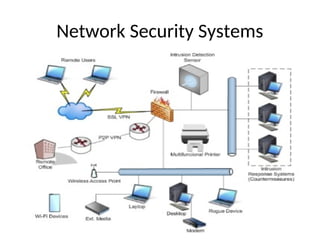
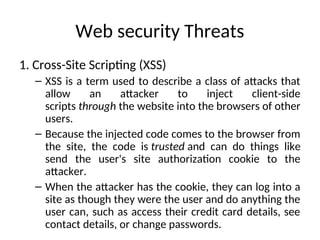
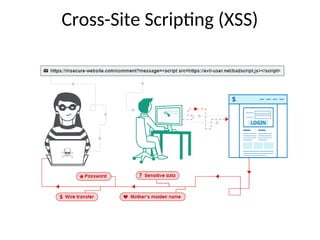
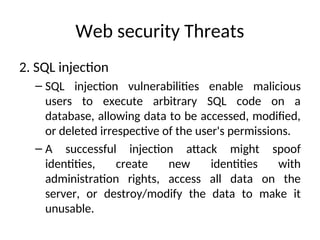
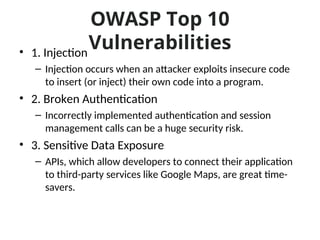
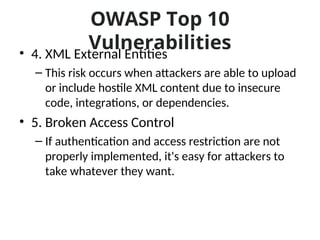
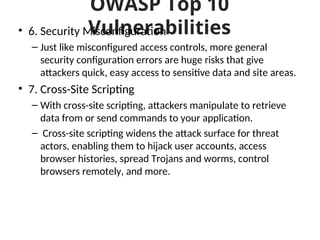
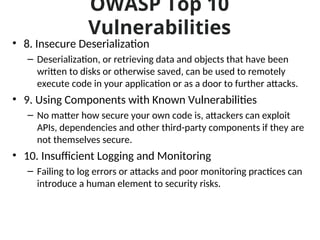
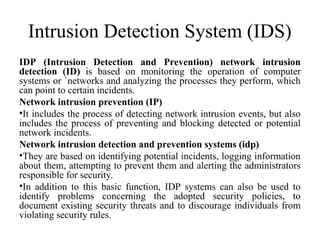
The document discusses various types of system vulnerabilities including hardware, software, network, and procedural vulnerabilities that can compromise security. It also outlines network security measures and tools such as firewalls, encryption, and antivirus software to protect against cyber threats. Additionally, it highlights the importance of application security, emphasizing authentication, authorization, and security testing to prevent unauthorized access and data breaches.