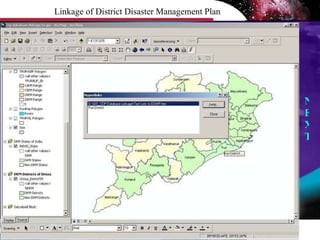
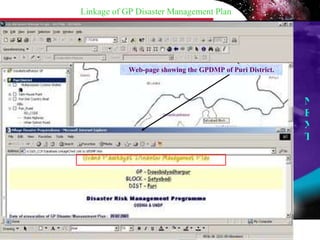
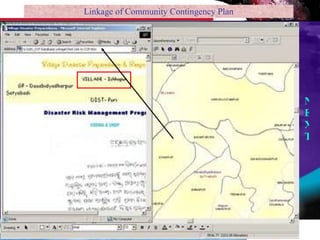
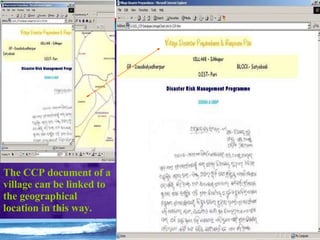
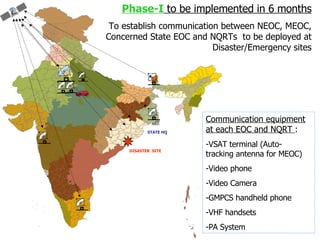
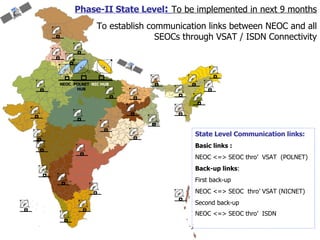
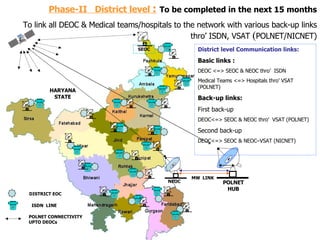
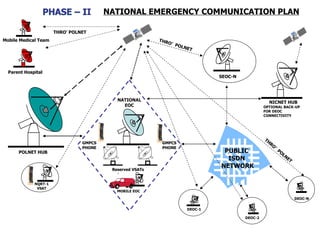
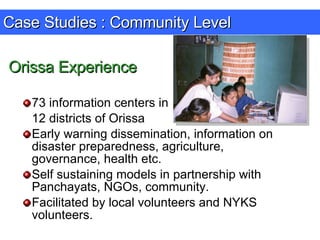
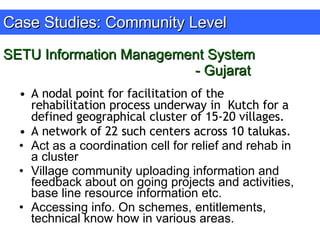
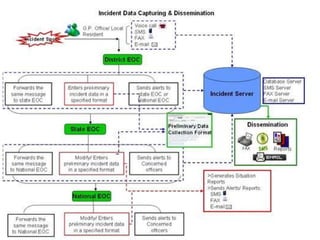
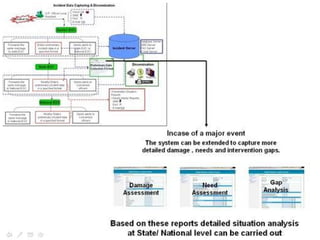
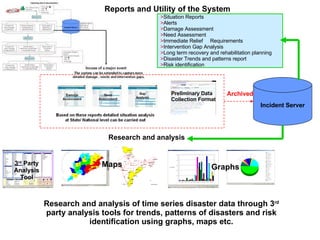
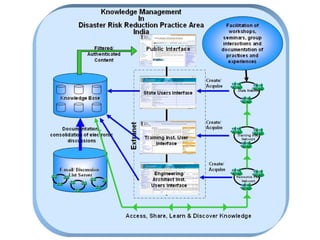
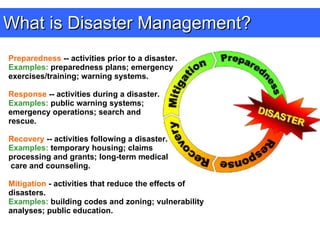
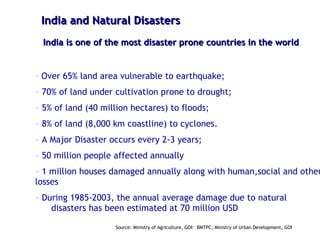
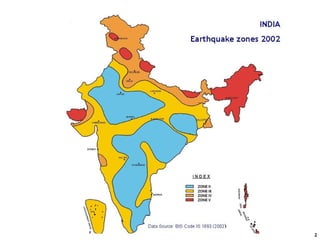
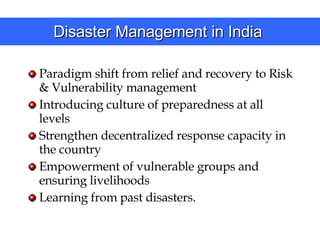
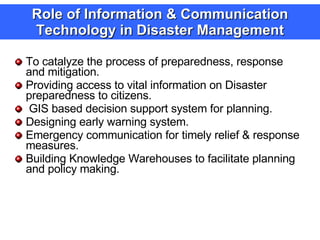
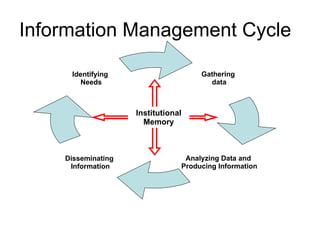
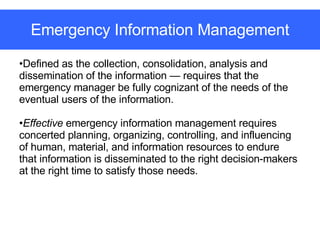
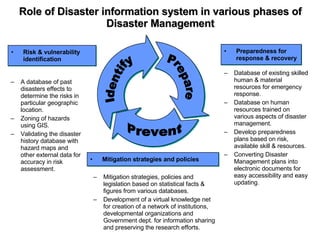
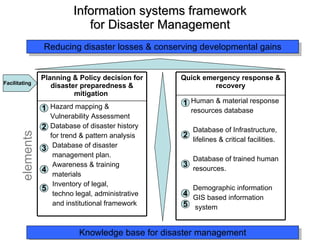
