Ic R20 Manual (1)
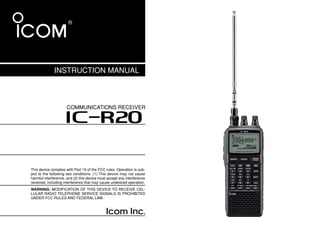
- 1. INSTRUCTION MANUAL COMMUNICATIONS RECEIVER iR20 This device complies with Part 15 of the FCC rules. Operation is sub- ject to the following two conditions: (1) This device may not cause harmful interference, and (2) this device must accept any interference received, including interference that may cause undesired operation. WARNING: MODIFICATION OF THIS DEVICE TO RECEIVE CEL- LULAR RADIO TELEPHONE SERVICE SIGNALS IS PROHIBITED UNDER FCC RULES AND FEDERAL LAW.
- 2. FOREWORD IMPORTANT Thank you for purchasing this Icom product. The IC-R20 COM- READ ALL INSTRUCTIONS carefully and completely MUNICATIONS RECEIVER is designed and built with Icom’s supe- before using the receiver. rior technology and craftsmanship. With proper care, this product should provide you with years of trouble-free operation. SAVE THIS INSTRUCTION MANUAL— This in- struction manual contains important operating instructions for We want to take a couple of moments of your time to thank you the IC-R20. for making your IC-R20 your radio of choice, and hope you agree with Icom’s philosophy of “technology first.” Many hours of research and development went into the design of your IC-R20. EXPLICIT DEFINITIONS D FEATURES WORD DEFINITION Personal injury, fire hazard or electric shock ❍ Covers 0.150–3304.999 MHz* wide R WARNING! may occur. frequency range CAUTION Equipment damage may occur. *Some frequency bands are inhibited according to version Recommended for optimum use. No risk of NOTE ❍ External power supply operation personal injury, fire or electric shock. ❍ 1250 memory channels* with 26 banks available *200 auto write and 50 scan edge channels are included. Icom, Icom Inc. and the logo are registered trademarks of Icom ❍ Built-in bar-antenna Incorporated (Japan) in the United States, the United Kingdom, Ger- many, France, Spain, Russia and/or other countries. ❍ Dualwatch operation i
- 3. PRECAUTION RWARNING! NEVER operate the receiver with a ear- NEVER expose the receiver to rain, snow or any liquids. phone, headphones or other audio accessories at high vol- The receiver may be damaged. ume levels. Hearing experts advise against continuous high NEVER operate or touch the receiver with wet hands. This volume operation. If you experience a ringing in your ears, re- may result in an electric shock or damage the receiver. duce the volume level or discontinue use. NEVER solder the battery cell. This may damage the bat- RWARNING! NEVER connect the receiver to an AC tery. outlet. This may pose a fire hazard or result in an electric shock. AVOID using or placing the receiver in direct sunlight or in areas with temperatures below –10°C (+14˚F) or above RWARNING! NEVER operate the receiver while dri- +60°C (+140˚F). ving a vehicle. Safe driving requires your full attention—any- thing less may result in an accident. AVOID the use of chemical agents such as benzine or al- cohol when cleaning, as they can damage the receiver’s sur- RWARNING! NEVER throw a battery cell or battery faces. pack into a fire since as internal battery gas can cause explo- Even when the receiver power is OFF, a slight current still sion. flows in the circuits. Remove batteries from the receiver when RWARNING! NEVER disassemble the battery pack. not using it for a long time. Otherwise, the installed batteries If the battery cell’s internal material (electrolyte liquid) gets will become exhausted, and will need to be recharged. into your eyes, wash your eyes with water and obtain treat- RESPECT other peaple’s privacy. Information overheard ment from an eye doctor immediately. but not intended for you cannot lawfully be used in any way. NEVER connect the receiver to a power source of more than 6 V DC directly. This will damage the receiver. For U.S.A. only NEVER connect the receiver to a power source using re- CAUTION: Changes or modifications to this device, not ex- pressly approved by Icom Inc., could void your authority to verse polarity. This will damage the receiver. operate this device under FCC regulations. ii
- 4. SUPPLIED ACCESSORIES OPERATING THEORY Electromagnetic radiation which has frequencies of q w e r 20,000 Hz (20 kHz*) and above is called radio frequency (RF) energy because it is useful in radio transmissions. The IC- R20 receives RF energy from 0.150 MHz* to 3304.999 MHz and converts it into audio frequency (AF) energy which in turn actuates a loudspeaker to create sound waves. AF energy is in the range of 20 to 20,000 Hz. *kHz is an abbreviation of kilohertz or 1000 hertz, MHz is abbreviation t y of megahertz or 1,000,000 hertz, where hertz is a unit of frequency. OPERATING NOTES The IC-R20 may receive its own oscillated frequency, result- ing in no reception or only noise reception, on some frequen- q Antenna (FA-B04RE) ………………………………………1 cies. w Belt clip (MB-98) …………………………………………1 set e Battery spacer ………………………………………………1 The IC-R20 may receive interference from extremely strong r Hand strap …………………………………………………1 signals on different frequencies or when using an external t Battery pack* (BP-206) ……………………………………1 high-gain antenna. yAC adaptor*(BC-149A/D) …………………………………1 (The shape of the BC-149A and BC-149D are different.) *Not supplied with some versions. iii
