Ikeepsafe Cyber Safety, Ethics and Security Competencies
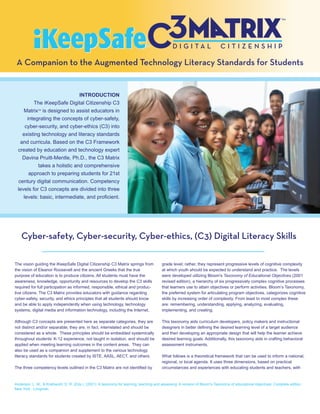
- 1. A Companion to the Augmented Technology Literacy Standards for Students INTRODUCTION The iKeepSafe Digital Citizenship C3 Matrix is designed to assist educators in TM integrating the concepts of cyber-safety, cyber-security, and cyber-ethics (C3) into existing technology and literacy standards and curricula. Based on the C3 Framework created by education and technology expert Davina Pruitt-Mentle, Ph.D., the C3 Matrix takes a holistic and comprehensive approach to preparing students for 21st century digital communication. Competency levels for C3 concepts are divided into three levels: basic, intermediate, and proficient. Cyber-safety, Cyber-security, Cyber-ethics, (C3) Digital Literacy Skills The vision guiding the iKeepSafe Digital Citizenship C3 Matrix springs from grade level; rather, they represent progressive levels of cognitive complexity the vision of Eleanor Roosevelt and the ancient Greeks that the true at which youth should be expected to understand and practice. The levels purpose of education is to produce citizens. All students must have the were developed utilizing Bloom's Taxonomy of Educational Objectives (2001 awareness, knowledge, opportunity and resources to develop the C3 skills revised edition), a hierarchy of six progressively complex cognitive processes required for full participation as informed, responsible, ethical and produc- that learners use to attain objectives or perform activities. Bloom’s Taxonomy, tive citizens. The C3 Matrix provides educators with guidance regarding the preferred system for articulating program objectives, categorizes cognitive cyber-safety, security, and ethics principles that all students should know skills by increasing order of complexity. From least to most complex these and be able to apply independently when using technology, technology are: remembering, understanding, applying, analyzing, evaluating, systems, digital media and information technology, including the Internet. implementing, and creating. Although C3 concepts are presented here as separate categories, they are This taxonomy aids curriculum developers, policy makers and instructional not distinct and/or separable; they are, in fact, interrelated and should be designers in better defining the desired learning level of a target audience considered as a whole. These principles should be embedded systemically and then developing an appropriate design that will help the learner achieve throughout students’ K-12 experience, not taught in isolation, and should be desired learning goals. Additionally, this taxonomy aids in crafting behavioral applied when meeting learning outcomes in the content areas. They can assessment instruments. also be used as a companion and supplement to the various technology literacy standards for students created by ISTE, AASL, AECT, and others. What follows is a theoretical framework that can be used to inform a national, regional, or local agenda. It uses three dimensions, based on practical The three competency levels outlined in the C3 Matrix are not identified by circumstances and experiences with educating students and teachers, with Anderson, L. W., & Krathwohl, D. R. (Eds.). (2001). A taxonomy for learning, teaching and assessing: A revision of Bloom's Taxonomy of educational objectives: Complete edition, New York : Longman.
- 2. input from multiple stakeholders including parents, students, educators, intentional interference, compromise, or incapacitation through the technology coordinators, media specialists, curriculum resource teachers, misuse of, or by unauthorized means of the Internet, public Internet safety experts, and industry security specialists. While C3 subject or private telecommunications systems, or other similar conduct areas have common ground, they also have significant content that is that violates federal, state, or international law, that harms distinct and important in discussing on an individual basis. interstate commerce of the US, or that threatens public health or safety.” In contrast, most of the issues covered in cyber-safety are steps that one can take to avoid revealing information by “social” Cyber-safety means. Cyber-safety addresses the ability to act in a safe and responsible manner on the Internet and other connected environments. These Cyber-ethics behaviors protect personal information and reputation and include Cyber-ethics is the discipline of using appropriate and ethical safe practices to minimize danger from behavioral-based, rather behaviors and acknowledging moral duties and obligations than hardware/software-based, problems. pertaining to online environments and digital media. Cyber-security Cyber-safety, security, and ethics cannot be stagnant, because Whereas cyber-safety focuses on acting safely and responsibly, technologies are dynamic and ever changing. For example, cyber-ethical cyber-security covers physical protection (both hardware and issues are experiencing vast transformation as a result of factors driven by software) of personal information and technology resources from the multi-media aspects of cell phones and the immense reservoir of unauthorized access gained via technological means. Cyber- information on the Internet. It is essential that educators have tools for security is defined by HR 4246, Cyber Security Information Act technology education that are also dynamic and evolving. The C3 Matrix (2000) as "the vulnerability of any computing system, software provides these tools for teachers and administrators—and the students program, or critical infrastructure to, or their ability to resist, they teach. © 2009. Internet Keep Safe Coalition. All rights reserved. This was developed, copyrighted, and distributed for incidental, classroom and limited commercial sharing. Copies and reproductions of this content, in whole or in part, may be reproduced or transmitted for incidental, classroom use. Commercial copying is allowed provided that all copies/transmissions contain IKSC copyright language and distribution restrictions. Direct questions to: legal@iKeepSafe.org.
