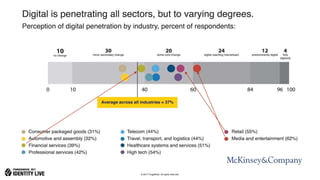
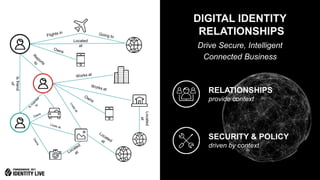
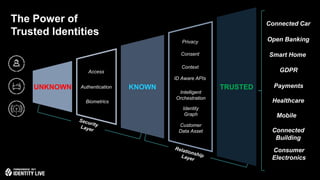
The document discusses the importance of digital identity and its role in digital transformation across industries, highlighting the need for customer insights, compliance with regulations like GDPR, and the security of connected devices. It presents trends in digital transformation, the growing number of connected devices expected by 2020, and the potential for increased revenue through improved customer experience strategies. Additionally, it emphasizes the significance of identity management in providing personalized and secure services across various channels and devices.