- 5. TABLE OF CONTENTS 1 2 FOREWORD .................................................. i I RF gain ................................................ 19 9 COMFORTABLE RECEIVING.......... 45–48 IMPORTANT .................................................. i I Duplex operation ................................. 20 I Tone/DTCS squelch operation............. 45 3 EXPLICIT DEFINITIONS ................................ i I AFC function........................................ 21 I Tone squelch frequency/DTCS code set- PRECAUTION ............................................... ii I NB/ANL functions ................................ 21 ting....................................................... 46 4 SUPPLIED ACCESSORIES ......................... iii I Band scope.......................................... 22 I DTCS polarity setting........................... 47 OPERATING THEORY ................................. iii I [DIAL] function assignment.................. 23 I Tone scan ............................................ 48 5 OPERATING NOTES ................................... iii 5 DUALWATCH OPERATION ............ 24–25 10 SET MODE ...................................... 49–59 6 TABLE OF CONTENTS ................................ iv I Setting audio volume ........................... 24 I General................................................ 49 QUICK REFERENCE GUIDE .................. I–VI I Squelch level setting............................ 24 I Set mode items.................................... 50 7 I Preparation ............................................. I I Main band selection............................. 25 11 OTHER FUNCTIONS ....................... 60–67 1 PANEL DESCRIPTION ........................ 1–7 I Band exchange.................................... 25 I Antenna selection ................................ 60 8 I Front, top and side panels .................... 1 6 MEMORY CHANNELS ..................... 26–33 I Weather channel operation ................. 61 I Function display .................................... 6 I General description ............................. 26 I Data cloning ........................................ 62 9 2 BATTERY CHARGING ...................... 8–10 I Memory channel programming............ 26 I Auto power-off function........................ 63 I Battery installation ................................. 8 I Memory bank setting ........................... 27 I IC recorder........................................... 64 10 I Caution .................................................. 9 I Memory bank selection........................ 28 I Partial reset ......................................... 67 I Battery charging .................................... 9 I Programming memory/bank name ...... 29 I All reset ............................................... 68 11 3 FREQUENCY AND CHANNEL SETTING I Selecting memory/bank name indication..... 30 12 CONTROL COMMAND ................... 68–69 12 .......................................................... 11–16 I Copying memory contents................... 31 I General................................................ 68 I Mode selection..................................... 11 I Memory clearing .................................. 32 I Data format.......................................... 68 13 I Operating band selection..................... 12 I Erasing/transferring bank contents...... 33 I Command table ................................... 68 I Setting a tuning step............................ 14 7 SCAN OPERATION ......................... 34–41 13 FREQUENCY TABLE ...................... 70–61 14 I Setting a frequency.............................. 14 I Scan types........................................... 34 I TV channels......................................... 70 I Selecting a memory channel ............... 10 I Full/band/programmed scan................ 35 I VHF marine channels .......................... 73 15 I Receive mode selection ...................... 16 I Scan edges programming ................... 36 I Weather channels................................ 73 I Lock function ....................................... 16 I Memory/bank/all bank scan................. 37 I Other communications in the USA ...... 74 16 4 BASIC OPERATION ........................ 17–23 I Auto-memory write scan...................... 38 I Other communications— other countries I Receiving............................................. 17 I Skip channel/frequency setting............ 39 ............................................................. 76 I Setting audio volume ........................... 17 I Scan resume condition ........................ 40 14 MAINTENANCE ..................................... 78 I Squelch level setting............................ 18 7 PRIORITY WATCH .......................... 42–44 I Troubleshooting ................................... 78 I Monitor function ................................... 18 I Priority watch types ............................. 42 15 SPECIFICATIONS ................................. 79 I Attenuator function .............................. 19 I Priority watch operation ....................... 43 16 OPTIONS ............................................... 80 iv
