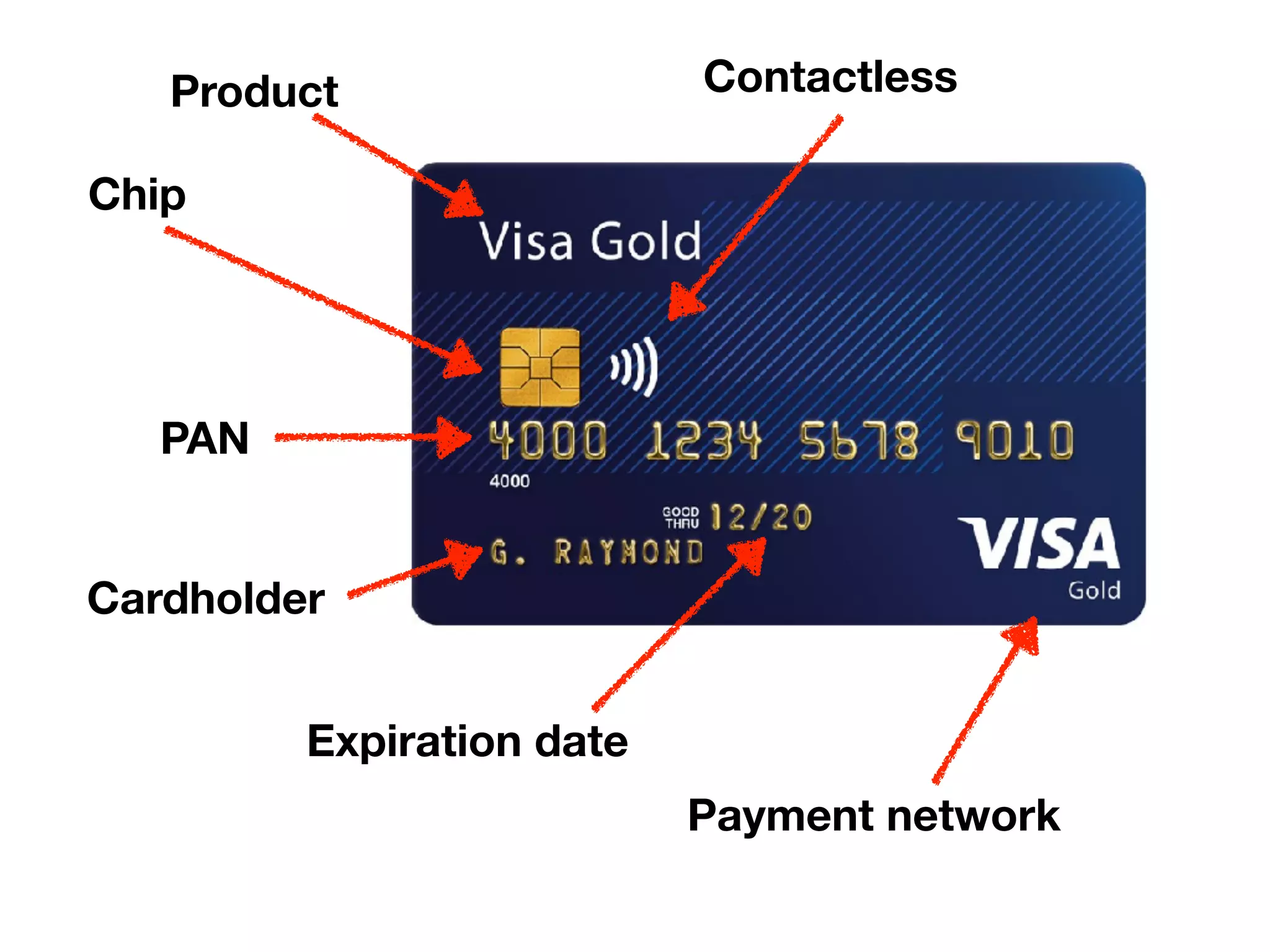
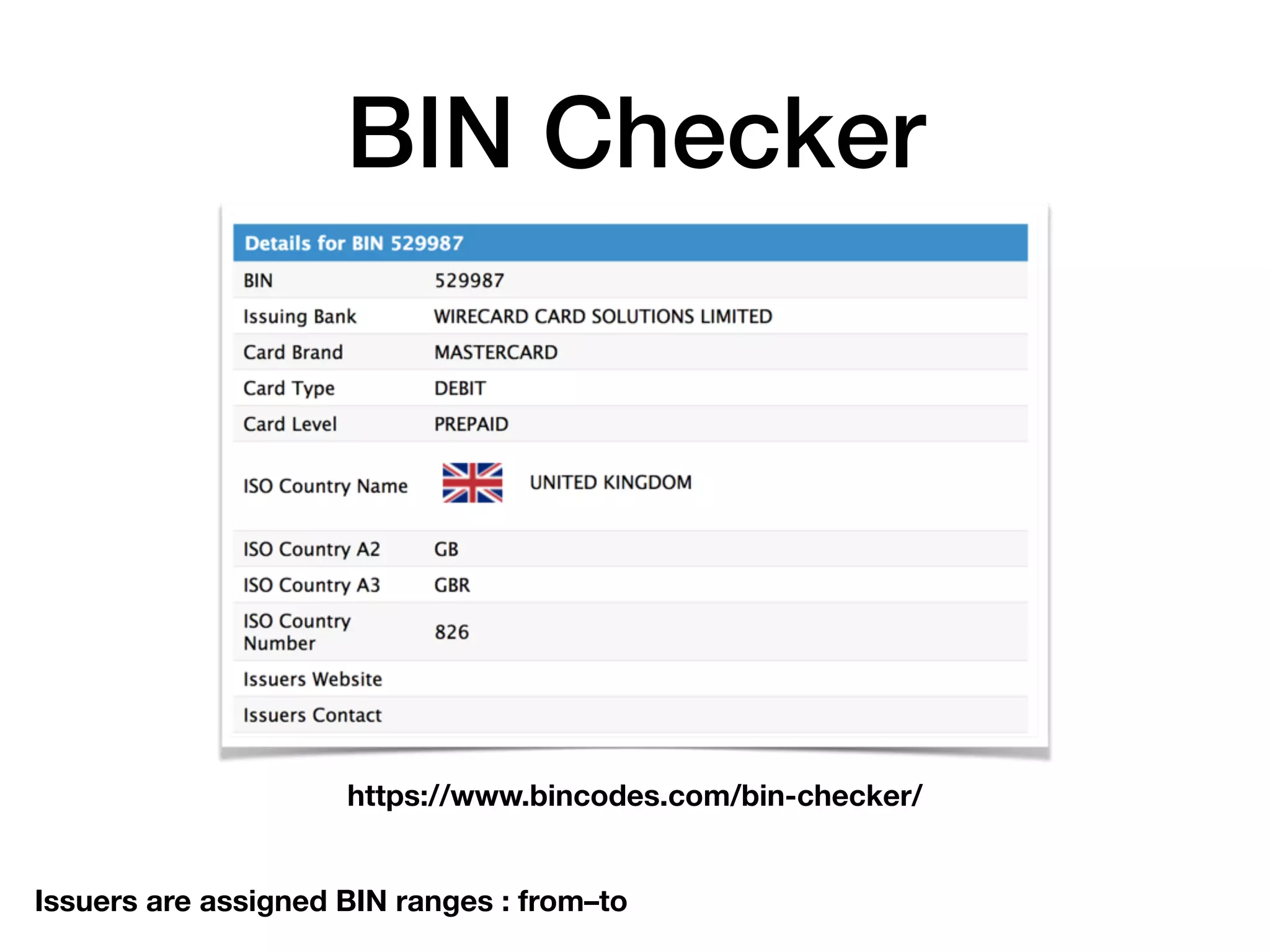
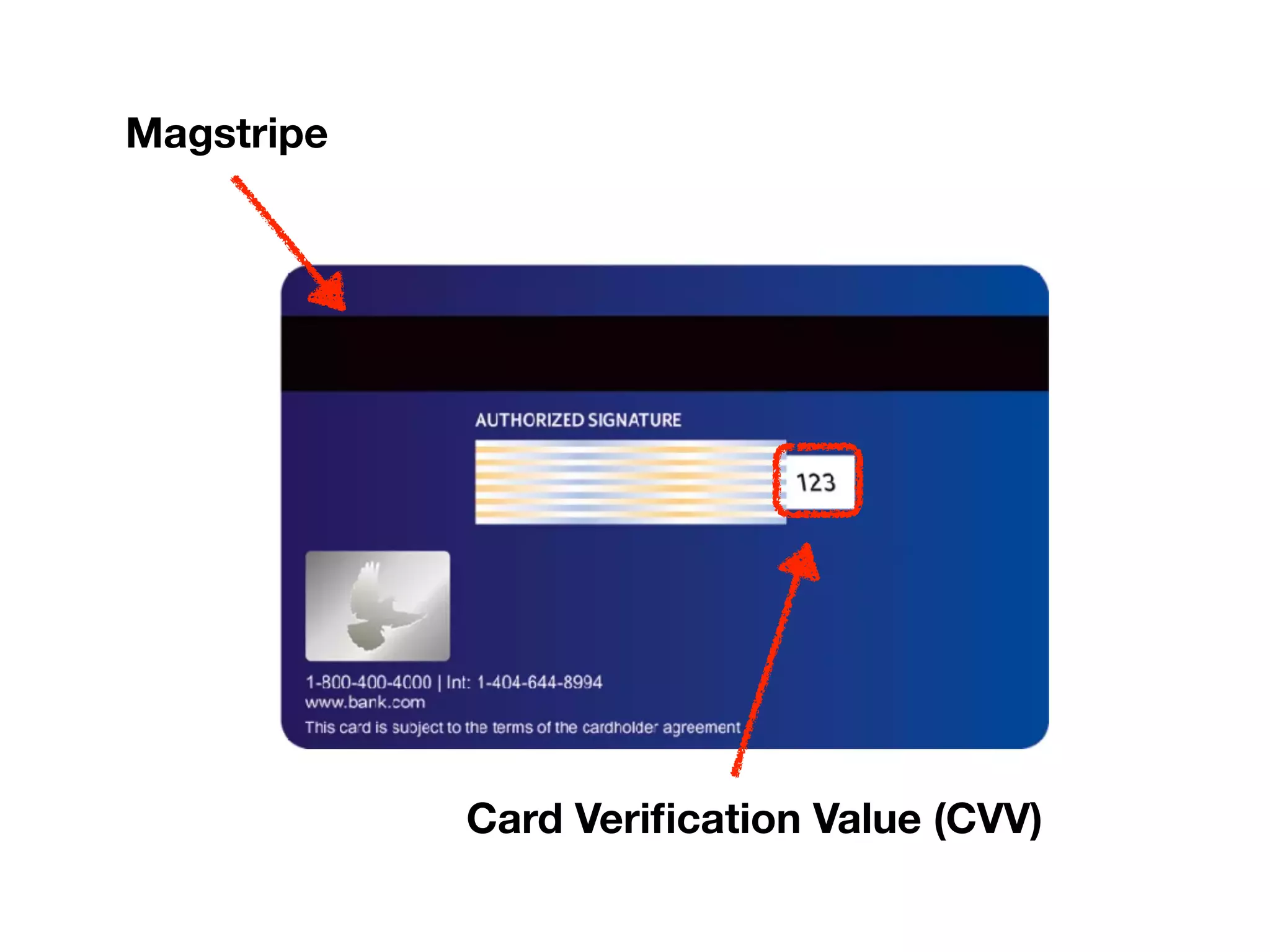
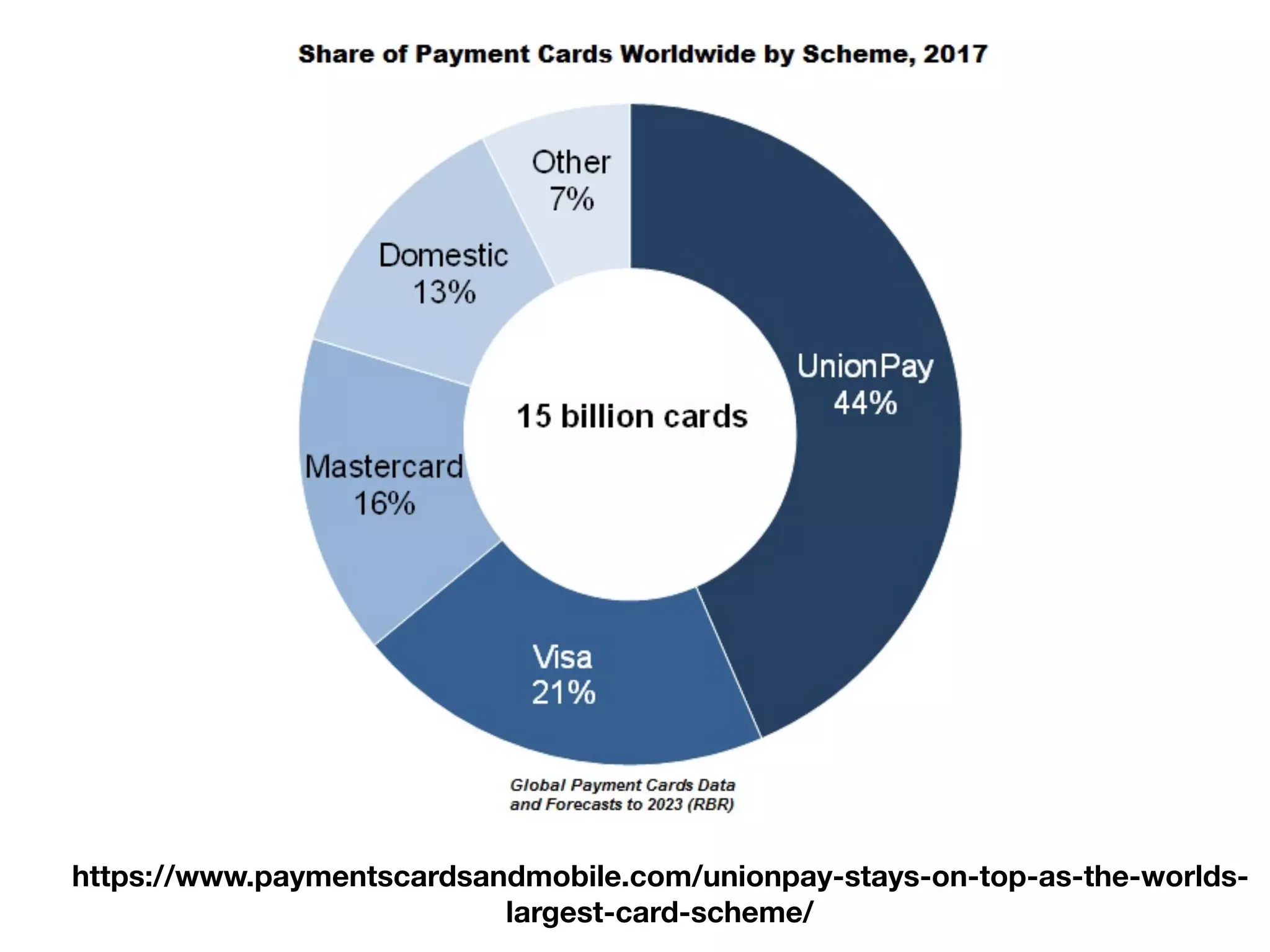
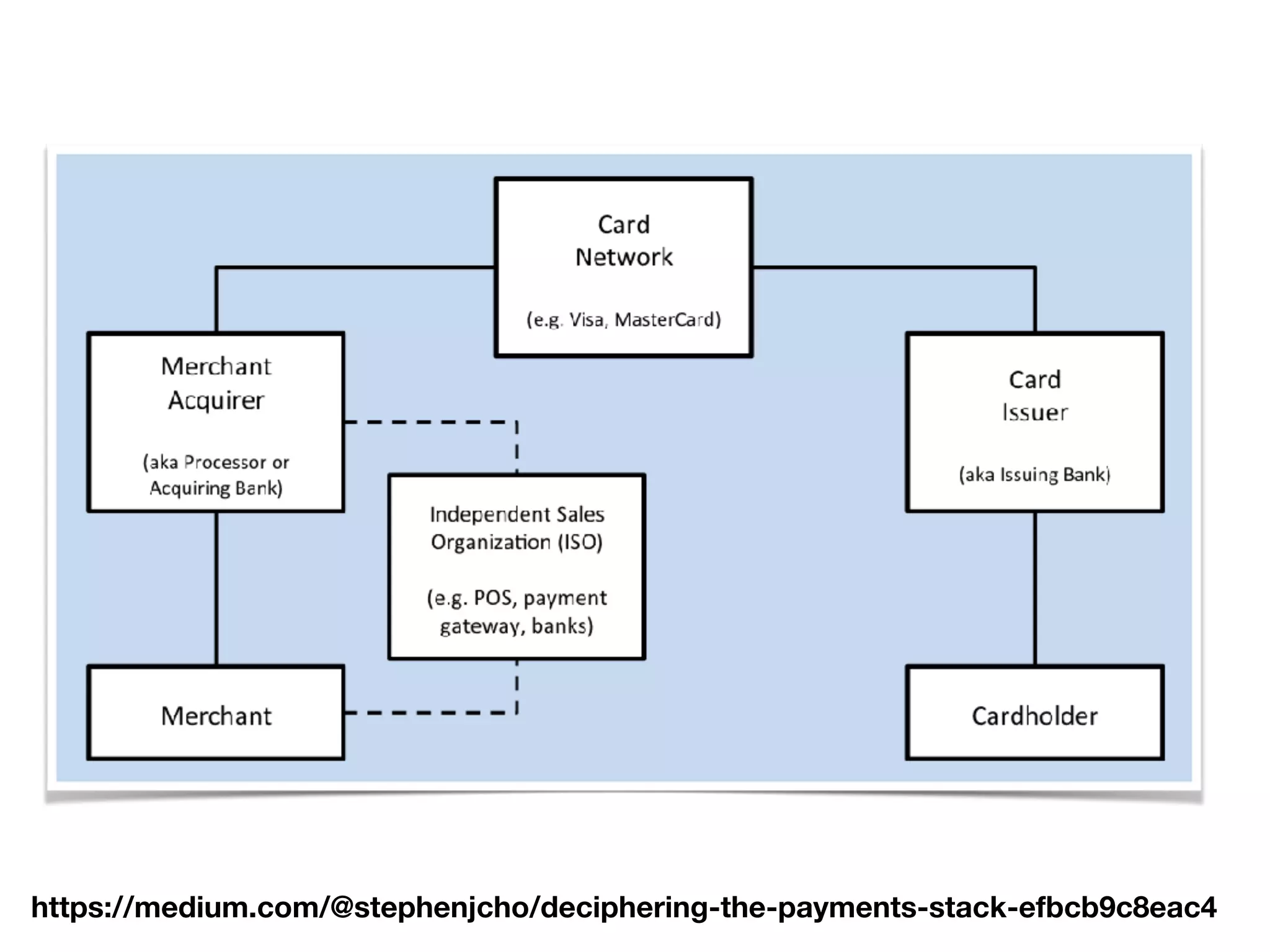
