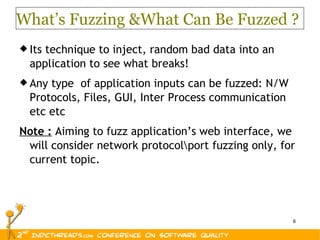
The document presents an overview of 'performfuzz', a technique combining performance testing and fuzzing to evaluate and enhance application security, particularly within web interfaces. It explores how fuzzing can identify vulnerabilities, such as buffer overflows and invalid memory references, through the injection of random data to stress-test application components. Additionally, it outlines best practices for mitigating performance degradation caused by fuzzing, emphasizing the importance of defensive security measures.


















![The End. Thank You! Aniket Kulkarni , Product Security Group, Symantec. [email_address]](https://image.slidesharecdn.com/performfuzz-onappplicationswebinterface-110326004623-phpapp02/85/Perform-fuzz-on-appplications-web-interface-20-320.jpg)