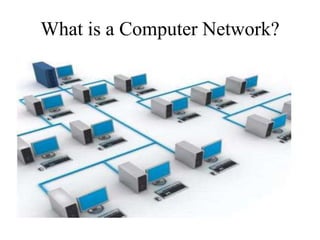
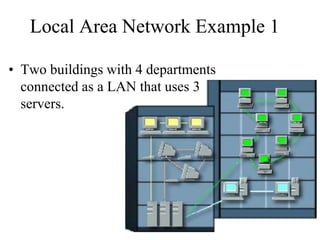
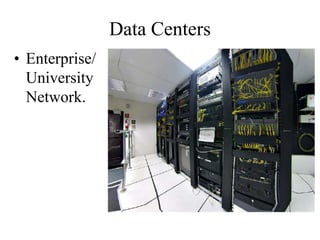
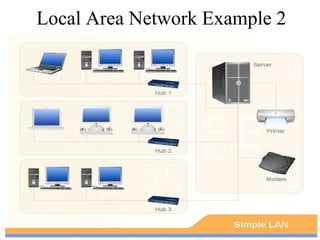
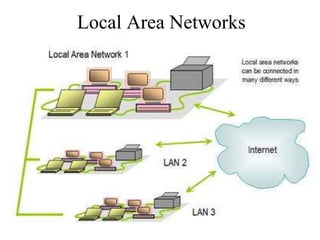
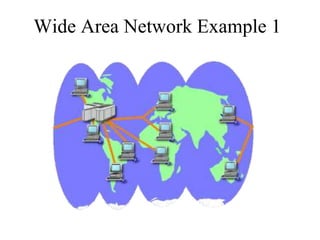
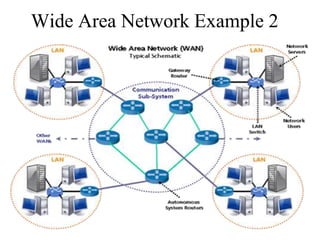
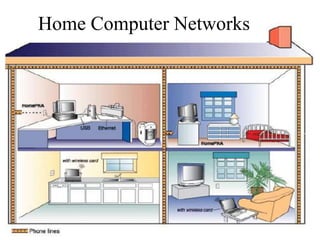
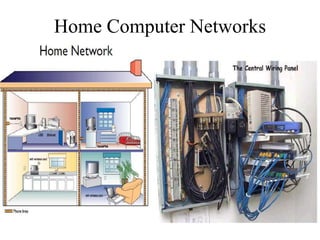
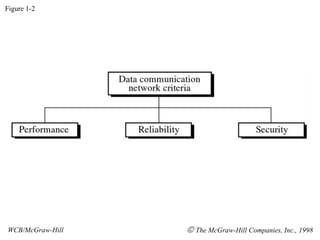
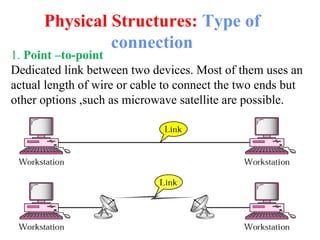
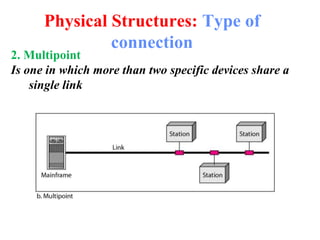
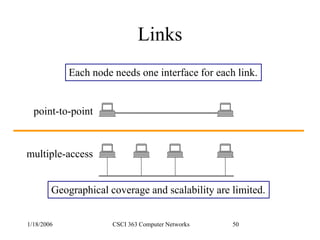
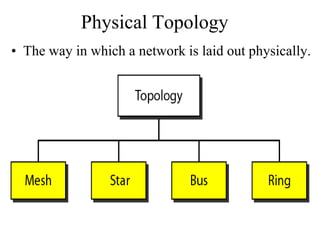
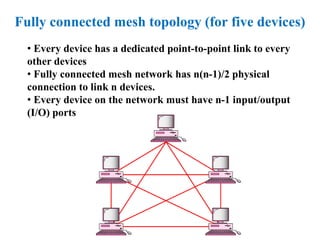
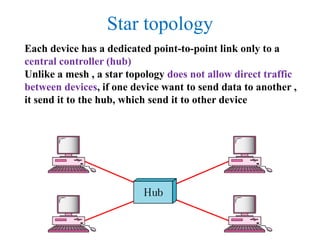
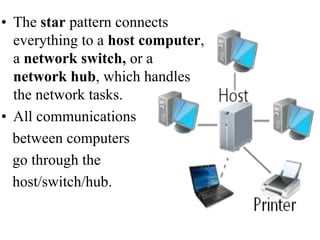
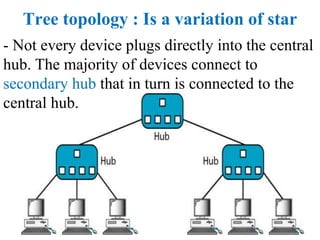
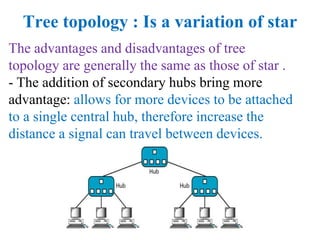
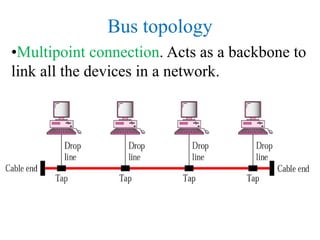
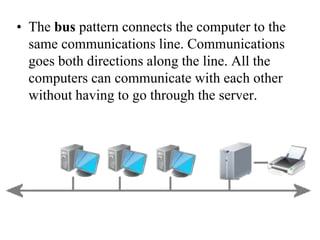
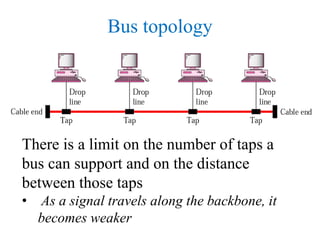
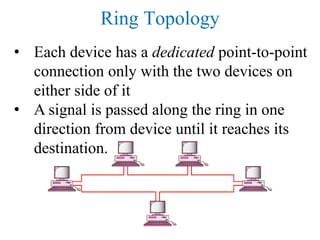
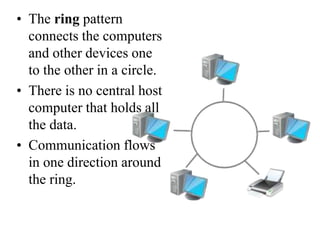
