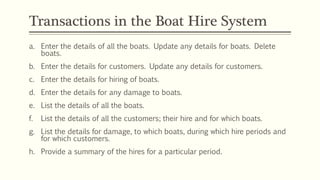
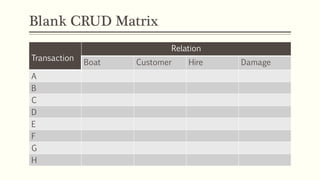
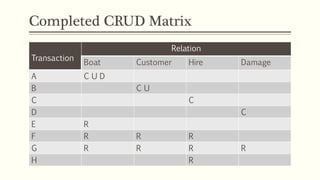
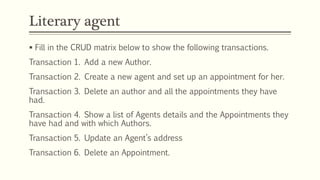
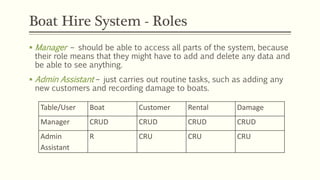
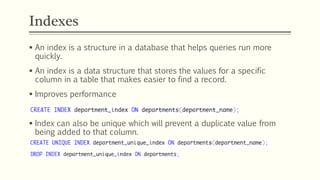
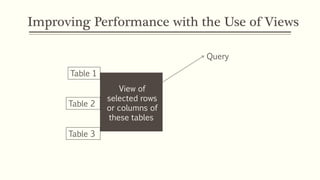
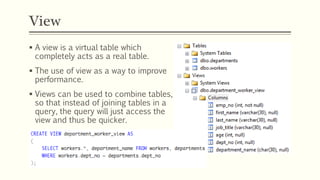
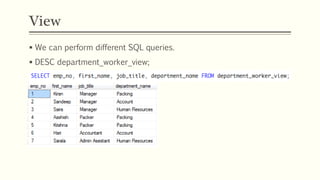
This document discusses database transactions and improving database performance. It defines transactions as operations on a database like create, retrieve, update and delete. Transactions can involve one or more of these operations on one or more tables. The document then provides examples of transactions for an appointment booking system and boat rental system. It discusses using indexes, views and denormalization to improve query performance by reducing the need to join tables. Permissions can be granted and revoked to users and roles to control database access.