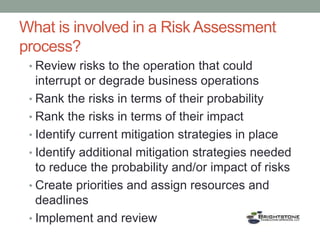
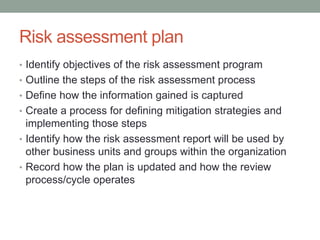
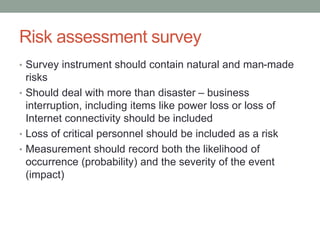
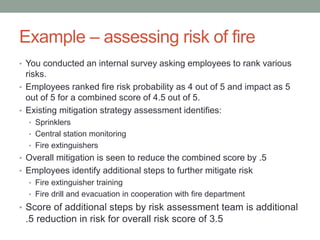
The document by Jim Booth emphasizes the importance of information security and risk assessment for regulatory compliance, operational improvement, and employee involvement. It outlines a structured risk assessment process that includes identifying, ranking, and mitigating risks affecting business operations, alongside creating and implementing a risk assessment plan. The document also provides examples of risk measurement and mitigation strategies, particularly focusing on risks like fire and employee error.