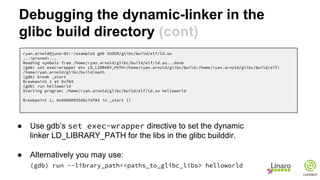
The document presents advanced toolchain usage techniques by Linaro toolchain experts, focusing on debugging and the dynamic linker. It includes detailed discussions on debugging scenarios, such as stepping into the dynamic linker's resolver and using GDB for debugging prior to the application's main function. Various tips and sample code are provided to showcase how to effectively utilize these toolchain techniques for debugging applications.


![Debugging and the Dynamic Linker
● The ELF INTERP program header for an application has the path to the
dynamic-linker embedded in header.
$ readelf -l main
Elf file type is EXEC (Executable file)
Entry point 0x400430
There are 7 program headers, starting at offset 64
Program Headers:
Type Offset VirtAddr PhysAddr
FileSiz MemSiz Flags Align
PHDR 0x0000000000000040 0x0000000000400040 0x0000000000400040
0x0000000000000188 0x0000000000000188 R E 8
INTERP 0x00000000000001c8 0x00000000004001c8 0x00000000004001c8
0x000000000000001b 0x000000000000001b R 1
[Requesting program interpreter: /lib/ld-linux-aarch64.so.1]](https://image.slidesharecdn.com/hkg15-207-advancedtoolchainusagepart3-150208181030-conversion-gate01/85/HKG15-207-Advanced-Toolchain-Usage-Part-3-5-320.jpg)
![Stepping into the dynamic linker’s
resolver (cont)
#include <stdio.h>
int main(void)
{
puts("hello world.");
puts(“hello again.”);
return 0;
}
ryan.arnold@juno-02:~/example$ gdb helloworld
(gdb) break main
Breakpoint 1 at 0x4005a0
(gdb) run
Starting program: /home/ryan.arnold/example/helloworld
Breakpoint 1, 0x00000000004005a0 in main ()
(gdb) disass
Dump of assembler code for function main:
0x0000000000400590 <+0>: stp x29, x30, [sp,#-16]!
0x0000000000400594 <+4>: mov x29, sp
0x0000000000400598 <+8>: adrp x0, 0x400000
0x000000000040059c <+12>: add x0, x0, #0x650
=> 0x00000000004005a0 <+16>: bl 0x400420 <puts@plt>
0x00000000004005a4 <+20>: adrp x0, 0x400000
0x00000000004005a8 <+24>: add x0, x0, #0x660
0x00000000004005ac <+28>: bl 0x400420 <puts@plt>
0x00000000004005b0 <+32>: mov w0, #0x0 // #0
0x00000000004005b4 <+36>: ldp x29, x30, [sp],#16
0x00000000004005b8 <+40>: ret
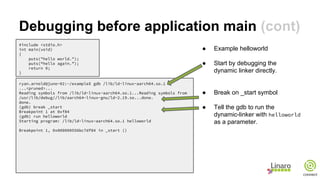
● Example helloworld
● WARNING: The details covered
here are implementation
specific to the link-editor and
are not necessarily part of the
ABI. The details can change!
● Invoke the debugger directly on
the application.
● The branch to puts@plt is
really a branch to special text
section code.](https://image.slidesharecdn.com/hkg15-207-advancedtoolchainusagepart3-150208181030-conversion-gate01/85/HKG15-207-Advanced-Toolchain-Usage-Part-3-16-320.jpg)
![(gdb) si
0x0000000000400420 in puts@plt ()
(gdb) disass
Dump of assembler code for function puts@plt:
=> 0x0000000000400420 <+0>: adrp x16, 0x411000 <__libc_start_main@got.
plt>
0x0000000000400424 <+4>: ldr x17, [x16,#24]
0x0000000000400428 <+8>: add x16, x16, #0x18
0x000000000040042c <+12>: br x17
End of assembler dump.
gdb) x/12i 0x0000000000400400
0x400400 <__gmon_start__@plt>: adrp x16, 0x411000 <__libc_start_main@got.
plt>
0x400404 <__gmon_start__@plt+4>: ldr x17, [x16,#8]
0x400408 <__gmon_start__@plt+8>: add x16, x16, #0x8
0x40040c <__gmon_start__@plt+12>: br x17
0x400410 <abort@plt>: adrp x16, 0x411000 <__libc_start_main@got.plt>
0x400414 <abort@plt+4>: ldr x17, [x16,#16]
0x400418 <abort@plt+8>: add x16, x16, #0x10
0x40041c <abort@plt+12>: br x17
0x400420 <puts@plt>: adrp x16, 0x411000 <__libc_start_main@got.plt>
0x400424 <puts@plt+4>: ldr x17, [x16,#24]
0x400428 <puts@plt+8>: add x16, x16, #0x18
=> 0x40042c <puts@plt+12>: br x17
...
