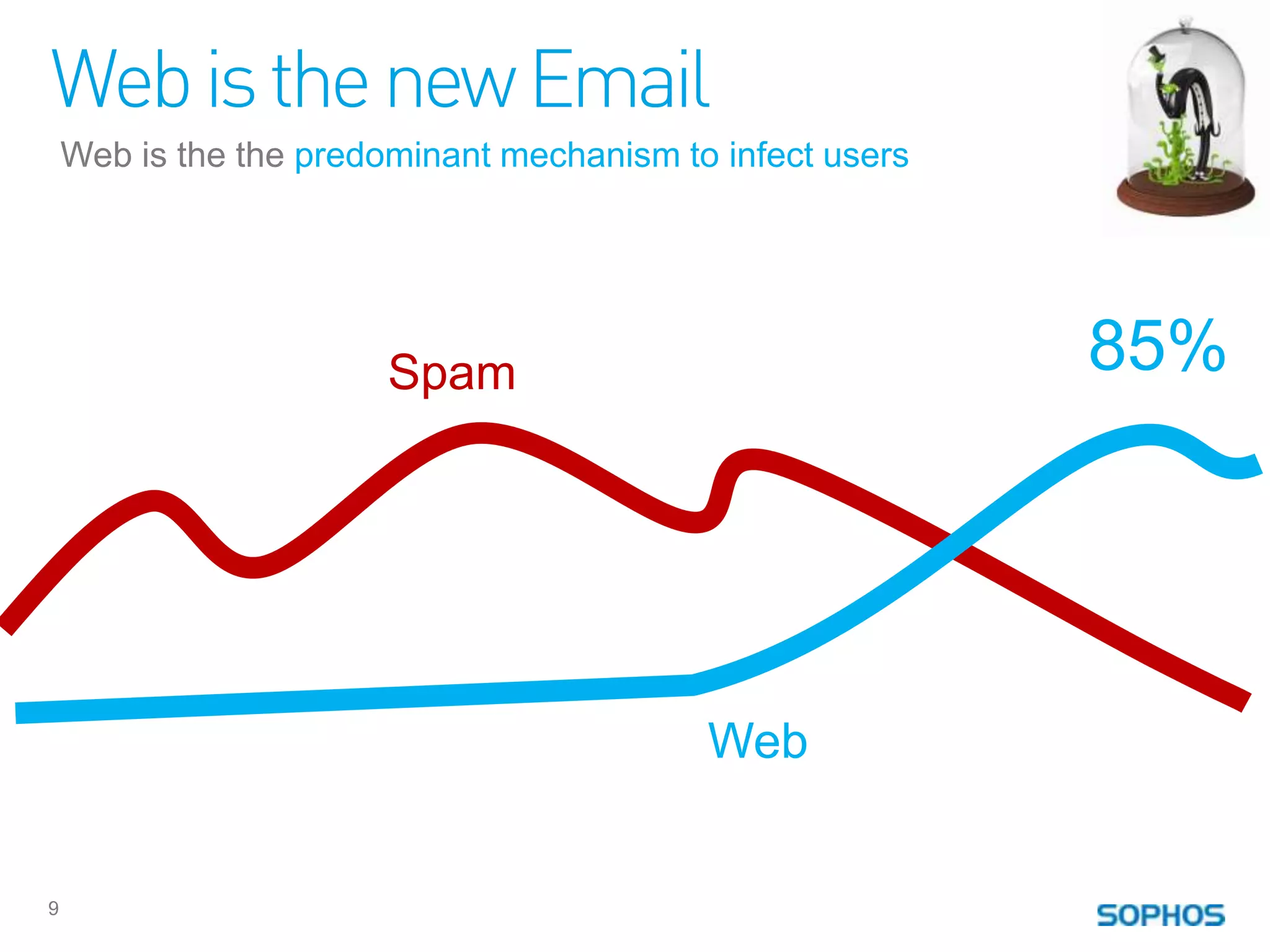
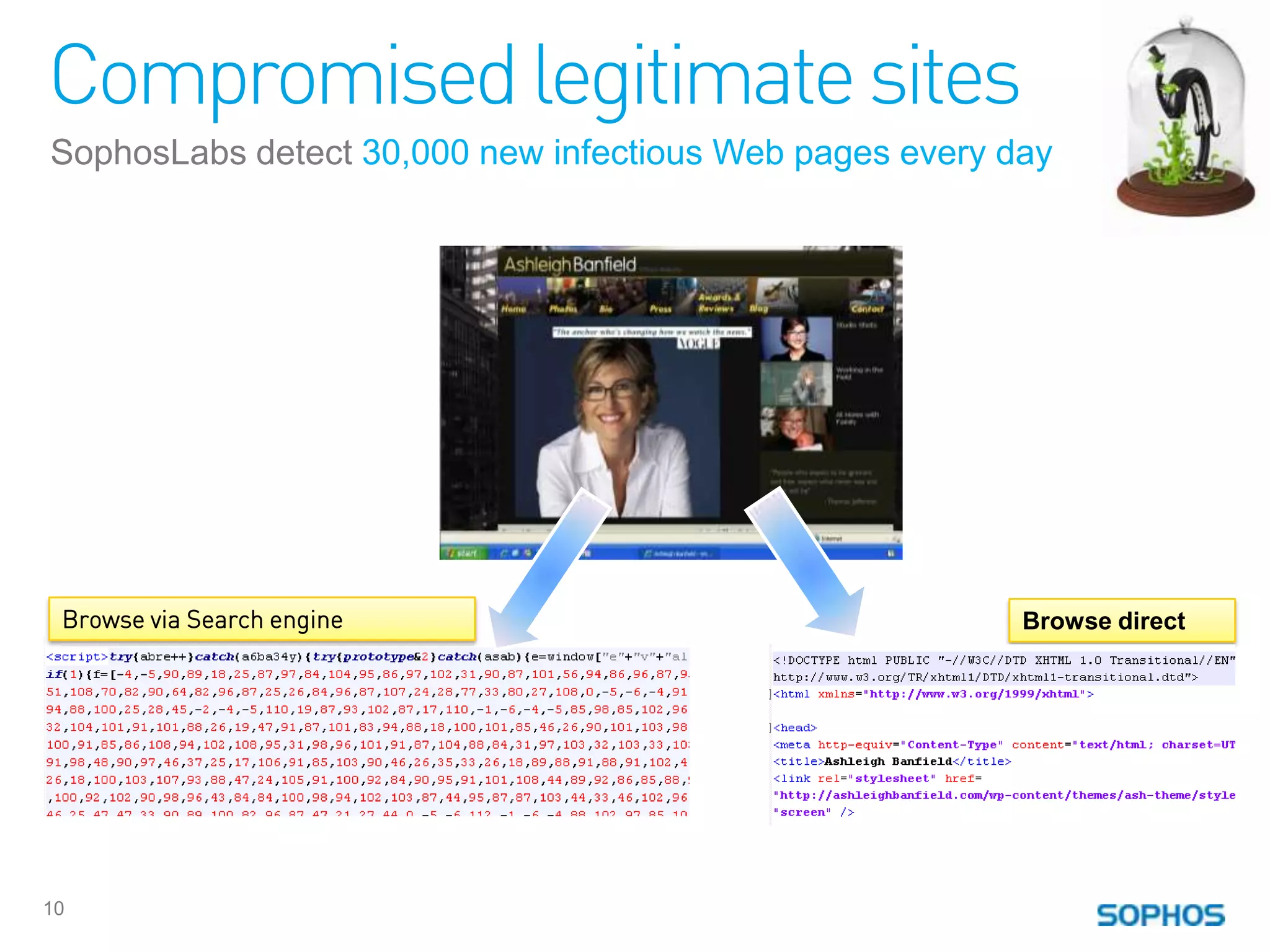
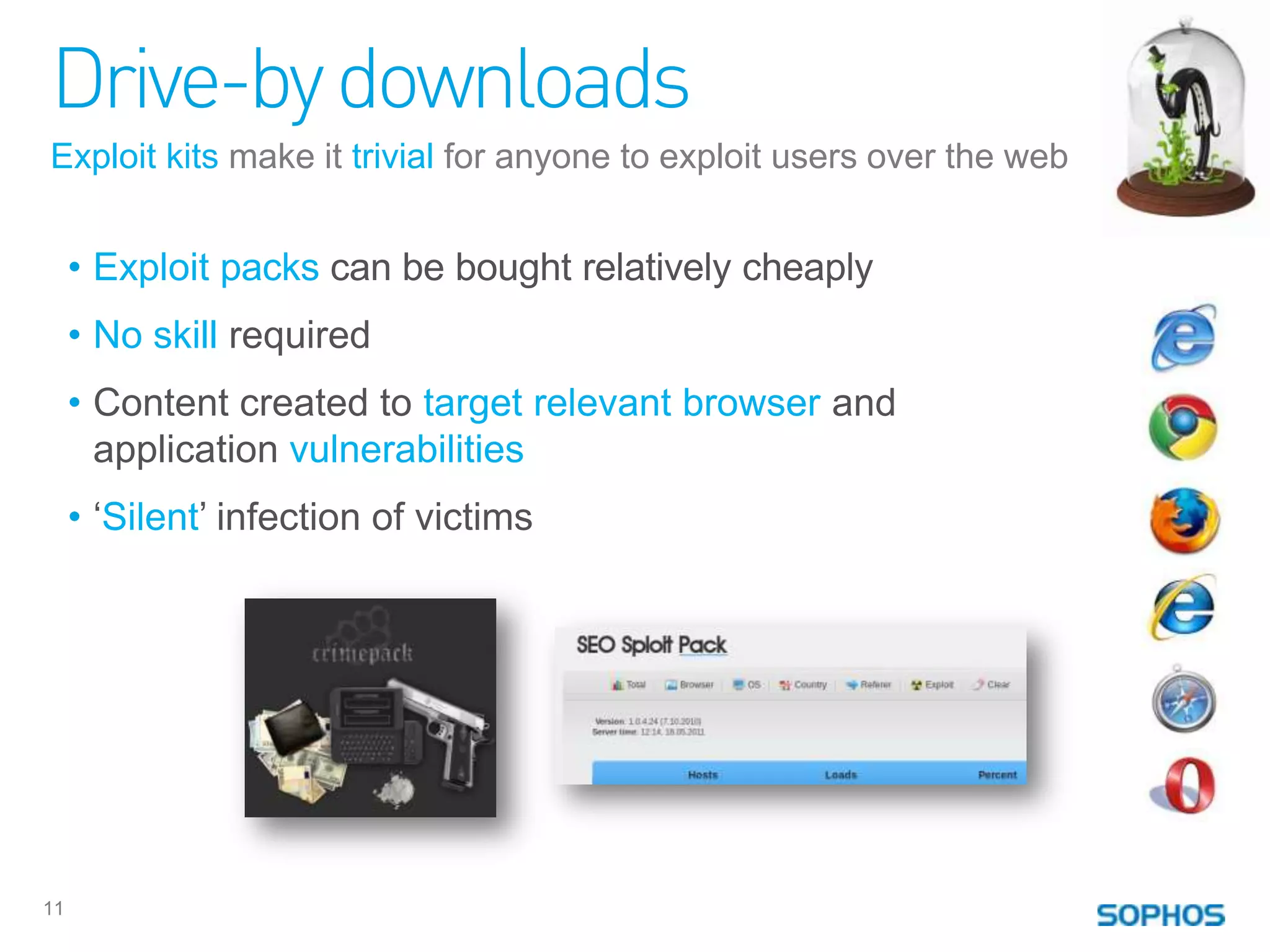