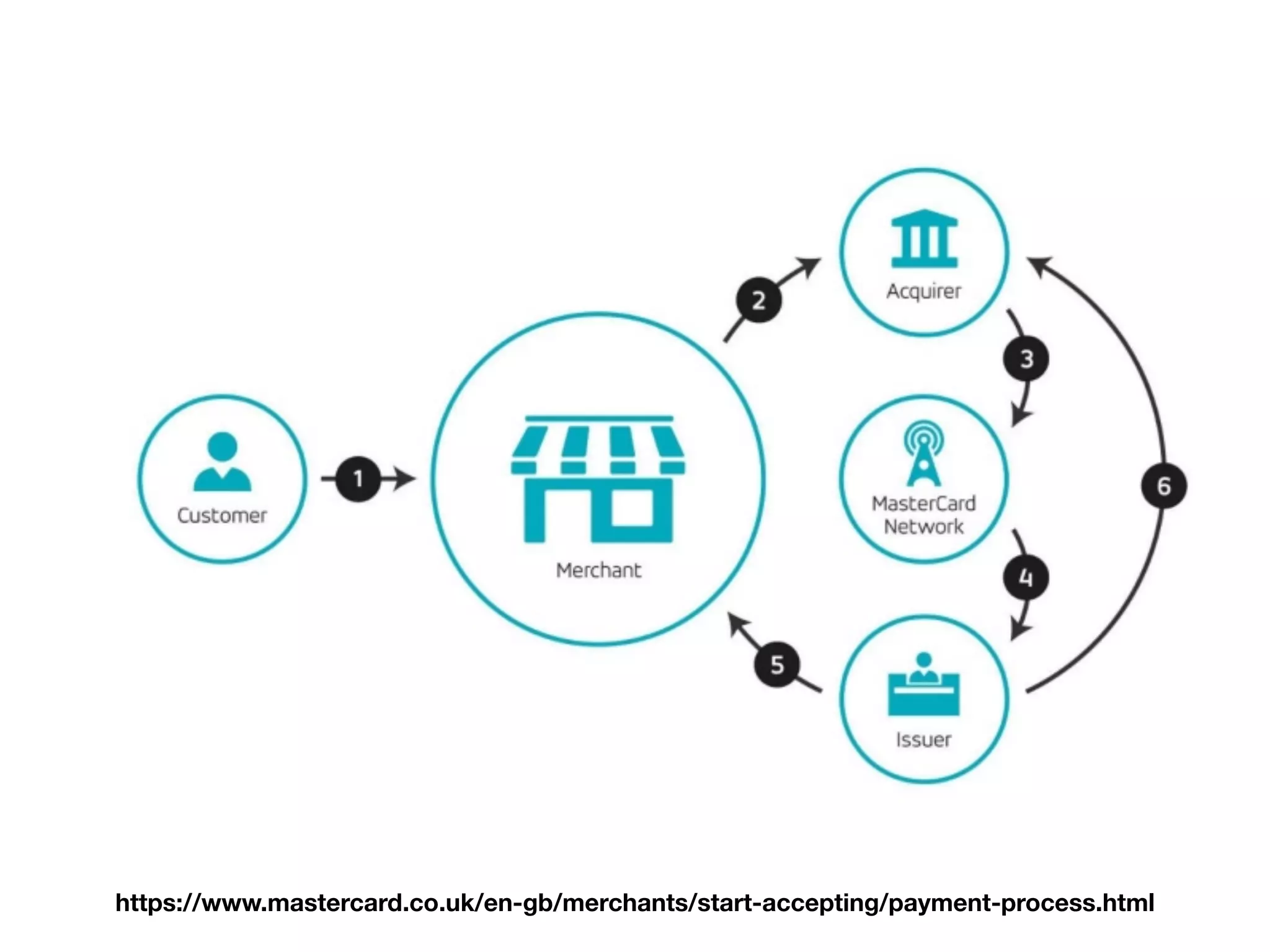
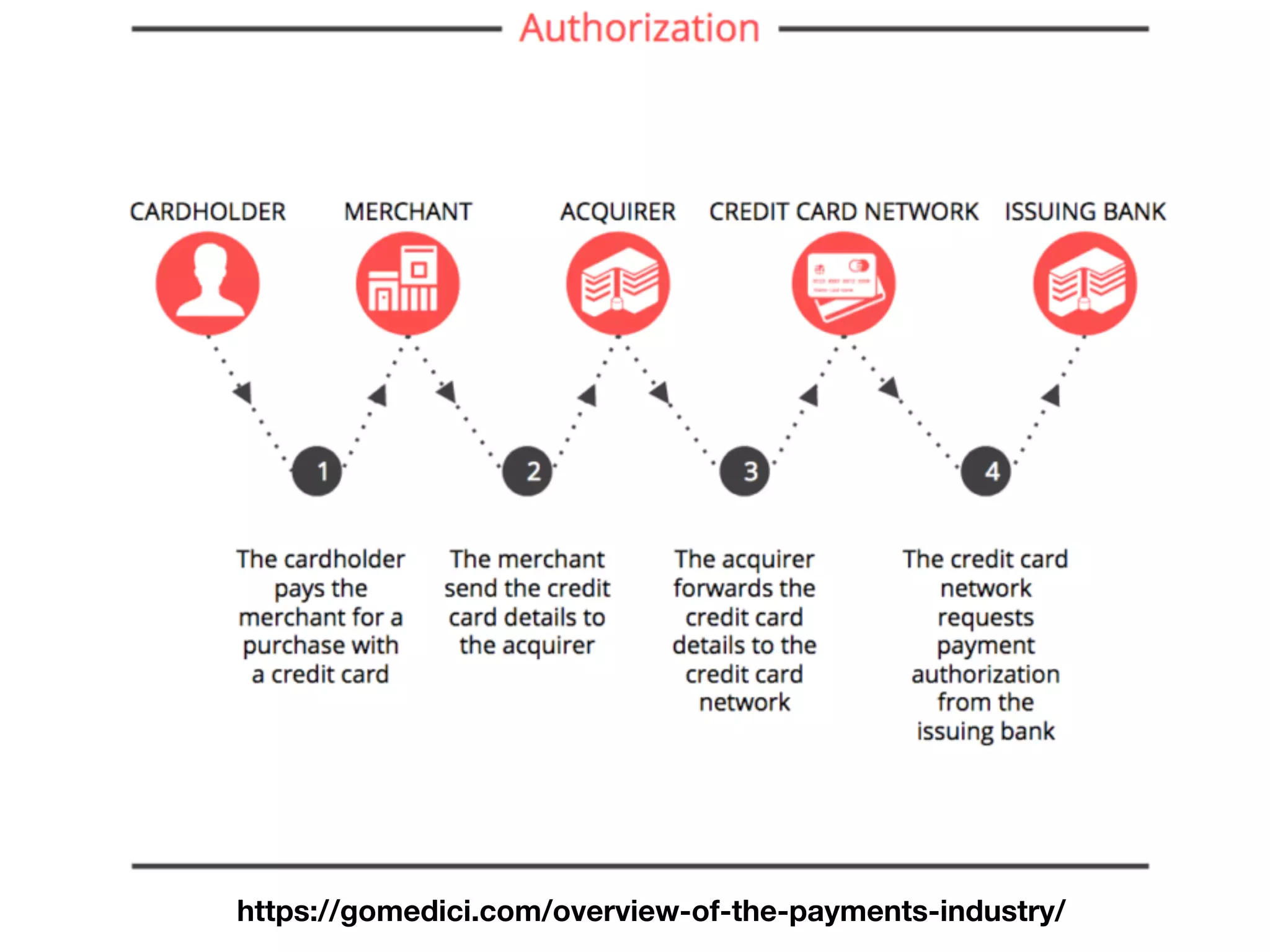
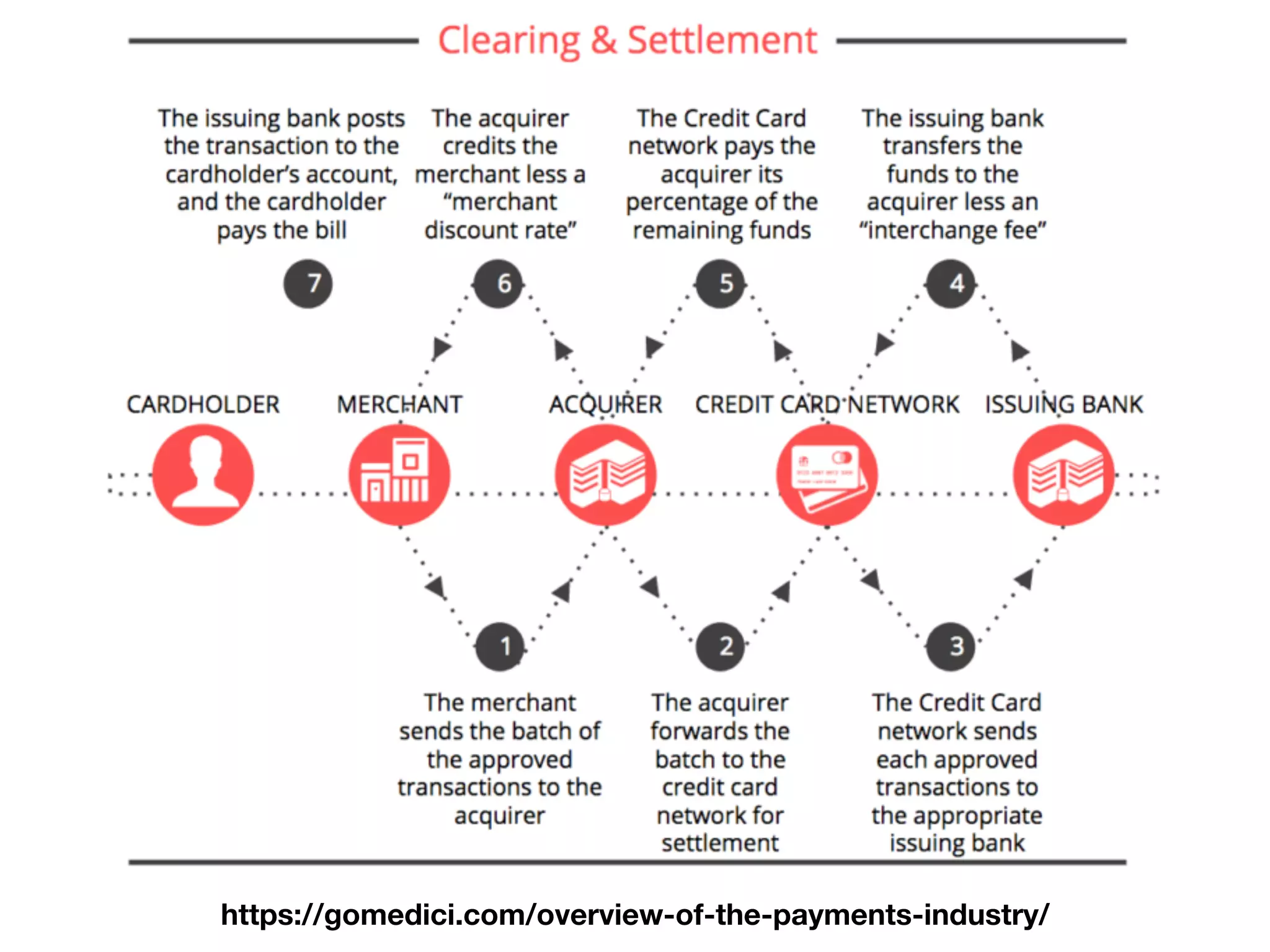
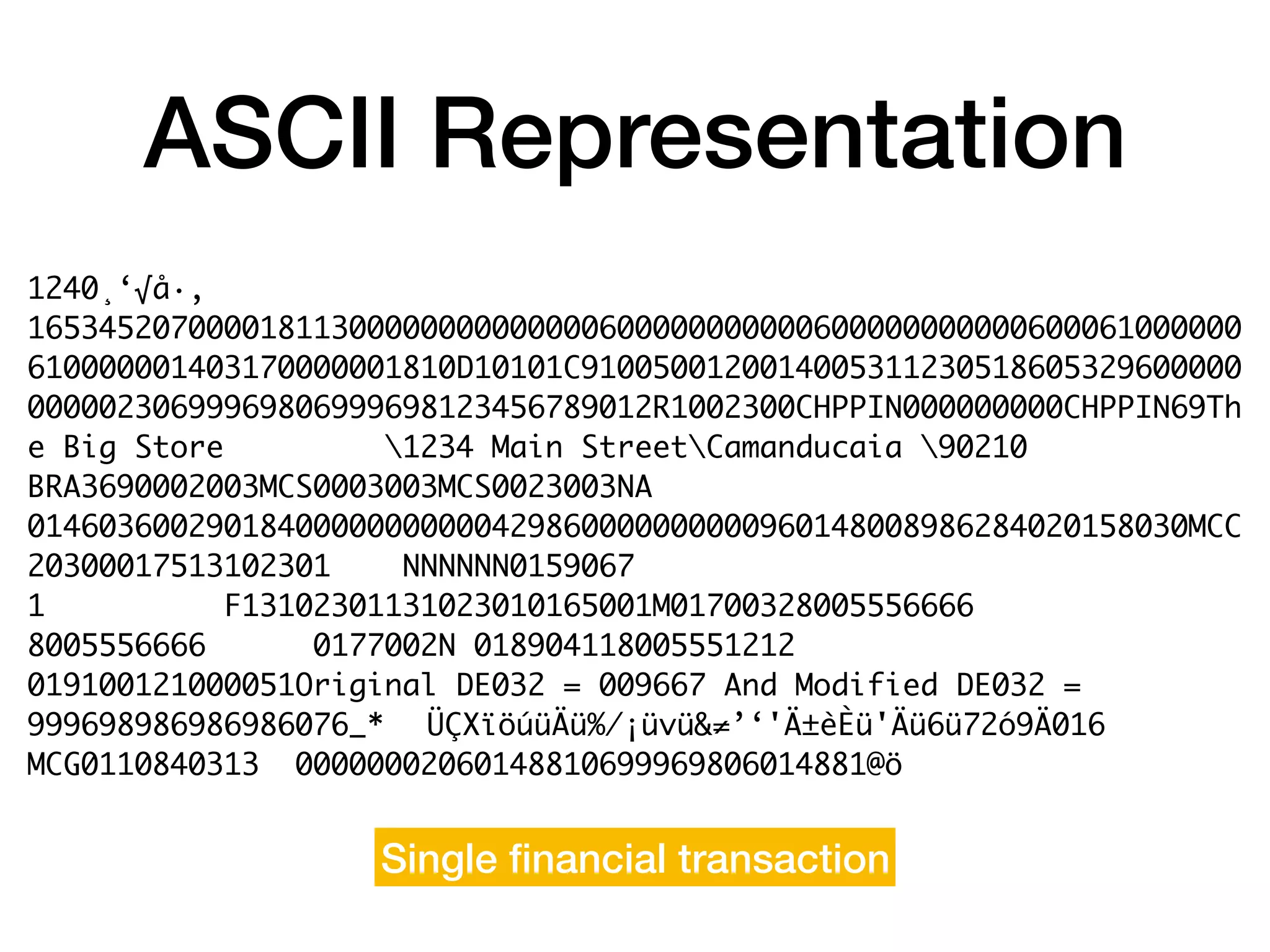
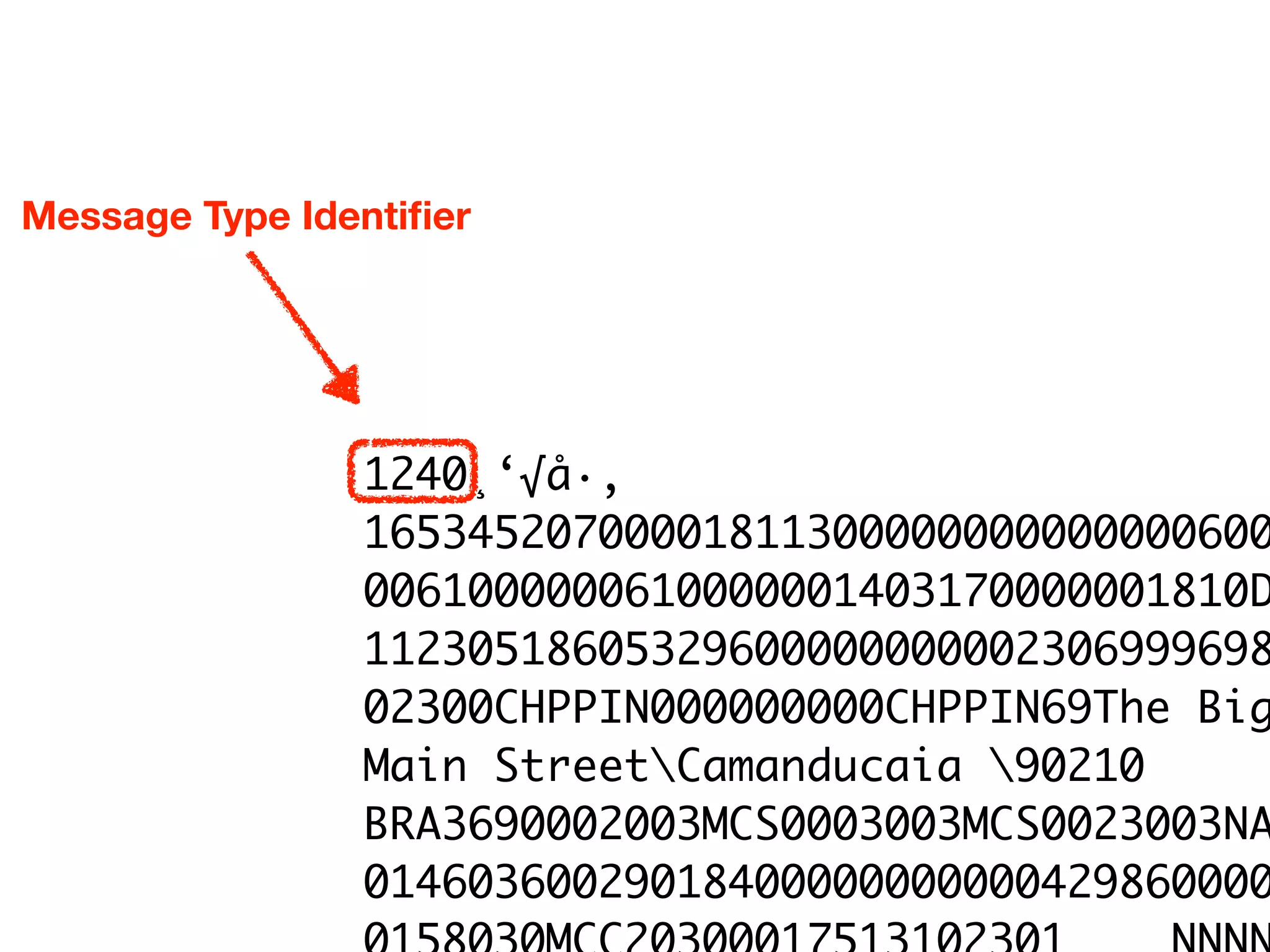