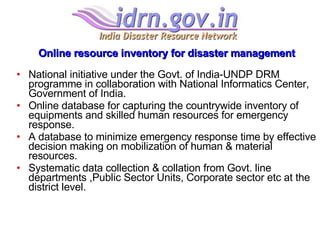
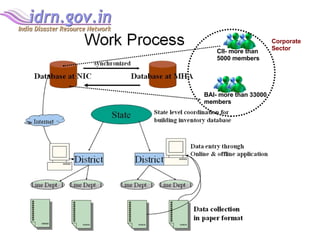
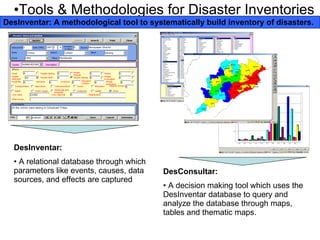
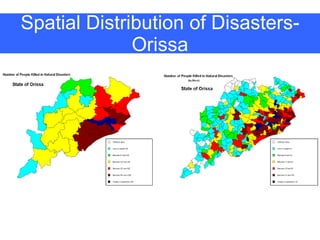
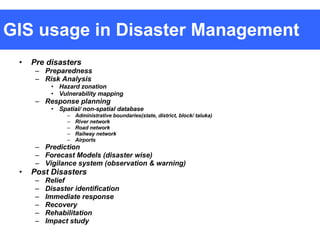
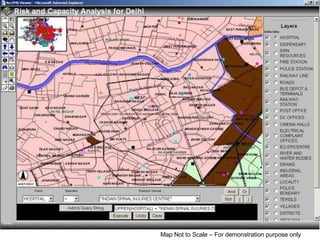
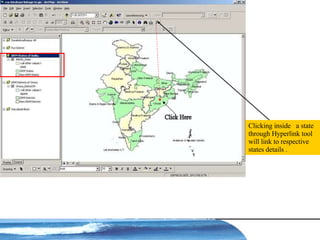
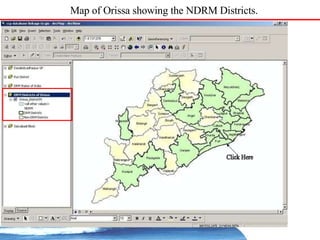
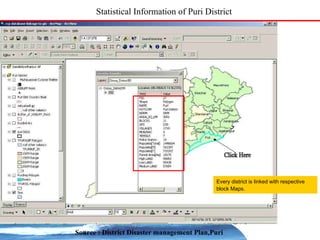
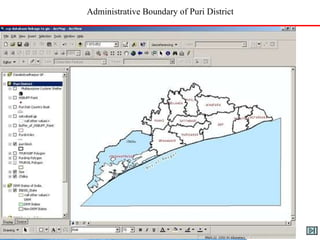
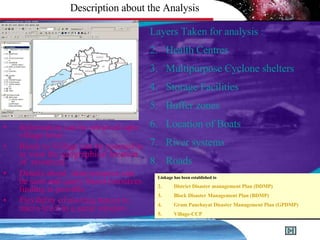
The document discusses the role of information and communication technology (ICT) in disaster risk management in India. It provides details on ICT systems and databases that can help with preparedness, response, recovery and mitigation efforts. These include hazard mapping, vulnerability assessments, disaster history databases, resource inventories, and GIS systems to facilitate planning and emergency response. Case studies are also presented on ICT tools currently used in India for disaster management.



