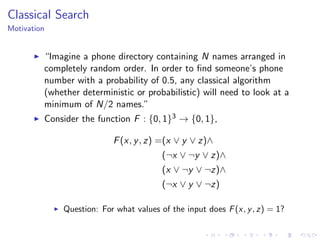
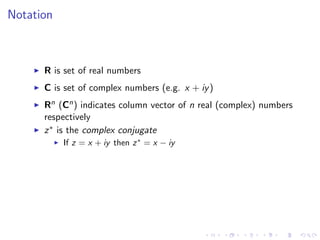
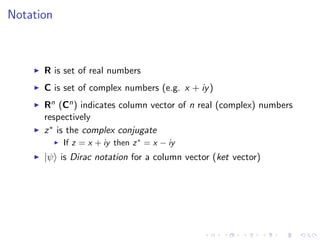
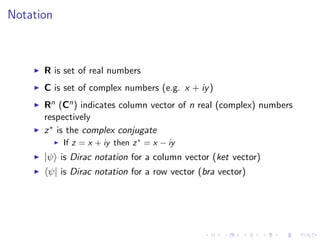
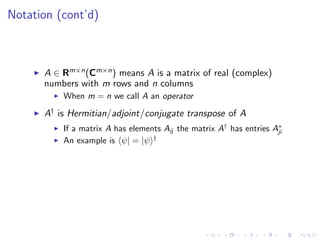
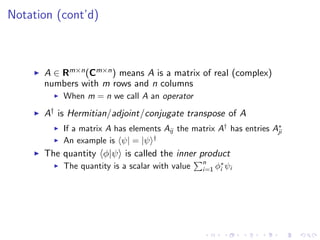
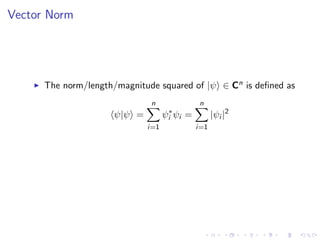
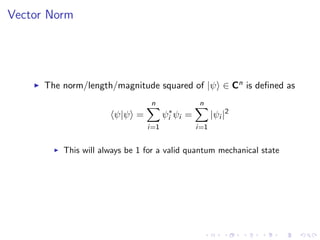
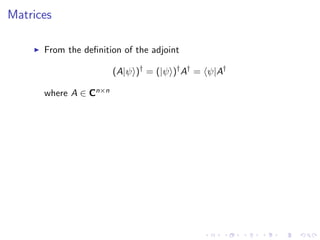
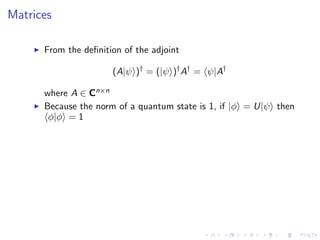
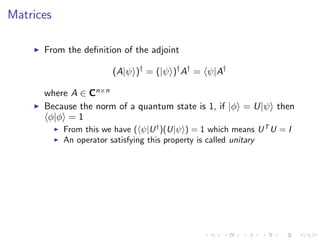
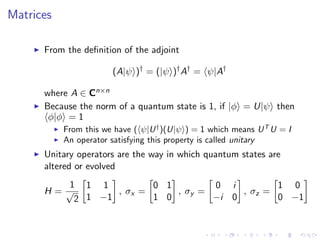
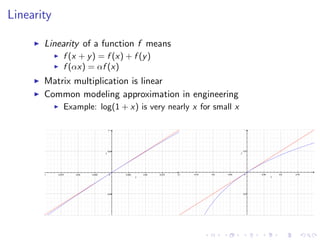
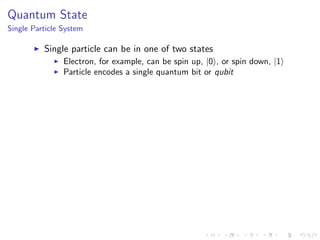
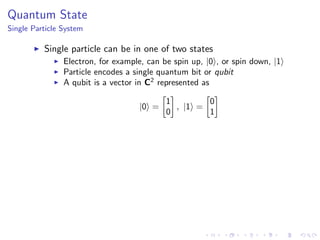
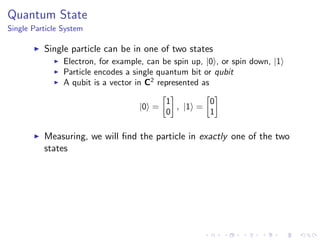
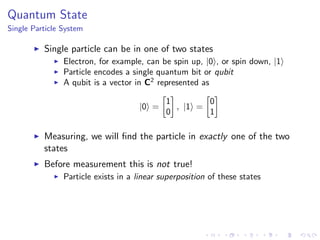
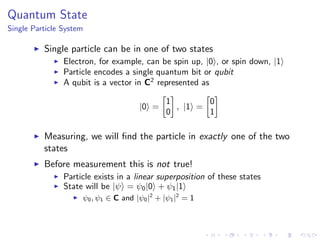
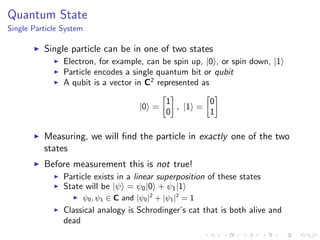
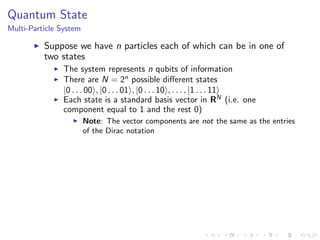
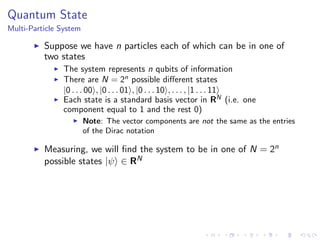