- 6. QUICK REFERENCE GUIDE I Preparation D Battery installation D Belt clip qRemove the battery cover from the receiver. Conveniently attaches to your belt. Attach the belt clip using the supplied screws. wInstall 3 R6(AA) size alkaline cell batteries. • Be sure to observe the correct polarity. w e q D Handstrap Slide the handstrap through the loop on the top of the rear panel as illustrated at below. Facilities carrying. Keep battery the contacts clean. It’s a good idea to clean the battery terminals once a week. I
- 7. QUICK REFERENCE GUIDE D Charging the battery Quick reference guide D Antenna IC-R20 Optional CP-18A/E Insert the supplied antenna into the Cigarette lighter cable antenna connector and screw down with DC-DC converter the antenna as shown at right. to cigarette lighter socket NEVER hold the antenna when car- to [DC] rying the receiver. jack AC adapter Keep the jack cover attached when BC-149A/D jack is not in use to protect the con- nectors from dust and moisture. ✔ For your information to AC outlet Third-party antennas may in- crease receiver performance. q Install the battery pack (BP-206). w Plug the AC adaptor into an AC outlet. e Insert the adaptor plug into the [DC] jack of the receiver. RWARNING!: NEVER charge the alkaline batteries. II
- 8. 1 PANEL DESCRIPTION I Front, top and side panels i q ANTENNA CONNECTOR (p. II) Connects the supplied antenna. u q w SQUELCH KEY [SQL] (p. 18) ➥ Push and hold to temporarily open the squelch and monitor the operating frequency. ➥ While pushing this key, rotate the tuning dial* to adjust the squelch level. w y e UP/DOWN KEYS [Y]/[Z] Y Z t Adjust audio volume level.* (p. 17) r r USB JACK [USB] Connect a PC via the optional OPC-1382 CLONING CABLE for Data/Audio cloning. e t EXTERNAL DC-IN CONNECTOR [DC] (p. 9) Connects an AC adaptor or an optional cigarette lighter KEYPAD cable for both charging the installed re-chargeable battery pack and operating. y EXTERNAL SPEAKER CONNECTOR [SP/CI-V] ➥ Connect an optional earphone or headphone. The internal speaker will not function when any exter- nal equipment is connected. (See p. 80 for a list of available options.) ➥ Connect an optional CT-17 for remote control operation. (p. 68) 1
- 9. PANEL DESCRIPTION 1 u LEFT DIAL [L-DIAL] qDUALWATCH/CLEAR KEY [DUALWATCH] 1 ➥ During single band operation, rotate to adjust audio vol- DUALWATCH ➥ Push for 1 sec. to toggle between single band ume level.* (p. 17) and dualwatch operation. (p. 24) ➥ During dualwatch operation, activates as the tuning dial ➥ Clears numeric key input. (p. 15) for upper side on the display.* ➥ Returns to previous operating condition while i RIGHT DIAL [R-DIAL] setting frequency or memory channel, or while ➥ Rotate to select the operating frequency.* (p. 12) in set mode. ➥ While scanning, changes the scanning direction.* ➥ Cancels the band scope or scan function. (p. 26) (pgs. 22, 35) ➥ While pushing [SQL], sets the squelch level.* (p. 18) ➥ While pushing [VFO MHz], sets the operating frequency w MAIN/SUB KEY [MAIN/SUB] (p. 25) in 1 MHz or 10 MHz in VFO mode.* (p. 14) MAIN/SUB ➥ During dualwatch operation, push to select the ➥ While pushing [BAND], selects the operating band in MAIN band or SUB band. VFO mode.* (p. 14) ➥ During dualwatch operation, push for 1 sec. to ➥ While dualwatch operation, activates as the tuning dial exchange the upper frequency and lower fre- for lower side on the display.* (p. 14) quency. e POWER KEY [PWR] KEYPAD Push for 1 sec. to turn the receiver power ON POWER DUALWATCH MAIN/SUB POWER and OFF. BAND VFO MODE MR MHz SCAN S.MW DIAL.SEL SWEEP CENTER r BAND KEY [BAND] 1 2 3 SCOPE ➥ Push to select the operating frequency band. T-SCAN SKIP M.N BAND 4 5 6 0 AFC (p. 14) TONE SET TS 7 8 9 LOCK ATT RF GAIN IC Recorder REC *The function of tuning control ([DIAL]) and volume control ([Y]/[Z]) can be traded. See page 23 for details. 2
- 10. 1 PANEL DESCRIPTION t VFO/MHz KEY [VFO MHz] i VOLUME/DIAL KEY [1 DIAL SEL] VFO ➥ Push to select VFO mode. (p. 11) DIAL SEL ➥ Inputs digit ‘1’ for frequency input, memory MHz ➥ Push for 1 sec. to toggle between the 1 MHz channel selection, etc. or 10 MHz tuning steps (p. 14 ➥ Push for 1 sec. to trade the volume control ([L- DIAL], [Y]/[Z]) and tuning control ([R-DIAL]) y MODE/SCAN KEY [MODE SCAN] functions. (p. 23) ➥ Push to select the operating mode (FM, WFM, MODE SCAN • √é appears when the [Y]/[Z] keys function as AM, USB, LSB, CW). (p. 16) a volume control. ➥ Push for 1 sec. to start a scan. (p. 35) o SWEEP KEY [2 SWEEP] (p. 22) SWEEP ➥ Inputs digit ‘2’ for frequency input, memory u MEMORY KEY [MR S.MW] channel selection, etc. MR ➥ Push to select between memory mode, TV ➥ Push for 1 sec. to select the tuning step for S.MW channel and PreSet channel. (p. 11) band scope function. Once a pushing this key, ➥ Push for 1 sec. to enter memory write condi- the band scope function sweeps once via the tion. (p. 26) new tuning step. ➥ Push for 2 sec. to write the operating fre- quency into the selected memory channel in !0 CENTER KEY [3 CENTER] (p. 22) VFO mode. CENTER ➥ Inputs digit ‘3’ for frequency input, memory Push [MR S.MW] for 2 sec. to transfer the dis- channel selection, etc. played frequency into the VFO in memory ➥ Push for 1 sec. to return the display frequency mode. (p. 31) of the band frequency. !1 SCOPE KEY [SCOPE] (p. 22) ➥ Push to activate the band scope function dur- SCOPE ing normal operating condition. Or push to stop continuous sweeping. ➥ Push for 1 sec. to start a continuous sweep- ing. 3
