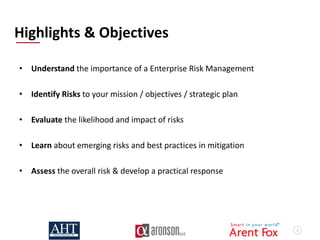
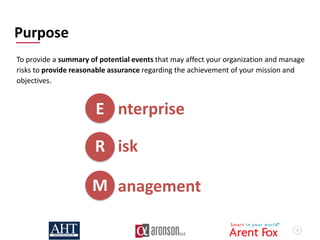
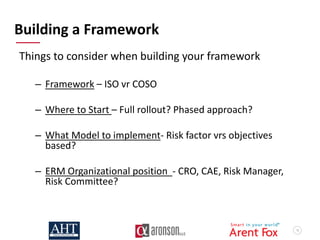
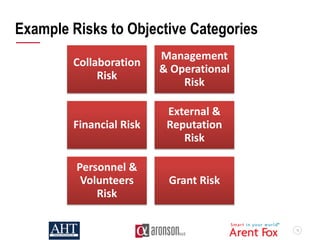
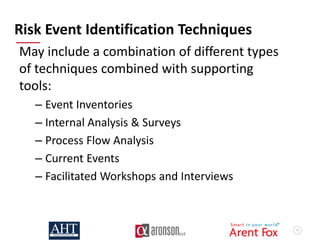
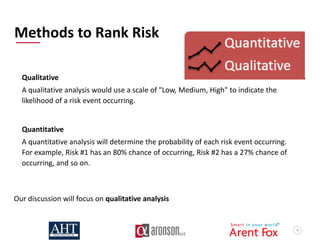
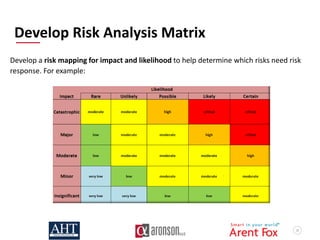
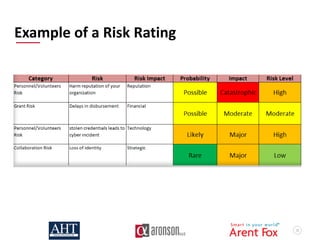
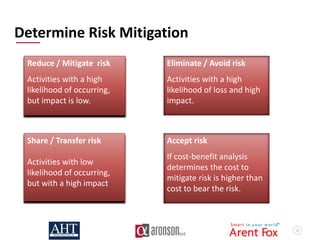
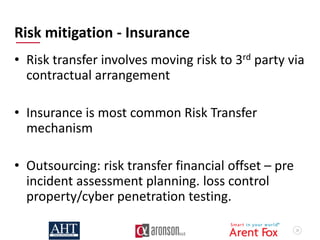
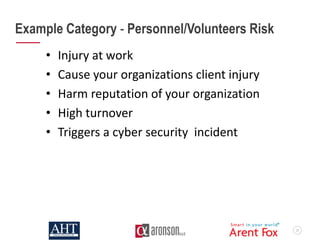
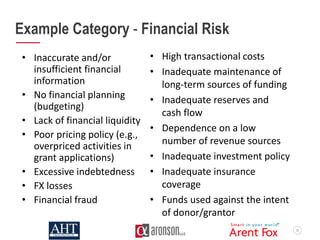
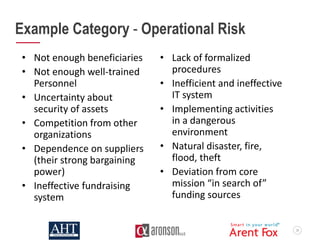
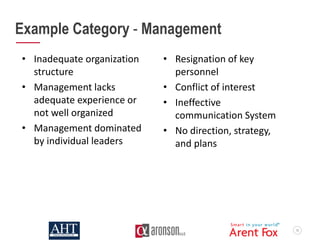
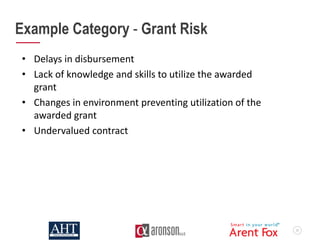
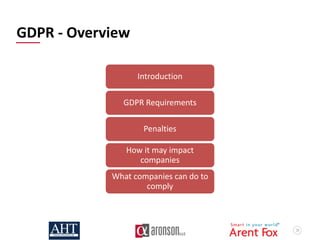
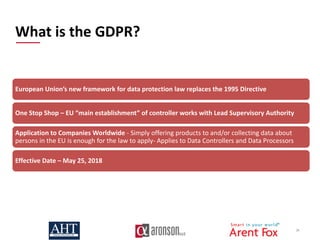
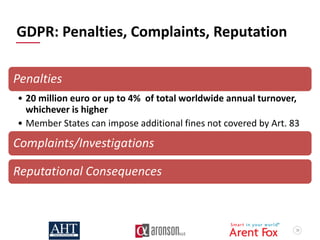
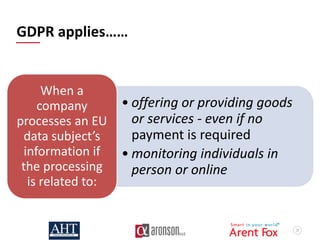
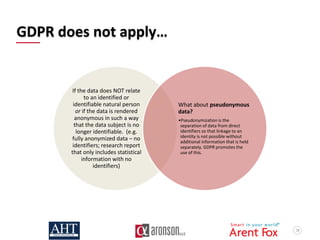
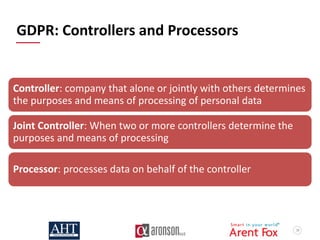
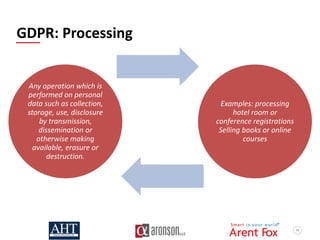
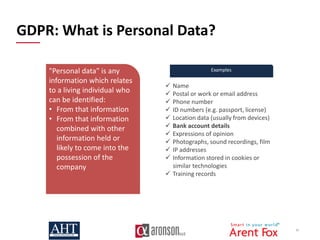
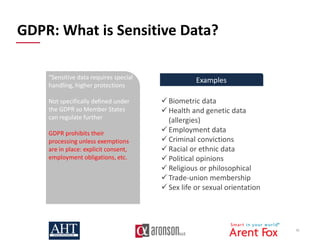