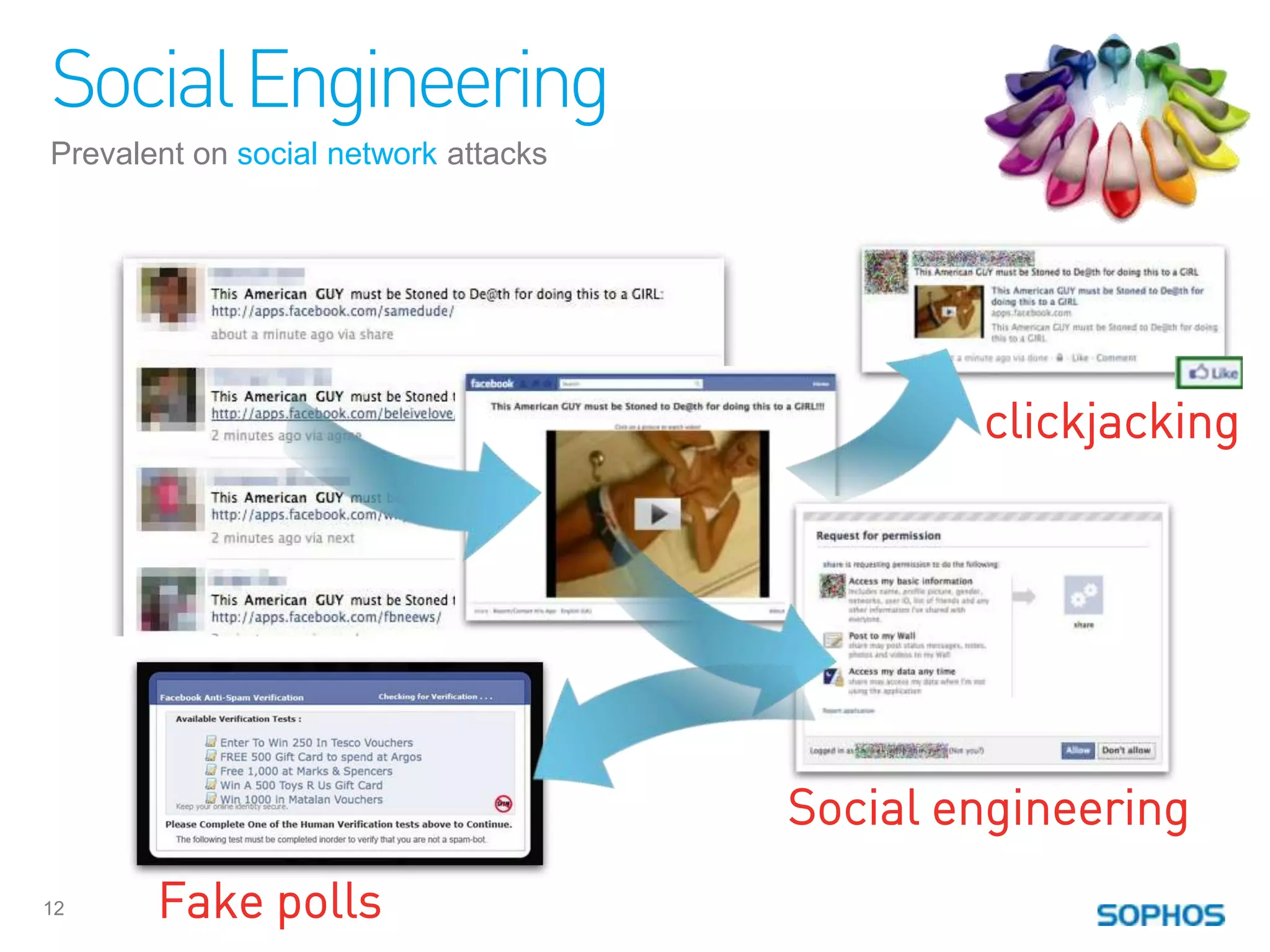
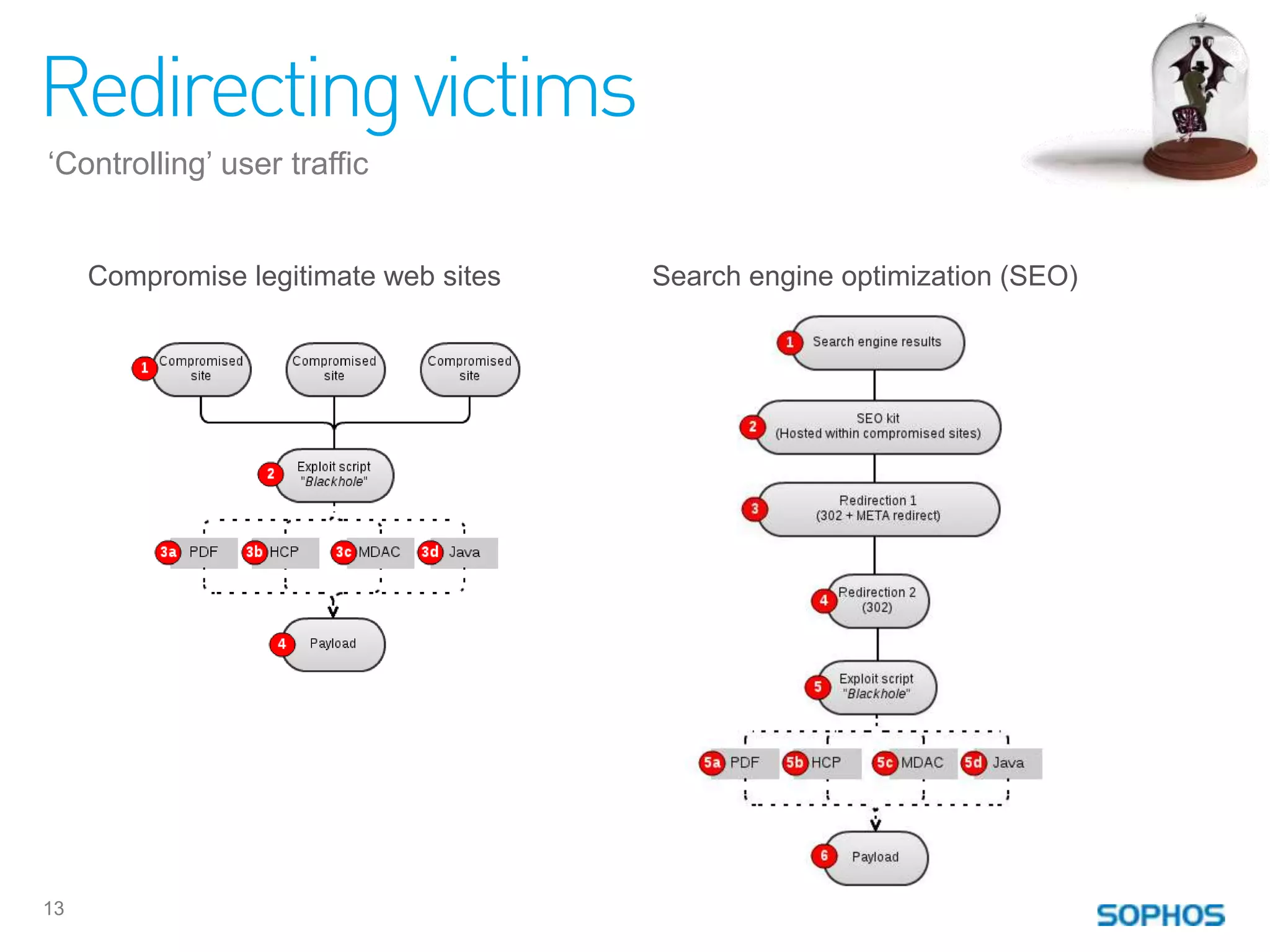
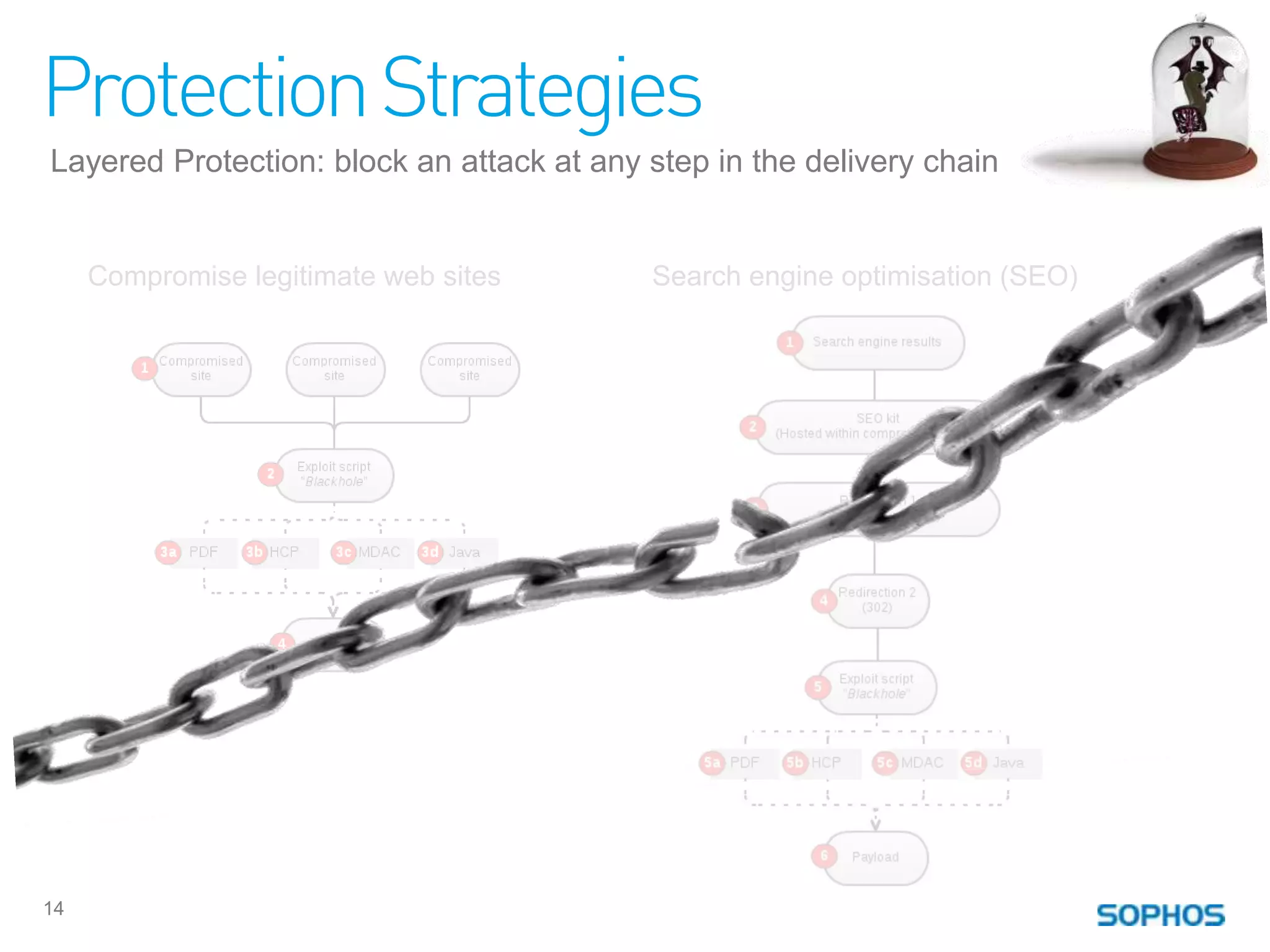
