Report
Share
Download to read offline
Recommended
Day 2.2 ip addressing

http://www.cyberintelligents.in
info@cyberintelligents.in
https://www.facebook.com/cyberintelligents
https://in.linkedin.com/in/cyberintelligents/en
https://cyberintelligents.wordpress.com/
http://cyberintelligent.blogspot.in
+91 9876162698 +919988288019
http://trainingcyberintelligents.blogspot.com
https://cyberintelligentsnews.wordpress.com/
Recommended
Day 2.2 ip addressing

http://www.cyberintelligents.in
info@cyberintelligents.in
https://www.facebook.com/cyberintelligents
https://in.linkedin.com/in/cyberintelligents/en
https://cyberintelligents.wordpress.com/
http://cyberintelligent.blogspot.in
+91 9876162698 +919988288019
http://trainingcyberintelligents.blogspot.com
https://cyberintelligentsnews.wordpress.com/
IPv4

IPv4 (Internet Protocol Version 4). This silde will give u all information about IPv4.
Hope so you like it Freinds.
and
Sorry if i can fulfill ur wish in the given IPv4 Presentation.
Basics of IP Addressing

This Powerpoint Presentation will give you about basic IPv4 addressing and Subnetting of IPv4.
IPv4 addressing and subnetting

IP protocol version 4 description with the basic concept on subnetting and NAT.
About ip address

hey! everybody this is my third and last pps of this month and i ensure that this will definately guide you about ip address and its contain and what r all different kinds of ip r available with questions tags specified also. all thoes who u cannot find on any search engine u can get all stuff here!!!!!!
hope u loved it ???!@@@#
IP and MAC Address

IP addresses are not random. They are mathematically produced and allocated by the Internet Assigned Numbers Authority (IANA), a division of the Internet Corporation for Assigned Names and Numbers (ICANN).
More Related Content
What's hot
IPv4

IPv4 (Internet Protocol Version 4). This silde will give u all information about IPv4.
Hope so you like it Freinds.
and
Sorry if i can fulfill ur wish in the given IPv4 Presentation.
Basics of IP Addressing

This Powerpoint Presentation will give you about basic IPv4 addressing and Subnetting of IPv4.
IPv4 addressing and subnetting

IP protocol version 4 description with the basic concept on subnetting and NAT.
About ip address

hey! everybody this is my third and last pps of this month and i ensure that this will definately guide you about ip address and its contain and what r all different kinds of ip r available with questions tags specified also. all thoes who u cannot find on any search engine u can get all stuff here!!!!!!
hope u loved it ???!@@@#
What's hot (20)
Computer Networking: Internet Protcol (IP) and IP Addressing

Computer Networking: Internet Protcol (IP) and IP Addressing
Similar to Ip and mac addressing
IP and MAC Address

IP addresses are not random. They are mathematically produced and allocated by the Internet Assigned Numbers Authority (IANA), a division of the Internet Corporation for Assigned Names and Numbers (ICANN).
IP Address in data communication and computer notework.ppt

IP Address in data communication and computer notework.ppt
-LAB 3-IP Addressing and Subnettinncgbg.pdf

Nodes and Links: Nodes are devices on a network (such as computers or routers) while links are the physical or logical
ipv4 (internet protocol version 4) 

This ppt for a seminar purpose in ipv4 and i uplaod this ppt only for education purpose.i make this ppt to choose many referances.
Lesson 13University of the CumberlandsProfessor Dr. I.docx

