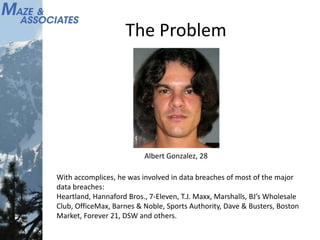
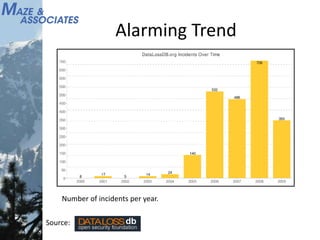
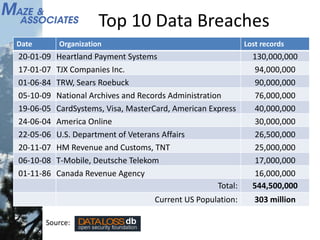
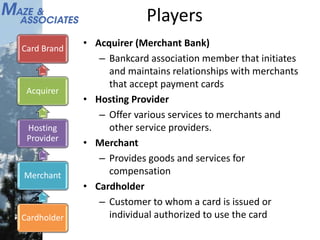
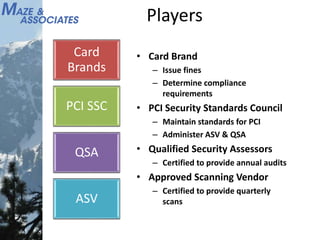
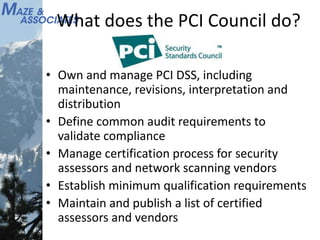
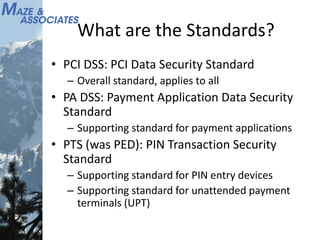
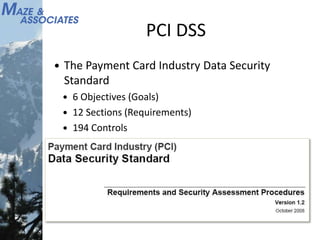
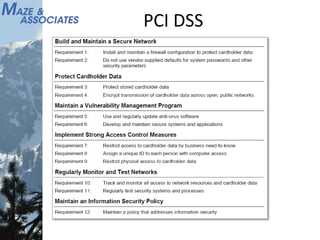
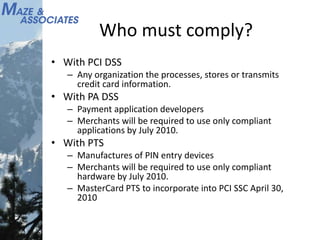
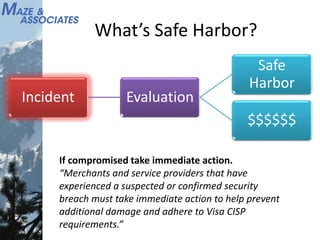
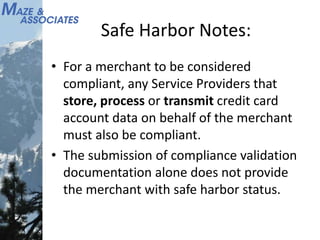
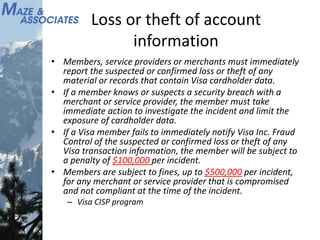
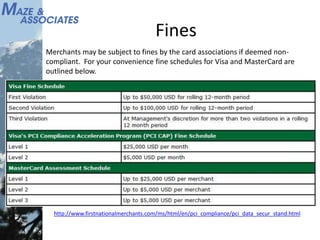
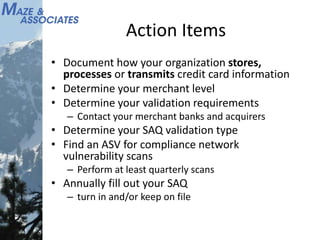
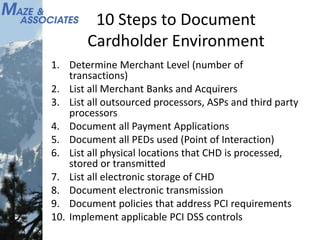
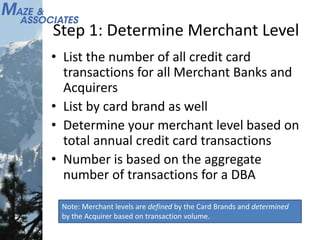
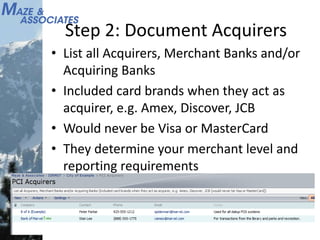
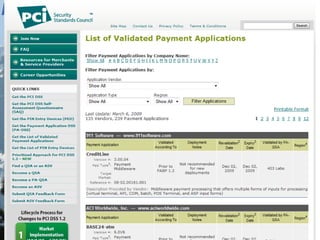
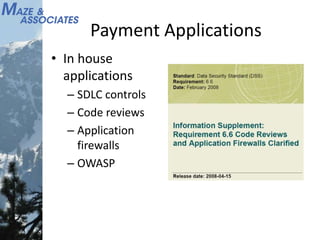
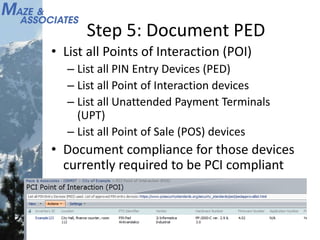
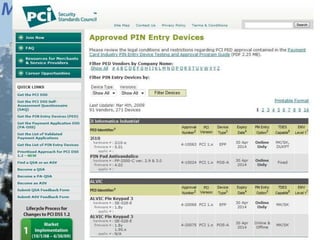