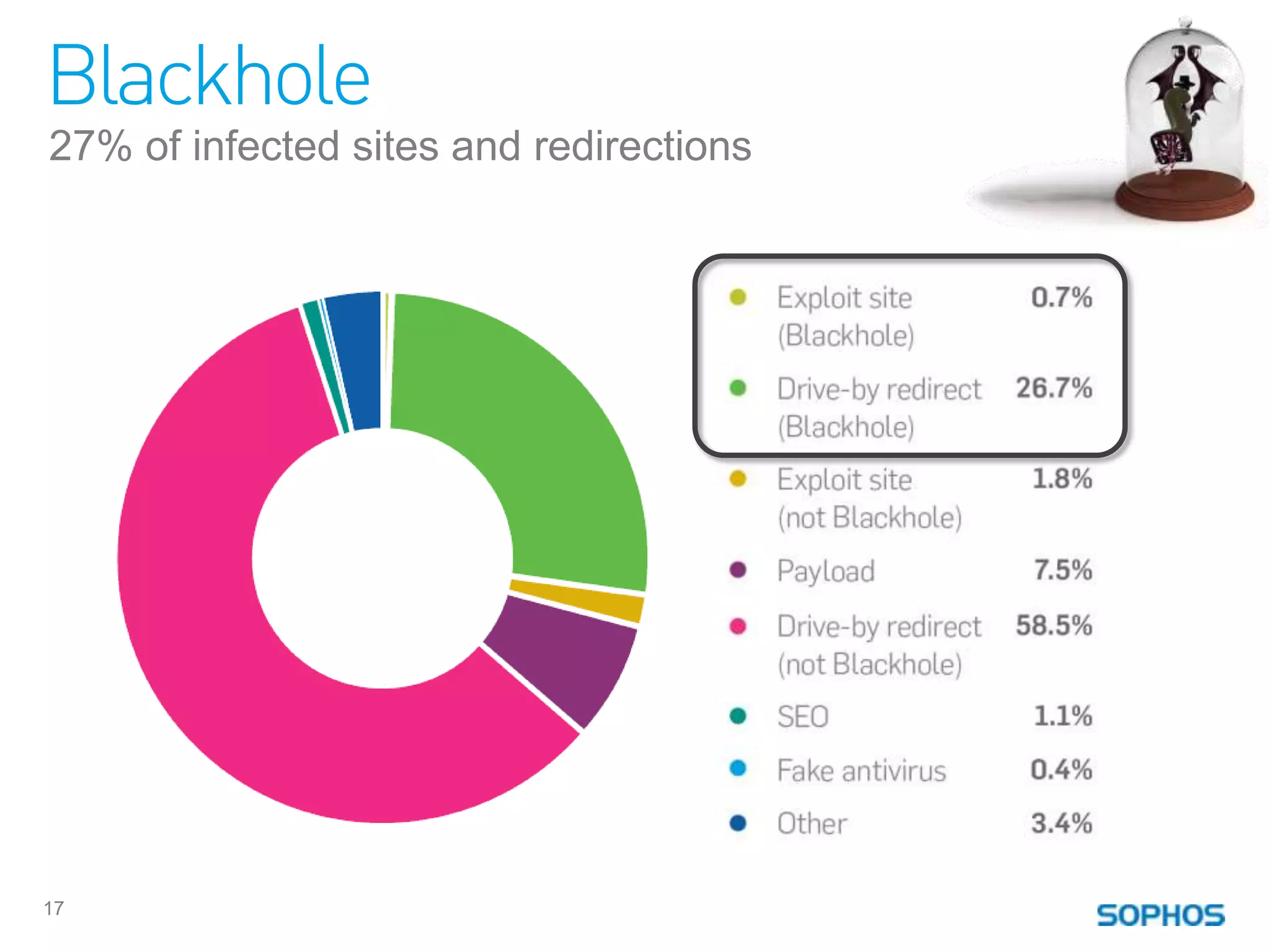
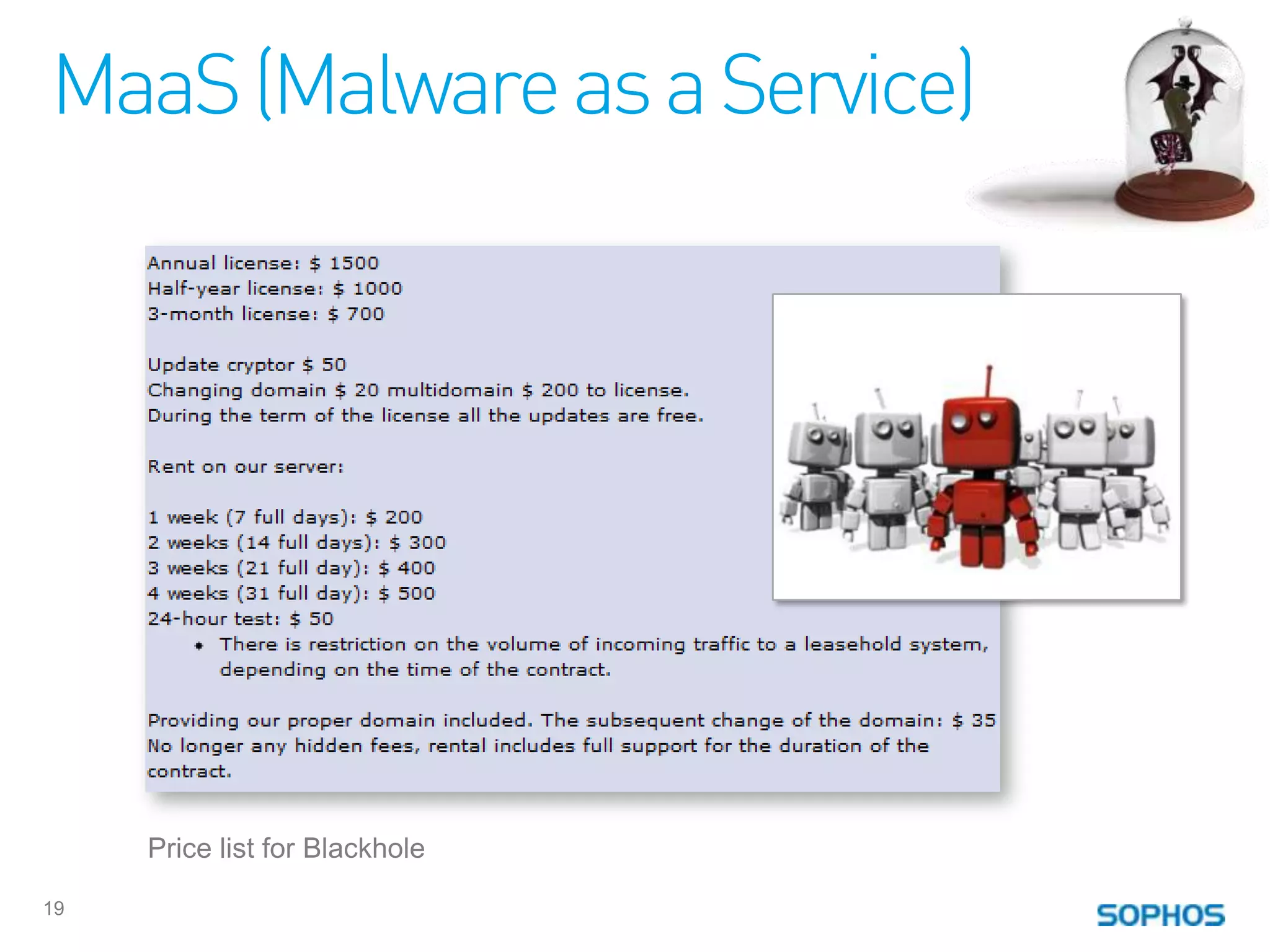
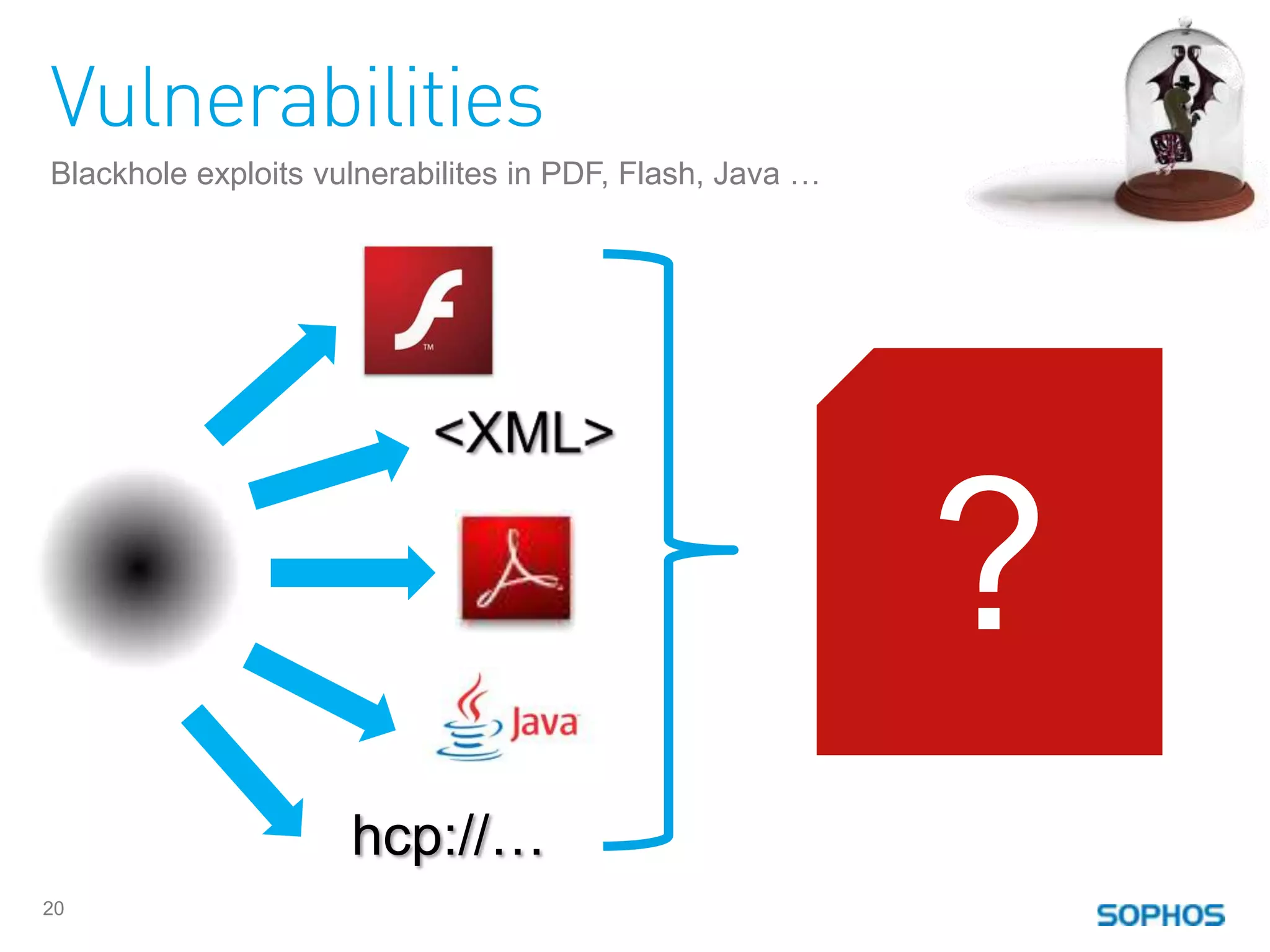