Lesson 13
University of the Cumberlands
Professor: Dr. Irvin R. Heard
Course: ISOL 634 Physical Security (20-21)
Reading AssignmentChapter 17
Individual Project 13
Identify and discuss the seven layers of the Open System Interconnection (OSI) model and their importance on TCP/IP operation.
Minimum two pages.
Helpful topics to research:OSI LayersHow TCP/IP WorksTCP/IP Operates on Open Systems Interconnection Levels 3 (IP) and 4 (TCP) TCP/UDP/RTP User Datagram Protocol TCP/IP Address Schemes
Open Systems Interconnection (OSI) Reference ModelLayer 7--Application layerLayer 6--Presentation layerLayer 5--Session layerLayer 4--Transport layerLayer 3--Network layerLayer 2--Data Link layerLayer 1--Physical layer
OSI – Upper and Lower LevelsThe seven layers of the OSI reference model can be divided into two categories: upper layers and lower layers.The upper layers of the OSI model deal with application issues and generally are implemented only in software. The highest layer, application, is closest to the end user. Both users and application-layer processes interact with software applications that contain a communications component. The term upper layer is sometimes used to refer to any layer above another layer in the OSI model.The lower layers of the OSI model handle data transport issues. The physical layer and data-link layer are implemented in hardware and software. The other lower layers generally are implemented only in software. The lowest layer, the physical layer, is closest to the physical network medium (the network cabling, for example, and is responsible for actually placing information on the medium.
TCP/IP
The networking industry uses the OSI seven layer model as a standard, however before that was a standards TCP/IP was being developed (OSI was just completed first and adopted). Both models have similar goals. Its often to see developers apply OSI terminology to TCP/IP.
Similarities
The most compatible aspects at the Transport and Internet layers (called the Network in OSI)
TCP/UDP/RTP
Click the titles to review resourcesTransportation Protocols: UDP,TCP & RTPTeach Yourself TCP/IP in 24 hrs (Book)
TCP/IP Address SchemesTCP/IP includes an Internet addressing scheme that allows users and applications to identify a specific network or host to communicate with. An Internet address works like a postal address, allowing data to be routed to the chosen destination. TCP/IP provides standards for assigning addresses to networks, subnetworks, hosts, and sockets, and for using special addresses for broadcasts and local loopback.
Internet addresses are made up of a network address and a host (or local) address. This two-part address allows a sender to specify the network as well as a specific host on the network. A unique, official network address is assigned to each network when it connects to other Internet networks. However, if a local network is not going to connect to other Internet networks, it can be assigned any ...
IP Address

IP Address is a unique identification given to Host, network device, server for data communication. IP
Address stand for Internet Protocol address, it is an addressing scheme used to identify a system on a
network. It is a unique address that certain electronic devices currently use to communicate with each
other on a network using internet protocol.
chapter 6.pptx

This is my work it is very good ppt ic yiu read this book you will get better knowledge about computer system I am a fresh electrical engineering graduate from Gondar university Institute of electrical and computer engineering intending to continue my development as communication engineer. In terms of results and objectives, I am enthusiastic and hard working. I am mature enough for the position because I have taken the basic communication engineering courses such as introduction to communication system , digital communication system, advanced computer system, switching and intelligent network ,
Electrical power system ,electrical work shop I,&II ,electrical lab 1,2,3,4, programing course math lab++,java, assembly language, introduction to control system, digital signal processing, signal and system analysis ,fundamental of electrical circuit, electrical measurement ,embedded system, I am familiar with cisco configuration,multism.organized a team of four students for thesis project
Projects
a four-month internship experience on antenna design for Ethio telecom
a six-month thesis project experience on performance analysis of aquastic echo cancellation in teleconference
semester project FM transmitter practically
university network design using sisco
online shopping using graphical user interface
other mini project such as QAM,error detection and correction using humming algorism Transcripts are records of students’ academic performance. They are the most valuable private
and sensitive documents. Utmost care is taken in their recording, storing and issuance. The
following is a set of regulation governing issuance of transcripts.
a. No student records are shown or given to a third party without the written
consent of the student. The University College may make discretionary
exceptions to this.
b. No transcripts will be issued for requests made through third parties ,that is
representatives, friends or relatives, agencies, etc. in exceptional cases
transcripts are given to third parties if the third party meets the following
conditions :
i.
The third party must carry a power of attorney;
ii. The third party does not demand that the transcripts be given to him/her;
iii. The third party must sign an affidavit to the effect that it assumes full
responsibilities for any disputes arising from the possibility that the
Registrar’s office is misled into sending transcripts to persons who have
no legal claims over the document.
c. All students who have dropped out, withdrawn or graduated from the
University College must present an official clearance sheet to get
transcripts and other services. Third parties of such students must present
clearance sheets of students they represent. The official clearance form or its
equivalent clears the students from all their financial and other obligations to
the University College.
d. Transcripts given by the Registrar Office are of two kinds: student copy and
official copy. The student copy is a trans
ip addressing & routing