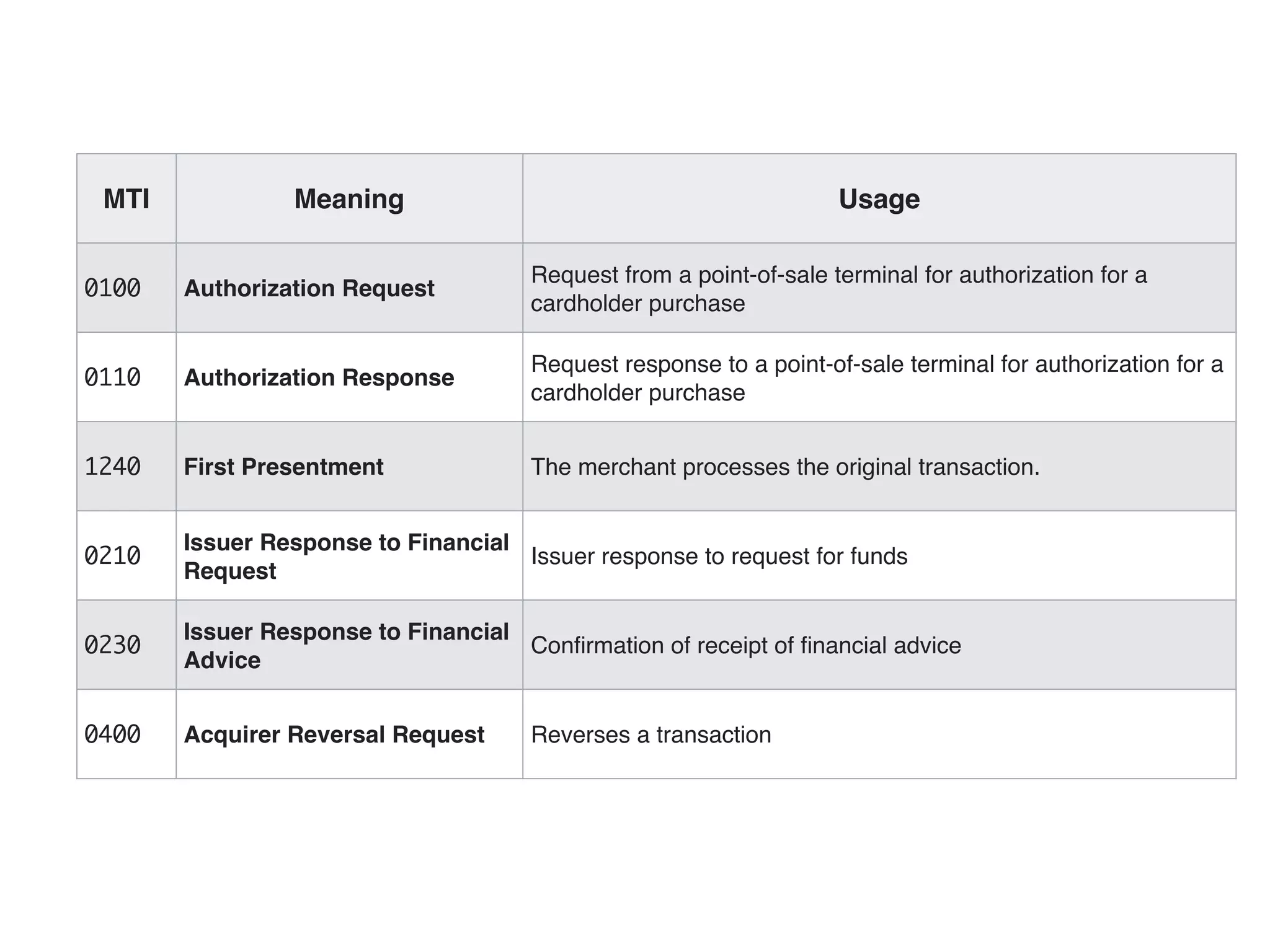
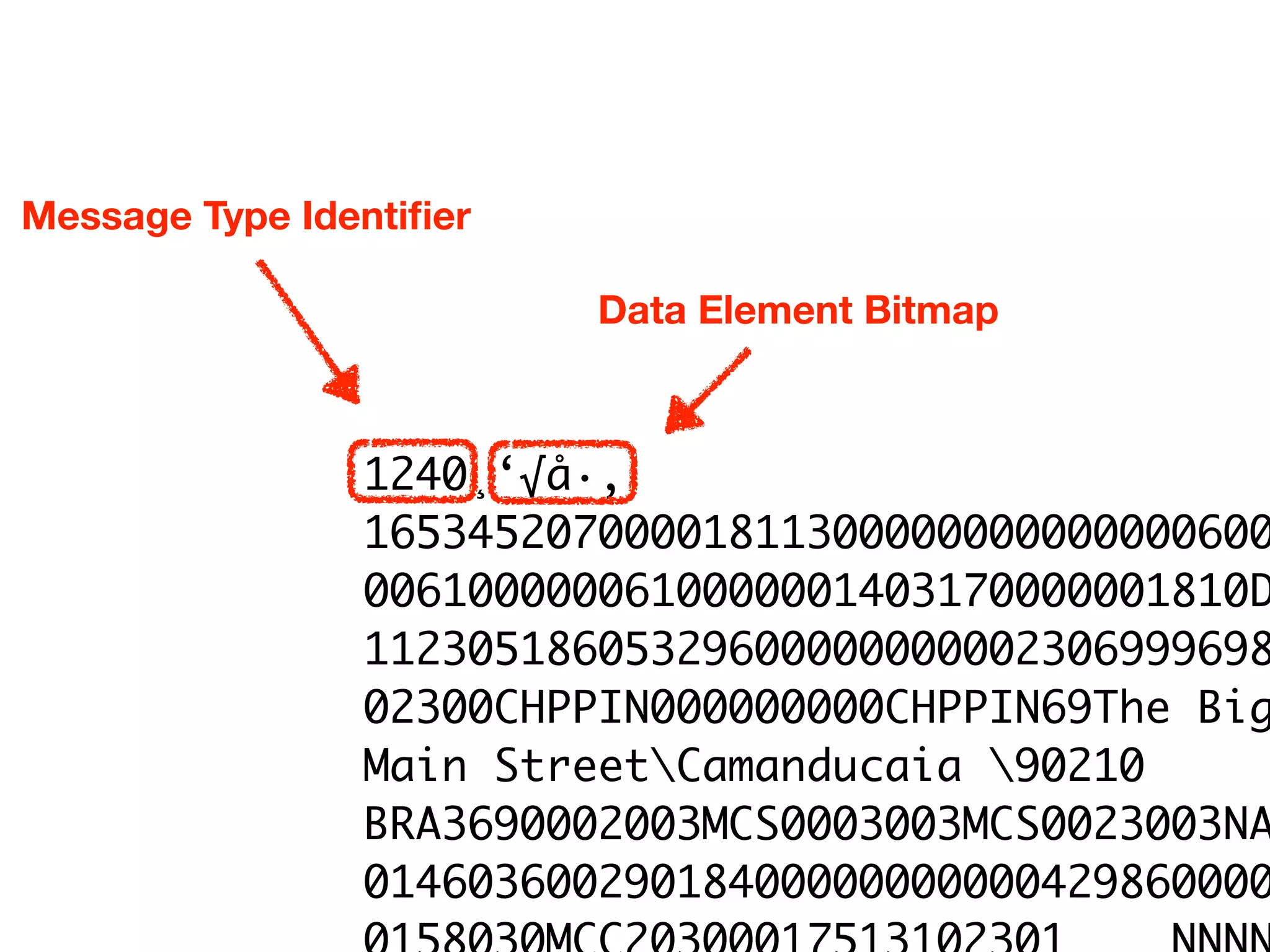
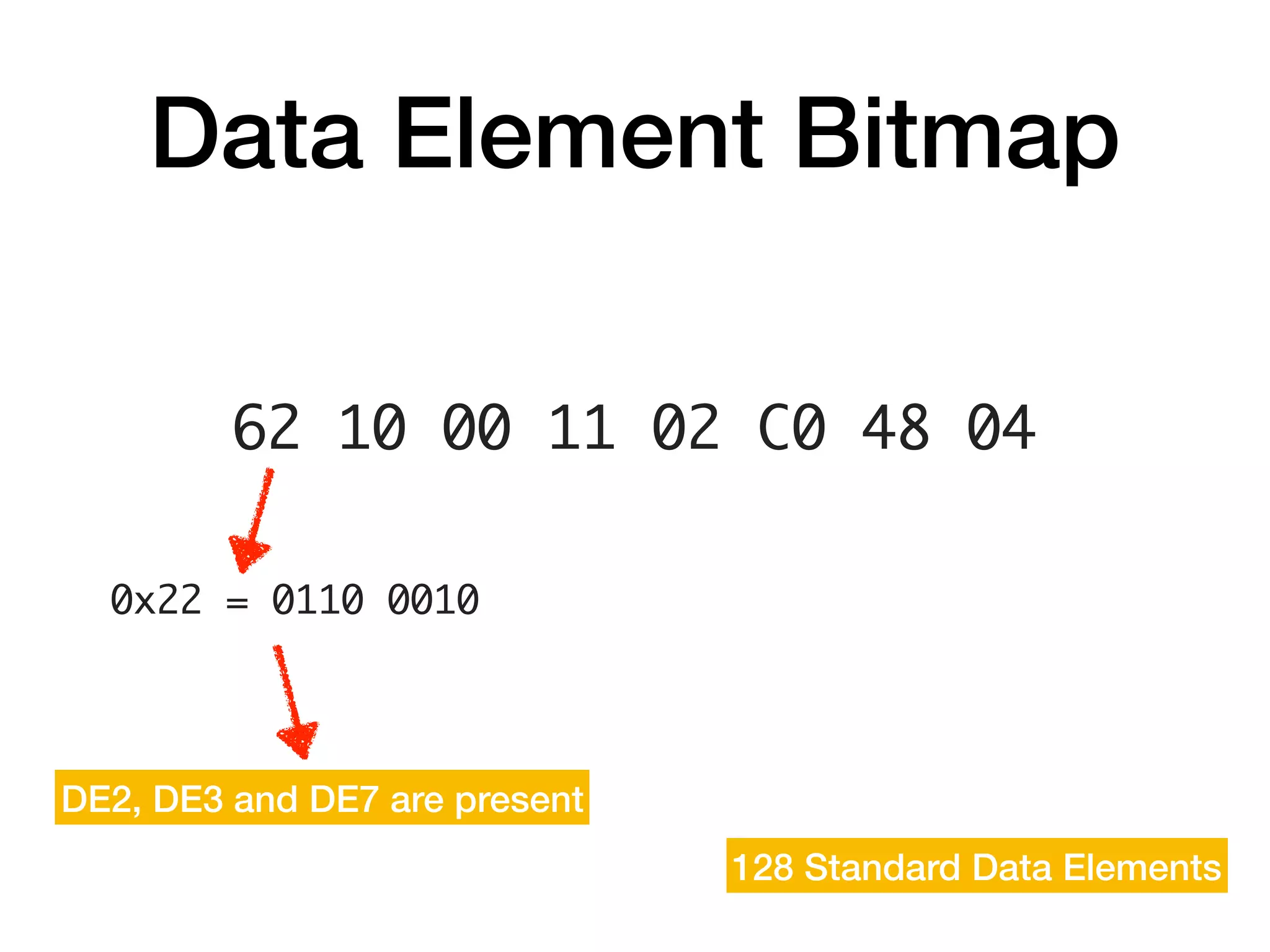
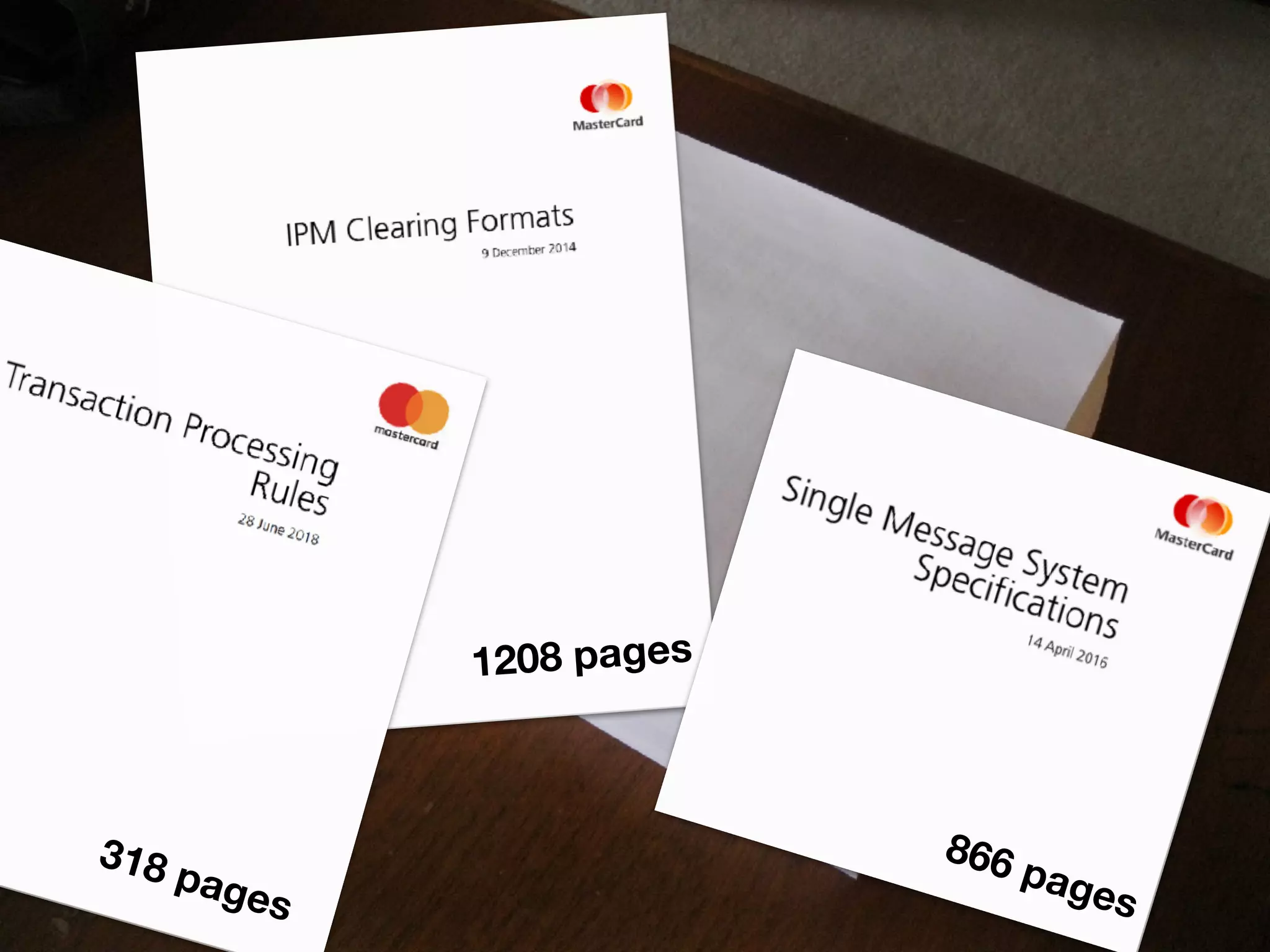
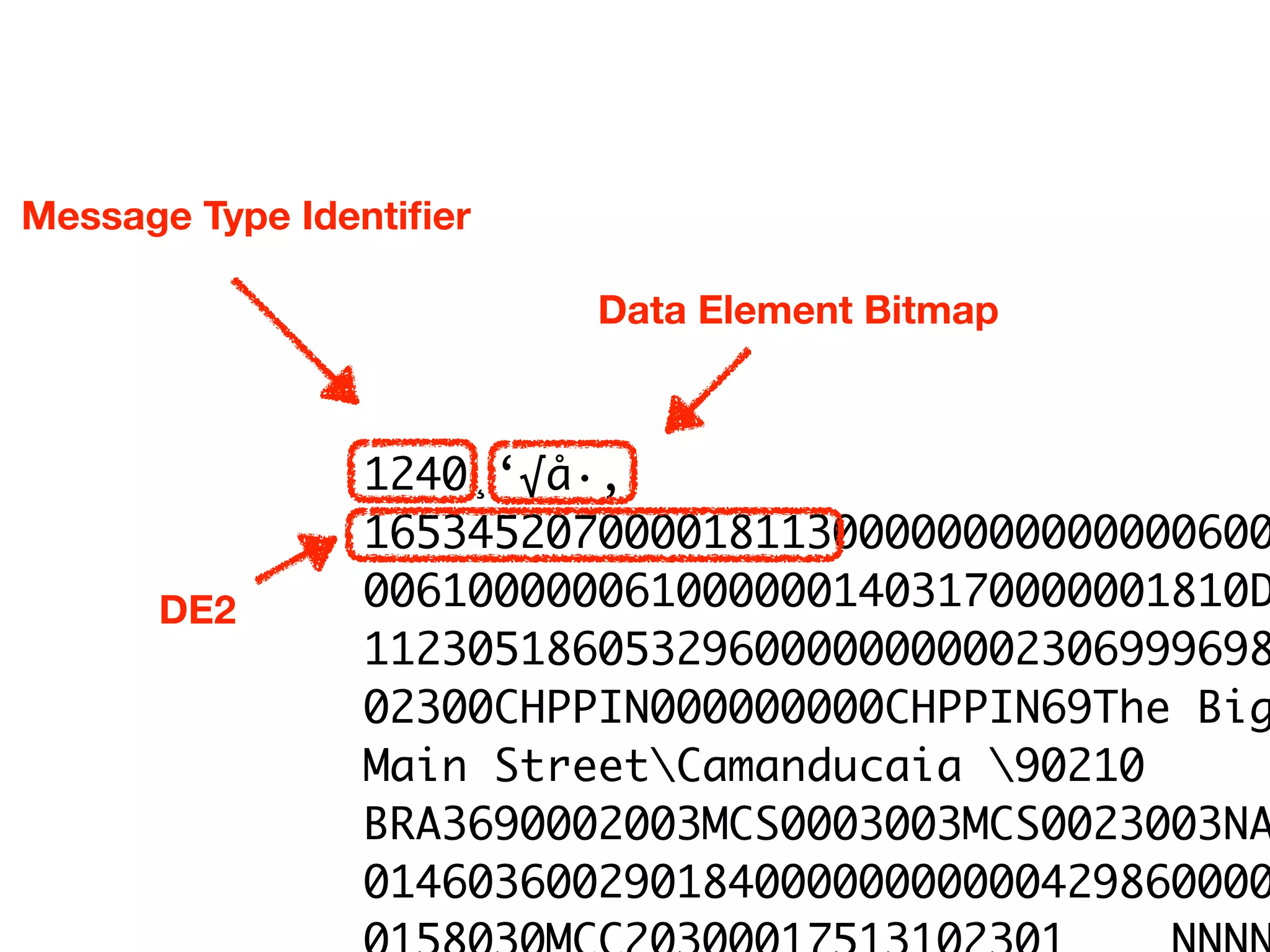
