Account credentials and session tokens are often not properly protected, allowing unauthorized access to user accounts. Flaws in authentication and session management can undermine security controls and privacy. Attackers exploit weaknesses like ineffective logout processes, password management, and session timeouts to hijack user sessions by stealing or guessing credentials and session tokens. Application developers must implement secure authentication, strong password policies, session management best practices like early session expiration, and logging to prevent such attacks.
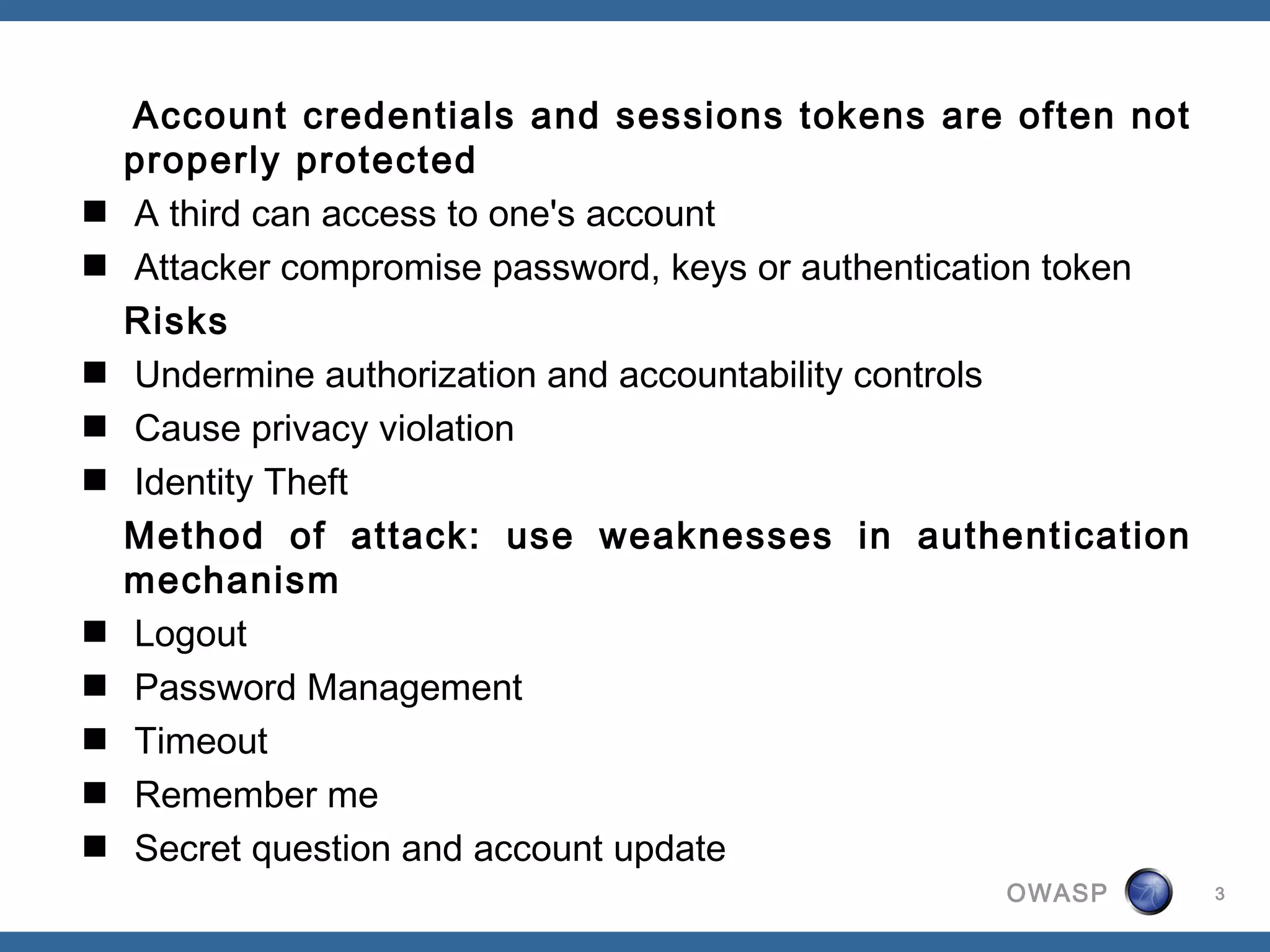
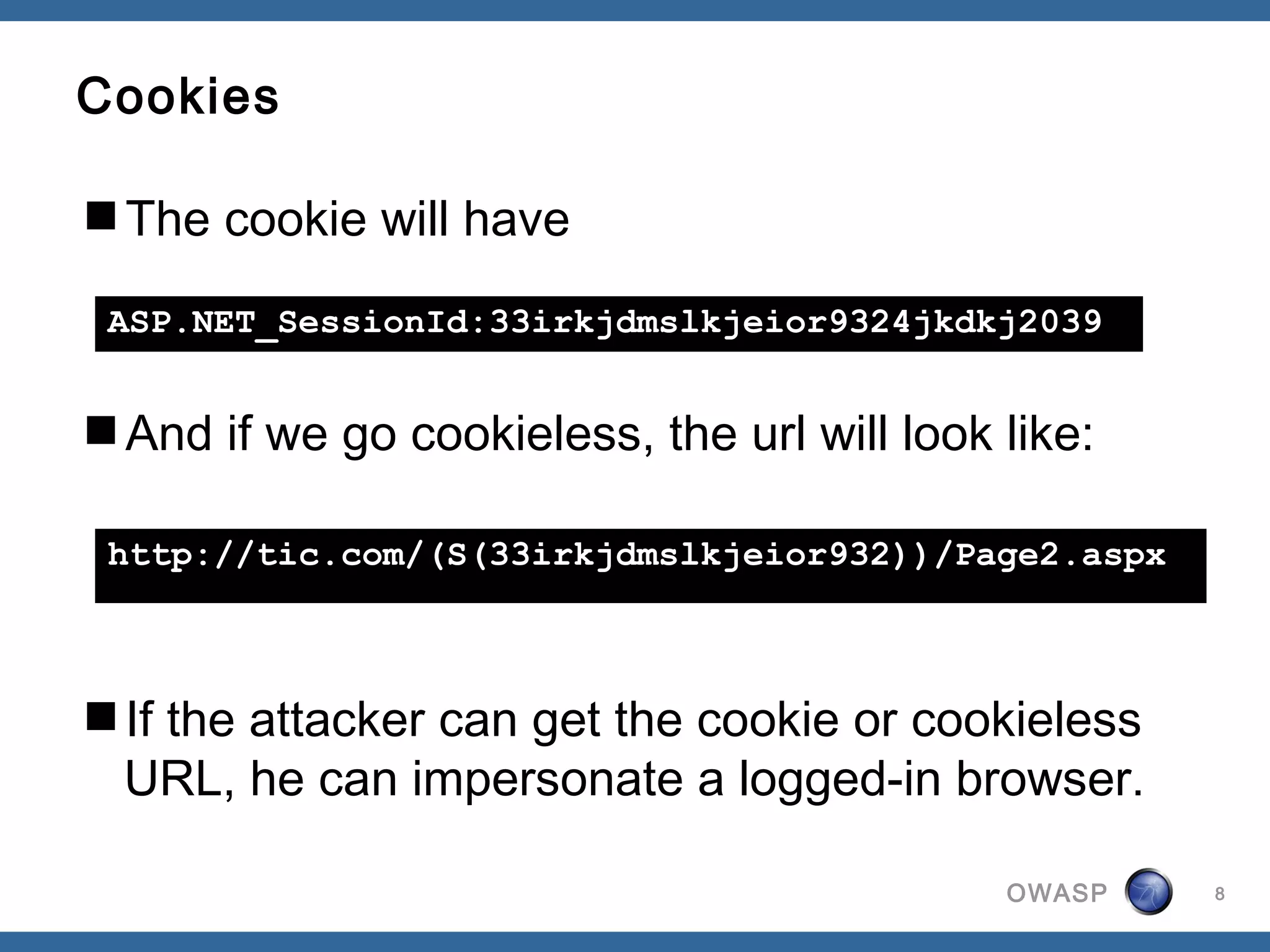
![Example Scenario
Login page with UserID/Password.
Another page with “Welcome, user”
How does 2nd page know user is logged in?
On login.aspx, we write a session object.
Session["Username"] = txtUsername.Text;
And on Page2.aspx, we read the session object.
username = (Session["Username"] ??
"Guest").ToString();
OWASP 7](https://image.slidesharecdn.com/a3-brokenauthenticationandsessionmanagement-120809025002-phpapp02/75/OWASP-Serbia-A3-broken-authentication-and-session-management-7-2048.jpg)