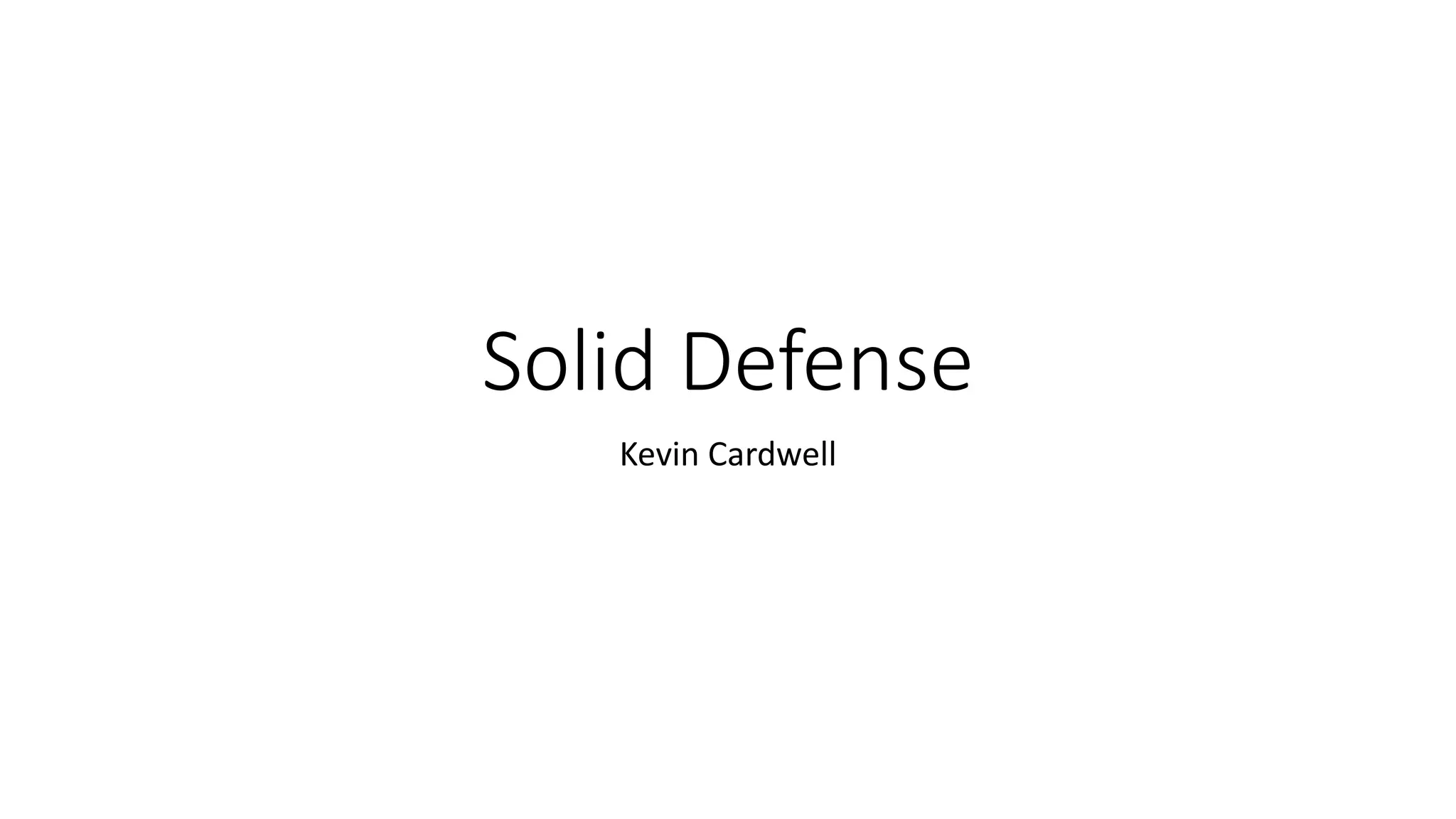
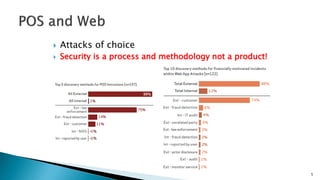
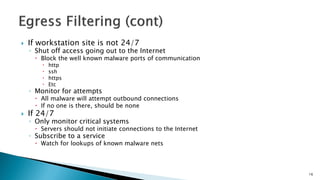
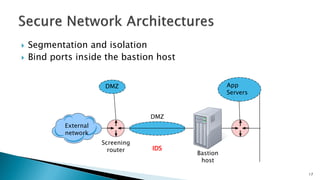
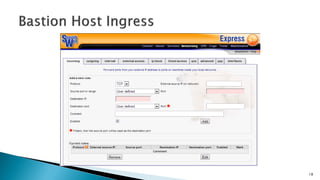
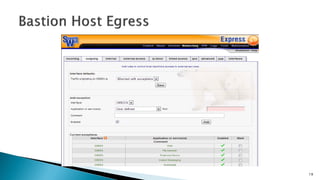
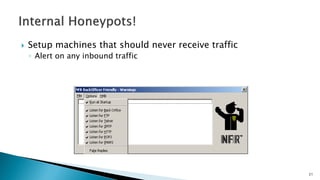
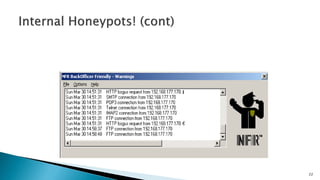
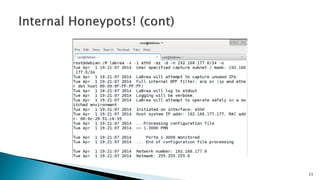
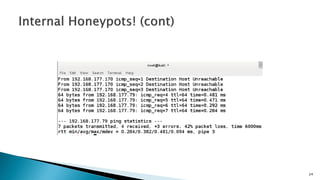
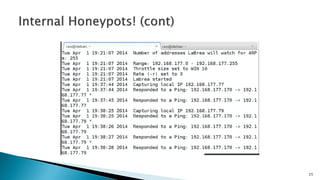
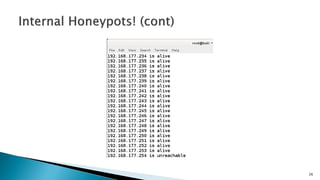
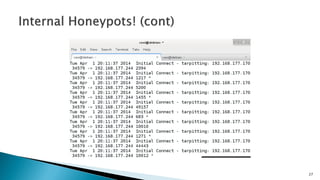
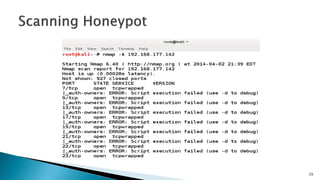
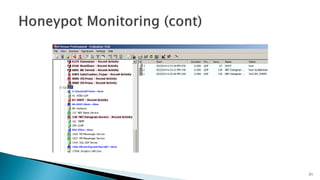
This document discusses proven defense measures for network security. It recommends implementing firewall filters to block unauthorized inbound and outbound traffic. Specific measures include egress filtering to block traffic from being spoofed on the network, blackhole routing to drop spoofed packets, and shutting off or monitoring outbound access from workstations when not in use. It also recommends network segmentation, binding ports on bastion hosts, using intrusion detection systems, sinkholing malicious domains, and monitoring systems that should never receive inbound traffic. The overall message is that security is a process that involves hardening systems, applying patches, and implementing layered defenses like firewall filtering to block threats.