- 11. PANEL DESCRIPTION 1 !2 TONE SCAN KEY [4 T-SCAN] !5 AFC KEY [0 AFC] 1 T SCAN ➥ Inputs digit ‘4’ for frequency input, memory ➥ Inputs digit ‘0’ for frequency input, memory channel selection, etc. AFC channel selection, etc. 2 ➥ Push for 1 sec. to start a tone scan. (p. 48) ➥ Push for 1 sec. to turn the AFC (Automatic 3 Frequency Control) function ON and OFF. !3 FREQUENCY SKIP KEY [5 SKIP] 4 (p. 21) SKIP ➥ Inputs digit ‘5’ for frequency input, memory channel selection, etc. !6 TONE SQUELCH KEY [7 TONE] 5 ➥ Push for 1 sec. to turn the frequency skip TONE ➥ Inputs digit ‘7’ for frequency input, memory 6 function ON and OFF in VFO mode. (p. 39) channel selection, etc. 7 • “PSKIP” appears when the frequency skip function ➥ Push for 1 sec. to activate the following tone is in use. squelch functions in order. 8 ➥ Push for 1 sec. to set the memory channel as • Tone squelch — “TSQL” appears. (p. 46) 9 the following skip channel in memory mode in • Pocket beep — “TSQLS” appears. (p. 46) order. (p. 39) • DTCS squelch — “DTCS” appears. (p. 46) 10 • Skip channel — “SKIP” appears. • DTCS beep — “DTCSS” appears. (p. 46) 11 • Frequency skip channel — “PSKIP” appears. • VSC function — “VSC” appears. (p. 46) • Non-skip channel — no skip indicator appears. • No tone operation — no tone indicator appears. 12 ➥ Push for 1 sec. to program a paused fre- 13 !7 SET MODE KEY [8 SET] quency as a skip frequency while scanning. SET ➥ Inputs digit ‘8’ for frequency input, memory 14 (p. 39) channel selection, etc. !4 MEMORY NAME KEY [6 M.N] ➥ Push for 1 sec. to enter the set mode. 15 M.N ➥ Inputs digit ‘6’ for frequency input, memory 16 channel selection, etc. ➥ Push for 1 sec. to turn the memory name indi- cation ON and OFF. (p. 30) 4
- 12. 1 PANEL DESCRIPTION !8 TUNING STEP KEY [9 TS] @2 STOP/PLAY [I ≈] TS ➥ Push for 1 sec. to select the tuning step. ➥ Push to start the recorded audio. (p. 64) (p. 14) ➥ Push to stop the recording or playing audio. ➥ Inputs digit ‘9’ for frequency input, memory (p. 64) channel selection, etc. ➥ Push for 1 sec. to enter the play speed set mode. Push to select the item after selecting !9 LOCK KEY [• LOCK] with [R-DIAL]. (p. 65) ➥ Inputs MHz digit for frequency input. (p. 15) LOCK ➥ Push for 1 sec. to toggle the lock function ON @3 RECORD KEY [ REC] and OFF. (p. 16) REC ➥ Push for 1 sec. to enter the record set mode. •“ ” appears while the key lock function is in use. Push to select the item after selecting with [R- DIAL]. (p. 65) @0 REWIND/ATTENUATOR KEY [ΩΩ ATT] ➥ Push to start recording audio. (p. 64) ATT ➥ Push to select the track for recorded audio. ➥ Push to pause recording audio. (p. 64) (p. 64) ➥ Push and hold to rewind during playing the recorded audio. (p. 64) ➥ Push for 1 sec. to turn the attenuator function ON and OFF during normal operation. (p. 19) @1 SKIP/RF GAIN KEY [≈≈ RF GAIN] RF GAIN ➥ Push to select the track for recorded audio. (p. 64) ➥ Push and hold to skip the recorded audio. (p. 64) ➥ Push for 1 sec. to enter the RF GAIN set mode. Push to select the item after selecting with [R-DIAL]. (p. 19) 5
- 13. PANEL DESCRIPTION 1 I Function display 1 q w er t y !6 w e u 2 -DUP TSQL PS 3 -DUP TSQL AFC !0 !5 MODE FM ANL !4 145 000 PRIO 4 !4 145 000 t FM 000 i 5 !3 M:Amature2 w e u 6 PSKIP u q !5 o !2 √ PRI RIO µ 000 i !6 -DUP TSQL PS 7 ATT !4 433 000 PRIO 000 !0 i 8 FM 9 !1 !0 o !2 !1 !5 o 10 q BATTERY INDICATOR w DUPLEX INDICATORS (p. 20) 11 ➥“ ” appears when the installed batteries have “+DUP” appears when plus semi-duplex, “–DUP” appears 12 ample capacity. when minus semi-duplex (repeater) operation is selected. • They do not appear when operating with an external power 13 source. e SIGNAL SQUELCH INDICATORS ➥ “TSQL” appears while the tone squelch function is in 14 ➥“ ” appears when the batteries are nearing ex- haustion. use. (p. 46) 15 ➥ Scrolls while charging the installed BP-206. (p. 8) ➥ “DTCS” appears while the DTCS squelch function is in use. (p. 46) 16 ➥ “S” appears with the “TSQL” or “DTCS” indicator while the pocket beep function (with CTCSS or DTCS) is in ➥ Battery indicator blinks when completely charged. use. (p. 46) ➥ “VSC” appears while the VSC (Voice Squelch Control) function is in use. (p. 46) 6
