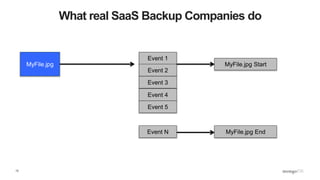
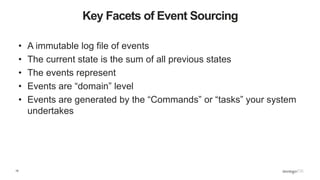
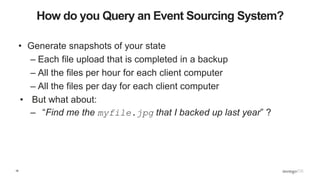
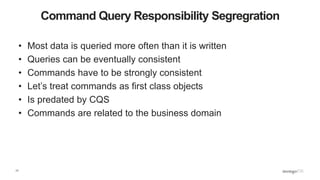
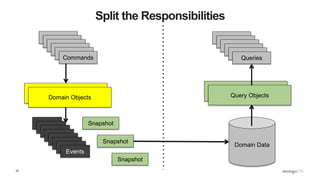
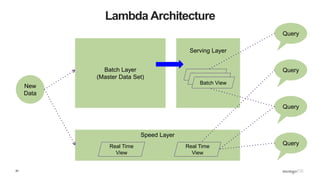
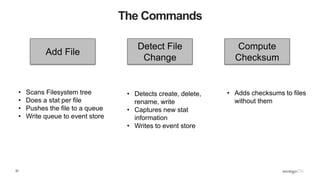
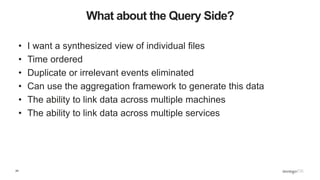
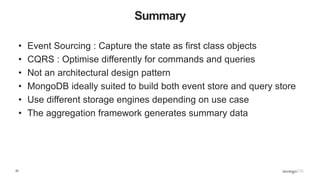
The document provides an introduction to Command Query Responsibility Segregation (CQRS) and event sourcing, explaining their significance in managing state and data in applications. It emphasizes the utility of event sourcing in various domains by tracking events and their states, while CQRS optimizes the handling of commands and queries. The author notes that these concepts are not strict design patterns but rather useful methodologies that can be implemented as needed.