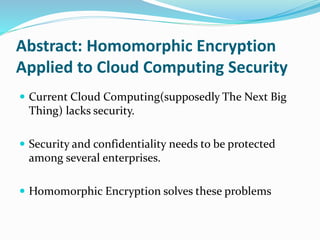
The document discusses homomorphic encryption, which allows computations to be performed on encrypted data and obtain an encrypted result without decrypting the inputs. It provides examples of partially homomorphic encryption schemes like RSA that allow only addition or multiplication, and fully homomorphic encryption introduced by Craig Gentry in 2009 that allows any computation. The document also discusses applications of homomorphic encryption like secure cloud computing and processing of sensitive encrypted medical records. It summarizes Craig Gentry's homomorphic encryption scheme and the HELib software library implementation.
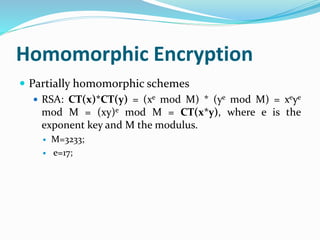
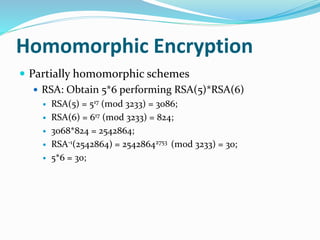
![Introduction
Homomorphic Encryption[1] is a form
of encryption which allows specific types of
computations to be carried out on ciphertext and
obtain an encrypted result which decrypted, matches
the result of operations performed on the plaintext.
For instance, one person could add two encrypted
numbers and then another person could decrypt the
result, without either of them being able to find the
value of the individual numbers.](https://image.slidesharecdn.com/henc-150320112736-conversion-gate01/85/Homomorphic-Encryption-2-320.jpg)





![Homomorphic Encryption
Fully homomorphic Encryption[2]:
A cryptosystem that supports arbitrary computation on ciphertexts is known as
fully homomorphic encryption (FHE) and is far more powerful. Such a scheme
enables the construction of programs for any desirable functionality, which can
be run on encrypted inputs to produce an encryption of the result.
Fully homomorphic Encryption schemes:
Craig Gentry scheme
Zaryab Khan scheme](https://image.slidesharecdn.com/henc-150320112736-conversion-gate01/85/Homomorphic-Encryption-13-320.jpg)

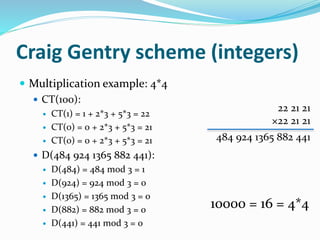
![Craig Gentry scheme (integers)
Craig Gentry scheme’s homomorphic assumptions
Addition: c1 + c2 = b1+ b2 + 2(x1+x2) + (k1+k2)p = b1 xor
b2 + 2x + kp
Decryption works if (b1+2x1) + (b2+2x2) is in [-N,N]
Multiplication: c1*c2 = b1*b2 + 2(b1x2 + b2x1 + 2x1x2) + kp
= b1*b2 + 2x + kp
Decryption works if (b1+2x1) * (b2+2x2) is in [-N,N]](https://image.slidesharecdn.com/henc-150320112736-conversion-gate01/85/Homomorphic-Encryption-15-320.jpg)

![HELib
Helib[4] is a software library that implements
homomorphic encryption (HE), specifically the
Brakerski-Gentry-Vaikuntanathan (BGV) scheme,
focusing on effective use of the Smart ciphertext
packing techniques and the Gentry-Halevi-Smart
optimizations.](https://image.slidesharecdn.com/henc-150320112736-conversion-gate01/85/Homomorphic-Encryption-18-320.jpg)


![Problems Solved
Wireless Sensor/Mesh Network.
Problems related to personal records like medical
records:
○ Analyze disease / treatment without disclosing them
○ Search for DNA markers without revealing DNA.
HELib[4] from IBM.
https://github.com/shaih/HElib/tree/master/src](https://image.slidesharecdn.com/henc-150320112736-conversion-gate01/85/Homomorphic-Encryption-21-320.jpg)
![References
[1]. Hacker Lexicon: What Is Homomorphic Encryption?
www.wired.com/2014/11/hacker-lexicon-homomorphic-encryption/
[2]. A Fully Homomorphic Encryption Scheme
www.crypto.stanford.edu/craig/craig-thesis.pdf
[3]. Homomorphic Encryption - MIT Technology Review
www2.technologyreview.com/article/423683/homomorphic-encryption/
[4]. IBM takes a big new step in cryptography practical homomorphic
encryption
nakedsecurity.sophos.com/2013/05/05/ibm-takes-big-new-step-in-cryptography/](https://image.slidesharecdn.com/henc-150320112736-conversion-gate01/85/Homomorphic-Encryption-24-320.jpg)