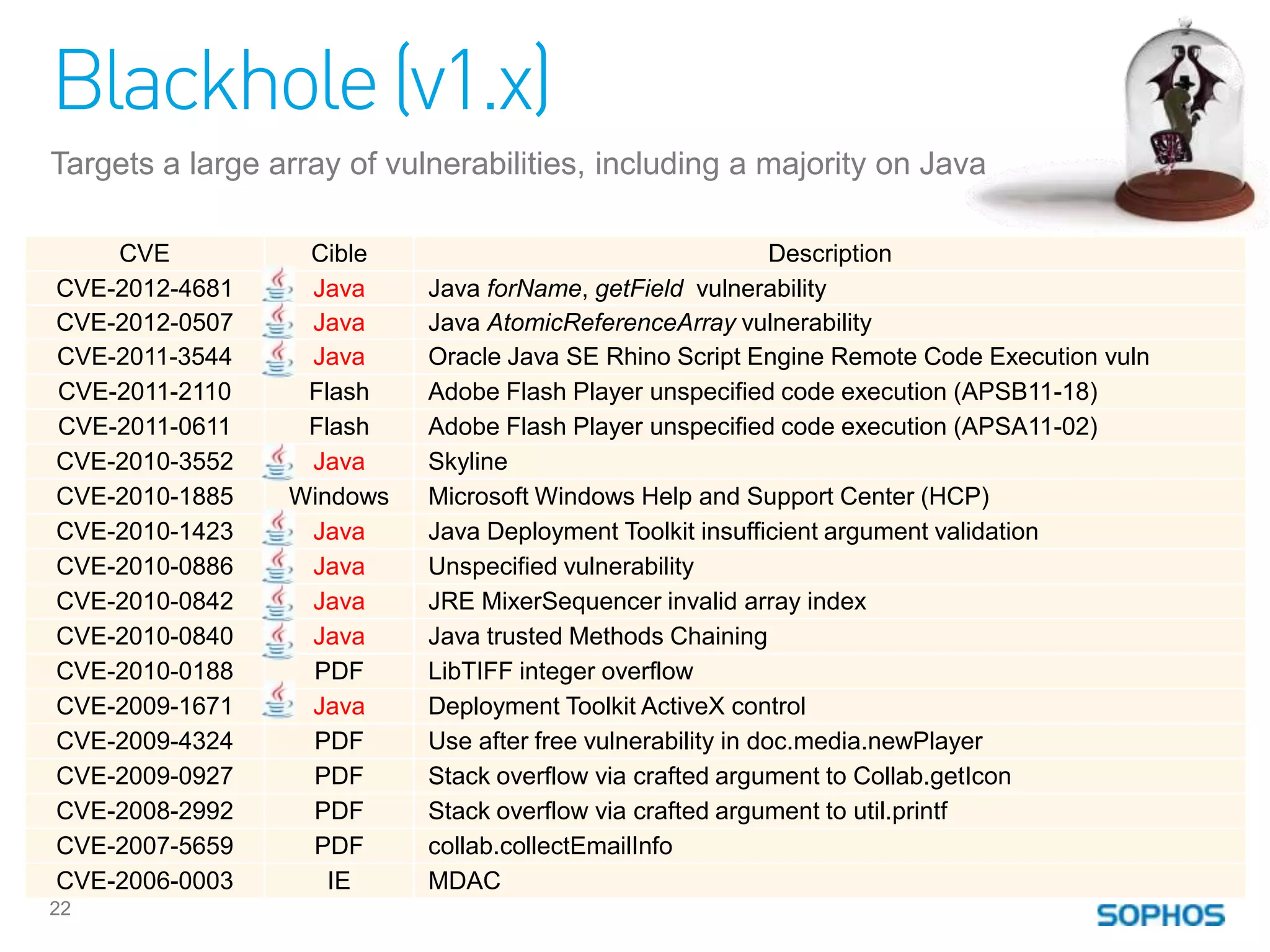
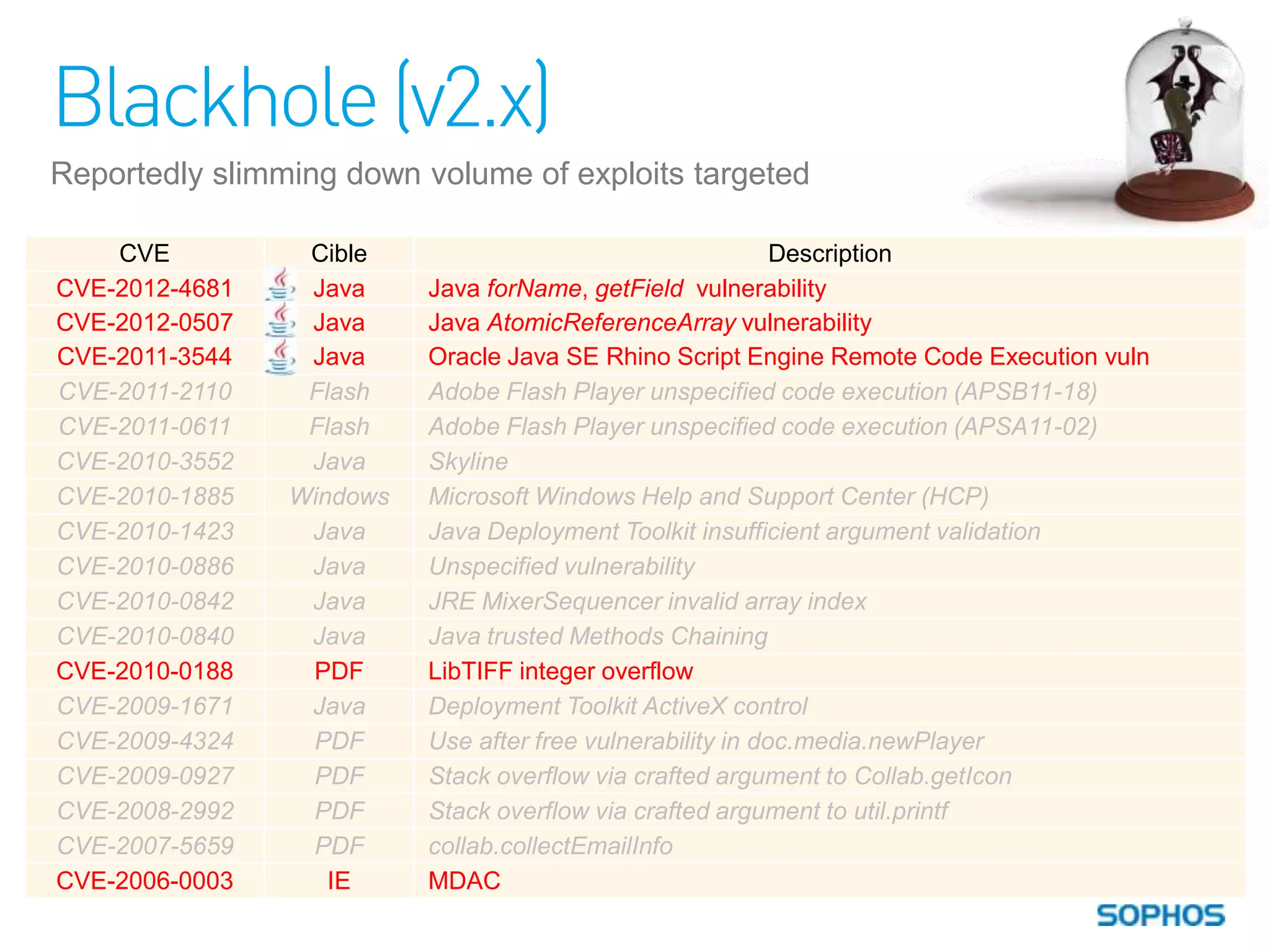
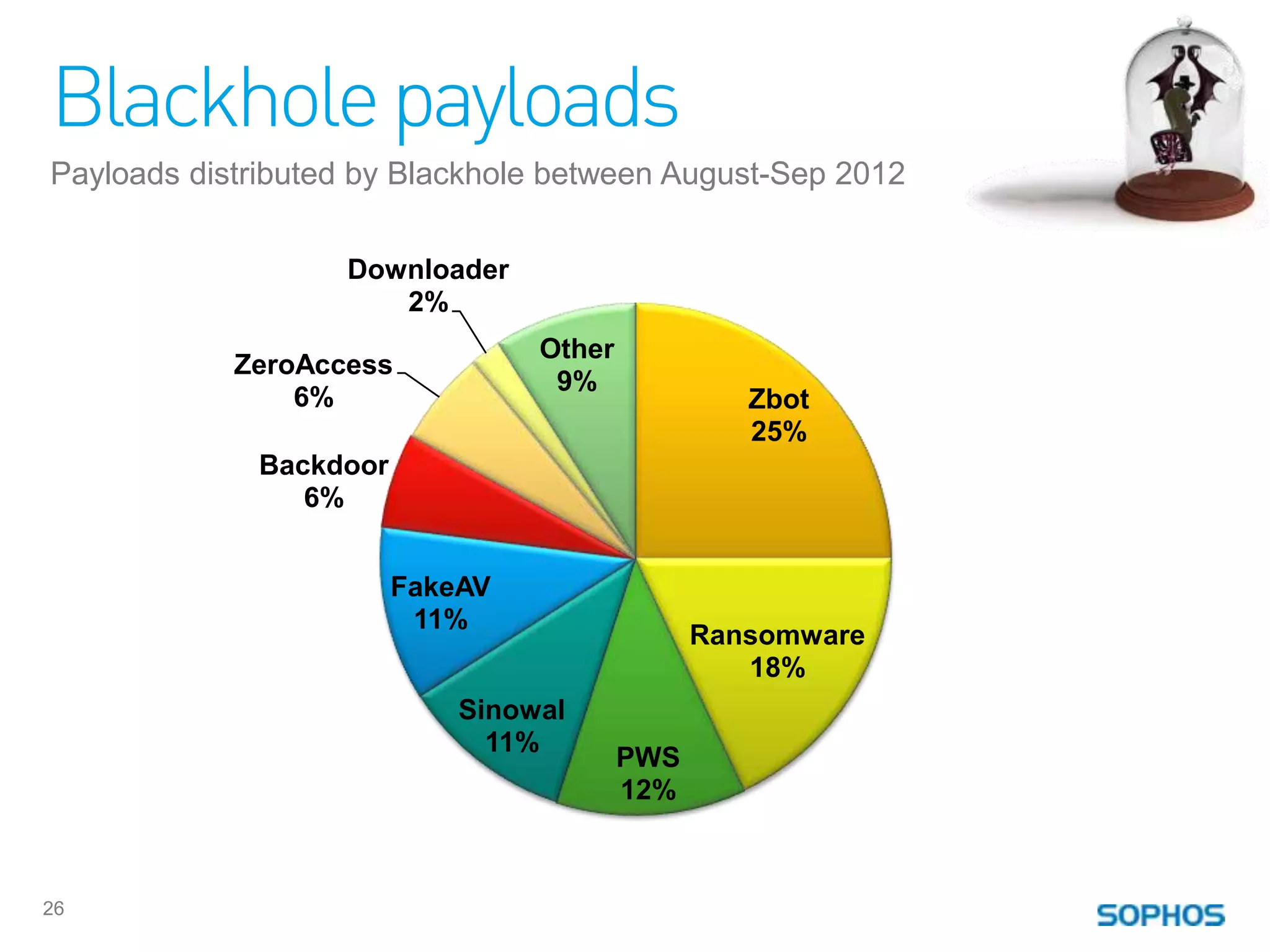
