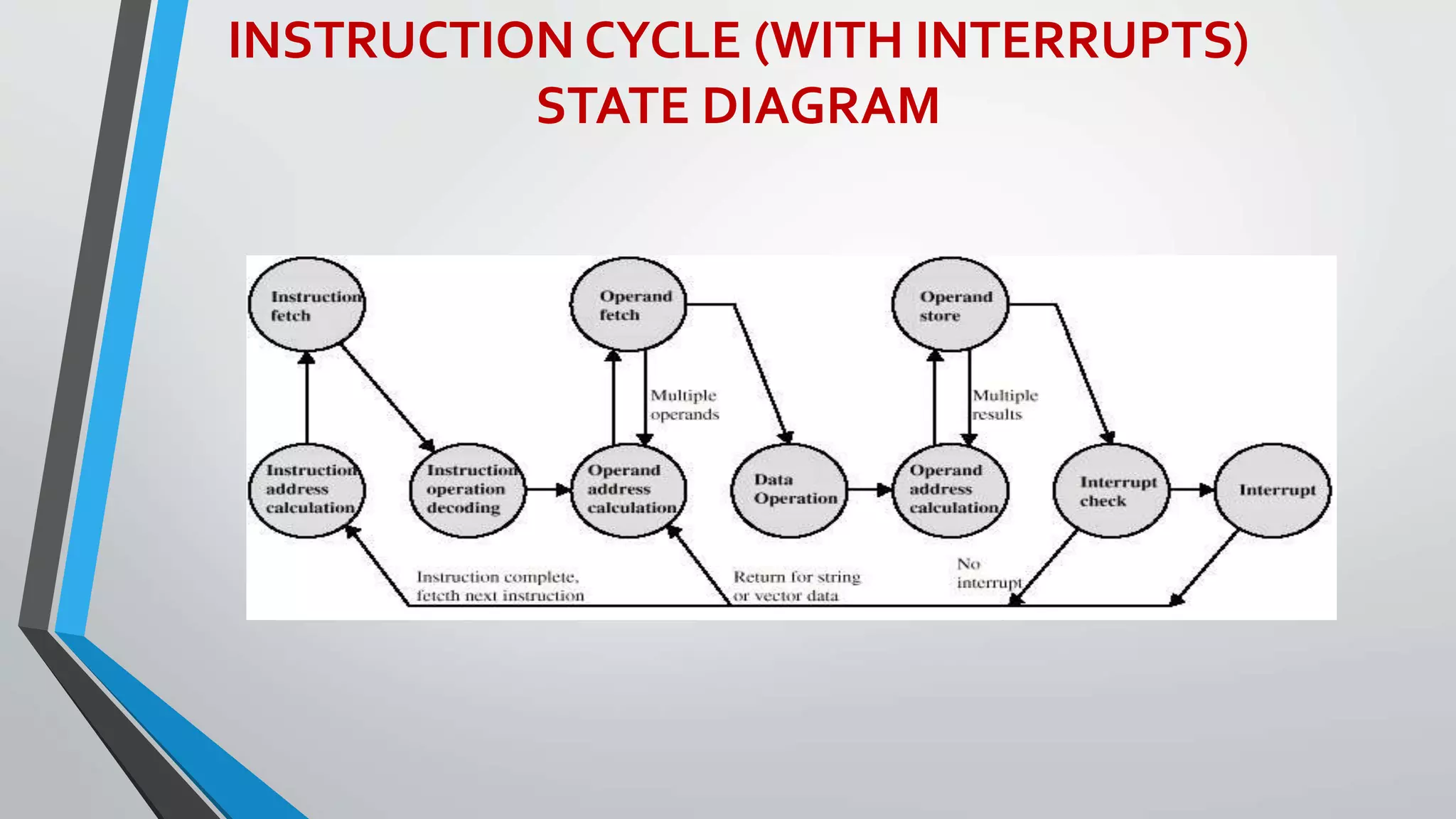
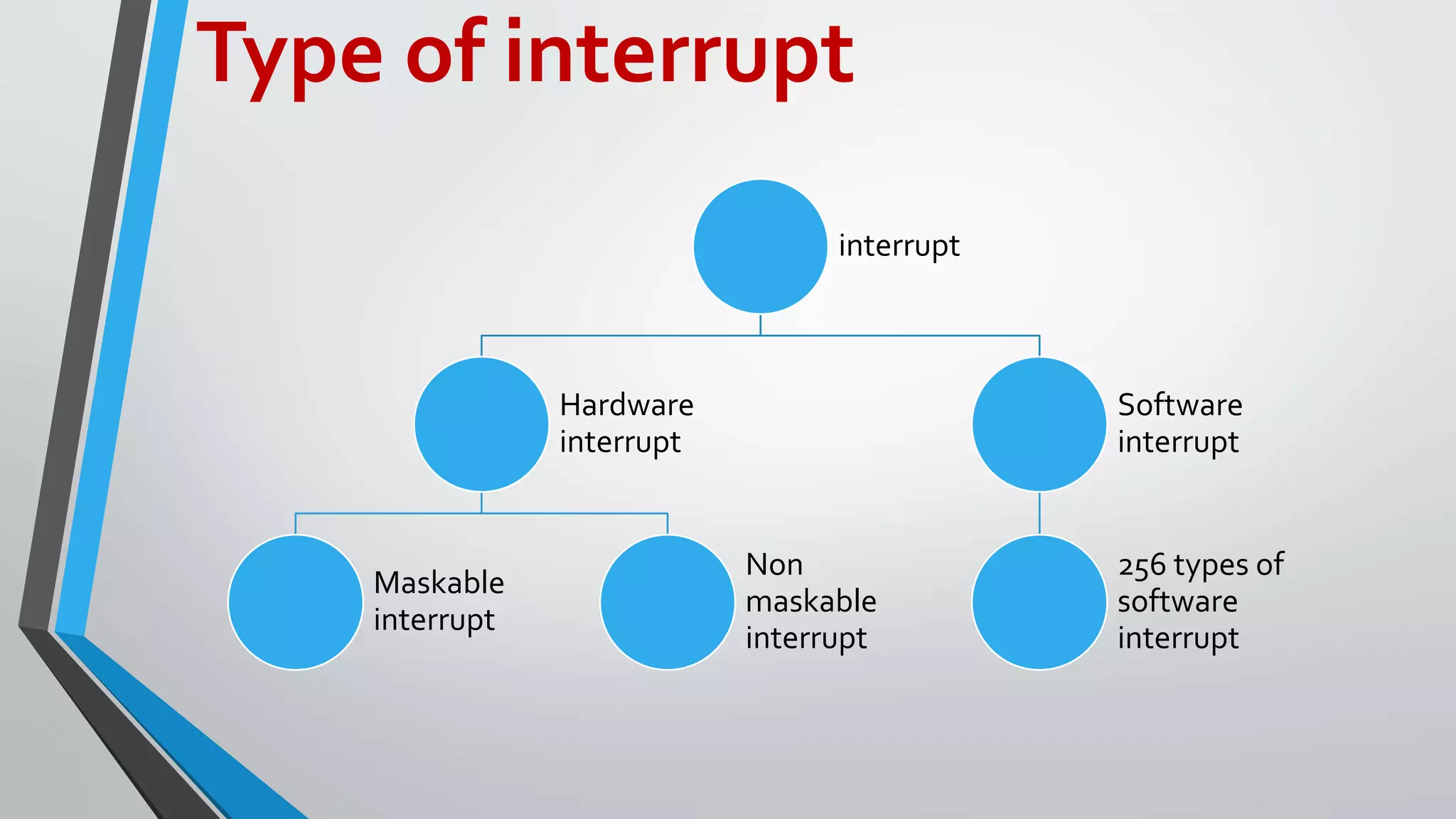
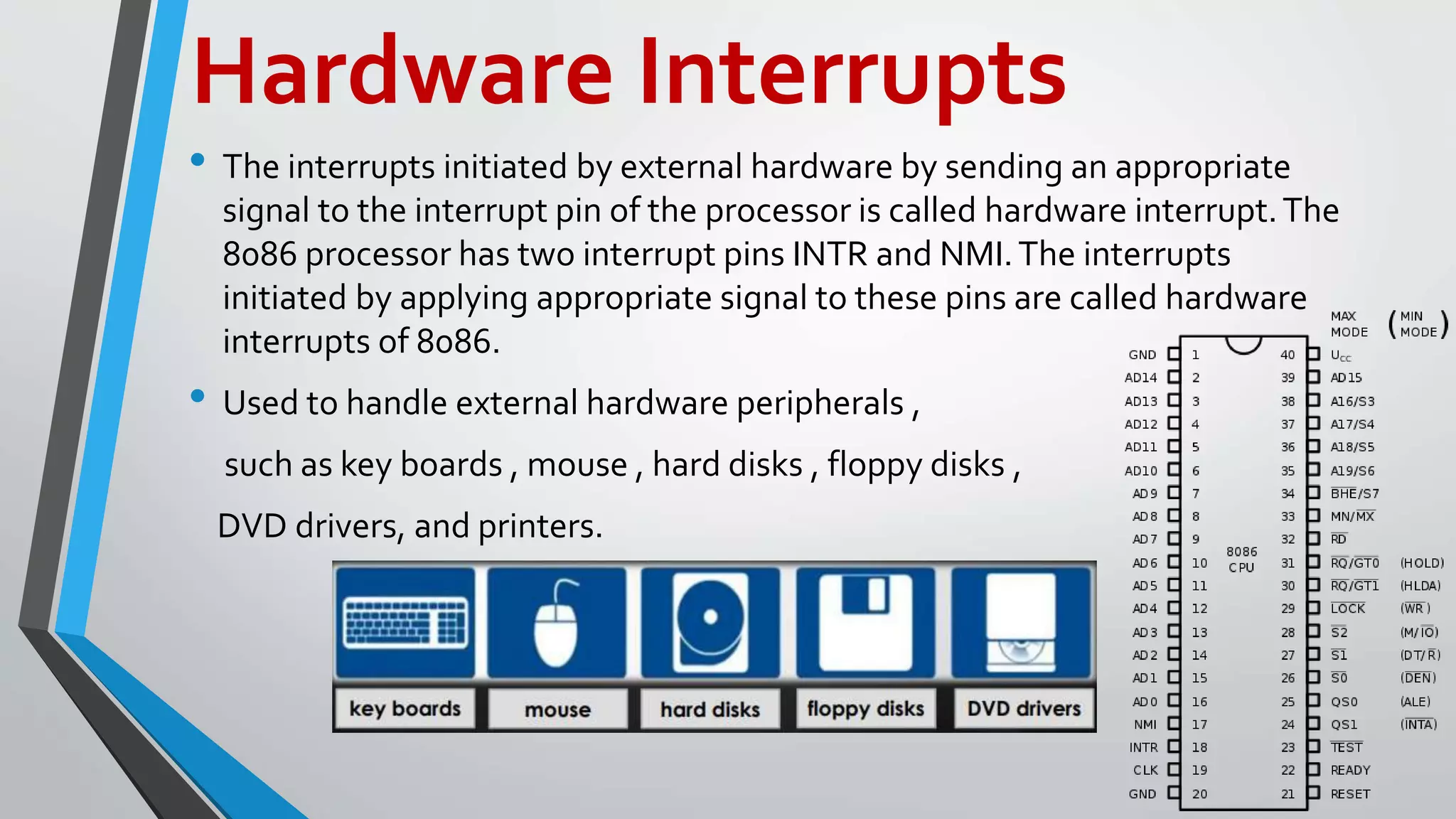