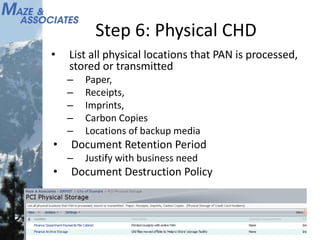
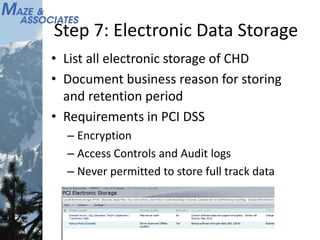
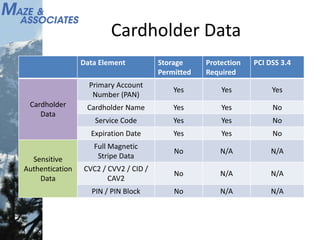
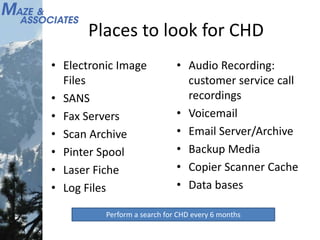
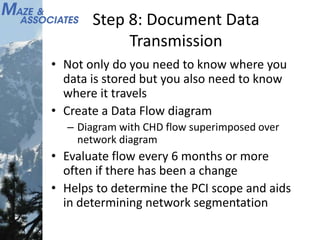
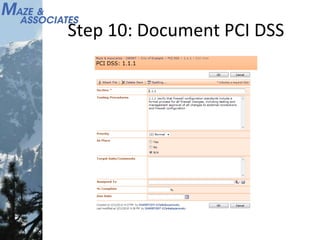
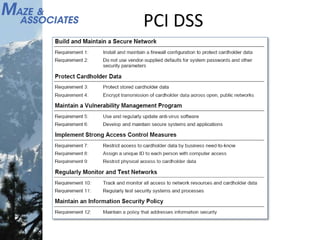
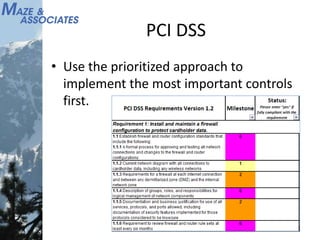
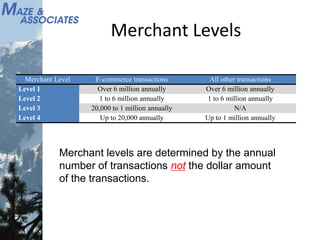
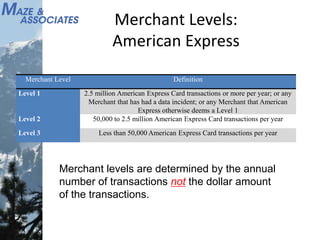
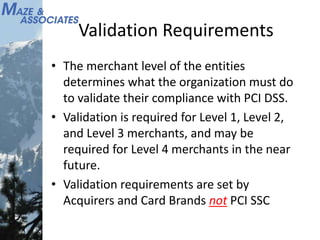
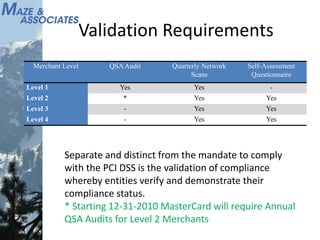
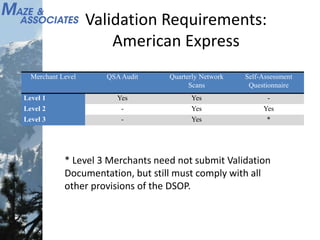
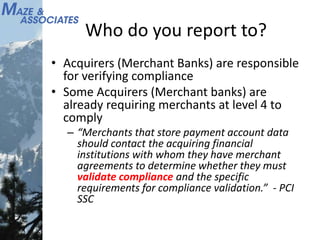
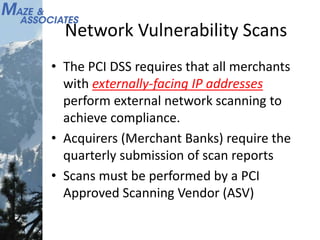
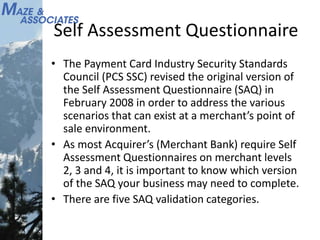
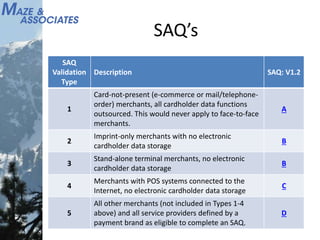
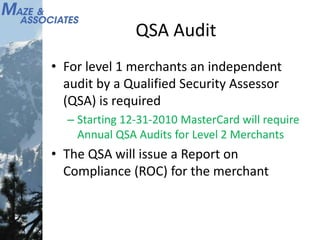
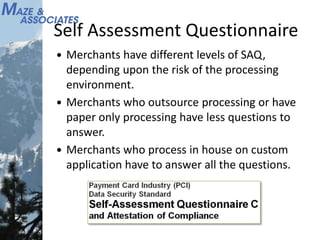
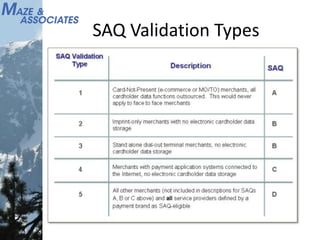
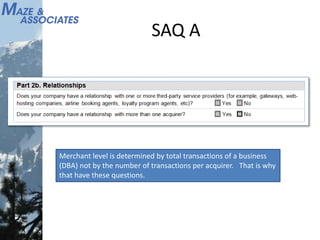
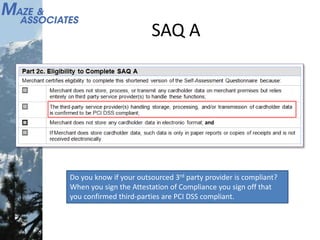
