This presentation provides an overview of hash functions and how they are used. It discusses:
- The history and applications of hashing, including hash tables and databases.
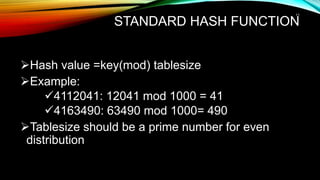
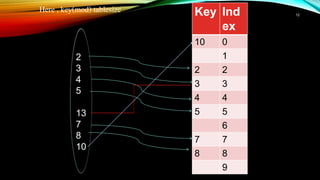
- How hash functions work by mapping data to a fixed size and introducing the concept of collisions.
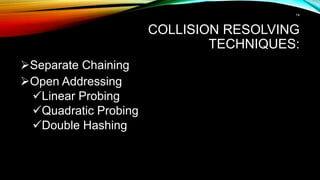
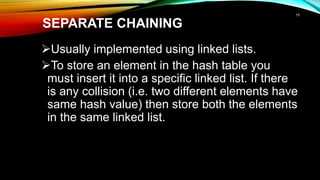
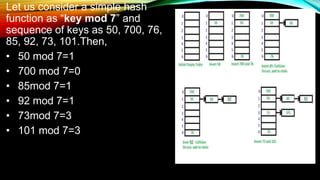
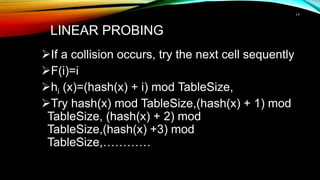
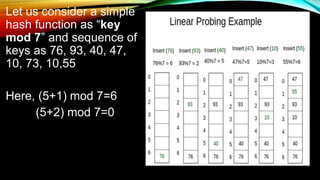
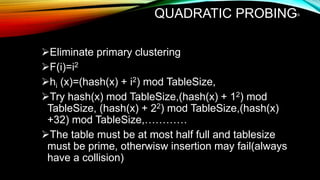
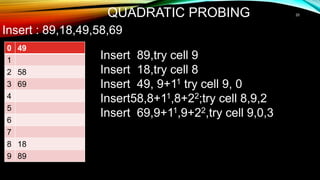
- Common hash function algorithms like separate chaining and linear probing and how they handle collisions.
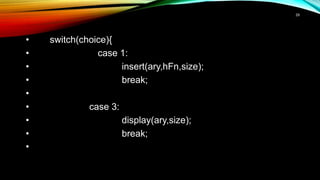
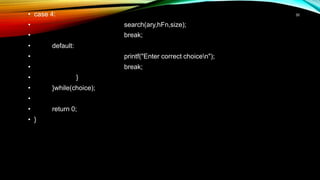
- An example implementation in C of a hash table with functions for insertion, searching, and display.
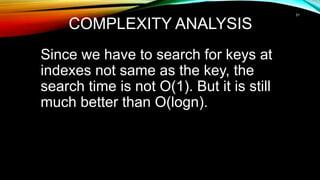
- The time complexity of hash table operations is better than logarithmic search but not constant like ideal hash functions.


![INSERT ALGORITHM
Hash-insert(T,k) // T= array that represent hash table
i = 0 to m // m = number of indices ,i=look counter
Repeat
• j = h(k,i) //J=hash value
• if T[j] == NIL
• T[j] = k
• return j
• else i = i + 1
until i == m
error “hash table overflow”
21](https://image.slidesharecdn.com/hash-function1-190307073622/85/Hash-function-21-320.jpg)
![SEARCH ALGORITHM
Hash-Search(T,k)
i = 0
repeat
• j = h(k,i)
• If T[j] == k
• Return T[ j]
• i = i + 1
until T[j]== NIL or i == m
return NIL
22](https://image.slidesharecdn.com/hash-function1-190307073622/85/Hash-function-22-320.jpg)
![IMPLEMENTATION
• #include<stdio.h>
• #include<limits.h>
•
•
• void insert(int ary[],int hFn, int size){
• int element,pos,n=0;
•
• printf("Enter key element to insertn");
• scanf("%d",&element);
•
• pos = element%hFn;
23](https://image.slidesharecdn.com/hash-function1-190307073622/85/Hash-function-23-320.jpg)
![while(ary[pos=! size) { // INT_MAX indicates that cell is empty. So if cell is empty loop will
break and goto bottom of the loop to insert element
if(ary[pos]== INT_MAX)
break;
pos = (pos+1)%hFn;
n++;
if(n==size)
break;
}
if(n==size)
printf("Hash table was full of elementsnNo Place to insert this elementnn");
else
ary[pos] = element; //Inserting element
}
24](https://image.slidesharecdn.com/hash-function1-190307073622/85/Hash-function-24-320.jpg)
![• void search(int ary[],int hFn,int size){
• int element,pos,n=0;
•
• printf("Enter element you want to searchn");
• scanf("%d",&element);
•
• pos = element%hFn;
•
• while(n++ != size){
• if(ary[pos]==element){
• printf("Element found at index %dn",pos);
• break;
• }
25](https://image.slidesharecdn.com/hash-function1-190307073622/85/Hash-function-25-320.jpg)
![• else
• if(ary[pos]==INT_MAX ||ary[pos]!=INT_MIN)
• pos = (pos+1) %hFn;
• }
• if(--n==size) printf("Element not found in hash tablen");
• }
• void display(int ary[],int size){
• int i;
•
• printf("IndextValuen");
•
•
26](https://image.slidesharecdn.com/hash-function1-190307073622/85/Hash-function-26-320.jpg)
![• for(i=0;i<size;i++)
• printf("%dt%dn",i,ary[i]);
• }
• int main(){
• int size,hFn,i,choice;
•
• printf("Enter size of hash tablen");
• scanf("%d",&size);
•
• int ary[size];
•
• printf("Enter hash function [if mod 10 enter 10]n");
• scanf("%d",&hFn);
27](https://image.slidesharecdn.com/hash-function1-190307073622/85/Hash-function-27-320.jpg)
![• for(i=0;i<size;i++)
• ary[i]=INT_MIN; //Assigning INT_MIN indicates that
cell is empty
•
• do{
• printf("Enter your choicen");
• printf(" 1-> Insertn 2-> Deleten 3-> Displayn
4-> Searchingn 0-> Exitn");
• scanf("%d",&choice);
28](https://image.slidesharecdn.com/hash-function1-190307073622/85/Hash-function-28-320.jpg)