- 3. C3 Framework Promoting Responsible Use I. Cyber-Ethics Students recognize and practice responsible and appropriate use while accessing, using, collaborating, and creating technology, technology systems, digital media and information technology. Students demonstrate an understanding of current ethical and legal standards, the rights and restrictions that govern technology, technology systems, digital media and information technology within the context of today’s society. Students will: A. Understand and follow acceptable polices (school, home and community), and understand the personal and societal consequences of inappropri- ate use. B. Demonstrate and advocate for ethical and legal behaviors among peers, family, and community. C. Practice citing sources of text and digital information and make informed decisions about the most appropriate methods for avoiding plagiarism. D. Make ethical and legal decisions while using technology, technology systems, digital media and information technology when confronted with usage dilemmas. E. Exhibit responsibility and Netiquette when communicating digitally. F. Recognize the signs and emotional effects, the legal consequences and effective solutions for Cyberbullying. G. Recognize appropriate time and place to use digital tools, techniques and resources. H. Understand the importance of online identity management and monitoring. Advocate others to understand the importance of Online Reputation Management. II. Cyber-Safety Students practice safe strategies to protect themselves and promote positive physical and psychological well-being when using technology, technology systems, digital media and information technology including the Internet. Students will: A. Recognize online risks, to make informed decisions, and take appropriate actions to protect themselves while using technology, technology systems, digital media and information technology. B. Make informed decisions about appropriate protection methods and safe practices within a variety of situations. C. Demonstrate and advocate for safe behaviors among peers, family, and community. III. Cyber-Security Students practice secure strategies when using technology, technology systems, digital media and information technology that assure personal protection and help defend network security. Students will: A. Recognize online risks, make informed decisions, and take appropriate actions to protect themselves while using technology, technology systems, digital media and information technology. B. Make informed decisions about appropriate protection methods and secure practices within a variety of situations. C. Demonstrate commitment to stay current on security issues, software and effective security practices. D. Advocate for secure practices and behaviors among peers, family, and community. Pruitt-Mentle, D. (2000). The C3 framework: Cyberethics, cybersafety and cybersecurity implications for the educational setting. C3 is a trademark registered with ETPRO. Materials can be used for educational and non-profit use. For other uses, contact Davina Pruitt-Mentle, dpruitt@umd.edu.