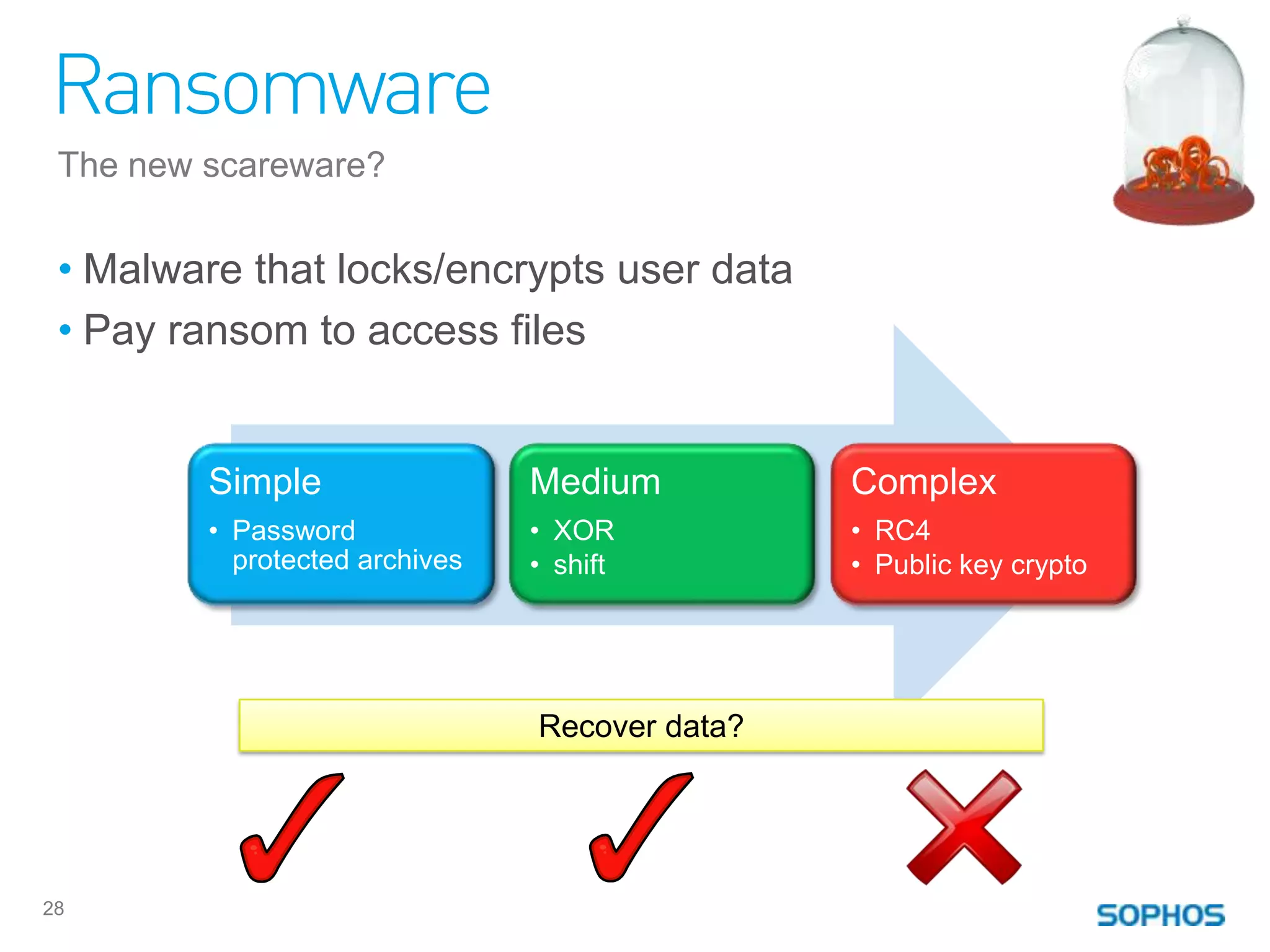
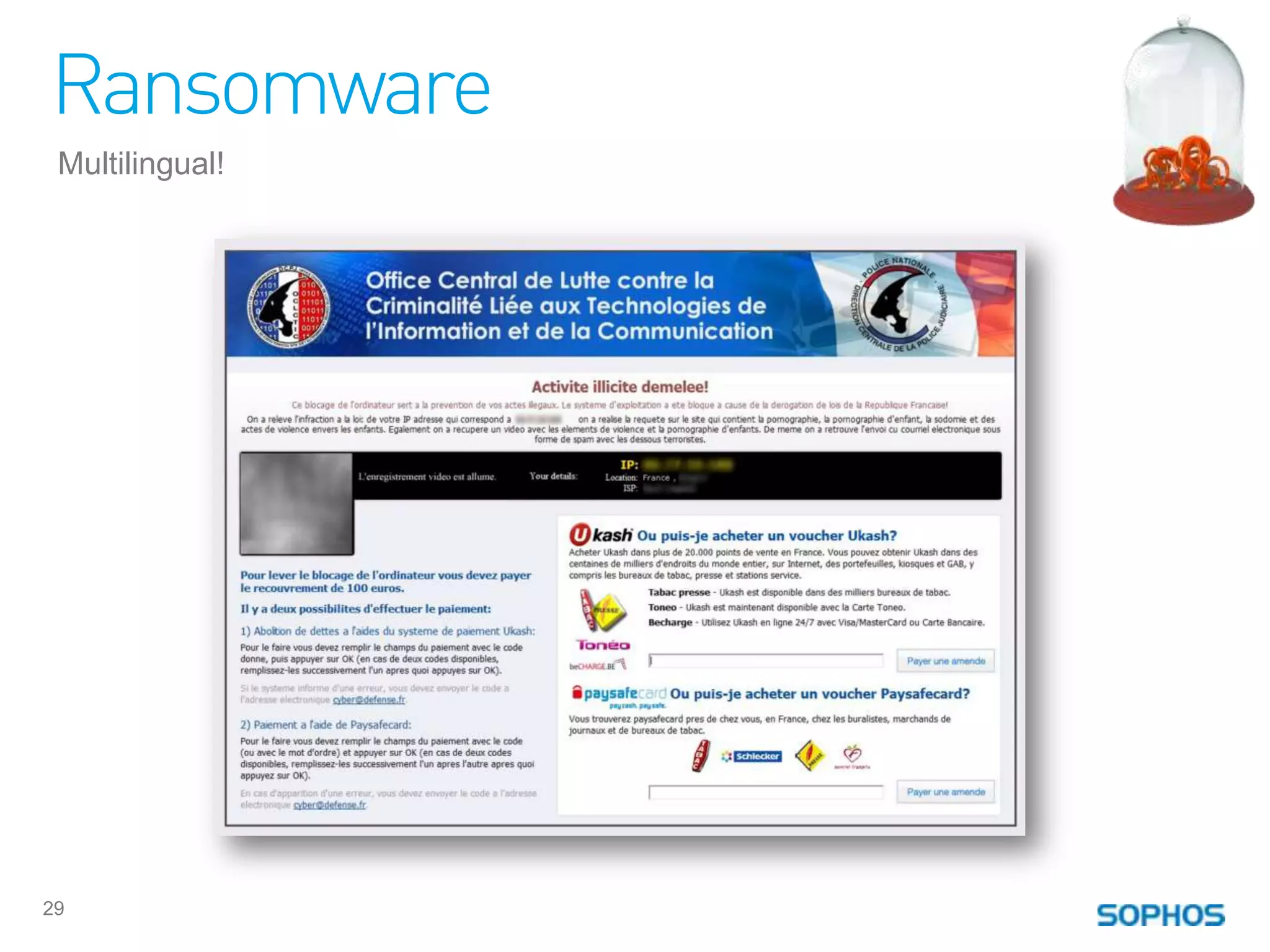
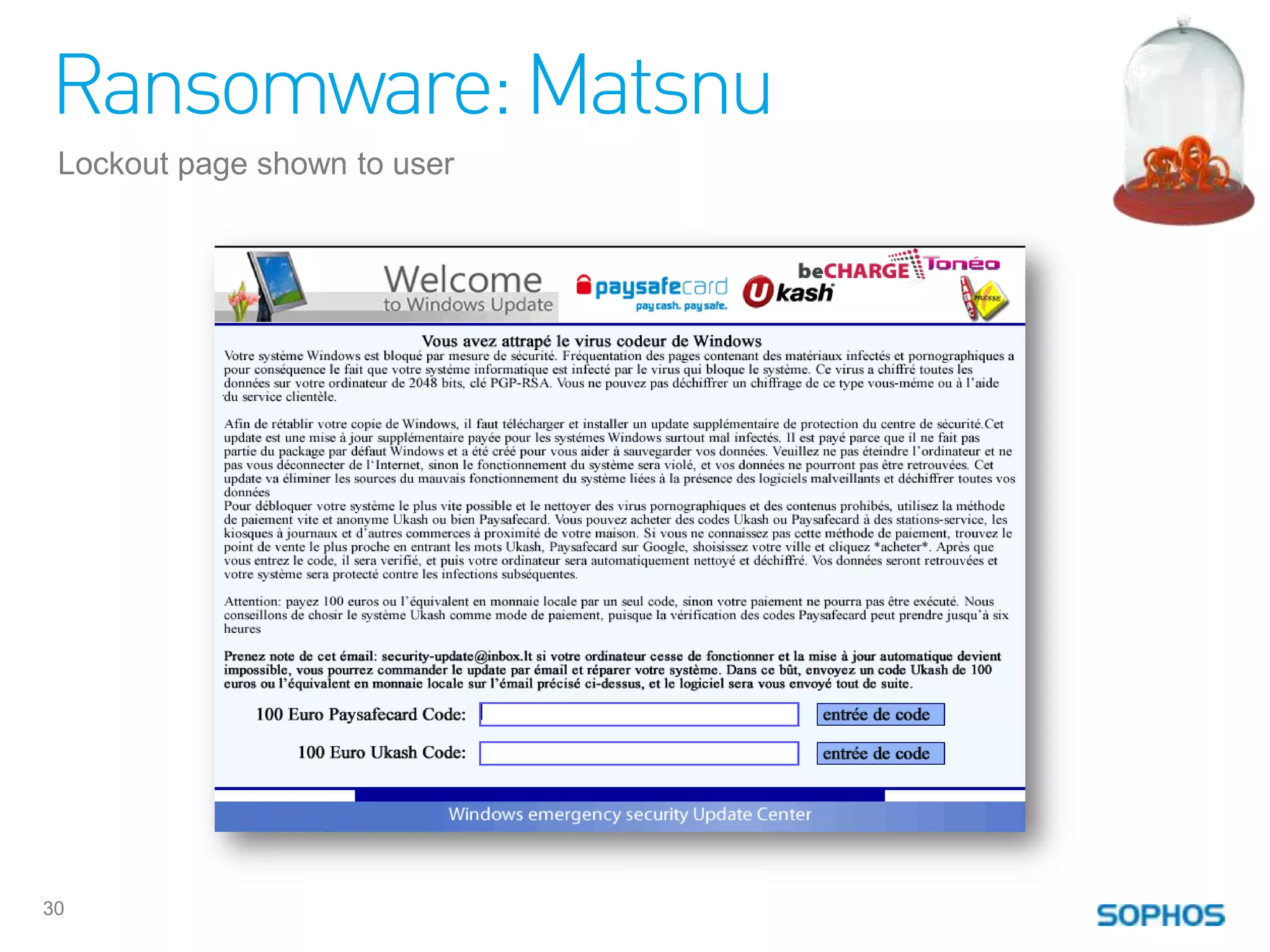
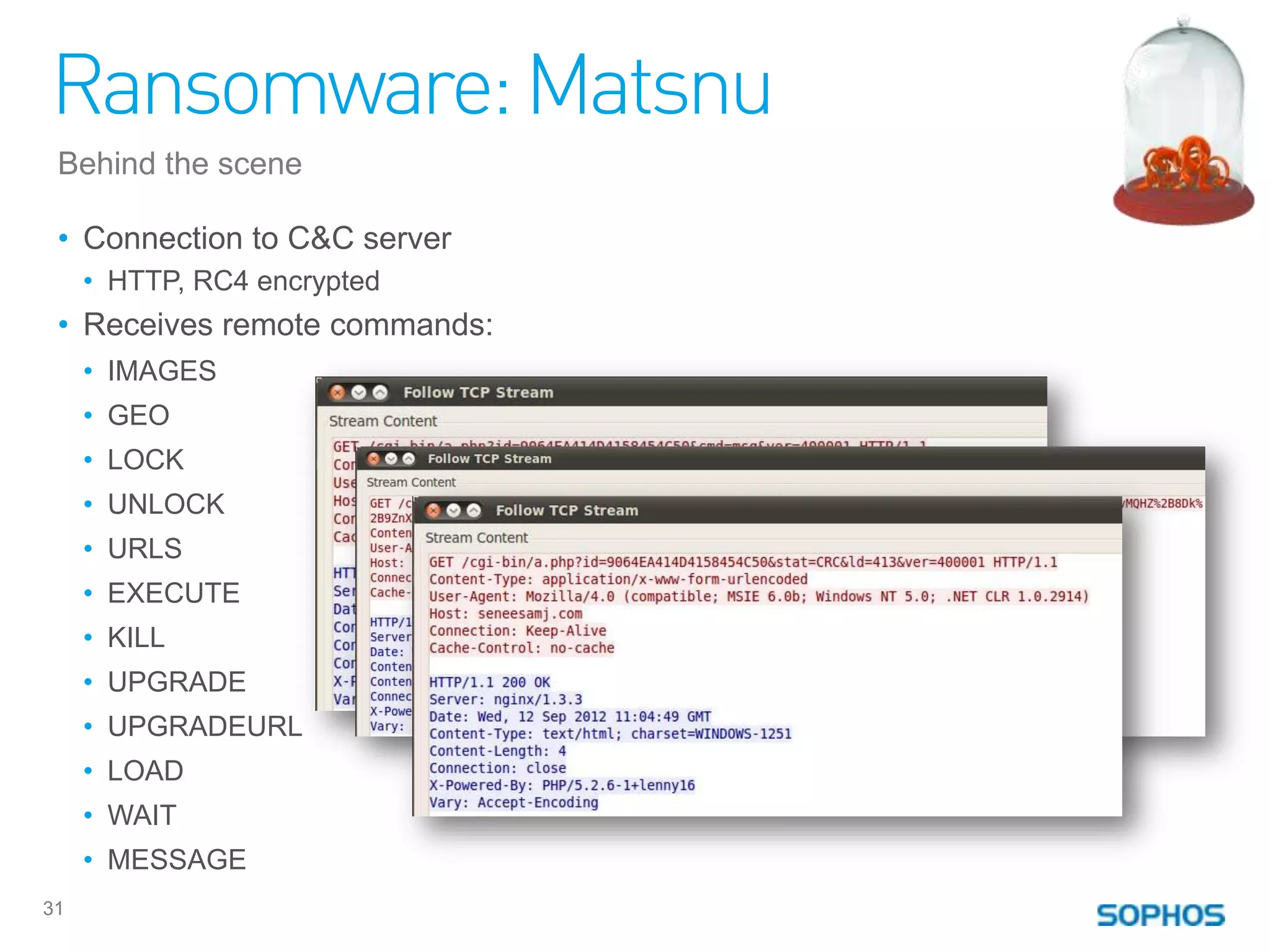