![Location of Health Centres [Block Level] NEXT Next Slide: Map extent zoomed further to a scale of 1: 1,50,000 and greater to obtain location of health centres in the GP Level](https://image.slidesharecdn.com/ict-in-disaster-risk-reduction-india-case-1213544654618621-8/85/Ict-In-Disaster-Risk-Reduction-India-Case-42-320.jpg)
![Location of Health Centres [GP Level] Zoomed in to a scale of NEXT Next Slide: Map extent zoomed further to a scale of 1: 40,000 or greater to obtain location of health centres in the Village Level](https://image.slidesharecdn.com/ict-in-disaster-risk-reduction-india-case-1213544654618621-8/85/Ict-In-Disaster-Risk-Reduction-India-Case-43-320.jpg)
![Location of Health Centres [Village Level] NEXT](https://image.slidesharecdn.com/ict-in-disaster-risk-reduction-india-case-1213544654618621-8/85/Ict-In-Disaster-Risk-Reduction-India-Case-44-320.jpg)
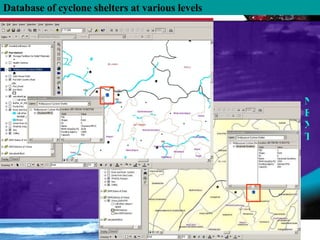
![Location of Multipurpose Cyclone Shelters [Block Level] NEXT One can view the location of existing resources in the block by clicking the layers ON .](https://image.slidesharecdn.com/ict-in-disaster-risk-reduction-india-case-1213544654618621-8/85/Ict-In-Disaster-Risk-Reduction-India-Case-45-320.jpg)
![NEXT Location of Multipurpose Cyclone Shelters [ GP Level]](https://image.slidesharecdn.com/ict-in-disaster-risk-reduction-india-case-1213544654618621-8/85/Ict-In-Disaster-Risk-Reduction-India-Case-46-320.jpg)
![NEXT Location of Multipurpose Cyclone Shelters [Village Level] Particular resource can be viewed from District to Village level by changing the scale in the same window. In case to obtain more than one resource select the desired layers as shown in the next slides.](https://image.slidesharecdn.com/ict-in-disaster-risk-reduction-india-case-1213544654618621-8/85/Ict-In-Disaster-Risk-Reduction-India-Case-47-320.jpg)
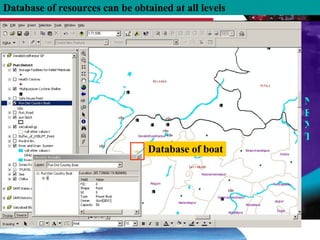
![NEXT Location of Storage Facilities, Boats and River system [Block Level]](https://image.slidesharecdn.com/ict-in-disaster-risk-reduction-india-case-1213544654618621-8/85/Ict-In-Disaster-Risk-Reduction-India-Case-48-320.jpg)
![NEXT Location of Storage Facilities, Boats and River system [GP Level]](https://image.slidesharecdn.com/ict-in-disaster-risk-reduction-india-case-1213544654618621-8/85/Ict-In-Disaster-Risk-Reduction-India-Case-49-320.jpg)
![NEXT Location of Storage Facilities, Boats and River system [Village Level]](https://image.slidesharecdn.com/ict-in-disaster-risk-reduction-india-case-1213544654618621-8/85/Ict-In-Disaster-Risk-Reduction-India-Case-50-320.jpg)
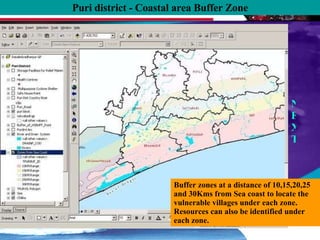
![NEXT Location of resources in the respective Coastal area Buffer Zone [Block Level]](https://image.slidesharecdn.com/ict-in-disaster-risk-reduction-india-case-1213544654618621-8/85/Ict-In-Disaster-Risk-Reduction-India-Case-52-320.jpg)
![NEXT Location of resources in the respective Coastal area Buffer Zone [GP Level]](https://image.slidesharecdn.com/ict-in-disaster-risk-reduction-india-case-1213544654618621-8/85/Ict-In-Disaster-Risk-Reduction-India-Case-53-320.jpg)
![NEXT Location of resources in the respective Coastal area Buffer Zone [Village Level]](https://image.slidesharecdn.com/ict-in-disaster-risk-reduction-india-case-1213544654618621-8/85/Ict-In-Disaster-Risk-Reduction-India-Case-54-320.jpg)