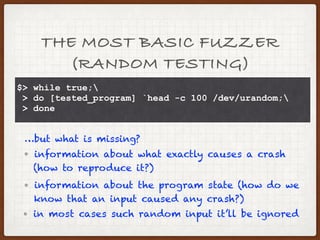
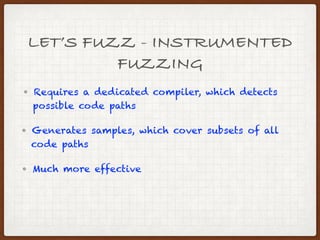
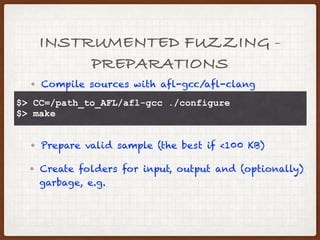
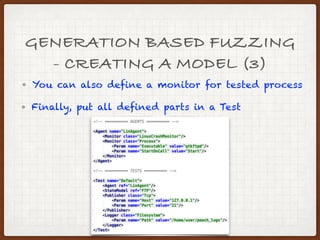
Fuzzing is a method of discovering software faults by providing unexpected input and monitoring for exceptions. There are two main types of fuzzers: mutation-based fuzzers which mutate valid samples, and generation-based fuzzers which require samples to be defined. Fuzzing discovers bugs by providing invalid input to any software, so it should always be considered as a testing method. A fuzzer contains an input generator, history of generated inputs, and a process monitor.