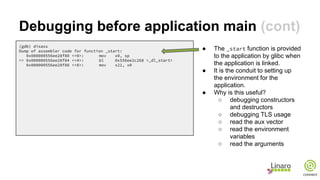
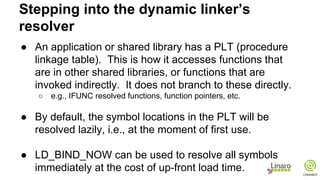
● Step into the branch
● This is special text
section code that loads
the address of the symbol
from the PLT slot
corresponding to the puts
symbol.
● If we look at the text
section a bit in front of
this chunk we can see
two very similar chunks
for other functions that
load addresses from their
PLT slots
Stepping into the dynamic linker’s
resolver (cont)](https://image.slidesharecdn.com/hkg15-207-advancedtoolchainusagepart3-150208181030-conversion-gate01/85/HKG15-207-Advanced-Toolchain-Usage-Part-3-17-320.jpg)
![(gdb) break *0x000000000040042c
Breakpoint 2 at 0x40042c
(gdb) c
Continuing.
Breakpoint 2, 0x000000000040042c in puts@plt ()
(gdb) disass
Dump of assembler code for function puts@plt:
0x0000000000400420 <+0>: adrp x16, 0x411000
<__libc_start_main@got.plt>
0x0000000000400424 <+4>: ldr x17, [x16,#24]
0x0000000000400428 <+8>: add x16, x16, #0x18
=> 0x000000000040042c <+12>: br x17
End of assembler dump.
(gdb) info reg x17
x17 0x4003d0 4195280
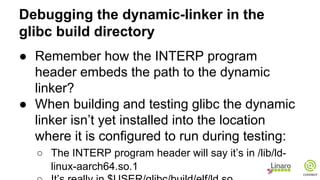
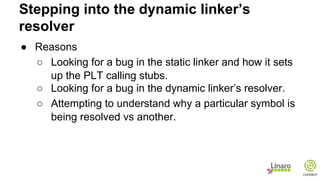
● Let’s see what value is
loaded from the PLT slot
for puts.
● The address 0x4003d0 is
in the text section for this
executable!
Stepping into the dynamic linker’s
resolver (cont)](https://image.slidesharecdn.com/hkg15-207-advancedtoolchainusagepart3-150208181030-conversion-gate01/85/HKG15-207-Advanced-Toolchain-Usage-Part-3-18-320.jpg)

![(gdb) si
0x00000000004003d0 in ?? ()
(gdb) x/5i 0x4003d0
=> 0x4003d0: stp x16, x30, [sp,#-16]!
0x4003d4: adrp x16, 0x410000
0x4003d8: ldr x17, [x16,#4088]
0x4003dc: add x16, x16, #0xff8
0x4003e0: br x17
(gdb) si
0x00000000004003d8 in ?? ()
(gdb) si
0x00000000004003dc in ?? ()
(gdb) si
0x00000000004003e0 in ?? ()
(gdb) x/5i 0x4003d0
0x4003d0: stp x16, x30, [sp,#-16]!
0x4003d4: adrp x16, 0x410000
0x4003d8: ldr x17, [x16,#4088]
0x4003dc: add x16, x16, #0xff8
=> 0x4003e0: br x17
(gdb) info reg x17
x17 0x7fb7fe59a8 548547746216
(gdb) x/1i 0x7fb7fe59a8
0x7fb7fe59a8 <_dl_runtime_resolve>: stp x8, x9, [sp,#-208]!