- 4. C3 YBER-SAFETY Physical and Psychological Well-being: Students practice safe strategies to protect themselves and promote positive physical and psychological well-being when using technology, technol- ogy systems, digital media and information technology, including the Internet. BASIC INTERMEDIATE PROFICIENT A. Recognize online risks, make Safe and Responsible Practices Safe and Responsible Practices Safe and Responsible Practices informed decisions, and take Recognize and discuss safety issues Recognize safety issues* related to Recognize and discuss safety issues appropriate actions to protect technology, technology systems, digital related to technology, technology related to technology, technology themselves while using technol- media and information technology systems, digital media and information systems, digital media and information ogy, technology systems, digital including the Internet (e.g., online technology including the Internet (e.g., technology including the Internet (e.g., media and information technology. predator tactics, posting controversial online predator tactics, posting controver- online predator tactics, posting controver- content). sial content). sial content). Use safe practices related to technology, Use safe practices and procedures Use safe practices and procedures technology systems, digital media and related to technology, technology related to technology, technology information technology including the systems, digital media and information systems, digital media and information Internet. technology including the Internet. technology including the Internet. Recognize and understand the purpose Explain the purpose of technology, Explain the purpose of and analyze the of protection measures (including filtering technology systems, digital media and use of different protection measures for systems) for various types of technology, information technology protection technology, technology systems, digital technology systems, digital media and measures. media and information technology. information technology. B. Make informed decisions about Adhere to privacy and safety guidelines, Adhere to privacy and safety guidelines, Adhere to privacy and safety guidelines, appropriate protection methods policies, and procedures. policies, and procedures. policies, and procedures. and secure practices within a Discuss the potential for addictive Describe technology and Internet Describe and practice procedures for variety of situations. behaviors and the excessive use of addictive behaviors. disciplined and productive Internet use technology and Internet. Describe procedures for exiting an (e.g., balance between time on and off the Describe procedures for exiting an inappropriate site. Internet). inappropriate site. Describe procedures for reducing the Describe and practice procedures for Describe procedures for reducing the chance of being a victim of cyber-bullying. exiting an inappropriate site. chance of being a victim of cyber-bullying. Describe effective steps to manage and Describe and practice procedures for Describe procedures for reporting resolve a cyber-bullying situation. reducing the chance of being a victim of cyber-bullying and other inappropriate Model understanding about current safety cyber-bullying. behavior or content. needs. Describe and practice effective steps to manage and resolve a cyber-bullying situation. C. Demonstrate and advocate for Model personal safety within a variety of Model personal safety within a variety of safe behaviors among peers, situations. situations. family, and community. Demonstrate commitment to stay current on safety issues and effective protection practices. Advocate for safe practices and behaviors among peers, family, and community. * Safety issues could include but are not limited to: upload and download of objectionable content, cyber-bullying, reputation damage, response to unwanted communications from businesses or predators, and Internet addiction.
- 5. C3 YBER-SECURITY Digital Security: Practice secure strategies that assure personal protection and help defend network security. BASIC INTERMEDIATE PROFICIENT A. Recognize Secure Practices Secure Practices Secure Practices security risks, make Understand and discuss security risks and the Understand security risks and the potential harm of Understand and discuss security risks and informed decisions, potential harm of intrusive applications related to intrusive applications related to technology, the potential harm of intrusive applications and take appropriate technology systems, digital media, and information technology, technology systems, digital media related to technology, technology systems, actions to protect technology including the Internet (e.g. email viruses, and information technology including the Internet digital media and information technology themselves while digital propaganda, spy ware, adware, identity theft, (e.g. email viruses, digital propaganda, spy ware, including the Internet (e.g. email viruses, using technology, phishing/pharming/spoofing scams, spam, social adware, identity theft, digital propaganda, spy ware, adware, identity technology systems, engineering). phishing/pharming/spoofing scams, spam, social theft, phishing/pharming/spoofing scams, digital media and Understand effective basic security practices engineering). spam, social engineering). information technol- related to technology, technology systems, digital Describe and practice effective security Practice effective security practices and media and information technology including the practices, beyond the basic level, related to analyze new options, beyond the intermediate ogy. Internet (e.g., strong passwords, protecting technology, technology systems, digital media level, related to technology, technology password and user ID, not disclosing important and information technology including the Internet. systems, digital media and information personal information, minimizing/evaluating pop up Recognize and understand the purpose of technology including the Internet and critically ads). security protection measures for technology, evaluate digital resources. Recognize and understand the purpose of technology systems, digital media and informa- Recognize and understand the purpose of technology, technology systems, digital media and tion technology. security protection measures for technology, information technology security protection measures. Model understanding about current security technology systems, digital media and Discuss strategies for managing everyday hardware needs. information technology. and software problems. B. Make informed Adhere to security guidelines, policies, and Adhere to security guidelines, policies, and decisions about procedures. procedures. appropriate protec- Use effective strategies for managing everyday Describe and practice strategies for managing tion methods and hardware and software problems. everyday hardware and software problems. Use effective strategies for securing wireless Describe and practice strategies for securing secure practices connections (e.g., connecy to only legitimate wi-fi wireless connections (e.g., connect to only within a variety of hot spots or turn off wi-fi, turn off file share mode, legitimate wi-fi hot spots or turn off wi-fi, turn off situations. encrypt sensitive data/ information, use and file share mode, encrypt sensitive data/ update anti-virus software, use a firewall, update information, use and update anti-virus software, operating system). use a firewall, update operating system. C. Demonstrate Model secure practices within a variety of Model secure practices within a variety of commitment to stay digital communities. digital communities. current on security issues, software and effective security practices. D. Advocate for Advocate for secure practices and behaviors secure practices and among peers, family, and community. behaviors among peers, family, and community.