The IP addresses used to identify systems on a TCP/IP network. The IP address is an absolute identifier of both the individual machine and the network on which it resides.
Every IP datagram packet transmitted over a TCP/IP network contains the IP addresses of the source system that generated it and the destination system for which it’s intended in its IP header.
Similar to Ip and mac addressing (20)
IP Address in data communication and computer notework.ppt

IP Address in data communication and computer notework.ppt
Lesson 13University of the CumberlandsProfessor Dr. I.docx

Lesson 13University of the CumberlandsProfessor Dr. I.docx
Recently uploaded
The Challenger.pdf DNHS Official Publication

Read| The latest issue of The Challenger is here! We are thrilled to announce that our school paper has qualified for the NATIONAL SCHOOLS PRESS CONFERENCE (NSPC) 2024. Thank you for your unwavering support and trust. Dive into the stories that made us stand out!
Mule 4.6 & Java 17 Upgrade | MuleSoft Mysore Meetup #46

Mule 4.6 & Java 17 Upgrade | MuleSoft Mysore Meetup #46
Event Link:-
https://meetups.mulesoft.com/events/details/mulesoft-mysore-presents-exploring-gemini-ai-and-integration-with-mulesoft/
Agenda
● Java 17 Upgrade Overview
● Why and by when do customers need to upgrade to Java 17?
● Is there any immediate impact to upgrading to Mule Runtime 4.6 and beyond?
● Which MuleSoft products are in scope?
For Upcoming Meetups Join Mysore Meetup Group - https://meetups.mulesoft.com/mysore/
YouTube:- youtube.com/@mulesoftmysore
Mysore WhatsApp group:- https://chat.whatsapp.com/EhqtHtCC75vCAX7gaO842N
Speaker:-
Shubham Chaurasia - https://www.linkedin.com/in/shubhamchaurasia1/
Priya Shaw - https://www.linkedin.com/in/priya-shaw
Organizers:-
Shubham Chaurasia - https://www.linkedin.com/in/shubhamchaurasia1/
Giridhar Meka - https://www.linkedin.com/in/giridharmeka
Priya Shaw - https://www.linkedin.com/in/priya-shaw
Shyam Raj Prasad-
https://www.linkedin.com/in/shyam-raj-prasad/
How to Split Bills in the Odoo 17 POS Module

Bills have a main role in point of sale procedure. It will help to track sales, handling payments and giving receipts to customers. Bill splitting also has an important role in POS. For example, If some friends come together for dinner and if they want to divide the bill then it is possible by POS bill splitting. This slide will show how to split bills in odoo 17 POS.
Instructions for Submissions thorugh G- Classroom.pptx

This presentation provides a briefing on how to upload submissions and documents in Google Classroom. It was prepared as part of an orientation for new Sainik School in-service teacher trainees. As a training officer, my goal is to ensure that you are comfortable and proficient with this essential tool for managing assignments and fostering student engagement.
The approach at University of Liverpool.pptx

How libraries can support authors with open access requirements for UKRI funded books
Wednesday 22 May 2024, 14:00-15:00.
GIÁO ÁN DẠY THÊM (KẾ HOẠCH BÀI BUỔI 2) - TIẾNG ANH 8 GLOBAL SUCCESS (2 CỘT) N...

GIÁO ÁN DẠY THÊM (KẾ HOẠCH BÀI BUỔI 2) - TIẾNG ANH 8 GLOBAL SUCCESS (2 CỘT) N...Nguyen Thanh Tu Collection
https://app.box.com/s/4hfk1xwgxnova7f4dm37birdzflj806wEthnobotany and Ethnopharmacology ......