- 14. 1 PANEL DESCRIPTION r ANL/NB INDICATOR (pgs. 21, 52) o SIGNAL STRENGTH INDICATOR ➥ “ANL” appears when the ANL (Automatic Noise Limitter) Shows the receivng signals relative to signal strength. function is in use. The ANL function is available only for !0 PRIORITY WATCH INDICATOR (p. 42) AM mode. Appears when priority watch is in use. ➥ “NB” appears when the noise blanker function is in use. The noise blanker function is available while in !1 ATTENUATOR INDICATOR (p. 19) LSB/USB/CW modes. Appears when the RF attenuator is in use. t LOCK INDICATOR (p. 16) !2 VOLUME/DIAL EXCHANGE INDICATOR (p. 23) Appears when the lock function is activated. ➥“√ ” appears when the normal operation. ➥“∂ ” appears when the functions of the tuning con- y AFC INDICATOR (p. 21) trol and volume control are traded. Appears when the lock function is activated. • The AFC function is available for single band operation only. !3 MEMORY/BANK NAME INDICATOR Shows the memory name or bank name. u SKIP INDICATORS (p. 39) • This indication is available when memory name or bank name is ➥ “SKIP” appears when the selected memory channel is programmed. specified as a skip channel. ➥ “PSKIP” appears when the displayed frequency is spec- !4 FREQUENCY READOUT ified as a skip frequency. Shows an operating frequency. • The smaller readout appears at right when tuning step is se- i CHANNEL SECTION INDICATOR (p. 11) lected 0.1 kHz or 0.01 kHz steps. ➥ “ µ ” and three digits channel number appear when • The decimal point blinks during scan. memory channel is selected. ➥ “ å ” and three digits channel number appear when !5 RECEIVE MODE INDICATOR (p. 16) auto-memory write channel is selected. Shows the selected receive mode. ➥ “TV” appears when TV channel is selected. • FM, WFM AM, LSB, USB and CW are available. ➥ “WX”* appears when weather channel is selected. !6 MAIN BAND INDICATOR (p. 24) *Available for the USA version only. “ å ” and “TV” indi- Shows the main band on upper display or lower display. cations appear for single band operation only. • This indication appears only when dualwatch operation. 7
- 15. BATTERY CHARGING 2 I Battery installation 1 Before installing, or replacing the batteries, push [POWER] D Battery pack installation 2 for 1 sec. to turn the power OFF. q Remove the battery cover from the receiver. 3 qRemove the battery cover from the receiver. w Remove the supplied battery spacer for R6 (AA) size bat- tery use. 4 e Install the Li-Ion battery pack (BP-206). 5 • Be sure to observe the correct direction. • Charge Li-Ion battery pack before use. 6 •Battery pack installation 7 8 wInstall 3 R6 (AA) size alkaline batteries. 9 • Be sure to observe the correct polarity. w 10 q e 11 12 •Battery pack removal 13 14 15 16 Keep the battery contacts clean to avoid rust or poor con- tact. It’s a good idea to clean the battery terminals once a week. 8
- 16. 2 BATTERY CHARGING I Caution I Battery charging D Battery caution D Regular charging • CAUTION! NEVER short the battery terminals. Also, current q Attach the battery pack (BP-206) to the receiver. (See may flow into nearby metal objects such as a necklace, so page 8) be careful when placing battery pack in handbags, etc. wPlug the AC adaptor (BC-149A/D*) into an AC outlet; or the • NEVER incinerate used battery pack or battery cells. Inter- optional CP-18A/E into a cigarette lighter socket. nal battery gas may cause explosion. * Not supplied with some versions. • NEVER mix old and new batteries. e Insert the adaptor plug into [DC] of the receiver. • Make sure all battery cells are the same brand, type and • Charging periods: 8 hours (w/BP-206) capacity. Either of the above may cause a fire hazard or damage the IC-R20 Optional CP-18A/E Cigarette lighter cable receiver if ignored. with DC-DC converter D Charging caution to cigarette • Recommended temperature for charging: lighter socket ±0˚C to +35˚C (; +32˚F to +95˚F) to [DC] jack • Connect the supplied (or optional for some versions) AC adaptor or optional cigarette lighter cable only when charg- AC adapter BC-149A/D ing the battery pack (BP-206). NEVER use other manufac- ture’s chargers. CAUTION: BE SURE to disconnect the CP-18A/E from to AC outlet the cigarette lighter socket when charging is finished, be- cause, a slight current still follows in the CP-18A/E and the vehicle’s battery will become exhausted. 9
- 17. BATTERY CHARGING 2 D CP-18A/E fuse replacement D Rapid charging with the BC-156 If the fuse blows or the receiver stops functioning while oper- The optional BC-156 provides rapid charging of battery ating with the optional CP-18A/E, find the source of the prob- packs. 2 lem if possible, and replace the damaged fuse with a new rated one (FGB 5 A) as shown below. • Charging periods: 2.5 hours (w/BP-206) Shorten or remove the antenna. Turn power OFF. Check the orientation. Fuse 5 A BC-156 CAUTION: Shorten or remove the telescoping antenna be- fore charging to prevent the receiver from overturning. If the charge indicator flashes orange, there may be a problem with the battery pack (or charger). Reinsert the battery pack or contact your dealer. 10
- 18. 3 FREQUENCY AND CHANNEL SETTING I Mode selection D VFO mode D Memory mode/PreSet*/TV*/Weather† channels VFO mode is used for the desired frequency setting within the Memory mode is used for operation of memory channels frequency coverage. which have programmed frequencies. PreSet channels are used for most-often used frequencies for quick recall. ➥ Push [VFO MHz] to select VFO mode. *Appears only when PreSet channels/TV channels are • VFO mode indication programmed via the optional CS-R20. DUALWATCH MAIN/SUB POWER -DUP TSQL AFC † Available for the USA version only. VFO MODE FM ANL 146 560 BAND VFO MODE MR DIAL.SEL MHz SWEEP SCAN CENTER S.MW MHz qPush [MR S.MW] to select the memory mode, PreSet, TV 1 2 3 SCOPE or Weather channel in sequence. T-SCAN SKIP M.N PSKIP w Rotate [R-DIAL] to select the desired channel. 4 5 6 0 AFC √ TONE SET TS • Only programmed memory channels can be selected. 7 8 9 ATT RF GAIN LOCK IC Recorder • Entering keypad directly can be selected the desired channel. REC • See p. 26 for memory programming details. • Memory mode indication DUALWATCH MAIN/SUB POWER What is VFO? -DUP TSQL AFC MR MODE FM ANL VFO is an abbreviation of Variable Frequency Oscillator. Fre- 146 100 BAND VFO MODE MR MHz SCAN S.MW S.MW DIAL.SEL SWEEP CENTER quencies for receiving are generated and controlled by the 1 2 3 SCOPE VFO. T-SCAN SKIP M.N PSKIP 4 5 6 0 AFC √ µ 001 TONE SET TS 7 8 9 LOCK ATT RF GAIN IC Recorder REC “µ ” and memory channel number appear. 11