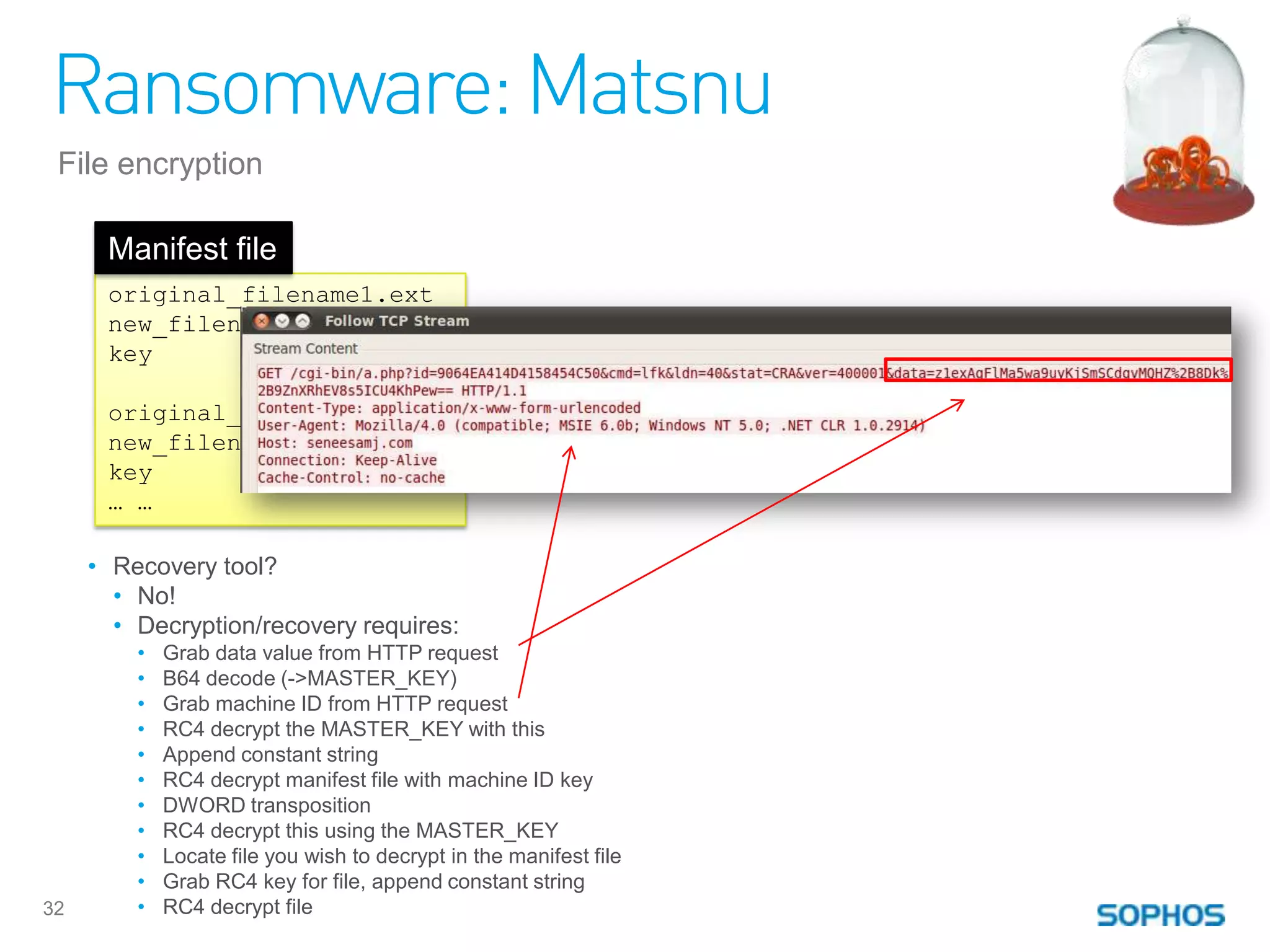
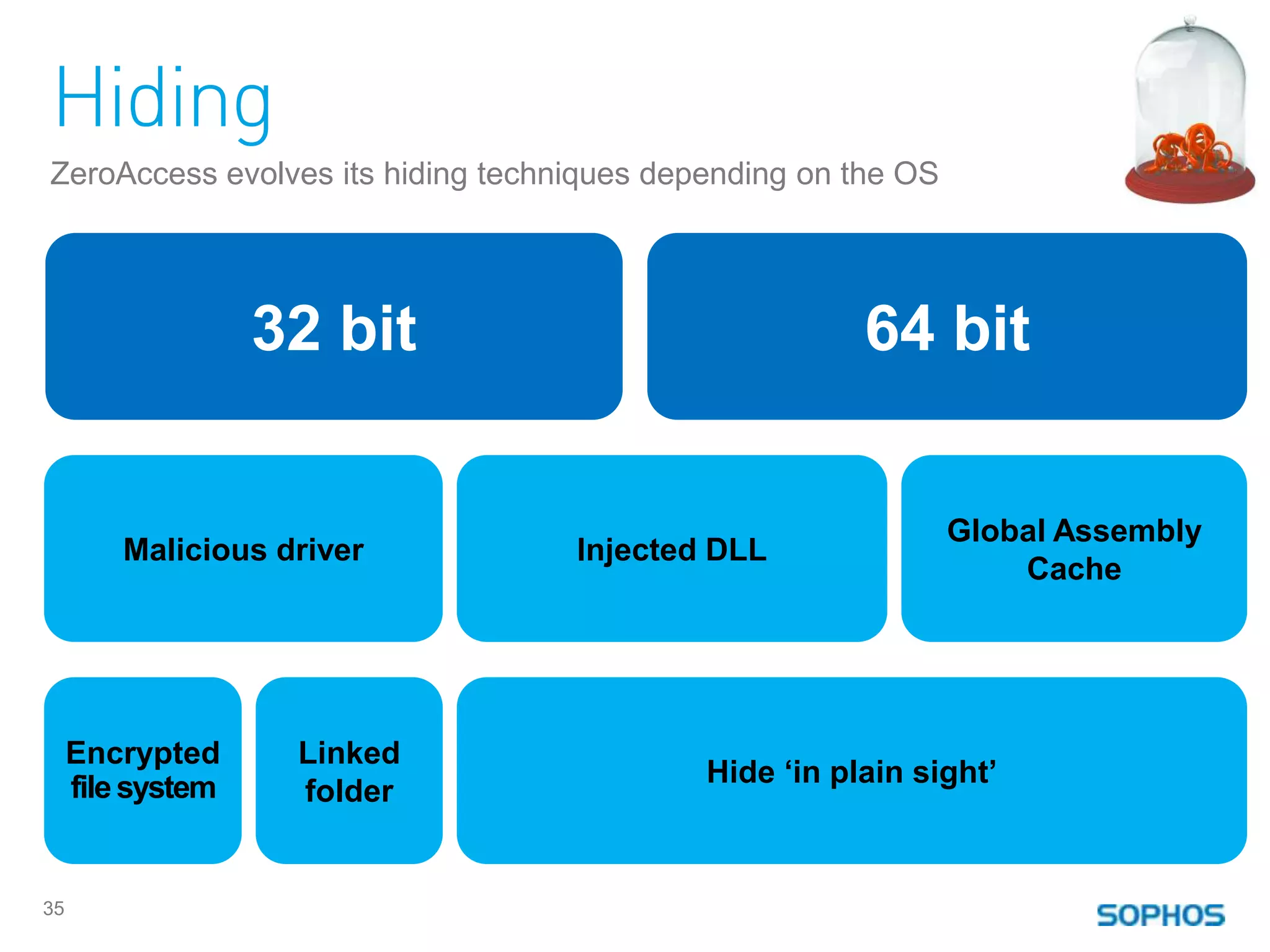
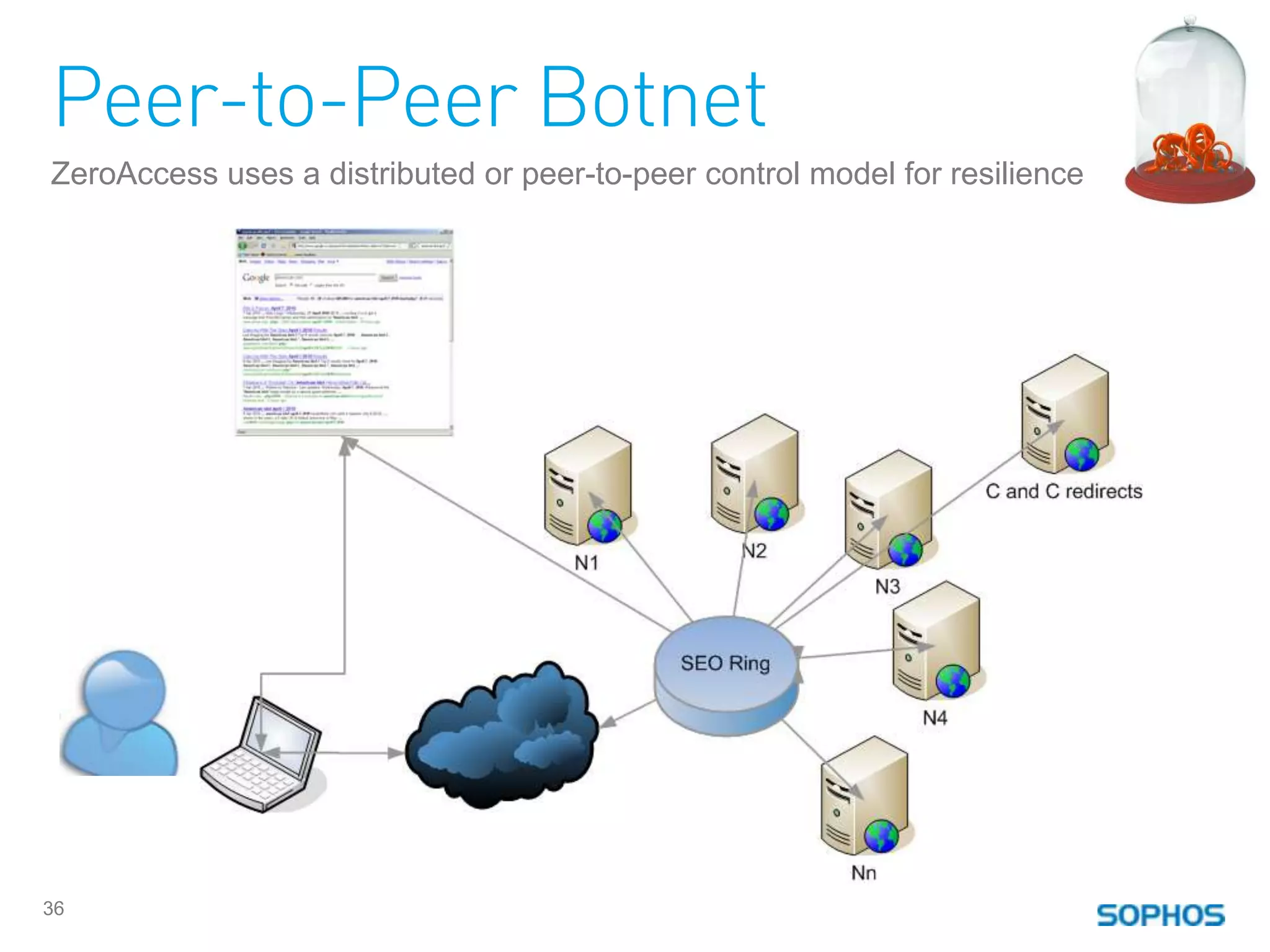