Ethnobotany and Ethnopharmacology:
Ethnobotany in herbal drug evaluation,
Impact of Ethnobotany in traditional medicine,
New development in herbals,
Bio-prospecting tools for drug discovery,
Role of Ethnopharmacology in drug evaluation,
Reverse Pharmacology.
TESDA TM1 REVIEWER FOR NATIONAL ASSESSMENT WRITTEN AND ORAL QUESTIONS WITH A...

TESDA TM1 REVIEWER FOR NATIONAL ASSESSMENT WRITTEN AND ORAL QUESTIONS WITH ANSWERS.
Operation Blue Star - Saka Neela Tara

Operation “Blue Star” is the only event in the history of Independent India where the state went into war with its own people. Even after about 40 years it is not clear if it was culmination of states anger over people of the region, a political game of power or start of dictatorial chapter in the democratic setup.
The people of Punjab felt alienated from main stream due to denial of their just demands during a long democratic struggle since independence. As it happen all over the word, it led to militant struggle with great loss of lives of military, police and civilian personnel. Killing of Indira Gandhi and massacre of innocent Sikhs in Delhi and other India cities was also associated with this movement.
special B.ed 2nd year old paper_20240531.pdf

Instagram:-
https://instagram.com/special_education_needs_01?igshid=YmMyMTA2M2Y=
WhatsApp:-
https://chat.whatsapp.com/JVakNIYlSV94x7bwunO3Dc
YouTube:-
https://youtube.com/@special_education_needs
Teligram :- https://t.me/special_education_needs
Slide Shere :-
https://www.slideshare.net/shabnambano20?utm_campaign=profiletracking&utm_medium=sssite&utm_source=ssslideview
Polish students' mobility in the Czech Republic

Polish students mobility to the Czech Republic within eTwinning project "Medieval adventures with Marco Polo"
The geography of Taylor Swift - some ideas

Geographical themes connected with Taylor Swift's ERAS tour - coming to the UK in June 2024
Model Attribute Check Company Auto Property

In Odoo, the multi-company feature allows you to manage multiple companies within a single Odoo database instance. Each company can have its own configurations while still sharing common resources such as products, customers, and suppliers.
Unit 8 - Information and Communication Technology (Paper I).pdf

This slides describes the basic concepts of ICT, basics of Email, Emerging Technology and Digital Initiatives in Education. This presentations aligns with the UGC Paper I syllabus.
Thesis Statement for students diagnonsed withADHD.ppt

Presentation required for the master in Education.
Unit 2- Research Aptitude (UGC NET Paper I).pdf

This slide describes the research aptitude of unit 2 in the UGC NET paper I.
Recently uploaded (20)
Mule 4.6 & Java 17 Upgrade | MuleSoft Mysore Meetup #46

Mule 4.6 & Java 17 Upgrade | MuleSoft Mysore Meetup #46
Instructions for Submissions thorugh G- Classroom.pptx

Instructions for Submissions thorugh G- Classroom.pptx
GIÁO ÁN DẠY THÊM (KẾ HOẠCH BÀI BUỔI 2) - TIẾNG ANH 8 GLOBAL SUCCESS (2 CỘT) N...

GIÁO ÁN DẠY THÊM (KẾ HOẠCH BÀI BUỔI 2) - TIẾNG ANH 8 GLOBAL SUCCESS (2 CỘT) N...
TESDA TM1 REVIEWER FOR NATIONAL ASSESSMENT WRITTEN AND ORAL QUESTIONS WITH A...