- 19. FREQUENCY AND CHANNEL SETTING 3 I Operating band selection The receiver can receive the AM broadcast, HF bands, • Memory mode indication • TV channel indication 50 MHz, FM broadcast, VHF air, 144 MHz, 300 MHz, 400 MHz, 800 MHz,* 1200 MHz or 2400 MHz. 3 -DUP TSQL AFC -DUP TSQL AFC MODE FM ANL MODE WFMANL 146 100 2 ch ➥ Push [BAND] several times to select the desired frequency band. PSKIP PSKIP • When a memory mode is selected, push [VFO MHz] to select √ µ 001 √ TV VFO mode first, then push [BAND] to select the desired band. ➥ While pushing and holding [BAND], rotating [R-DIAL] also “µ ” and memory channel “TV” indication appears. selects frequency band. number appear. • PreSet channel indication • Weather channel indication (USA version only) [R-DIAL] -DUP TSQL AFC -DUP TSQL AFC MODE WFMANL MODE FM ANL 76 000 1 PSKIP PSKIP √ 0 √ WX BAND PreSet channel number appears. “WX” indication appears. Available frequency bands are differ depending on version. See the specification for details. *Some frequency ranges are inhibited for the USA version due to local regulation. 12
- 20. 3 FREQUENCY AND CHANNEL SETTING • Available frequency bands MODE AM MODE AM MODE FM MODE WFM 1620 5 000 51 000 76 000 AM broadcast band HF band 50 MHz band FM broadcast band MODE AM : Push BAND 118 000 VHF air band MODE FM 2425 000 BAND : Rotating while pushing 2400 MHz band Initial frequencies shown are differ according to version. MODE FM 146 010 144 MHz band MODE FM MODE FM MODE FM MODE FM 1295 000 800 000 440 000 370 000 1200 MHz band 800 MHz band 400 MHz band 300 MHz band 13
- 21. FREQUENCY AND CHANNEL SETTING 3 I Setting a tuning step I Setting a frequency The tuning step can be selected for each frequency band in- D Using the dial dependently , however, the tuning steps, 8.33 kHz and 9 kHz, q Push [VFO MHz] to select VFO mode, if necessary. are appeared when setting the tuning step for the VHF air w Select the desired frequency band with [BAND]. 3 band and AM broadcast band, respectively. The following tun- • Or, while pushing and holding [BAND], rotate the [R-DIAL] to se- ing steps are available for the IC-R20. lect the desired frequency band. • 0.01 kHz • 0.1 kHz • 1.0 kHz • 5.0 kHz • 6.25 kHz e Rotate [R-DIAL] to select the desired frequency. • 8.33 kHz • 9.0 kHz • 10.0 kHz • 12.5 kHz • 15.0 kHz • The frequency changes according to the preset tuning steps. • 20.0 kHz • 25.0 kHz • 30.0 kHz • 50.0 kHz • 100.0 kHz See the left section for setting the tuning step. • Push [VFO MHz] for 1 sec. then rotate [R-DIAL] to change the D Tuning step selection frequency in 1 MHz steps, or push for 1 sec. again then rotate [R-DIAL] to change the frequency in 10 MHz steps. (Each push q Push [VFO MHz] to select VFO mode, if necessary. for 1 sec. toggles 1 MHz or 10 MHz tuning steps.) w Push [BAND] to select the desired frequency band. • Or, while pushing and holding [BAND], rotate the [R-DIAL] to se- lect the desired frequency band. e Push [9 TS] for 1 sec. to enter tuning step selecting condition. r Rotate [R-DIAL] to select the desired tuning step. [R-DIAL] MODE FM t Push [9 TS] to return to VFO mode. 146 010 00 [R-DIAL] changes the frequen- [R-DIAL] cy according to the selected -DUP TSQL AFC MODE FM ANL BAND tuning step. 146 010 VFO MODE FM BAND √ PSKIP MHz 146 010 00 SET TS:5.0kHz VFO MHz While pushing [VFO MHz], [R- TS 5 kHz tuning step DIAL] changes the frequency in 9 1 MHz steps (default). 14
- 22. 3 FREQUENCY AND CHANNEL SETTING D Using the keypad The frequency can be directly set via numeral keys. • When editting a frequency outside of the fre- Pushing [VFO MHz] omits the entry of 100 kHz and below, when you want to quency range, the previously displayed frequency edit to these digits “0.” Push [DUALWATCH] to cancel the entry. is automatically recalled after editting last digit. qPush [VFO MHz] to select VFO mode, if • Editting to 0.684 MHz • Editting to 1260 MHz • Changing 100 kHz and necessary. below. w Enter the desired frequency via the keypad. • Direct input can be set until 1 kHz digit, rotate MODE AM MODE FM Editting 1260.000 MHz [R-DIAL] to set below 1 kHz frequency after set tuning steps, if necessary. (See the previ- 0 AFC 000 010 1 1 000 to 1260.240 MHz ous page for setting the tuning step.) MODE AM MODE FM MODE FM LOCK 000 010 2 12 000 LOCK 1260 240 DUALWATCH MODE AM MODE FM MODE FM VFO MHz 6 000 684 6 126 000 2 1260 240 1 2 3 MODE AM MODE FM MODE FM 4 5 6 0 AFC 8 000 684 0 AFC 1260 000 4 1260 240 7 8 9 LOCK MODE AM MODE FM MODE FM 000 684 1260 000 1260 240 VFO 4 MHz 0 AFC 15