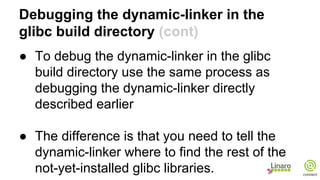
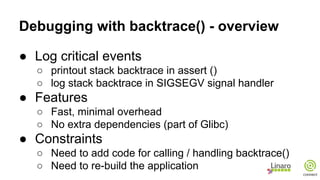
● This is special code in the
text section that loads the
address of the dynamic-
linker’s resolver, namely
_dl_runtime_resolve
● The first time every
symbol is referenced via
its PLT entry the dynamic
linker will first have locate
the address via the
resolver.
Stepping into the dynamic linker’s
resolver (cont)](https://image.slidesharecdn.com/hkg15-207-advancedtoolchainusagepart3-150208181030-conversion-gate01/85/HKG15-207-Advanced-Toolchain-Usage-Part-3-20-320.jpg)
![(gdb) break *0x00000000004005ac
Breakpoint 2, 0x00000000004005ac in main ()
(gdb) si
0x0000000000400420 in puts@plt ()
(gdb) si
0x0000000000400424 in puts@plt ()
(gdb) si
0x0000000000400428 in puts@plt ()
(gdb) si
0x000000000040042c in puts@plt ()
(gdb) disass
Dump of assembler code for function puts@plt:
0x0000000000400420 <+0>: adrp x16, 0x411000
<__libc_start_main@got.plt>
0x0000000000400424 <+4>: ldr x17, [x16,#24]
0x0000000000400428 <+8>: add x16, x16, #0x18
=> 0x000000000040042c <+12>: br x17
End of assembler dump.
(gdb) info reg x17
x17 0x7fb7ef0ad8 548546743000
(gdb) x/1i 0x7fb7ef0ad8
0x7fb7ef0ad8 <_IO_puts>: stp x29, x30, [sp,#-80]!
● Break on the second
puts@plt invocatin and
step through the text
chunk for loading the
address from the PLT.
● Notice that the PLT slot
for puts now contains
the non-local address for
_IO_puts.
Stepping into the dynamic linker’s
resolver (cont)](https://image.slidesharecdn.com/hkg15-207-advancedtoolchainusagepart3-150208181030-conversion-gate01/85/HKG15-207-Advanced-Toolchain-Usage-Part-3-21-320.jpg)
![Debugging with backtrace() - assert()
#include <execinfo.h> /* Also need stdio.h and stdlib.h. */
void assert (void) /* Print out full backtrace(). */
{
char **strings;
int i, size, max = 10;
void **buffer = malloc (max * sizeof (*buffer));
while ((size = backtrace (buffer, max)) == max) /* Loop until we get full backtrace. */
buffer = realloc (buffer, (max *= 2) * sizeof (*buffer));
strings = backtrace_symbols (buffer, size); /* Get printable strings. */
for (i = 0; i < size; ++i)
fprintf (stderr, “%sn”, strings[i]);
free (buffer); /* Free backtrace info. */
free (strings); /* Don’t free strings[i]! */
}](https://image.slidesharecdn.com/hkg15-207-advancedtoolchainusagepart3-150208181030-conversion-gate01/85/HKG15-207-Advanced-Toolchain-Usage-Part-3-24-320.jpg)
![Debugging with backtrace() - SIGSEGV
#include <execinfo.h>
#include <signal.h>
#include <stdlib.h>
static void sigsegv_handler (int sig) { /* Handle SIGSEGV and SIGBUS. */
int size;
void *buffer[100]; /* Can’t malloc() in signal handler! */
size = backtrace (buffer, 100);
backtrace_symbols_fd (buffer, size, 2); /* Send backtrace to stderr. */
}
int main () {
signal (SIGSEGV, sigsegv_handler);
signal (SIGBUS, sigsegv_handler);
*((int *) 0) = 0;
return 0;