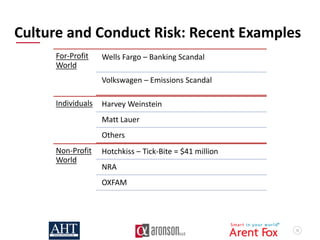
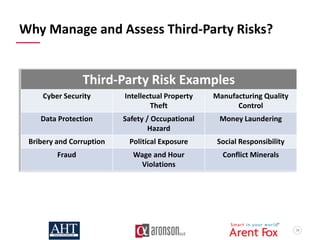
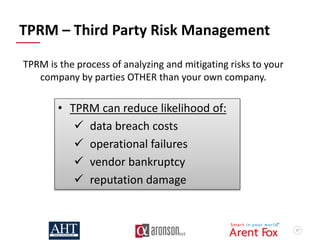
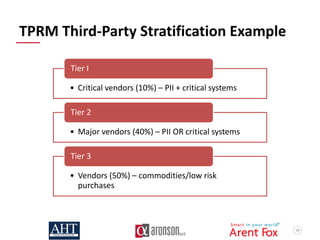
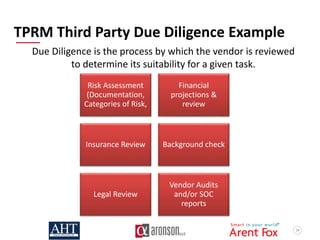
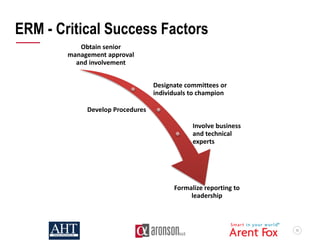
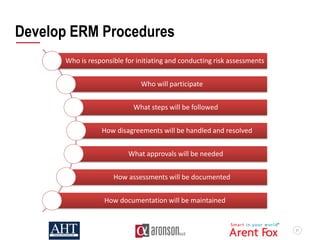
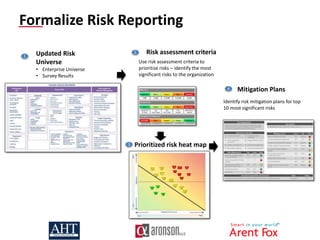
The document outlines enterprise risk management (ERM) practices and the importance of identifying and mitigating emerging risks relevant to organizations, particularly focusing on nonprofits and educational institutions. It highlights the roles of key professionals in risk advisory and data protection, offering strategies for risk assessment, mitigation, and compliance with regulations like GDPR. Additionally, it emphasizes the need for a structured approach to ERM, covering various types of risks such as operational, financial, and reputational, while providing guidelines for developing a robust risk management framework.