TESDA TM1 REVIEWER FOR NATIONAL ASSESSMENT WRITTEN AND ORAL QUESTIONS WITH A...
Basic phrases for greeting and assisting costumers

Basic phrases for greeting and assisting costumers
Unit 8 - Information and Communication Technology (Paper I).pdf

Unit 8 - Information and Communication Technology (Paper I).pdf
Thesis Statement for students diagnonsed withADHD.ppt

Thesis Statement for students diagnonsed withADHD.ppt
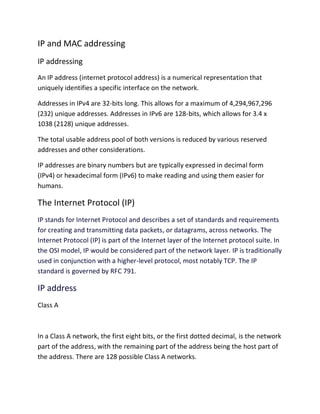
Ip and mac addressing
- 1. IP and MAC addressing IP addressing An IP address (internet protocol address) is a numerical representation that uniquely identifies a specific interface on the network. Addresses in IPv4 are 32-bits long. This allows for a maximum of 4,294,967,296 (232) unique addresses. Addresses in IPv6 are 128-bits, which allows for 3.4 x 1038 (2128) unique addresses. The total usable address pool of both versions is reduced by various reserved addresses and other considerations. IP addresses are binary numbers but are typically expressed in decimal form (IPv4) or hexadecimal form (IPv6) to make reading and using them easier for humans. The Internet Protocol (IP) IP stands for Internet Protocol and describes a set of standards and requirements for creating and transmitting data packets, or datagrams, across networks. The Internet Protocol (IP) is part of the Internet layer of the Internet protocol suite. In the OSI model, IP would be considered part of the network layer. IP is traditionally used in conjunction with a higher-level protocol, most notably TCP. The IP standard is governed by RFC 791. IP address Class A In a Class A network, the first eight bits, or the first dotted decimal, is the network part of the address, with the remaining part of the address being the host part of the address. There are 128 possible Class A networks.
- 2. 0.0.0.0 to 127.0.0.0 However, any address that begins with 127. is considered a loopback address. Example for a Class A IP address: 2.134.213.2 Class B In a Class B network, the first 16 bits are the network part of the address. All Class B networks have their first bit set to 1 and the second bit set to 0. In dotted decimal notation, that makes 128.0.0.0 to 191.255.0.0 as Class B networks. There are 16,384 possible Class B networks. Example for a Class B IP address: 135.58.24.17 Class C In a Class C network, the first two bits are set to 1, and the third bit is set to 0. That makes the first 24 bits of the address the network address and the remainder as the host address. Class C network addresses range from 192.0.0.0 to 223.255.255.0. There are over 2 million possible Class C networks. Example for a Class C IP address: 192.168.178.1 Class D Class D addresses are used for multicasting applications. Unlike the previous classes, the Class D is not used for "normal" networking operations. Class D addresses have their first three bits set to “1” and their fourth bit set to “0”. Class D addresses are 32-bit network addresses, meaning that all the values within the range of 224.0.0.0 – 239.255.255.255 are used to uniquely identify multicast
- 3. groups. There are no host addresses within the Class D address space, since all the hosts within a group share the group’s IP address for receiver purposes. Example for a Class D IP address: 227.21.6.173 Class E networks are defined by having the first four network address bits as 1. That encompasses addresses from 240.0.0.0 to 255.255.255.255. While this class is reserved, its usage was never defined. As a result, most network implementations discard these addresses as illegal or undefined. The exception is 255.255.255.255, which is used as a broadcast address. Example for a Class D IP address: 243.164.89.28 MAC address Stands for "Media Access Control Address," and no, it is not related Apple Macintosh computers. A MAC address is a hardware identification number that uniquely identifies each device on a network. The MAC address is manufactured into every network card, such as an Ethernet card or Wi-Fi card, and therefore cannot be changed. Because there are millions of networkable devices in existence, and each device needs to have a unique MAC address, there must be a very wide range of possible addresses. For this reason, MAC addresses are made up of six two-digit hexadecimal numbers, separated by colons. For example, an Ethernet card may have a MAC address of 00:0d:83:b1:c0:8e. Fortunately, you do not need to know this address, since it is automatically recognized by most networks.