- 6. C3 YBER-ETHICS Legal and Ethical Issues: Students recognize and practice responsible and appropriate use while accessing, using, collaborating, and creating technology, technology systems, digital media and information technology. Students demonstrate an understanding of current ethical and legal standards, rights and restrictions governing technology, technology systems, digital media and information technology within the context of today’s society. BASIC INTERMEDIATE PROFICIENT A. Understand and Understand and follow acceptable Understand and follow acceptable Understand and follow acceptable use policies follow acceptable use policies (e.g., school, home, and use policies (e.g., school, home, and (e.g., school, home, and community settings). use polices (school, community settings). community settings). Demonstrate responsible use of technology, home and commu- Discuss basic issues related to Demonstrate responsible use of technology systems, digital media and information nity), and understand responsible use of technology, technology, technology systems, digital technology in different settings (e.g., school, home, the personal and technology systems, digital media and media and information technology in and community) and describe and analyze societal conse- information technology, and describe different settings (e.g., school, home, personal and societal consequences of inappropri- quences of inappro- personal consequences of inappropri- and community settings) and describe ate use. priate use. ate use*. and analyze personal and societal Make informed choices about acceptable use of consequences of inappropriate use. technology, technology systems, digital media and information technology when confronted with usage dilemmas. B. Demonstrate and Demonstrate and advocate for legal and ethical advocate for ethical behaviors among peers, family, and community and legal behaviors regarding responsible use of technology, technology among peers, family, systems, digital media and information technology. and community. C. Practice citing Understand and follow ethical Understand and follow ethical Understand and follow ethical standards of sources of text and standards of conduct (e.g., AUP, standards of conduct (e.g., AUP, conduct (e.g., AUP, Student Handbooks, Student digital information Student Handbooks, Student Code of Student Handbooks, Student Code of Code of Conduct, Honor Codes). and make informed Conduct, Honor Codes). Conduct, Honor Codes). Discuss definitions and basic concepts and issues decisions about the Discuss definitions and basic Discuss definitions and basic concepts related to plagiarism/electronic cheating and most appropriate concepts and issues related to and issues related to describe personal and societal consequences of methods for avoiding plagiarism/electronic cheating and plagiarism/electronic cheating and plagiarism. plagiarism. describe personal and societal describe personal and societal Demonstrate appropriate strategies for avoiding consequences of plagiarism. consequences of plagiarism. plagiarism (e.g., quoting, citing, acknowledging Demonstrate appropriate strategies Practice citing sources of text and source and/or paraphrasing) for avoiding plagiarism (e.g., quoting, digital information. Determine the most appropriate method for citing, acknowledging source and/or Determine and practice the use of avoiding plagiarism and create original work and paraphrasing). appropriate strategies for avoiding practice citing sources of text and digital informa- Discuss the importance of respecting plagiarism (e.g., quoting, citing, tion. the rights of others regarding their acknowledging source and/or Demonstrate and advocate for ethical behaviors work. paraphrasing). among peers, family, and community. * Inappropriate use could include, but is not limited to, viewing inappropriate content, using the school’s network for non-educational purposes, or work networks for non-school/work related activities, posting incorrect/inaccurate information, bullying, participating in hate groups, harassing or sending/posting mean comments, hacking, illegally downloading copyrighted materials/movies/music and/or making and sharing copies of copyrighted materials, etc..
