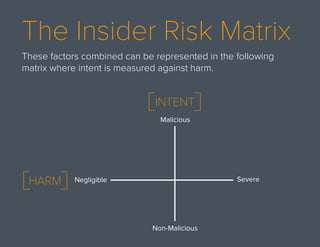
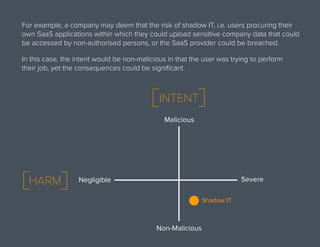
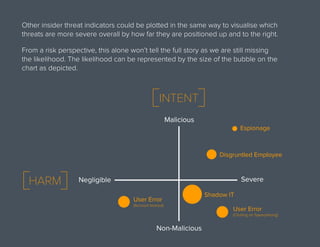
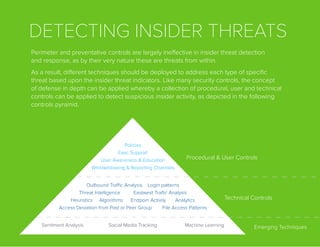
The document discusses insider threats as a primary concern for organizations, especially in the financial sector. It categorizes insiders into three types: non-malicious, malicious, and compromised, and highlights the challenges in detecting and responding to insider threats due to the complexity of human behavior. Various detection and response strategies, including technical controls and monitoring techniques, are recommended to effectively manage insider threats.