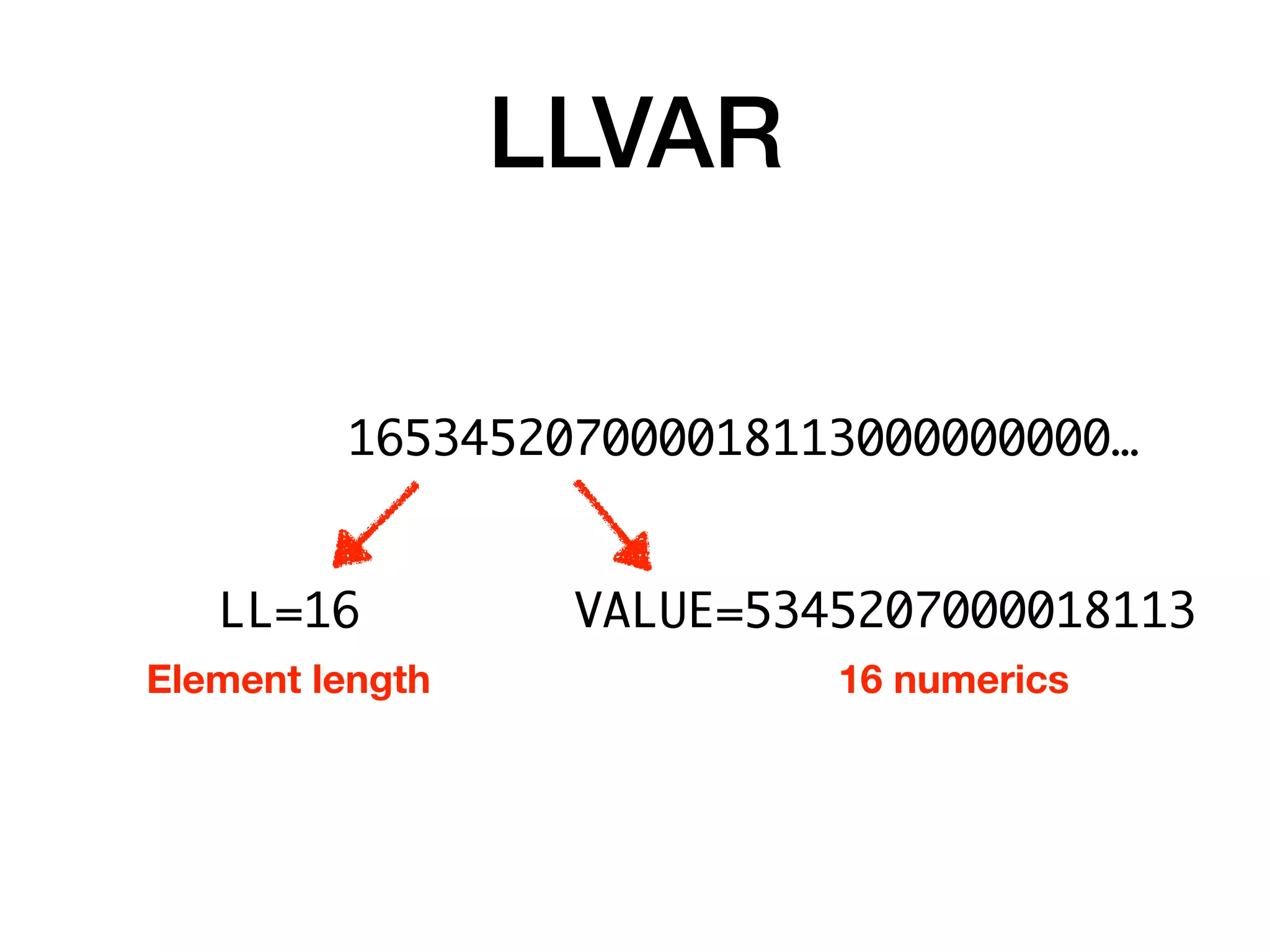
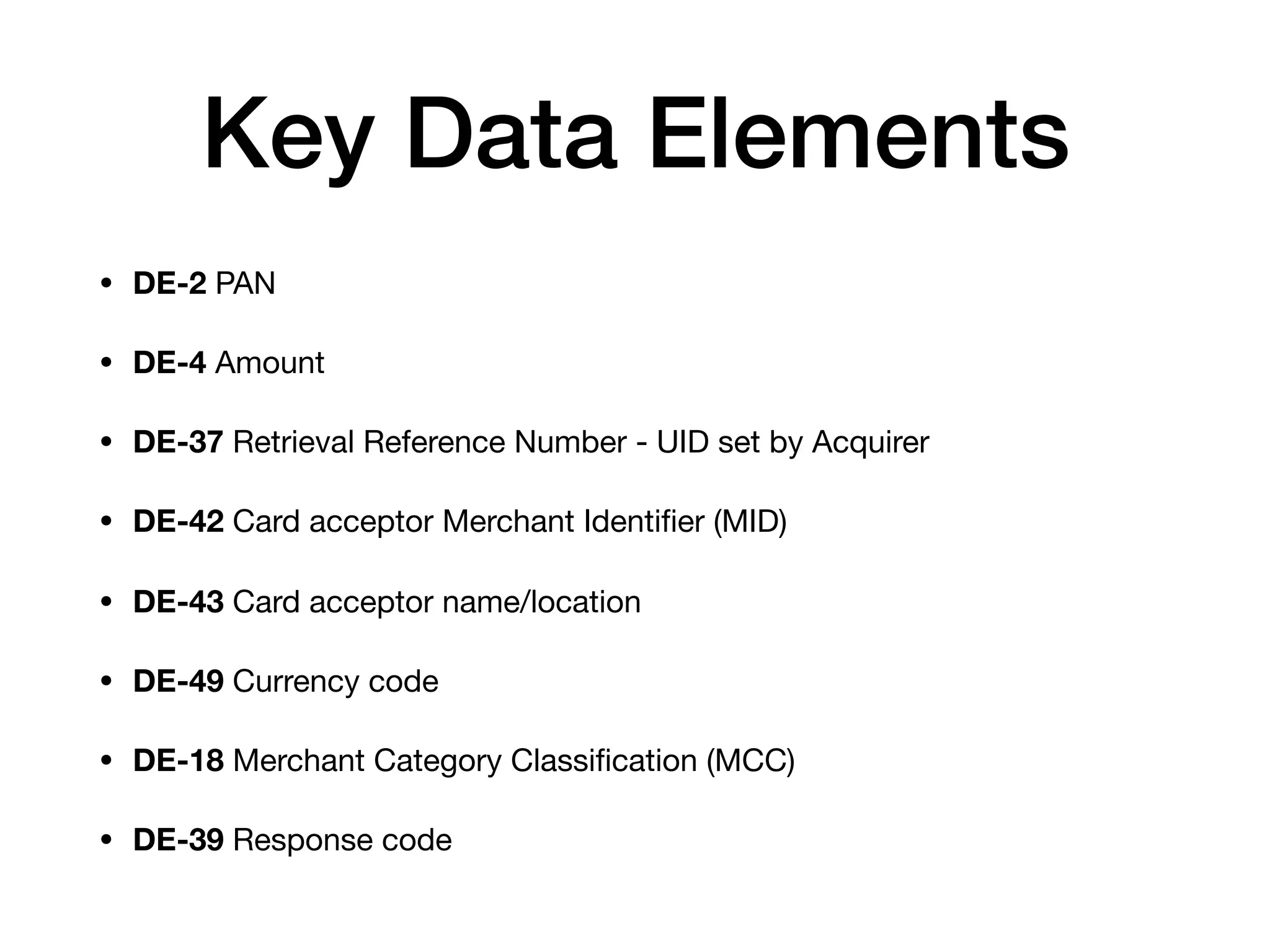
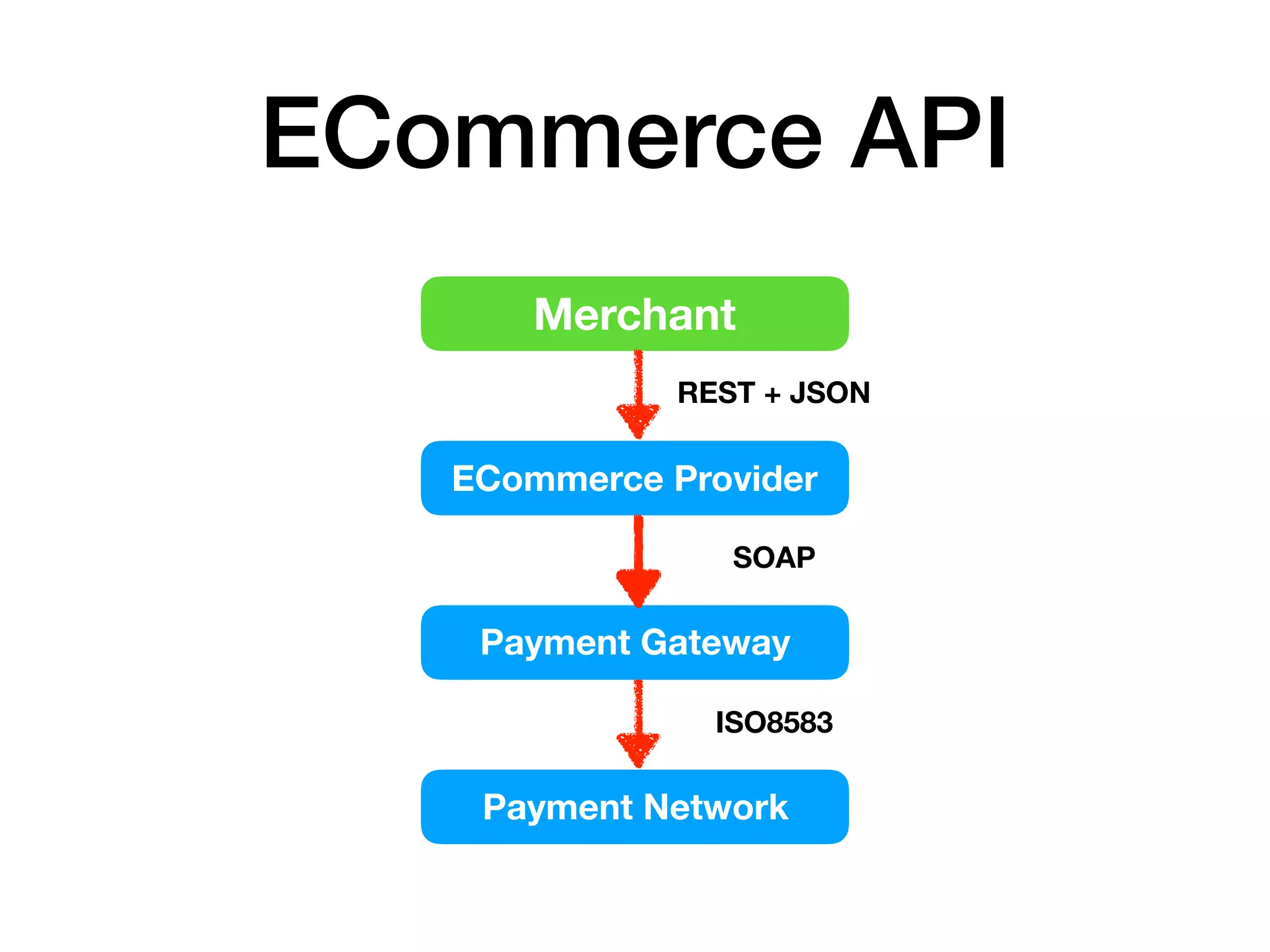
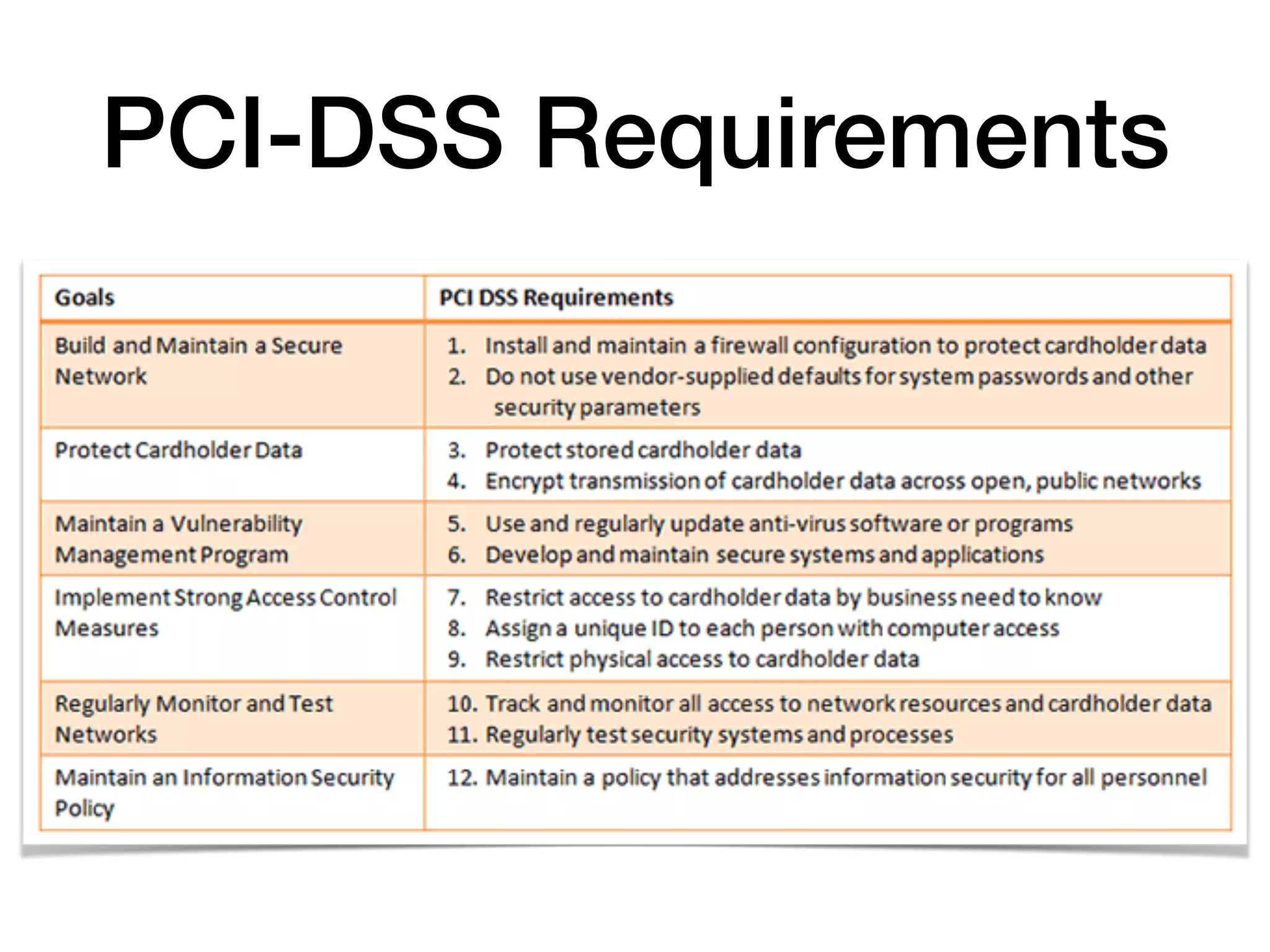
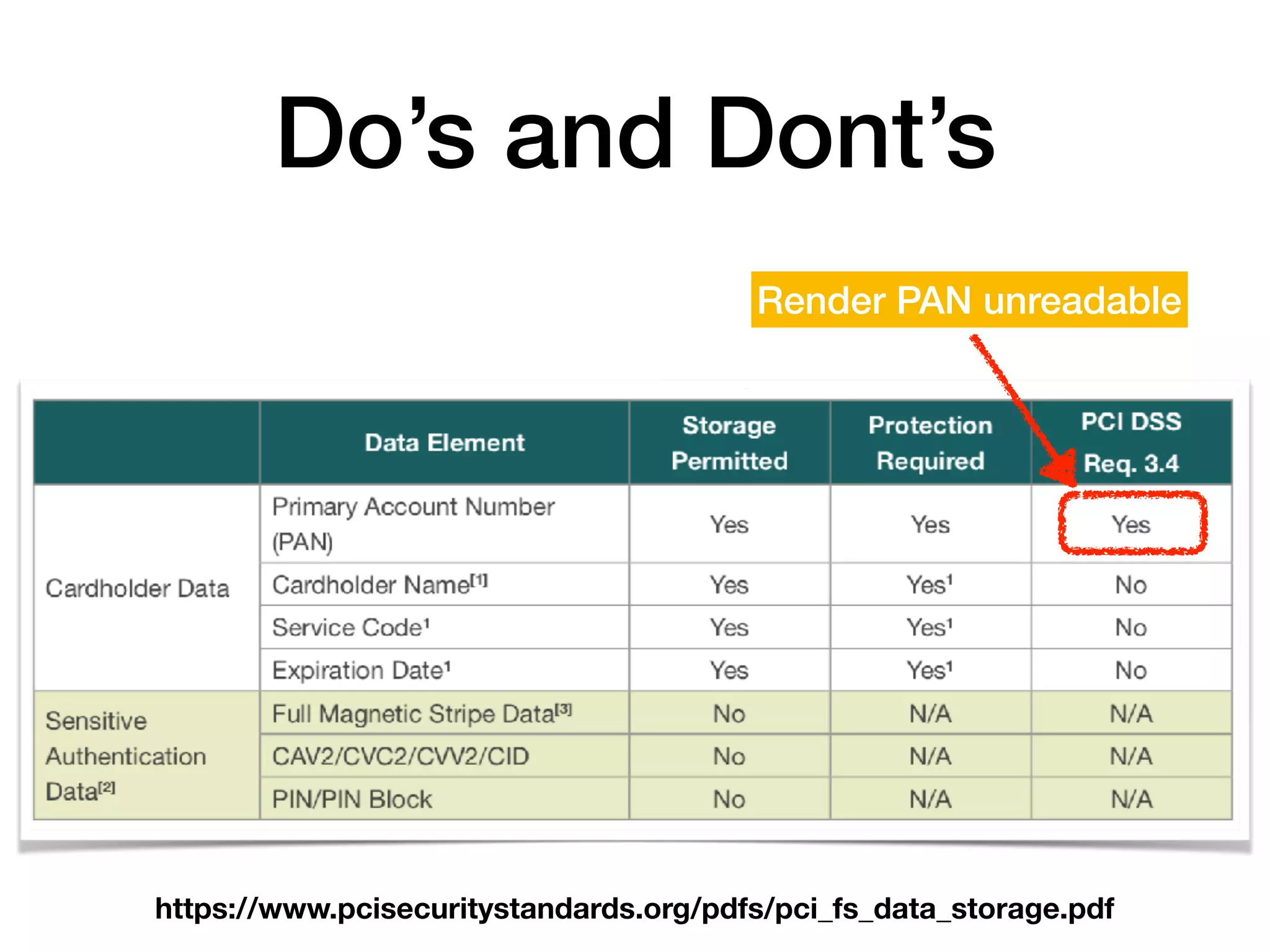