- 7. C3 YBER-ETHICS BASIC INTERMEDIATE PROFICIENT D. Make ethical Discuss definitions and basic concepts and Discuss definitions and basic concepts and Discuss definitions and basic concepts and issues and legal issues related to intellectual property, media issues related to intellectual property, media related to intellectual property, media copyright laws, decisions when copyright laws, private/public domain, fair copyright laws, private/public domain, fair private/public domain, fair use, and file sharing. confronted with use and file sharing. use, and file sharing. Describe personal and societal consequences of usage dilemmas Describe personal and societal conse- Describe personal and societal conse- respecting verses ignoring rights, laws and practices while using quences of respecting verses ignoring rights, quences of respecting verses ignoring such as copyright, private/public domain, fair use, technology, laws and practices such as copyright, rights, laws and practices such as and file sharing. technology private/public domain, fair use and file copyright, private/public domain, fair use Describe personal and societal consequences systems, digital sharing. and file sharing. involving intellectual property rights, media copyright media and Understand and follow school, home and Understand and follow school, home and laws, private/public domain, fair use, and file sharing. information community policies on access to information community policies on access to informa- Understand and follow school, home and commu- technology. resources. tion resources and adhere to local, state, nity policies on access to information resources and and federal laws. adhere to local, state, and federal laws. Demonstrate appropriate social and ethical Distinguish the legal implications between personal, behaviors when using technology and educational, and commercial uses of protected digital media including the recognition of works. intellectual property rights, fair use of Demonstrate social and ethical behaviors when copyrighted material, and legal file sharing using technology and digital media regarding or downloading of software, music and intellectual property recognition, fair use of videos. copyrighted material, including file-sharing and Make ethical and legal use of technology, pirating versus legal downloading of software, music technology systems, digital media and and videos. information technology when confronted Make ethical and legal use of technology, technol- with usage dilemmas. ogy systems, digital media and information technol- ogy when confronted with usage dilemmas. Demonstrate and advocate for legal and ethical behaviors in this domain among peers, family, and community. E. Exhibit respon- Recognize personal differences and Recognize personal differences and Recognize personal differences and practice sibility and practice etiquette within diverse situations. practice etiquette within diverse digital etiquette within diverse digital communities. netiquette (i.e Recognize positive and negative social and communities. Recognize and analyze positive and negative appropriate digital ethical behaviors when using technology Recognize positive and negative social and social and ethical behaviors when using technology communication and digital media and information technol- ethical behaviors when using technology and digital media and information technology. skills) when ogy. and digital media and information technol- communicating ogy. digitally.
- 8. C3 YBER-ETHICS BASIC INTERMEDIATE PROFICIENT F. Recognize the Understand and discuss the signs and Demonstrate a thorough understanding of Demonstrate a thorough understanding of the signs, emotional solutions for cyber-bullying. the signs, emotional effects, legal conse- signs, emotional effects, legal consequences effects, legal conse- Recognize appropriate time and place to quences of, and effective solutions for of, and effective solutions for cyber-bullying. quences of and use digital tools, techniques, and cyber-bullying. Make informed choices when confronted with effective solutions resources (e.g., when appropriate to use Recognize appropriate time and place to cyber-bullying dilemmas. for cyber-bullying. lingo and emoticons, when to use cell use digital tools, techniques, and resources Recognize appropriate time and place to use phone and text message). (e.g., when appropriate to use lingo and digital tools, techniques and resources (e.g., Apply proper communication skills when emoticons, when to use cell phone and text when appropriate to use lingo and emoticons, communicating digitally. message). when to use cell phone and text message). Apply appropriate communication skills when communicating digitally. Practice digital etiquette to support collabora- tion Advocate for proper netiquette behaviors among peers, family, and community. G. Recognize Understand that content posted to the Understand that content posted to the web Understand that content posted to the web or appropriate time and web or sent through other digital means or sent through other digital means (e.g., sent through other digital means (e.g., cell place to use digital (e.g., cell phones, cameras) is acces- cell phones, cameras) is accessible to a phones, cameras) are accessible to a wide tools, techniques sible to a wide audience and can be wide audience and can be permanently audience and can be permanently archived. and resources. permanently archived. archived. H. Understand the Understand the importance of online Understand the importance of online Understand the importance of online reputa- importance of online reputation management and monitoring reputation management and monitoring tion management and monitoring (ORM). identity management (ORM). (ORM). Recognize positive and negative uses of and monitoring Recognize positive and negative uses Recognize positive and negative uses of electronic media/postings as related to ORM. (ORM). Advocate of electronic postings as related to ORM electronic postings as related to ORM. Demonstrate appropriate strategies for others to understand Demonstrate appropriate strategies for protecting, monitoring, and/or positively the importance ORM. protecting, monitoring and/or positively promoting personal identity (i.e. ORM). promoting personal identity- Online Reputa- Analyze selected electronic media/postings tion Management and monitoring (ORM). and reflect, as an individual, on the appropri- ateness of each for effective ORM.
