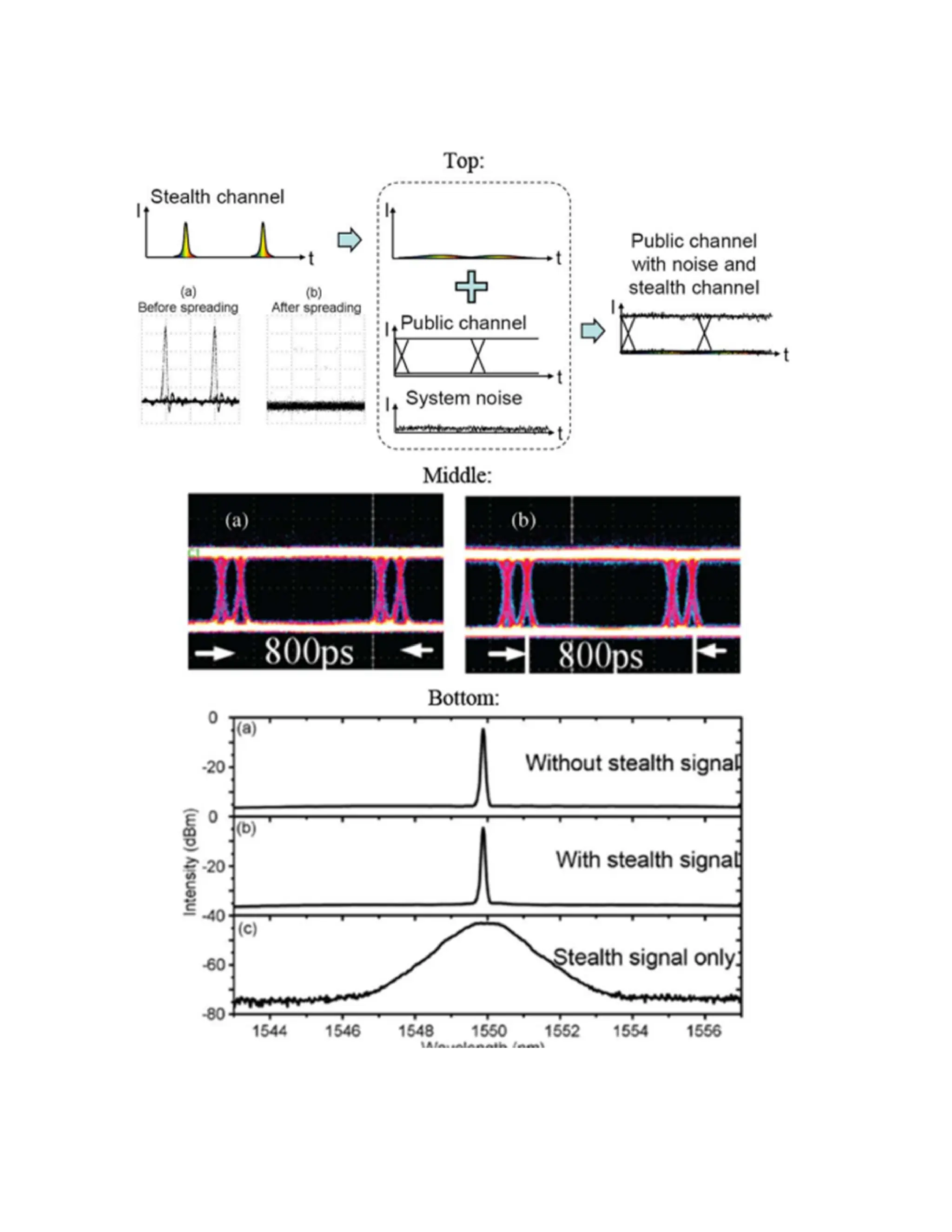
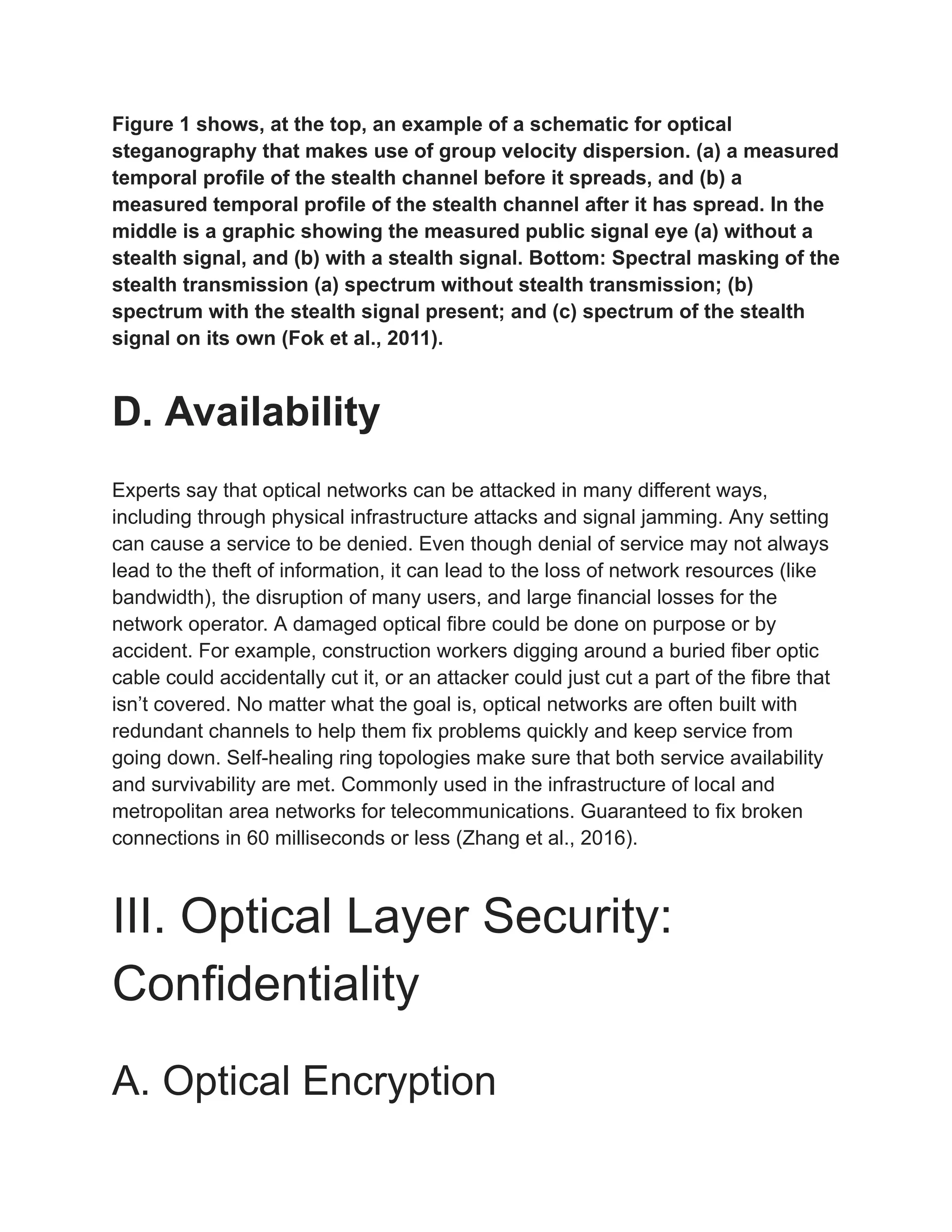
This document explores the physical layer security of optical networks, detailing various vulnerabilities like jamming, eavesdropping, and infrastructure attacks. It discusses innovative security measures such as optical steganography, encryption, and anti-jamming techniques that maintain high data rates while ensuring privacy and authentication. Researchers highlight how optical technology enhances network security through real-time data processing and the use of advanced codes for confidentiality and availability.