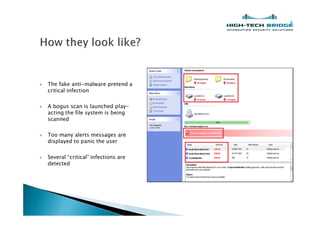
The document discusses the prevalence and tactics of fake malware and virus scanners that deceive users into purchasing non-functional programs through scare tactics and false alerts. It details case studies of how these scams operate, including misleading scans and compromised advertisements. Recommendations for prevention include using legitimate antimalware software, keeping systems updated, and being cautious with pop-ups.