}](https://image.slidesharecdn.com/hkg15-207-advancedtoolchainusagepart3-150208181030-conversion-gate01/85/HKG15-207-Advanced-Toolchain-Usage-Part-3-25-320.jpg)


![Address sanitizer example
Simple buffer overrun:
int main(void)
{
char *buf = malloc(10);
for (int i = 0; i <= 10; i++)
buf[i] = 0;
return buf[0];
}](https://image.slidesharecdn.com/hkg15-207-advancedtoolchainusagepart3-150208181030-conversion-gate01/85/HKG15-207-Advanced-Toolchain-Usage-Part-3-33-320.jpg)

![Address sanitizer example
Not all bad accesses will be caught:
int main(void)
{
char *buf = malloc(10);
sprintf(buf, "abcdefg %d", INT_MAX);
return buf[0];
}](https://image.slidesharecdn.com/hkg15-207-advancedtoolchainusagepart3-150208181030-conversion-gate01/85/HKG15-207-Advanced-Toolchain-Usage-Part-3-35-320.jpg)



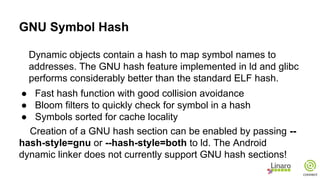
![GCC Attributes
Attributes:
● Language extensions (GNU C)
● Give directives or information to the compiler
● Act on verification, code usage or optimization
● Apply on Functions, Types, Variables or Labels
https://gcc.gnu.org/onlinedocs/gcc/Function-Attributes.html
https://gcc.gnu.org/onlinedocs/gcc/Type-Attributes.html
Syntax: __attribute__ ((ATTRIBUTE_LIST))
https://gcc.gnu.org/onlinedocs/gcc/Variable-Attributes.html
https://gcc.gnu.org/onlinedocs/gcc/Label-Attributes.html
Support added in the
standard since C++11
[[ attribute ]]
[[ gnu::att_name ]]](https://image.slidesharecdn.com/hkg15-207-advancedtoolchainusagepart3-150208181030-conversion-gate01/85/HKG15-207-Advanced-Toolchain-Usage-Part-3-51-320.jpg)

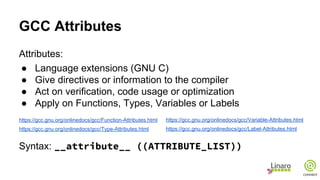
![GCC Attributes: Compile Time Checking
error (“message”)
warning (“message”)
deprecated (“message”) (c++14)
format (type,fstring,index)
format_arg (fstring)
nonnull (arg_index,...)
sentinel (index)
warn_unused_result
Apply on: Functions, Variables, Types
Effect: Raise compile time warnings or errors
Use cases: Code refactoring or assertions
extern int foo() __attribute__ ((error ("BAD")));
typedef int T __attribute__ ((deprecated))
T bar () { return foo();}
~$ gcc err.c
err.c:5:1: warning: 'T' is deprecated [-Wdeprecated-declarations]
T bar () {
^
err.c: In function 'bar':
err.c:6:10: error: call to 'foo' declared with attribute error: BAD
return (T) foo();
^
err.c](https://image.slidesharecdn.com/hkg15-207-advancedtoolchainusagepart3-150208181030-conversion-gate01/85/HKG15-207-Advanced-Toolchain-Usage-Part-3-54-320.jpg)
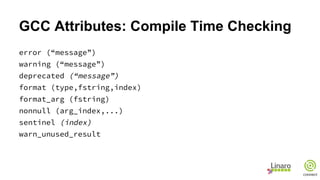
![GCC Attributes: Compile Time Checking
error (“message”)
warning (“message”)
deprecated (“message”)
format (type,fstring,index)
format_arg (fstring)
nonnull (arg_index,...)
sentinel (index)
warn_unused_result
Apply on: Functions
Effect: Argument checking
Use case: printf, scanf, strftime, strfmon like functions
extern void debug_msg (int level, const char *format, ...)