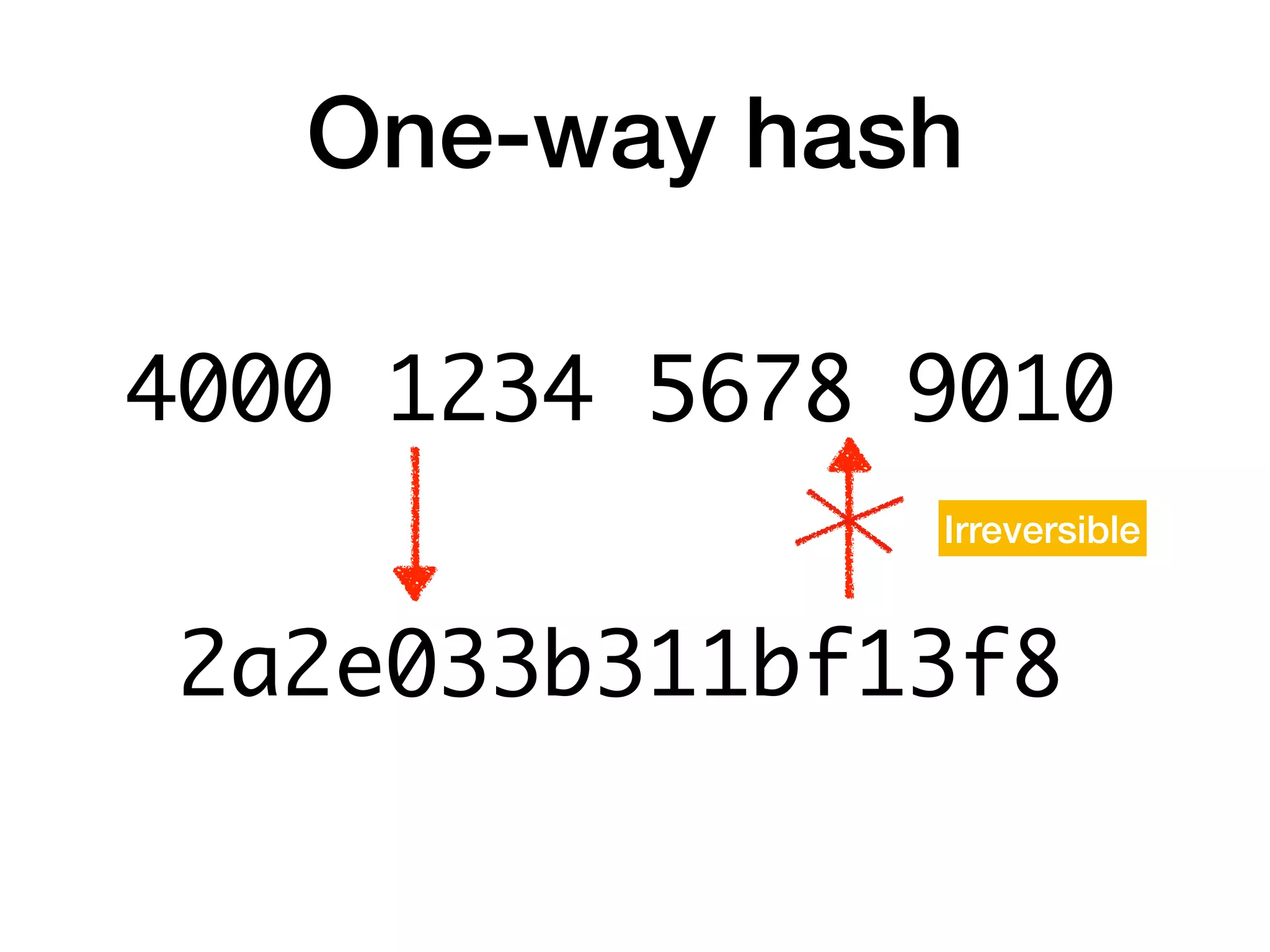
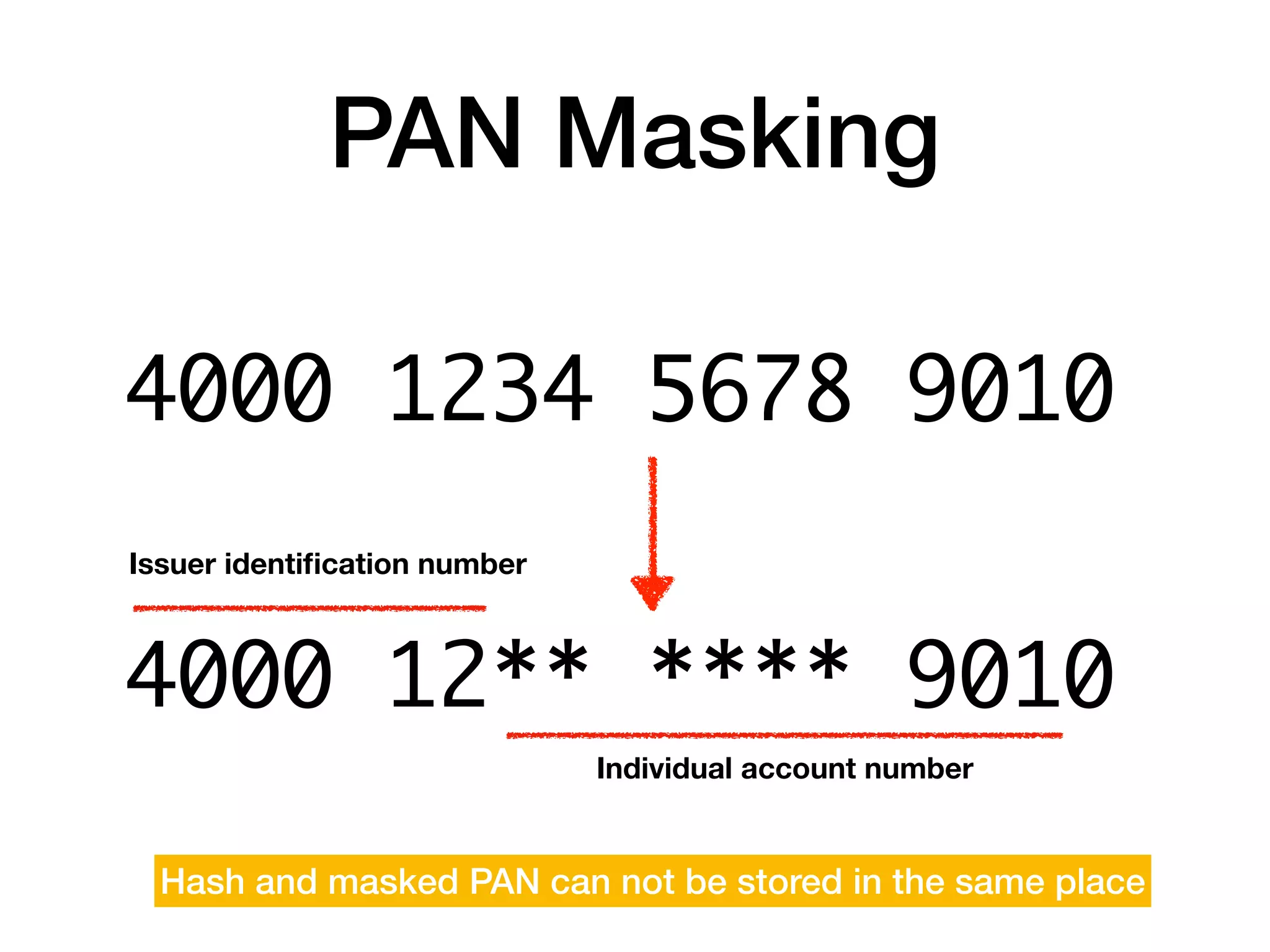
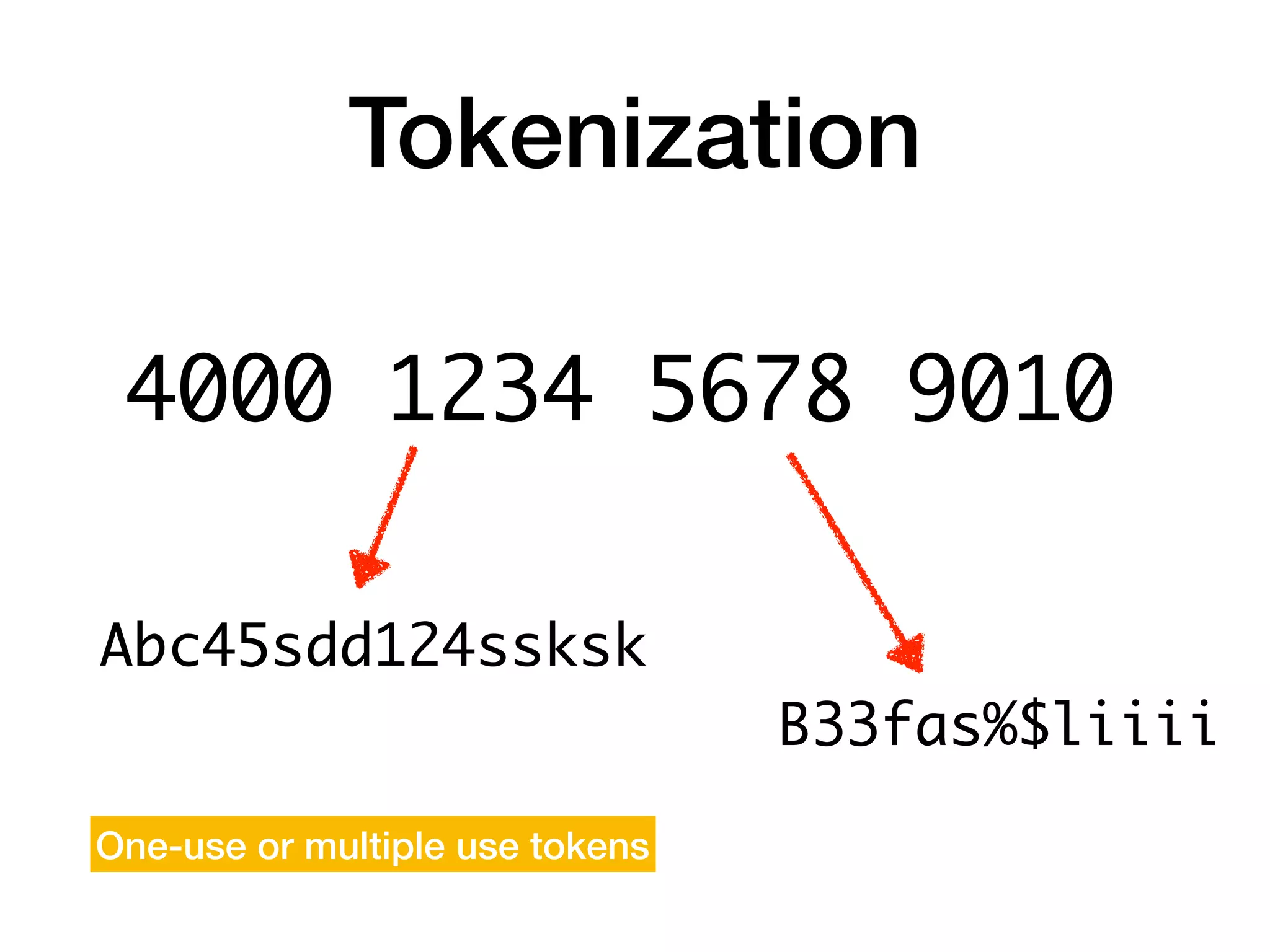
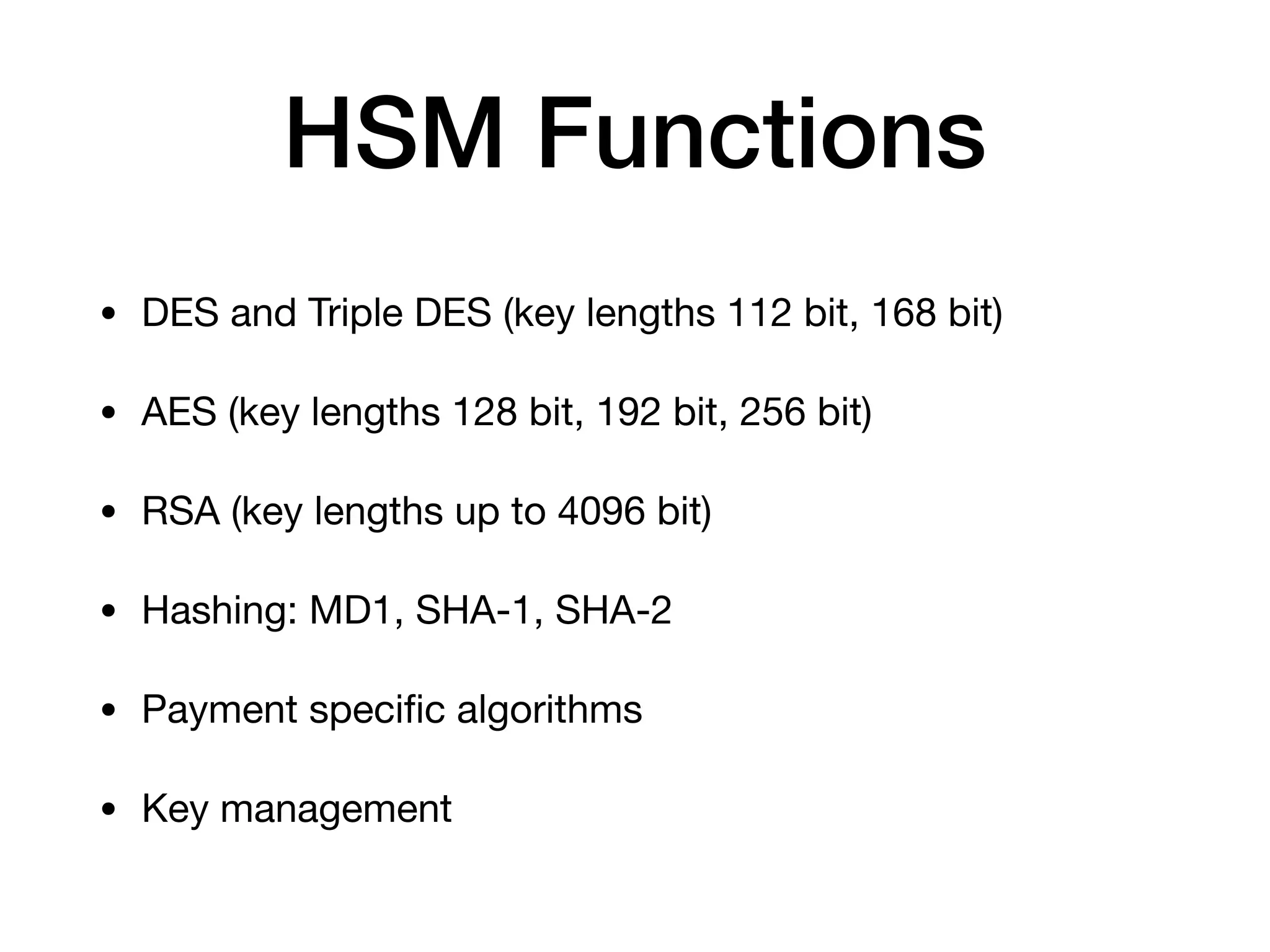
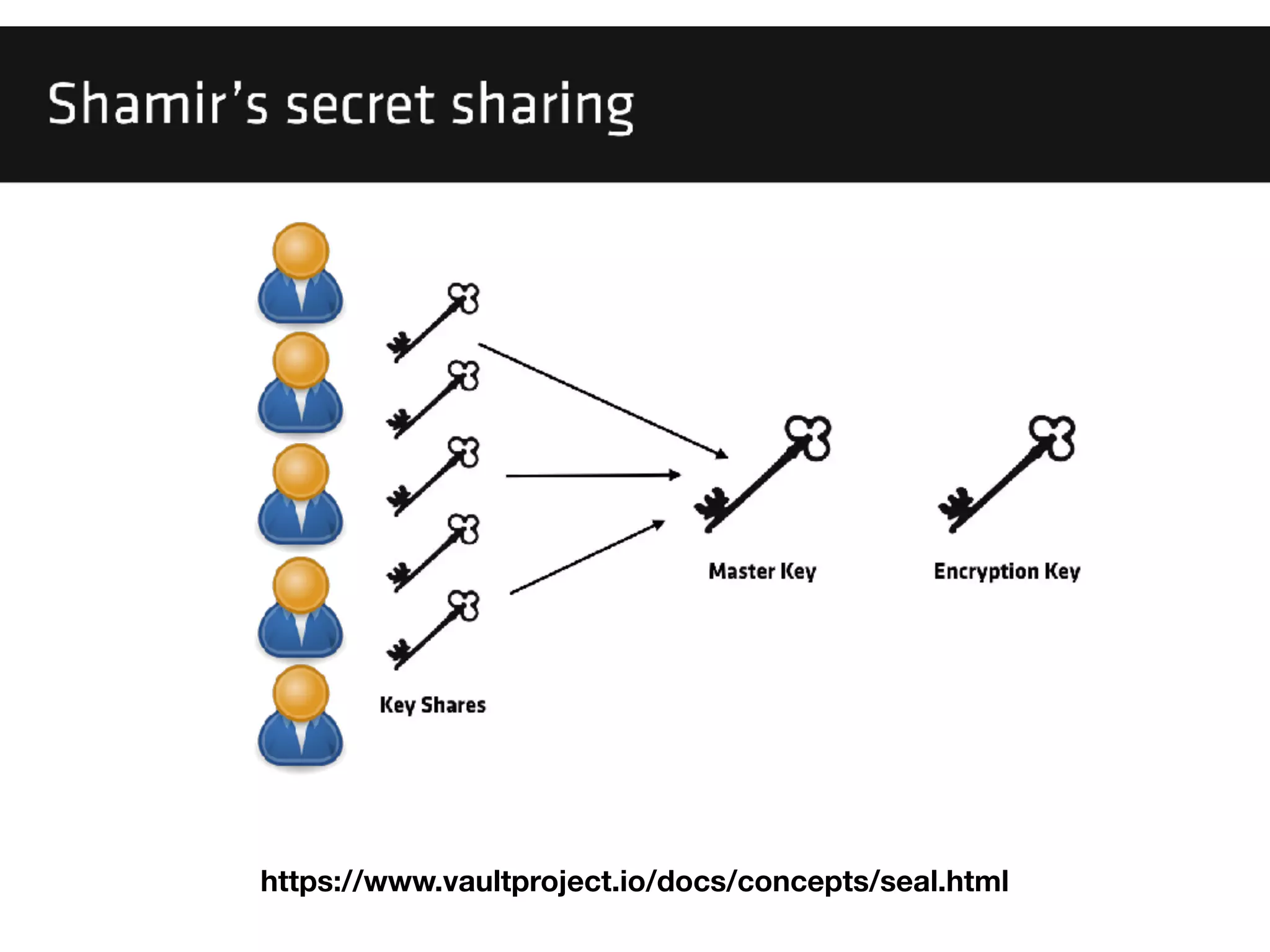
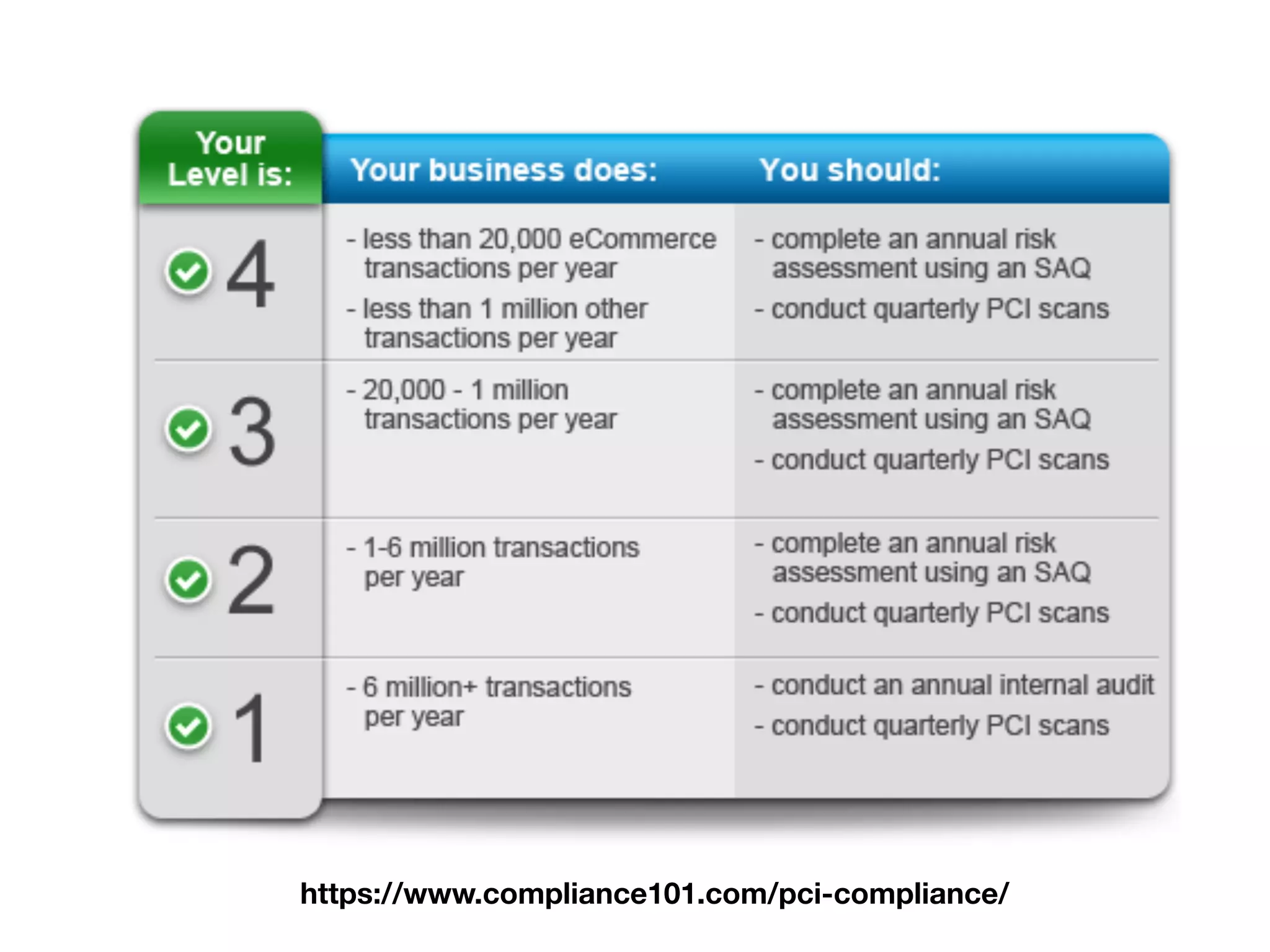