- 9. ! ! A!!U!!G!!M!!E!!N!!T T!!E!!D!! Technology!Litera acy!Standards s!for!Students!! ! This!graphh!is!designed!to!help!educators!see!how w!C3!concepts!(cyber"safet ty,!cyber"secu urity,!and!cyb ber" ethics)!can!be!integrated!into!existing!standards.!A!teacher!or!technology!coordinator!m may!refer!bacck!to! the!C3!Ma atrix!for!ways s!to!address!s ty,!and!ethics!while!teaching!concepts!f safety,!securit from!the!national! standards ! s. ! How!con ntent!addres sses:! ! ISTE/NETS•S!Stan ndards! ! AAASL!Standards!for!the!21st!Century!Learner! ! AAASL/AECT!Inform mation!Literacy!Standards!for!S Student!Learning g! ! KeepSafe!Digital!Citizenship!C3!M iK Matrix! ! 21st!Century!Fram 1 mework.! Activity/Moodule:! ! ! n!of!any!activity!do *!Completion oes!not!certify!com mpetency!in!the!identified!area;!how wever,!it!will!contribute!to!developm ment!of!the!compe etency! ISTE/NETS S•S!Standard!and! Indicato ors Addresssed!in! EXAMPLE Outcomes! this!act tivity! 1.!!Creativity!& &!Innovation! Students:! ! a. apply!existing!kno owledge!to!generate! ! Students!demo onstrate!creative! new!ideas,!produccts,!or!processes !!!Yes thinking,!construct!knowledge,!a and! b. create!original!wo orks!as!a!means!of! !!!No develop!innova ative!products!&! personal!or!group p!expression! processes! c. use!models!and!simulations!to!exploore! AASL!1.1.1,!1.2.1,!1.2.3.,!2.1.1.,! complex!systems!and!issues! 2.1.6 6.,!2.2.4.,!4.1.5.,!4. .1.8.!! d. identify!trends!and!forecast!possibilities.! AASL/A AECT!1.3,!3.2,!3.3,!5.3,!! iKeepSafe!C3!Ma atrix!! st t 21 !1.1,!1.4,!2.4,!2.5,!3.1,!! 2.!Communicat tion!and! Students:! Collaboration! a. interact,!collaboraate,!and!publish!w with! ! Students!use!digital!media!and! peers,!experts,!or!others!employing g!a! !!!Yes environments!t to!communicate!a and! environments!and! variety!of!digital!e !!!No work!collaboratively,!including!at!a! media.! distance,!to!sup pport!individual! b. communicate!info ormation!and!ideas! learning!and!co ontribute!to!the! effectively!to!mult tiple!audiences!us sing!a! learning!of!others.! variety!of!media!a and!formats.! AASL!1.1.9.,!1.3.2.,!1.3.4.,!2.1.4.,! c. develop!cultural!u understanding!and d! 4.,!2.3.2.,!3.1.1.,3.1.2.,! 2.1.5.,!2.2.4 global!awareness!by!engaging!with! 3.1.4.,!3.2.1.,!3.2.3.,!3.3 3.1.,! learners!of!other!c cultures.! 3.3.2.,3.44.3.,4.2.1.,4.3.1.,4..4.4.!! d. contribute!to!project!teams!to!prod duce! AASL/AECT!3.4,!!5.3,!9.1,!9.2,!9.3,! original!works!or!ssolve!problems.! 9.4,!7.1,!! C3!Coonceptual!Framew work! st 21 !1.2,!1.3,!3.1,!4.1,!4.2,!4.3, ,8.1,! 8.2,10.1,!10.2,!110.3,!! 3.!Research!an nd!Information! Students:! Fluency!! a. plan!strategies!to!guide!inquiry.! ! Students!applyy!digital!tools!to! b. locate,!organize,!a analyze,!evaluate,! !!!Yes gather,!evaluat te,!and!use! synthesize,!and!etthically!use!inform mation! !!!No information! from!a!variety!of!ssources!and!media a.! AASL!1.1.4,!1 1.1.5,!1.1.6.,!1.1.7,!2..1.1.,! c. evaluate!and!selec ct!information!souurces! 2.1.2.,!2.2.3.,!2. .2.4.,!3.1.1.,3.1.4.,!3..4.2.,! and!digital!tools!b based!on!the! 4.1.6.!!! 4 appropriateness!to!specific!tasks.!! AASL/AECT!1.2,!1.4,1.5,!2.1,!2.2,!2.3, ,!2.4,!! 3.1,!4.1,!4.2,,!6.1,!! d. process!data!and!report!results.! ! iKeepSafe!C3!M Matrix!! st 21 !2.4,!2.5,!5..1,!5.2,!6.3,!7.1,!7.2,!11.2,! 12.3!!