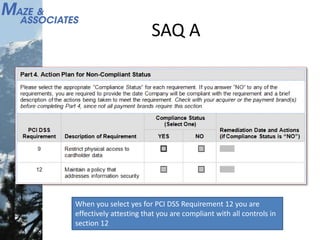
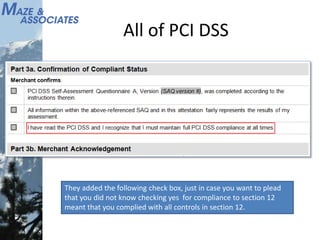
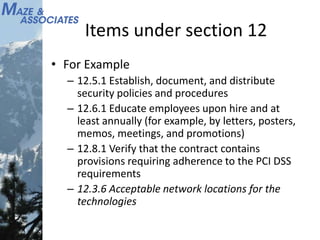
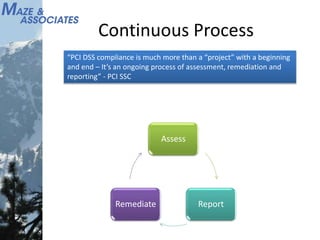
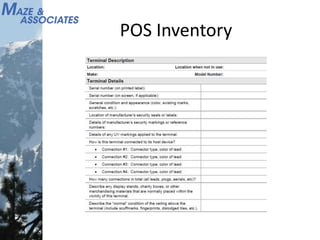
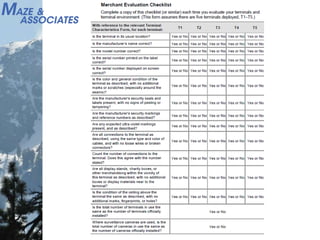
The document discusses the involvement of Albert Gonzalez in significant data breaches affecting numerous major companies, outlining the alarming trends in data incidents over the years. It details compliance requirements related to the Payment Card Industry Data Security Standards (PCI DSS), emphasizing the responsibilities of various players such as merchants, acquirers, and service providers in safeguarding cardholder data. Additionally, it provides a structured action plan for organizations to ensure compliance, including assessing merchant levels and documenting the storage and transmission of credit card information.