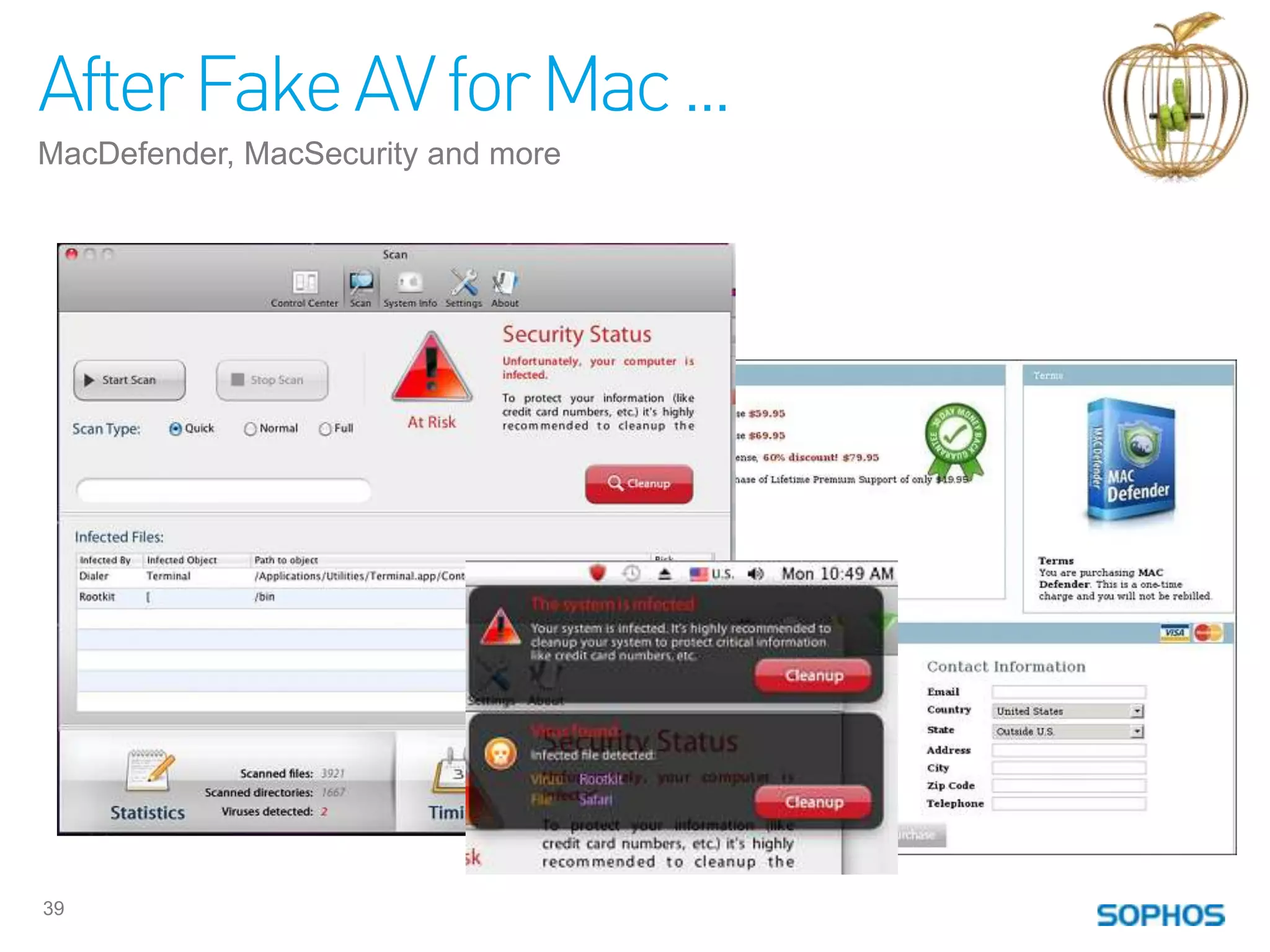
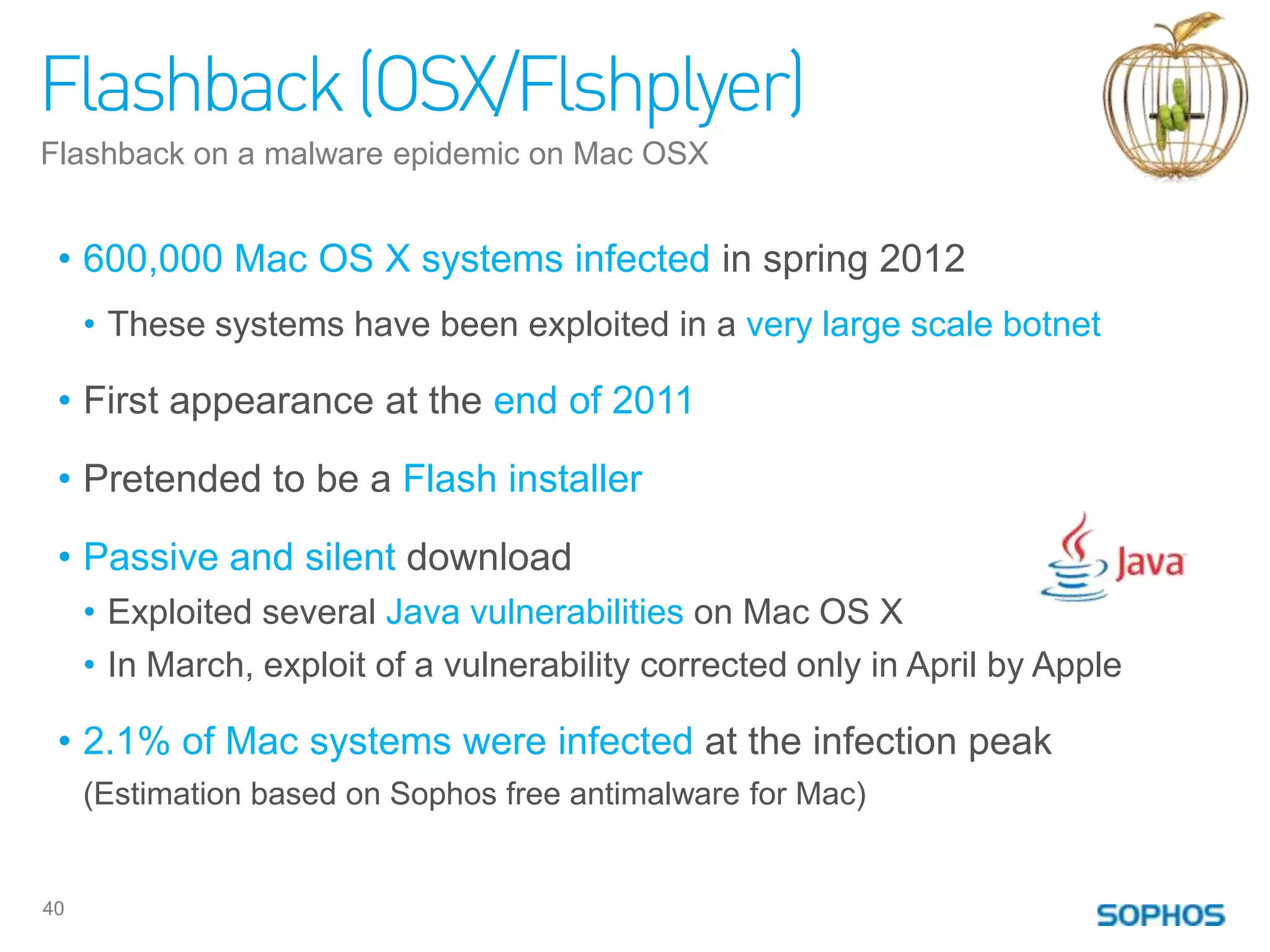
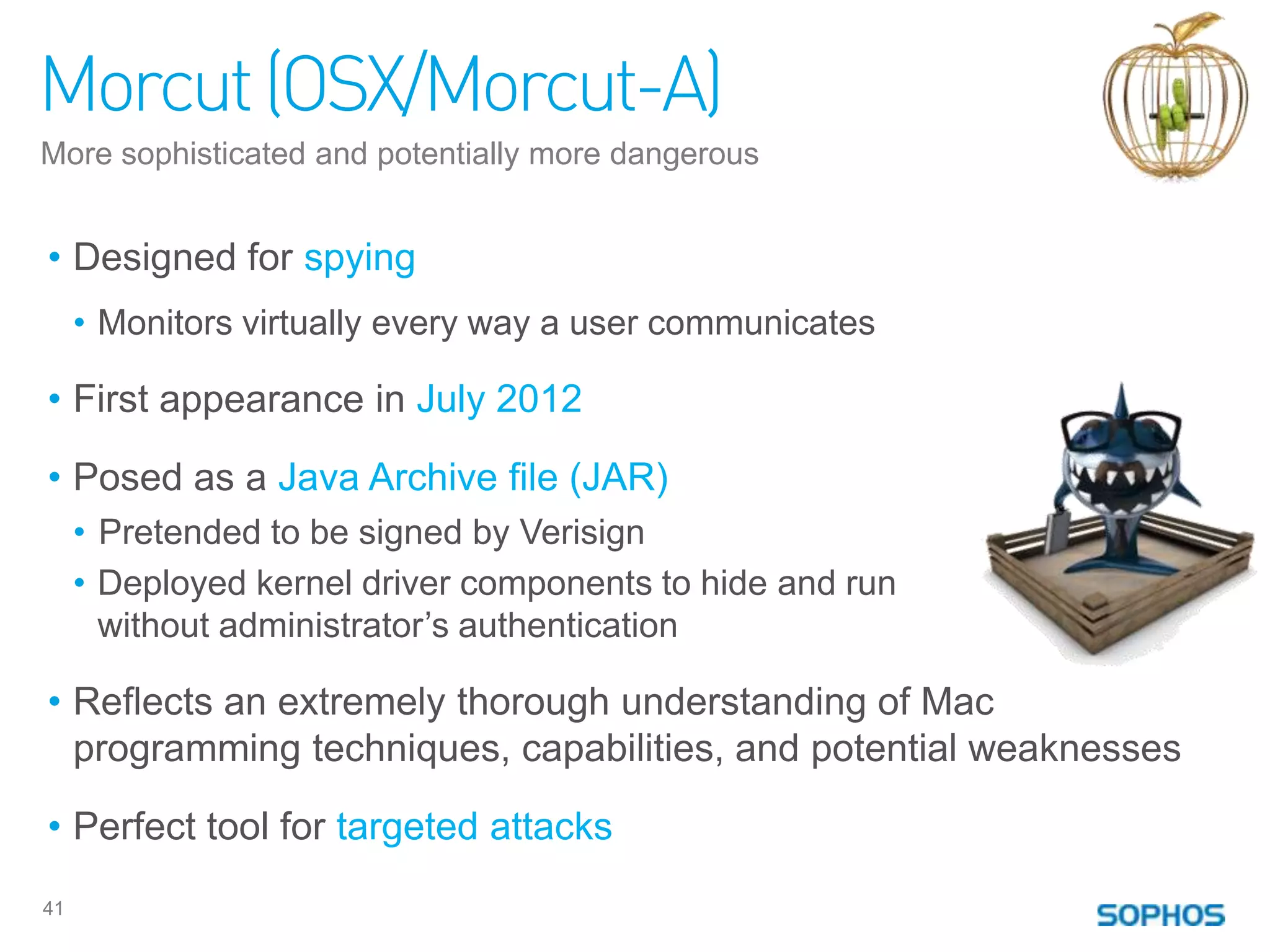