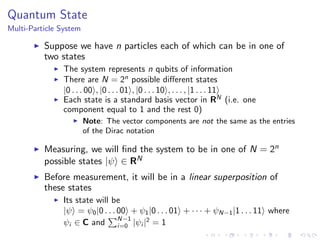
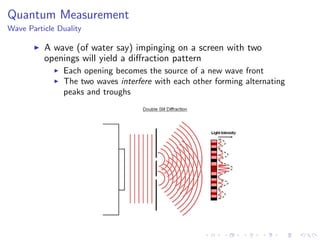
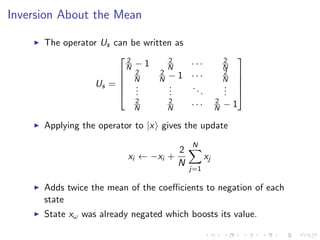
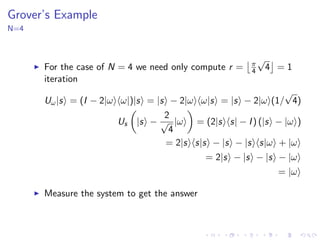
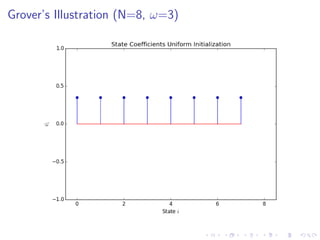
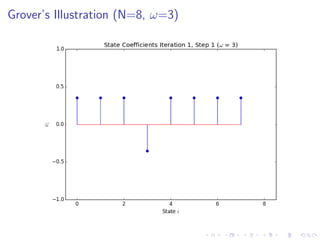
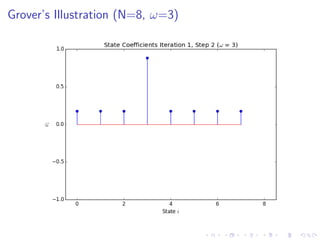
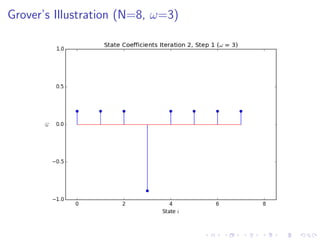
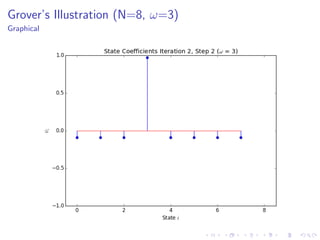
The document discusses Grover's algorithm, a quantum search algorithm that significantly improves the search complexity from O(n) for classical algorithms to O(√n) for large n. It provides a comprehensive overview of quantum mechanics, including essential concepts such as quantum states, linear superposition, and the Born rule, emphasizing the probabilistic nature of quantum measurements. Additionally, it elaborates on mathematical notations relevant to quantum mechanics and the implications of linearity in quantum systems.