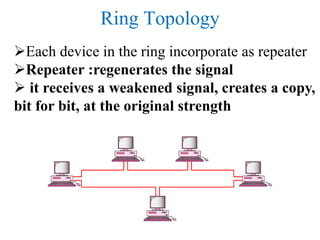
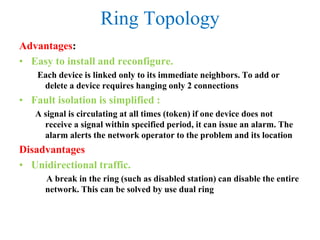
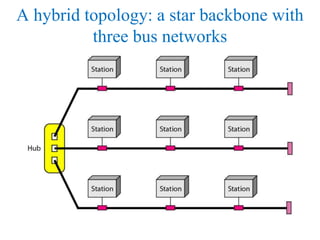
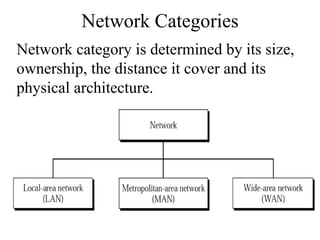
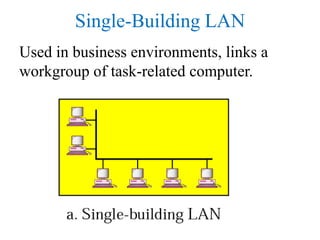
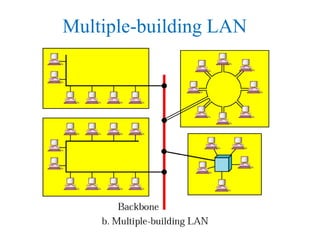
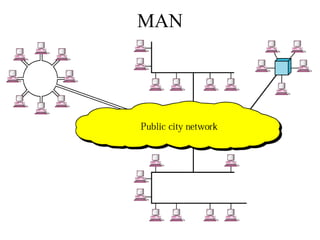
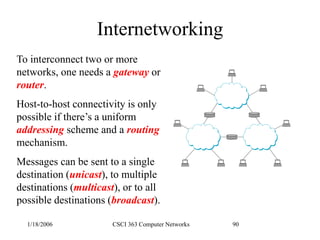
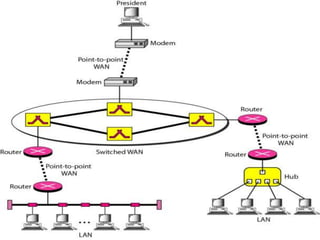
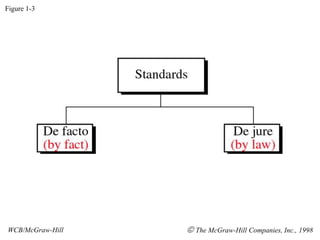
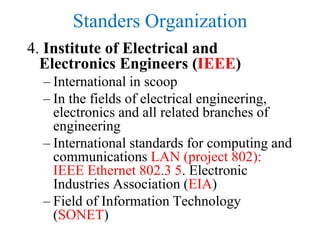
This document provides an introduction to computer networks. It defines key network concepts like local area networks (LANs), wide area networks (WANs), and the different physical network topologies including bus, star, ring, mesh, and hybrid networks. It discusses network performance metrics like throughput and delay. It also covers network criteria such as reliability, security, and standards organizations that help networks communicate. Examples of different network configurations are provided to illustrate LANs, WANs, and the various physical topologies.