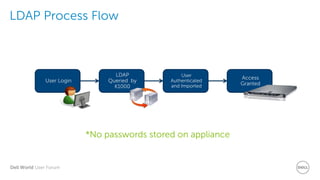
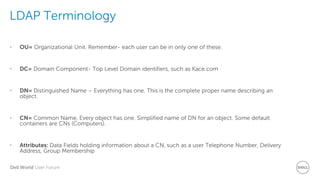
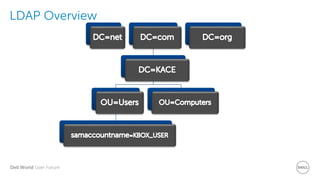
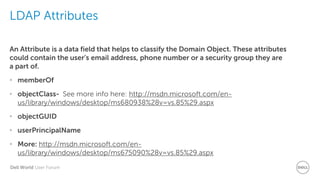
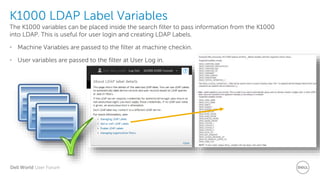
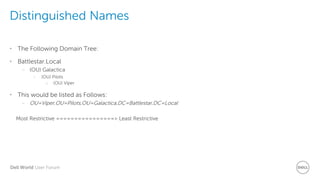
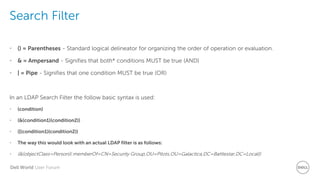
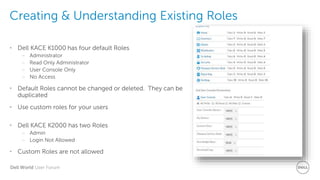
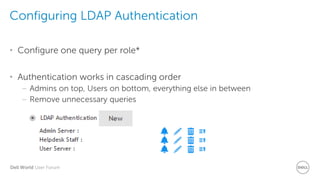
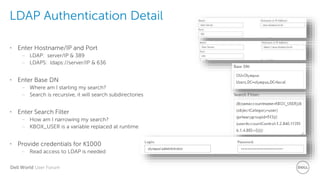
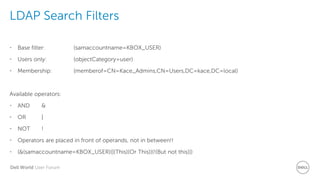
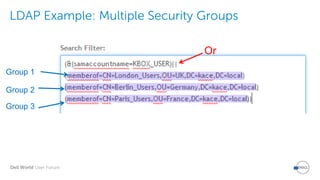
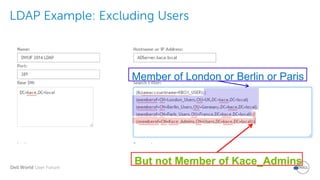
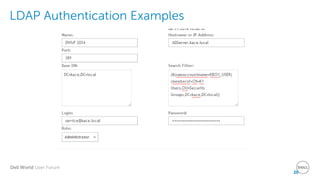
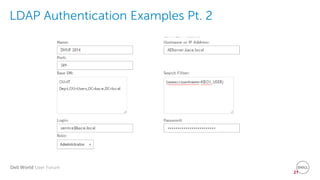
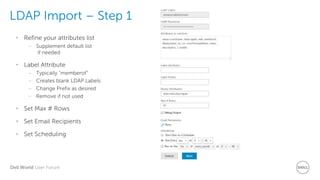
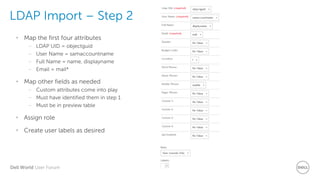
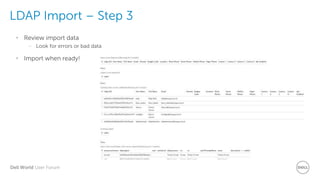
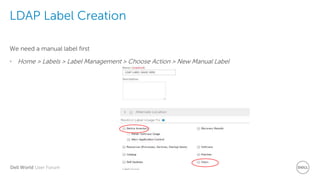
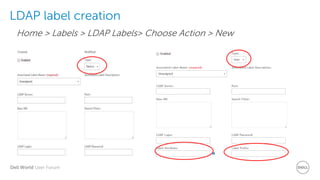
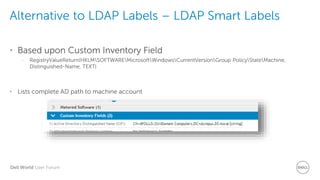
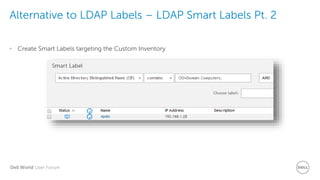
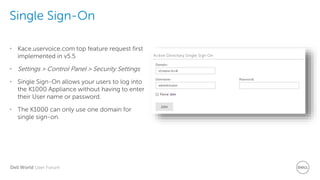
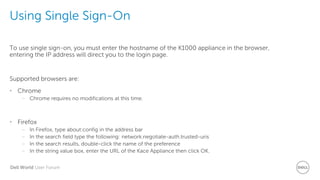
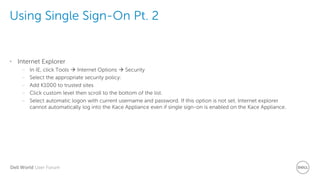
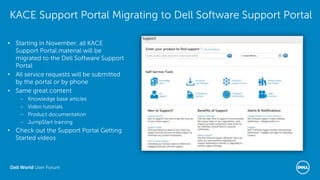
The document provides an overview of LDAP integration with K1000, including its benefits like streamlined authentication and user management. It details the process of configuring LDAP authentication, handling user roles, and creating LDAP labels for enhanced service desk operations. The document also highlights the single sign-on feature for user convenience and outlines important steps for setting up and managing LDAP attributes and labels.