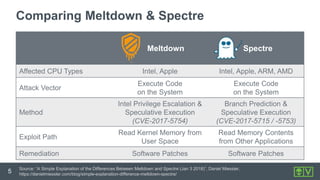
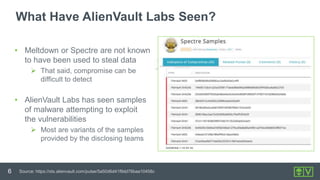
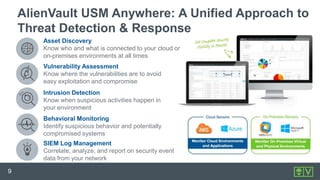
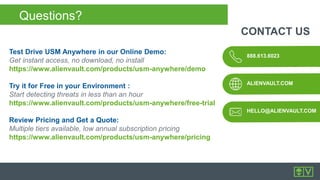
The document provides an overview of the Meltdown and Spectre vulnerabilities, including their impact on various CPU types and the methods of exploitation. It discusses the importance of detecting these vulnerabilities, available software patches, and recommendations for protecting systems, such as implementing Alienvault's USM Anywhere for continuous monitoring and threat detection. The document also highlights the role of threat intelligence and practical measures organizations should adopt to mitigate risks associated with these vulnerabilities.