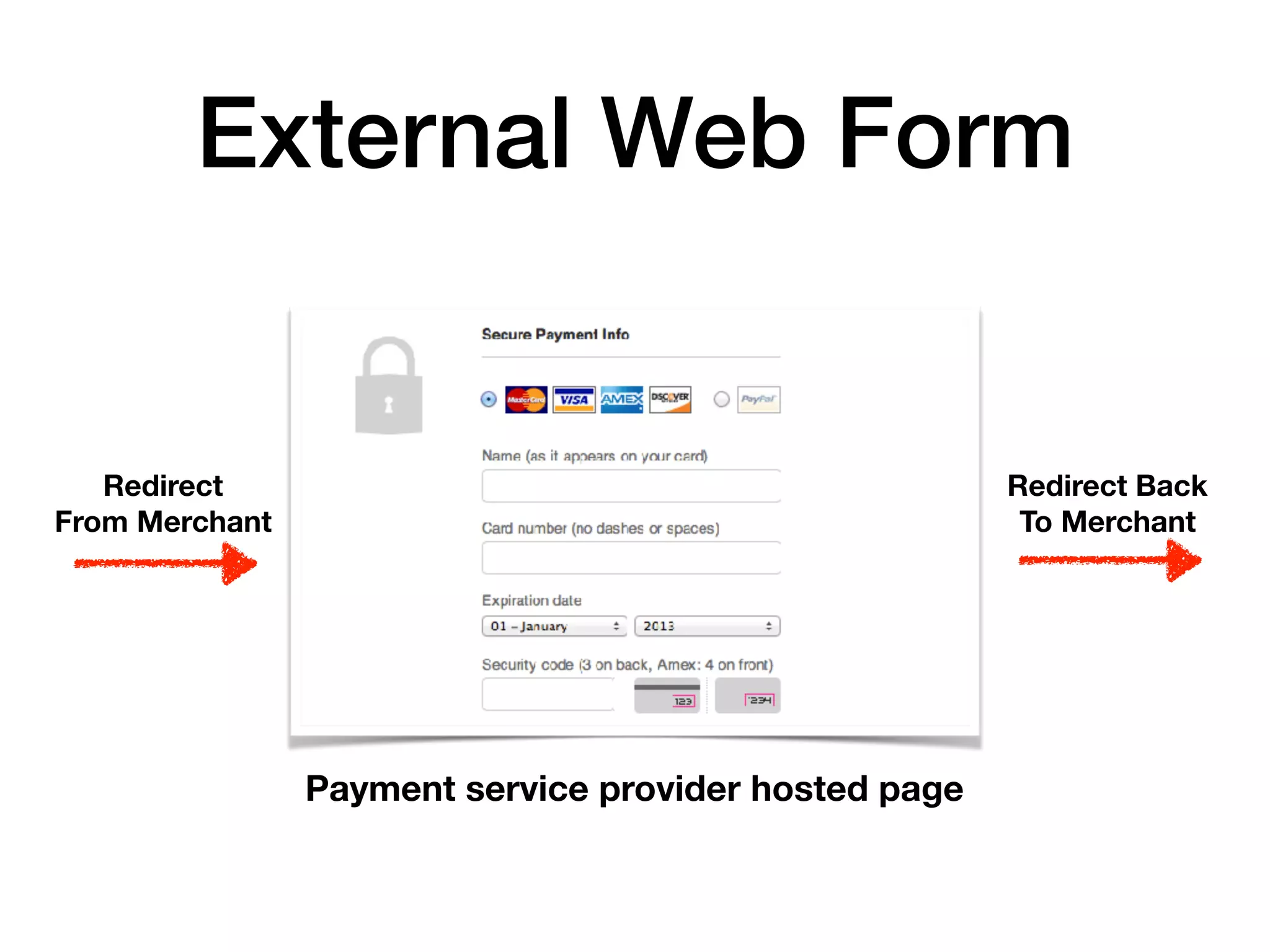
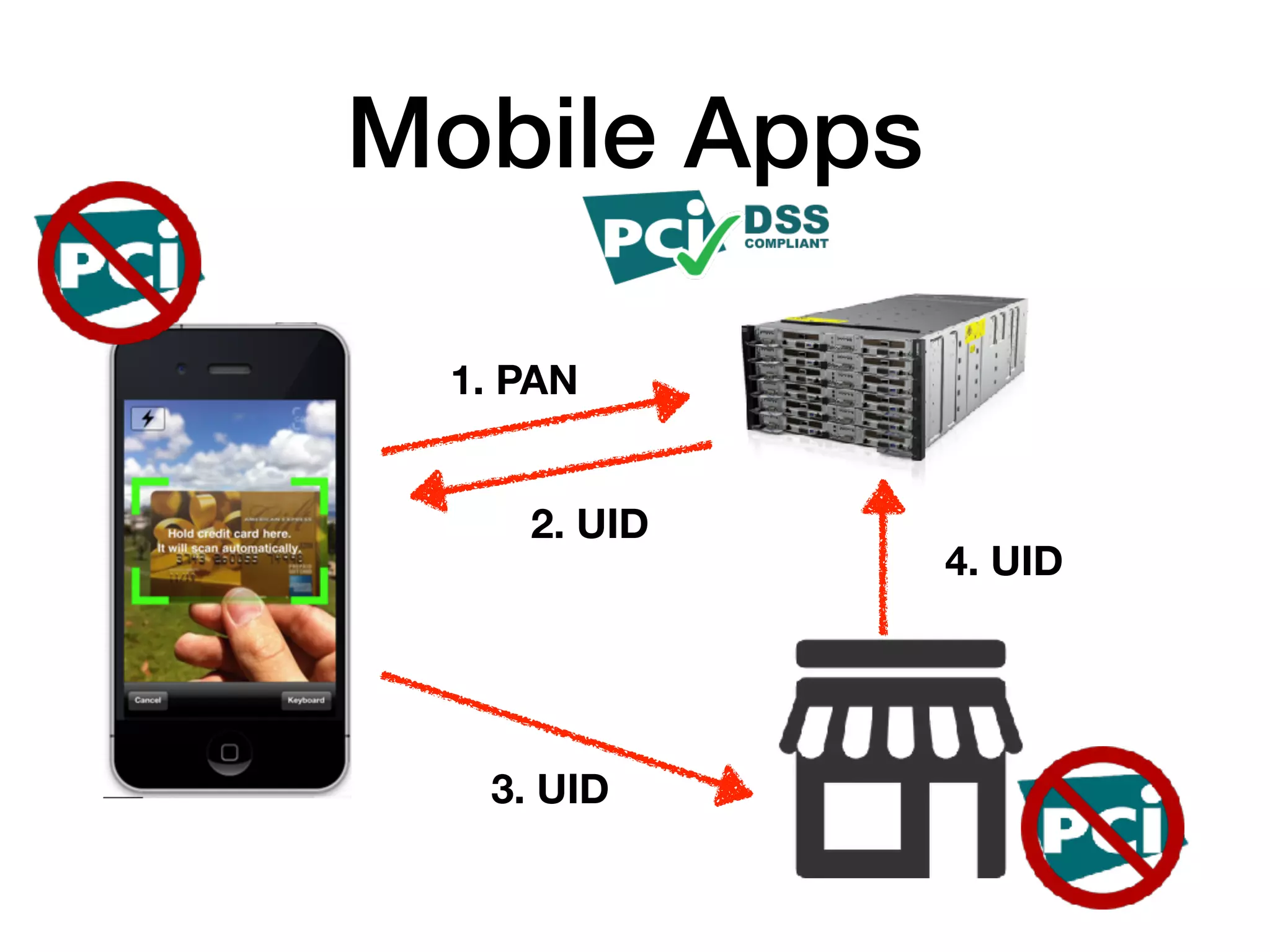
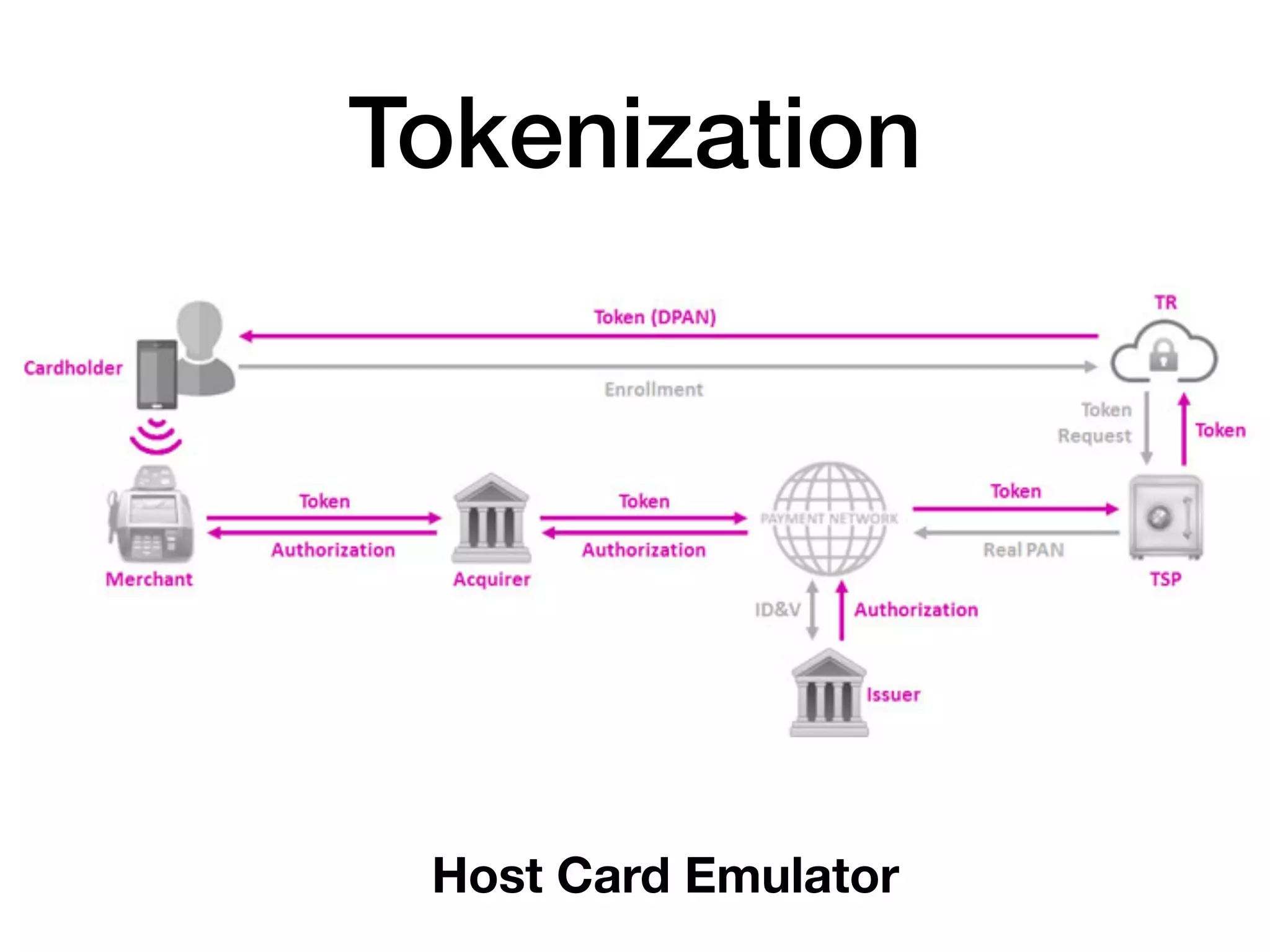
The document provides an overview of how payment cards work, detailing components such as card numbers, expiration dates, and payment networks, as well as the complex processes involved in processing transactions. It discusses authorization, transaction messages, and security standards like PCI-DSS, emphasizing the importance of protecting cardholder data. The document also highlights various technical details about transaction formats and encryption methods in the payments industry.