__attribute__ ((format(printf, 2, 3)));
void foo(int param) {
debug_msg (4, "In foo, param = %d , %s", param);
}
~$ gcc -S p.c
p.c: In function ’foo’:
p.c:5:2: warning: format ’%s’ expects a matching ’char *’ argument [-
Wformat=]
debug_msg (4, "In foo, param = %d , %s", param);
^
p.c](https://image.slidesharecdn.com/hkg15-207-advancedtoolchainusagepart3-150208181030-conversion-gate01/85/HKG15-207-Advanced-Toolchain-Usage-Part-3-55-320.jpg)
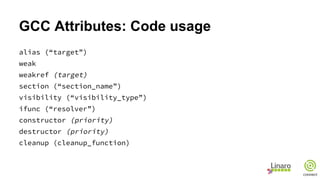
![GCC Attributes: Compile Time Checking
error (“message”)
warning (“message”)
deprecated (“message”)
format (type,fstring,index)
format_arg (fstring)
nonnull (arg_index,...)
sentinel (index)
warn_unused_result
Apply on: Functions
Effect: Warning if caller doesn’t use return value
int fn () __attribute__ ((warn_unused_result));
int foo () {
if (fn () < 0) return -1;
fn ();
}
~$ gcc -S wur.c
wur.c: In function ’foo’:
wur.c:5:5: warning: ignoring return value of ’fn’, declared with
attribute warn_unused_result [-Wunused-result]
fn ();
^
wur.c](https://image.slidesharecdn.com/hkg15-207-advancedtoolchainusagepart3-150208181030-conversion-gate01/85/HKG15-207-Advanced-Toolchain-Usage-Part-3-56-320.jpg)

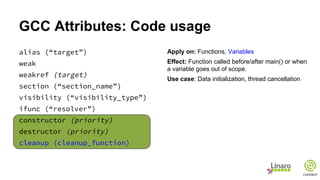

![GCC Attributes: Optimization
optimize
leaf
malloc
const
pure
noreturn (c++11)
nothrow
returns_nonnull
assume_aligned (align,offset)
Apply on: Functions
Effect: Improve optimization (inlining, constant
propagation, ...)
Use case: Help your compiler !
GCC can point you candidates for attributes:
-Wsuggest-attribute=[pure|const|noreturn|format]](https://image.slidesharecdn.com/hkg15-207-advancedtoolchainusagepart3-150208181030-conversion-gate01/85/HKG15-207-Advanced-Toolchain-Usage-Part-3-64-320.jpg)
![GCC Attributes: ARM
foo:
push {r7}
sub sp, sp, #12
add r7, sp, #0
str r0, [r7, #4]
str r1, [r7]
.syntax unified
@ 2 "arm.c" 1
@ MY CODE
@ 0 "" 2
.thumb
.syntax unified
nop
mov r0, r3
adds r7, r7, #12
mov sp, r7
@ sp needed
ldr r7, [sp], #4
bx lr
bar:
.syntax unified
@ 6 "arm.c" 1
@ MY CODE
@ 0 "" 2
.thumb
.syntax unified
nop
mov r0, r3
m_irq:
push {r0, r1, r3, r7}
sub sp, sp, #8
add r7, sp, #0
str r0, [r7, #4]
str r1, [r7]
.syntax unified
@ 10 "arm.c" 1
@ MY CODE
@ 0 "" 2
.thumb
.syntax unified
nop
mov r0, r3
adds r7, r7, #8
mov sp, r7
@ sp needed
pop {r0, r1, r3, r7}
subs pc, lr, #4](https://image.slidesharecdn.com/hkg15-207-advancedtoolchainusagepart3-150208181030-conversion-gate01/85/HKG15-207-Advanced-Toolchain-Usage-Part-3-67-320.jpg)
![GCC Attributes: ARM
f1:
push {r7}
sub sp, sp, #12
add r7, sp, #0
str r0, [r7, #4] @ float
str r2, [r7] @ float
.syntax unified
@ 14 "arm.c" 1
@ MY CODE
@ 0 "" 2
.thumb
.syntax unified
nop
mov r0, r3
adds r7, r7, #12
mov sp, r7
@ sp needed
ldr r7, [sp], #4
bx lr
f2:
push {r7}
sub sp, sp, #12
add r7, sp, #0
vstr.32 s0, [r7, #4]
vstr.32 s1, [r7]
.syntax unified
@ 18 "arm.c" 1
@ MY CODE
@ 0 "" 2
.thumb
.syntax unified
nop
mov r0, r3
adds r7, r7, #12
mov sp, r7
@ sp needed
ldr r7, [sp], #4
bx lr](https://image.slidesharecdn.com/hkg15-207-advancedtoolchainusagepart3-150208181030-conversion-gate01/85/HKG15-207-Advanced-Toolchain-Usage-Part-3-68-320.jpg)