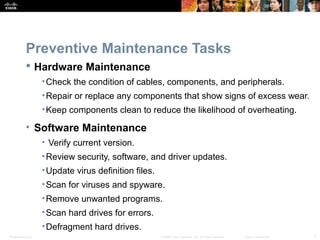
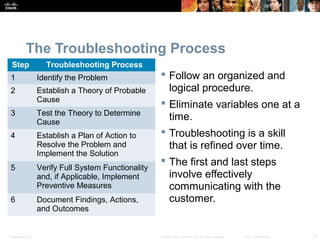
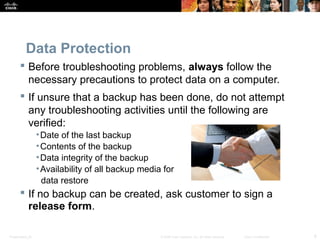
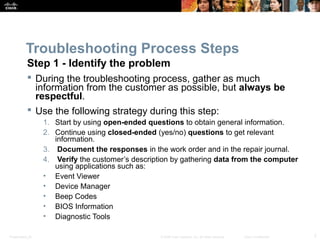
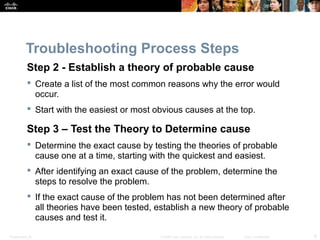
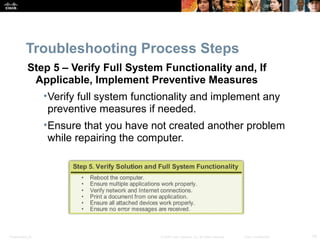
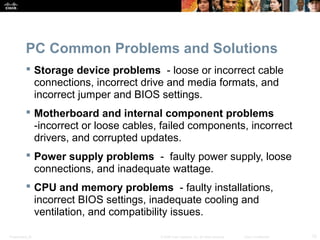
The document discusses preventive maintenance of IT systems. It describes the purpose and benefits of preventive maintenance as reducing downtime and repair costs while extending hardware lifespan. Preventive maintenance includes hardware tasks like cleaning components and software tasks like updating antivirus definitions. The troubleshooting process is outlined as six steps: identifying the problem, establishing the probable cause, testing theories, resolving the issue, verifying the solution, and documenting findings. Common computer problems and their solutions are also reviewed.