- 10. 4.!Critical!Thinking,!Problem! Students:! Solving!and!Decision!Making! a. identify!and!define!authentic!problems! ! ! and!significant!questions!for! !!!Yes! Students!use!critical!thinking!skills! investigation.! !!!No! to!plan!&!conduct!research,!manage! b. plan!and!manage!activities!to!develop!a! projects,!solve!problems,!and!make! solution!or!complete!a!project.! informed!decisions!using! c. collect!and!analyze!data!to!identify! appropriate!digital!tools!&! solutions!and/or!make!informed! resources! decisions.! ! d. use!multiple!processes!and!diverse! AASL!1.1.1,!1.1.3,!1.1.4.,!1.2.2.,! perspectives!to!explore!alternative! 1.2.4.,1.3.2.,!2.1.3.,3.1.4.,!3.2.3.,! solutions.! 3.3.4.,!4.2.3.!! AASL/AECT!6.2,!! iKeepSafe!C3!Matrix! st 21 !2.1,!2.2,2.4,!2.5,4.1,!4.2,8.1,! 8.2,!9.4,!9.5,!! 5.!Digital!Citizenship! Students:! ! a. advocate!and!practice!safe,!legal,!and! ! Students!understand!human,! responsible!use!of!information!and! !!!Yes! cultural,!and!social!issues!related! technology.! !!!No! to!technology!&!practice!legal!and! b. !exhibit!a!positive!attitude!toward!using! ethical!behavior! technology!that!supports!collaboration,! AASL!1.3.1.,!1.3.3.,!1.3.5.,!2.3.3.,! learning,!and!productivity.! 3.1.6.,!3.2.2.,3.3.7.,4.3.4.,!4.4.3.,! c. !demonstrate!personal!responsibility!for! 4.4.4.,!4.4.5.!!! lifelong!learning.! AASL/AECT!8.1,!8.2,!8.3,!7.1,!! d. exhibit!leadership!for!digital!citizenship.! C3!Conceptual!Framework!! st 21 !4.1,!4.2,!4.3,!5.2,!6.2,!6.3,!7.2,! 9.6,!10.1,!10.2,!10.3,!12.3!!! 6.!Technology!Operations!&! Students:! Concepts!! a. understand!and!use!technology!systems.! ! ! b. !select!and!use!applications!effectively! !!!Yes! Students!demonstrate!a!sound! and!productively.! !!!No! understanding!of!technology! c. troubleshoot!systems!and!applications.! concepts,!systems,!and!operations! d. !transfer!current!knowledge!to!learning! AASL!1.1.8.,!2.1.4.,!3.4.2.!!! of!new!technologies.! C3!Conceptual!Framework! ! Correlation!of!the!ISTE/NET•S!&!AASL/AECT,!21st!Century!Framework!and!C3!Matrix! ! © Internet Keep Safe Coalition 2009. All rights reserved. Educational Technology Policy, Research and Outreach. For information contact Davina Pruitt-Mentle, Ph.D. – (410) 531-3910 – dpruitt@umd.edu NETS•S -Educational Technology Standards and Performance Indicators for Students: http://www.iste.org/Content/NavigationMenu/NETS/ForStudents/2007Standards/NETS_for_Students_2007.htm AASL - http://www.ala.org/ala/mgrps/divs/aasl/aaslproftools/learningstandards/standards.cfm AASL/AECT - http://www.ala.org/ala/mgrps/divs/aasl/aaslproftools/informationpower/InformationLiteracyStandards_final.pdf st Partnership for 21 Century Skills http://www.21stcenturyskills.org/index.php?Itemid=120&id=254&option=com_content&task=view Numerical ordering of skill/definitions are assigned for brevity within table format. NETS for Students: National Educational Technology Standards for Students, Second Edition, © 2007, ISTE® (International Society for Technology in Education), www. ISTE.org<http://www.iste.org>. All rights reserved. !