- 23. FREQUENCY AND CHANNEL SETTING 3 I Receive mode selection I Lock function 1 Receive modes are determined by the physical properties of To prevent accidental frequency changes and unnecessary 2 the radio signals. The receiver has 6 receive modes: FM, function access, use the lock function. WFM, AM, LSB, USB and CW modes. The mode selection is 3 stored independently in each band and memory channels. ➥ Push [• LOCK] for 1 sec. to turn the lock function ON and 4 OFF. Typically, AM mode is used for the AM broadcast stations •“ ” appears while the lock function is activated. 5 (0.495–1.620 MHz) and VHF air band (118–135.995 MHz), Y Z • [SQL] and [Y]/[Z] can be used while the lock function is in use Y Z with default setting. Either or both [SQL] and [Y]/[Z] keys are 6 and WFM is used for FM broadcast stations (76–107.9 MHz). also be locked in set mode. (p. 49) 7 ➥ Push [MODE SCAN] several times to select the desired “ ” appears while the 8 receive mode. DUALWATCH MAIN/SUB POWER lock function is in use. BAND VFO MODE MR 9 -DUP TSQL AFC MHz SCAN S.MW MODE FM 10 146 010 DIAL.SEL SWEEP CENTER MODE FM ANL 146 010 DUALWATCH MAIN/SUB POWER 1 2 3 SCOPE T-SCAN SKIP M.N BAND VFO MHz MODE SCAN MR S.MW MODE SCAN PSKIP 4 5 6 0 AFC 11 DIAL.SEL SWEEP CENTER TONE SET TS PSKIP FM mode √ 1 T-SCAN 2 SKIP M.N 3 SCOPE 7 ATT 8 RF GAIN 9 LOCK IC Recorder LOCK 12 4 5 6 0 AFC MODE AM REC 13 118 000 TONE SET TS 7 8 9 LOCK ATT RF GAIN IC Recorder REC 14 PSKIP AM mode 15 MODE WFM 16 76 000 PSKIP WFM mode 16
- 24. 4 BASIC OPERATION I Receiving I Setting audio volume Make sure charged battery pack (BP-206) or brand new al- The audio level can be adjusted through 39 levels. kaline batteries are installed (p. 8). ➥ Push and hold [SQL], rotate [L-DIAL] or push [Y] or [Z] to Y Z q Push [POWER] for 1 sec. to turn power ON. adjust the audio level. wRotate [L-DIAL] (or push [Y] or [Z]) to set the desired Y Z Y Z • While using [Y]/[Z], pushing and holding either key change the audio level. audio level continuously. • The frequency display shows the volume level while setting. See • The display shows the volume level while setting. the section at right for details. -DUP TSQL AFC e Set the receiving frequency. (p. 14) [L-DIAL] MODE FM ANL r Set the squelch level. (p. 18) • While pushing [SQL], rotate [R-DIAL]. 146 010 SQL PSKIP • The first click of [R-DIAL] indicates the current squelch level. √ • “LEVEL 1” is loose squelch and “LEVEL 9” is tight squelch. VOL • “AUTO” indicates automatic level adjustment with a noise pulse count system. Minimum setting • Push and hold [SQL] to open the squelch manually. (no audio) tWhen a signal is received: • Squelch opens and audio is emitted. • The S-meter shows the relative signal strength level. √ VOL r Push for setting e Set frequency the squelch r Set squelch level (Push to monitor) √ VOL w Set audio level Maximum setting q [POWER] e Select band 17
- 25. BASIC OPERATION 4 I Squelch level setting I Monitor function The squelch circuit mutes the received audio signal depend- This function is used to listen to weak signals without disturb- ing on the signal strength. The receiver has 9 squelch levels, ing the squelch setting or to open the squelch manually even a continuously open setting and an automatic squelch setting. when mute functions such as the tone squelch are in use. ➥ While pushing and holding [SQL], rotate [R-DIAL] to se- 4 ➥ Push and hold [SQL] to monitor the operating frequency. lect the squelch level. • The 1st segment of the S-meter blinks. • “LEVEL 1” is loose squelch and “LEVEL 9” is tight squelch. • “AUTO” indicates automatic level adjustment with a noise pulse count system. -DUP TSQL AFC • “OPEN” indicates continuously open setting. MODE FM ANL [R-DIAL] SQL 146 010 -DUP TSQL AFC MODE FM ANL PSKIP √ 146 010 PSKIP SQL √ The 1st segment blinks SQUELCH:AUTO Automatic squelch The [SQL] key can be set to ‘sticky’ operation in expanded -DUP TSQL AFC set mode. See page 54 for details. MODE FM ANL 146 010 PSKIP √ SQUELCH:LEVEL9 Maximum level 18
- 26. 4 BASIC OPERATION I Attenuator function I RF gain The attenuator prevents a desired signal from distorting when The receiver gain can be reduced with the RF gain setting. very strong signals are near the desired frequency or when This may help to remove undesired weak signals while mon- very strong electric fields, such as from a broadcasting sta- itoring strong signals. The RF gain may be useful for setting a tion, are near your location. minimum level at which to hear signals for SSB/CW modes . ➥ Push [ΩΩ ATT] for 1 sec. to toggle the attenuator function ➥ Push [≈≈ RF GAIN] for 1 sec. to enter the RF gain set- ON and OFF. ting condition, then rotate [R-DIAL] to select the desired • “ATT” appears when the attenuator function is in use. RF gain level. • Normally this setting is used maximum level. • Push [DUALWATCH] to exit the RF gain setting condition. DUALWATCH MAIN/SUB POWER VFO MODE MR -DUP TSQL AFC [R-DIAL] BAND MHz SCAN S.MW -DUP TSQL AFC MODE FM ANL MODE USBANL 146 010 DIAL.SEL SWEEP CENTER 1 T-SCAN 2 SKIP M.N 3 SCOPE 14 120 4 5 6 0 AFC PSKIP PSKIP TONE SET TS √ √ 7 8 9 LOCK ATT RF GAIN IC Recorder ATT ATT SET-RF-GAIN:MAX REC Maximum level “ATT” appears while the attenuator functions is in -DUP TSQL AFC MODE USBANL use. RF GAIN 14 120 PSKIP √ SET-RF-GAIN:5 Setting level5 19