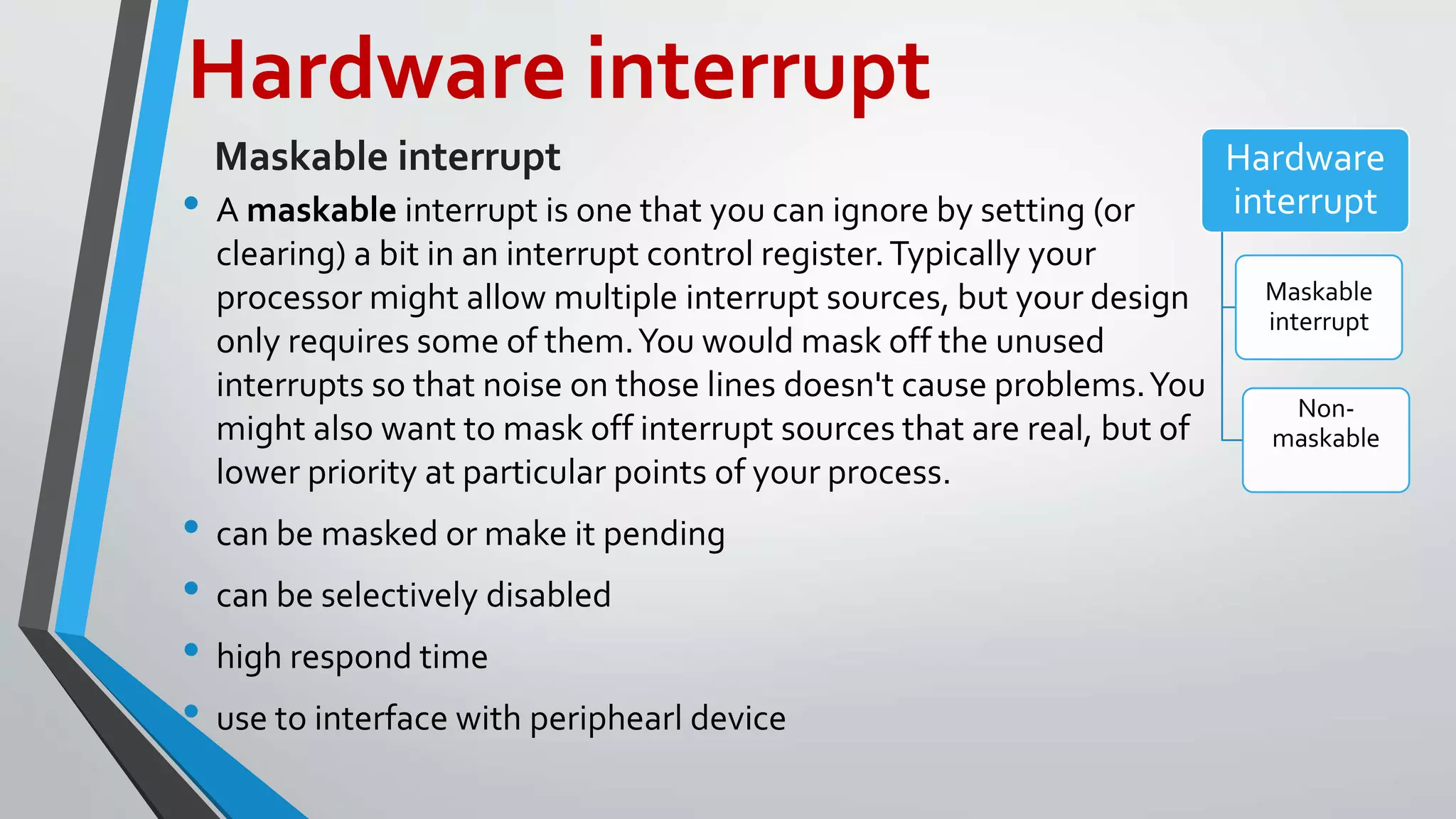
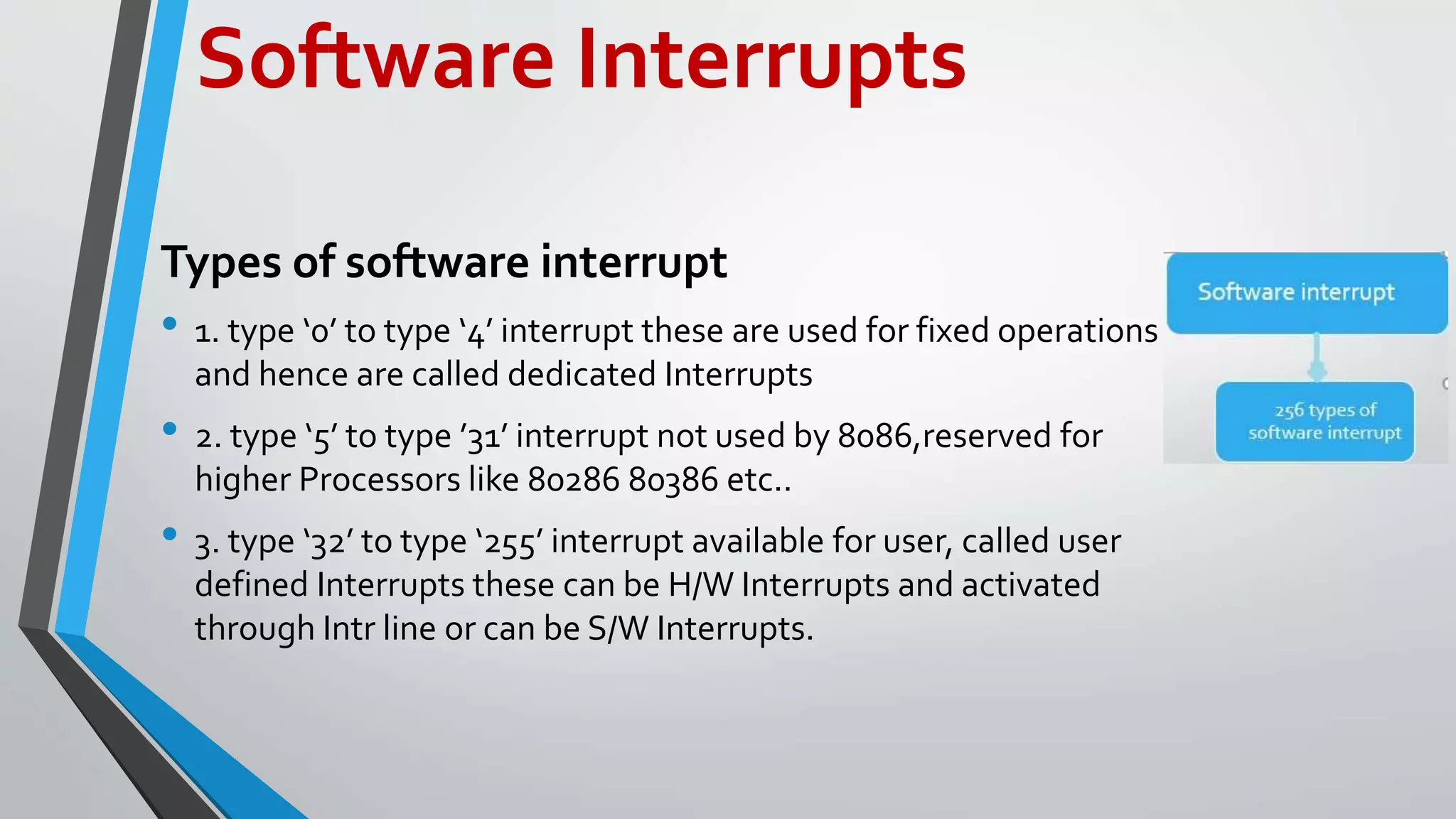
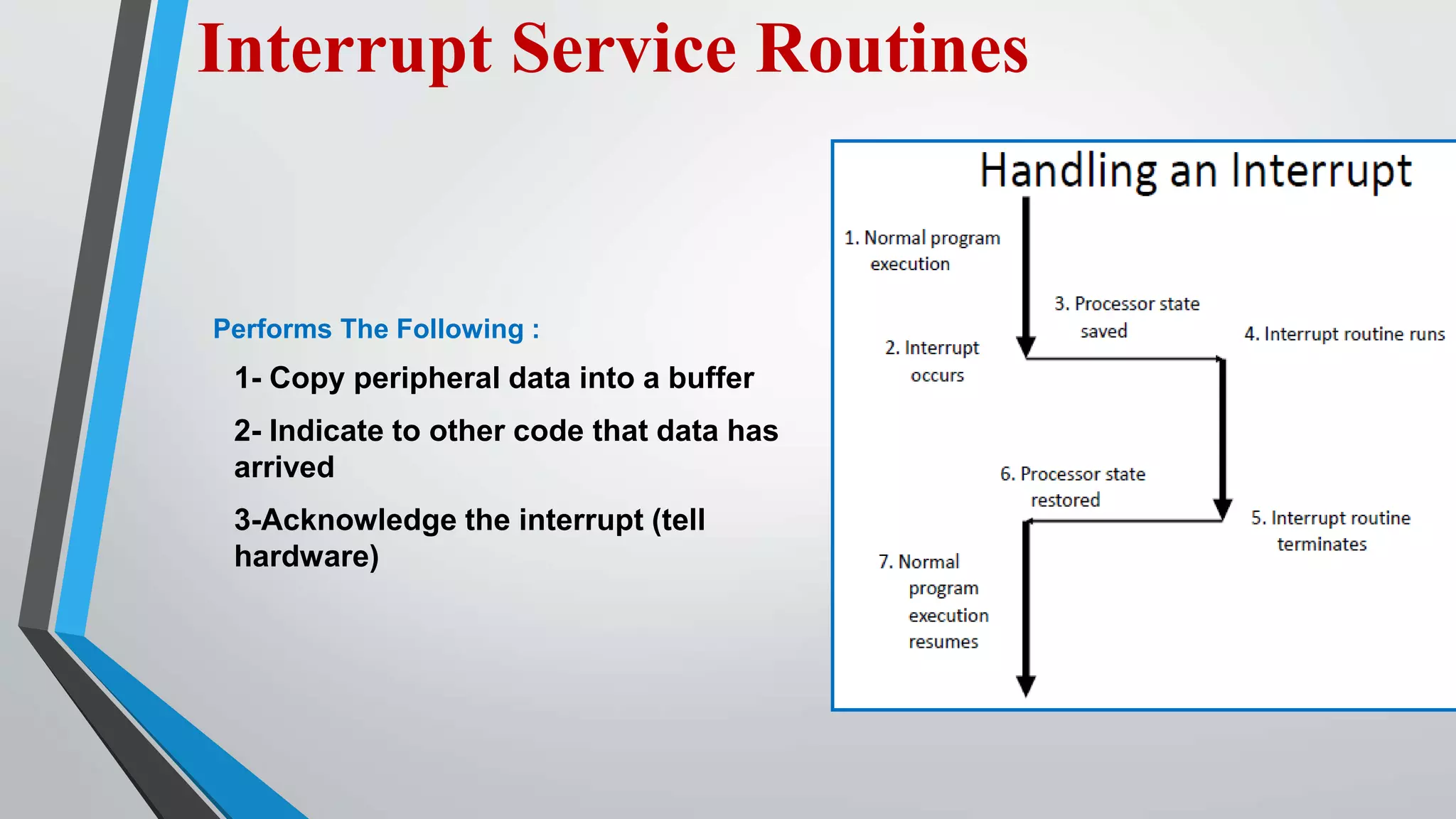
This document discusses interrupts in a computer system. It defines interrupts as events that break the normal sequence of instruction execution. There are hardware interrupts triggered by external devices and software interrupts triggered by internal instructions. The processor services interrupts by saving its state, jumping to an interrupt service routine, and then restoring its context to resume the original program. Interrupts allow the processor to efficiently service multiple devices simultaneously.