- 27. BASIC OPERATION 4 I Duplex operation USING EXPANDED SET MODE Duplex communication uses 2 different frequencies for trans- r Rotate [R-DIAL] to select “ON.” mitting and receiving. Generally, duplex is used in communi- tRotate [R-DIAL] to select “OFFSET FREQ,” then push cation through a repeater, some utility communications, etc. [8 SET]. OFFSET-FREQ 4 During duplex operation, the transmit station frequency is ---------------- shifted from the receive station frequency by the offset fre- ----0.000.00 quency. Repeater information (offset frequency and shift di- rection) can be programmed into memory channels. (p. 26) yRotate [R-DIAL] to set the desired offset frequency within D Setting 0.00000–159.99999 MHz range, then push [8 SET]. q Set the receive station frequency (repeater output frequency). • The tuning step, selected in VFO mode, is used for setting. w Push [8 SET] for 1 sec. to enter set mode. • Push [VFO MHz] for 1 sec. then rotate [R-DIAL] to change the eRotate [R-DIAL] to select “SET EXPAND” item, then push frequency in 1 MHz steps, or push for 1 sec. again then rotate [R-DIAL] to change the frequency in 10 MHz steps. (Each push [8 SET]. for 1 sec. toggles 1 MHz or 10 MHz tuning steps.) [R-DIAL] u Rotate [R-DIAL] to select “DUPLEX.” ***-SET-MODE-*** ---------------- -NOISE-BLANKER DUPLEX -ANL ---------------- -AF-FILTER >OFF -AM-ANTENNA --DUP -FM-ANTENNA -+DUP >SET-EXPAND DUALWATCH iRotate [R-DIAL] to select “–DUP” or “+DUP.” o Push [DUALWATCH] to exit set mode. SET !0 Push and hold [SQL] to monitor the transmit station fre- 8 quency (repeater input frequency) directly. 20
- 28. 4 BASIC OPERATION -DUP TSQL AFC MODE FM ANL 1260 000 I AFC function I NB/ANL function√ PSKIP The AFC (Automatic Frequency Control) function tunes the The NB (noise blanker) function removes pulse-type noise ATT displayed frequency automatically when an off-center fre- when USB, LSB or CW mode is selected. The ANL (Auto- quency is received. It activated in FM/WFM modes only with matic Noise Limitter) function reduces noise components single band operation. when AM mode is selected. ➥ Push [0 AFC] to toggle the AFC function ON and OFF. • “AFC” appears when the AFC function is in use. See page 22 for setting details “AFC” appears while the DUALWATCH MAIN/SUB POWER AFC function is in use. NOTE: No display indication appears during dualwatch function, but both functions are activate while in specific BAND VFO MODE MR DIAL.SEL MHz SWEEP SCAN CENTER S.MW -DUP TSQL AFC modes. 1 2 3 SCOPE MODE FM ANL T-SCAN 4 TONE SKIP 5 SET M.N 6 TS 0 AFC 0 AFC 1260 000 PSKIP 7 8 9 ATT RF GAIN LOCK IC Recorder √ REC ATT “ ” or “ ” appears when an off-frequency is received. NOTE: The AFC function is not available during duwal- watch operation. 21
- 29. BASIC OPERATION 4 I Band scope 1 The band scope function allows you to visually check a spec- e Push [SCOPE] momentarily to start single sweeping or 2 ified frequency range. Sweep range can be selected from ±14 push for 1 sec. to start continuous sweeping. kHz through ±1400 kHz. 3 • Signal conditions (strengths) appear starting from the center of the range. 4 q Set the desired frequency as band scope center frequency. r Rotate [R-DIAL] to set the highlighted cursor to the de- 5 w While pushing and holding [2 SWEEP], rotate [R-DIAL] to sired waveform and set the frequency of the signal. select the sweep steps, if desired. • Push [3 CENTER] for 1 sec. to return to original sweep center 6 • Available steps are 1, 5, 6.25, 8.33, 9, 10, 12.5, 15, 20, 25, 30, frequency. 7 50 and 100 kHz. t Push [DUALWATCH] to cancel sweeping and returns to • Each pushing [SWEEP] changes the sweep step and starts sin- normal condition. 8 gle sweeping at each times. 9 [R-DIAL] ✔ CONVENIENT! 10 -DUP TSQL AFC The scope function can also be started with the following op- MODE FM ANL eration for easy setting. 11 145 780 q Set the desired frequency as band scope center frequency. 12 PSKIP √ wPush [SWEEP] for 1 sec. to start single sweeping. 13 SWEEP • Each pushing [SWEEP] changes the sweep step and starts sin- SWEEP 10k gle sweeping at each times. 14 2 15 16 22
- 30. 4 BASIC OPERATION I [DIAL] function assignment The frequency control dial can be traded with an audio volume • Single band operation Y Z control dial or [Y]/[Z] keys to suit your preference. “√ ” indication “∂ ” indication Frequency, Memory channel, Audio volume ➥ Push [1 DIAL] for 1 sec. to toggle the dial function from tun- Squelch level, Scanning ing dial and audio volume. [R-DIAL] direction, Set mode item • “∂ Y Z ” appears when [Y]/[Z] function as an tuning dial. and condition set Audio volume set Frequency, Memory channel, [R-DIAL] -DUP TSQL AFC [L-DIAL] Squelch level, Scanning MODE FM ANL [Y]/[Z] direction, Set mode item [L-DIAL] 146 560 and condition set PSKIP √ • Dualwatch operation “ ” indication “ ” indication Frequency, Memory channel, Audio volume [R-DIAL] Squelch level, Scanning DIAL.SEL ∂ [L-DIAL] direction, Set mode item 1 and condition set Audio volume set Frequency, Memory channel, -DUP TSQL PS Squelch level, Scanning [Y]/[Z] direction, Set mode item 145 25000 PRIO 000 and condition set FM AFC -DUP TSQL PS 438 00000 PRIO 000 FM FM 23