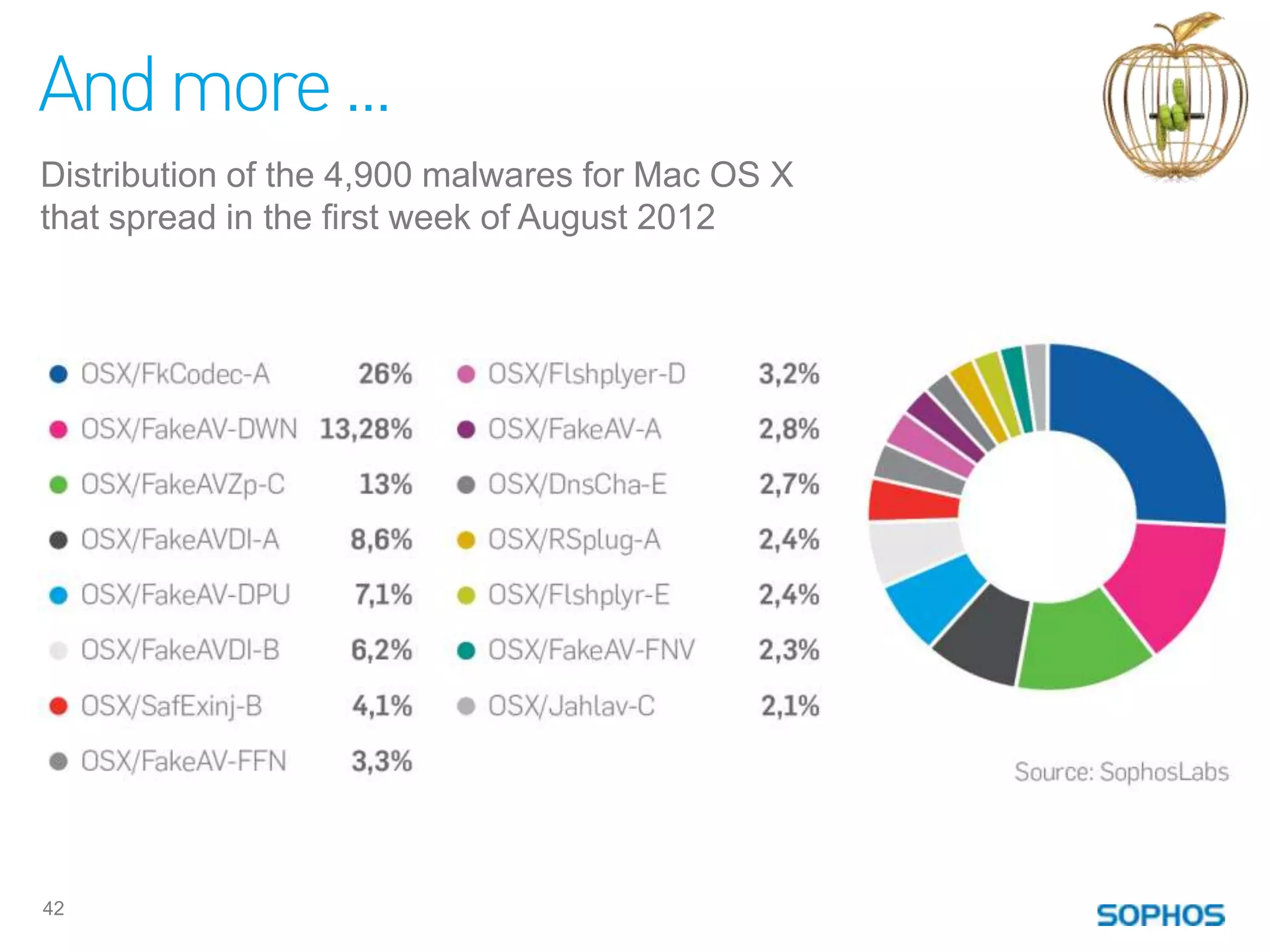
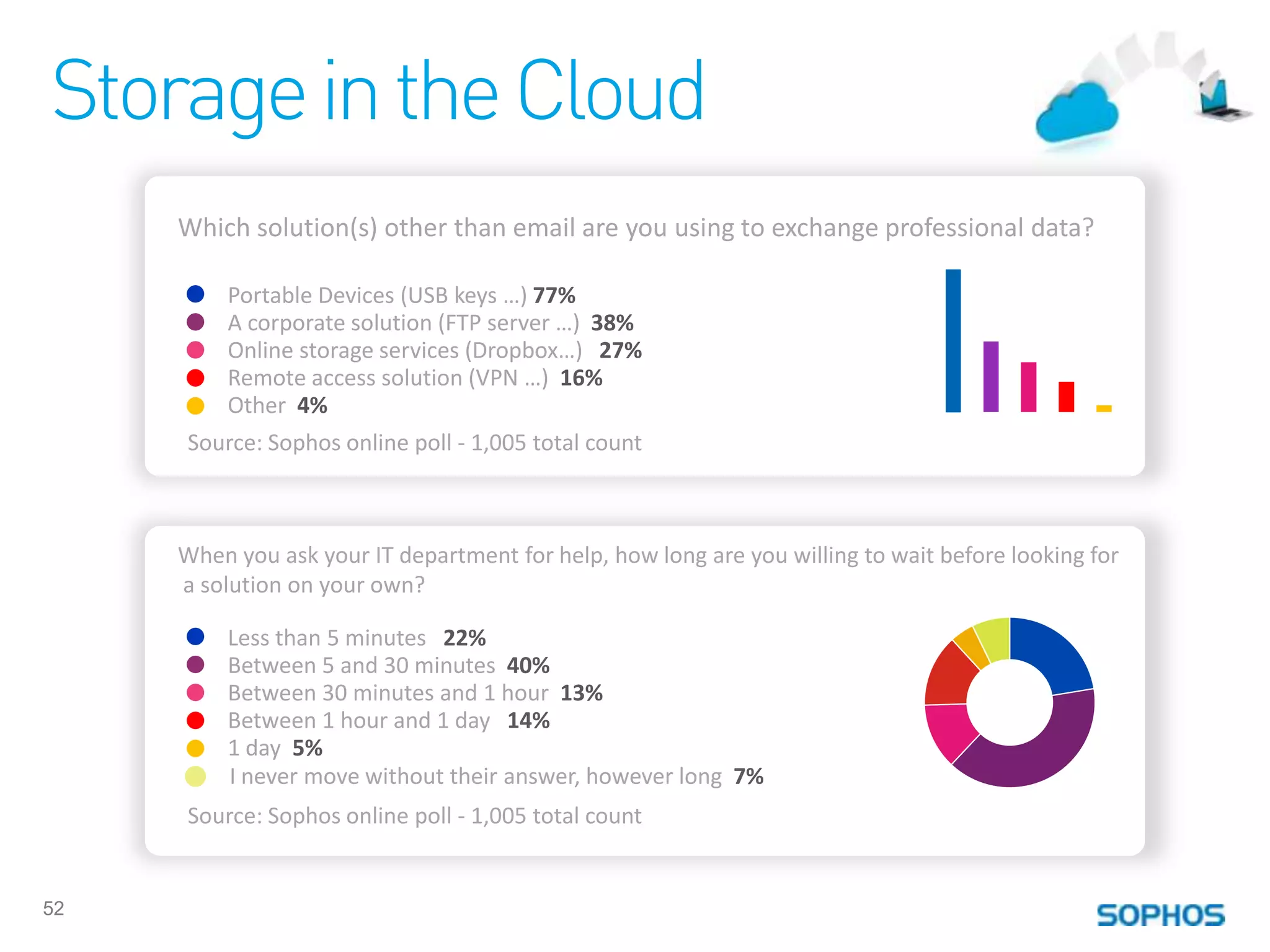
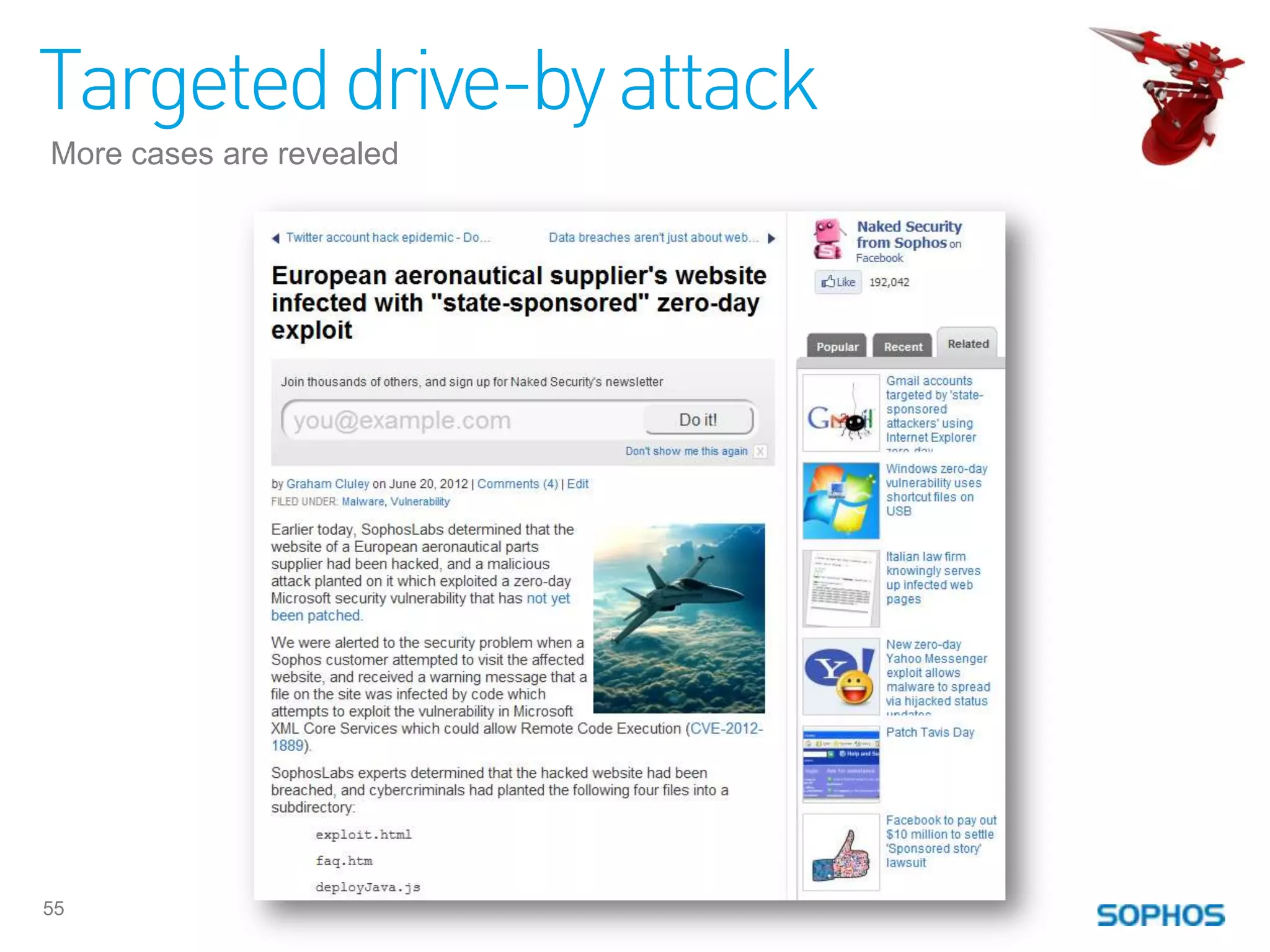
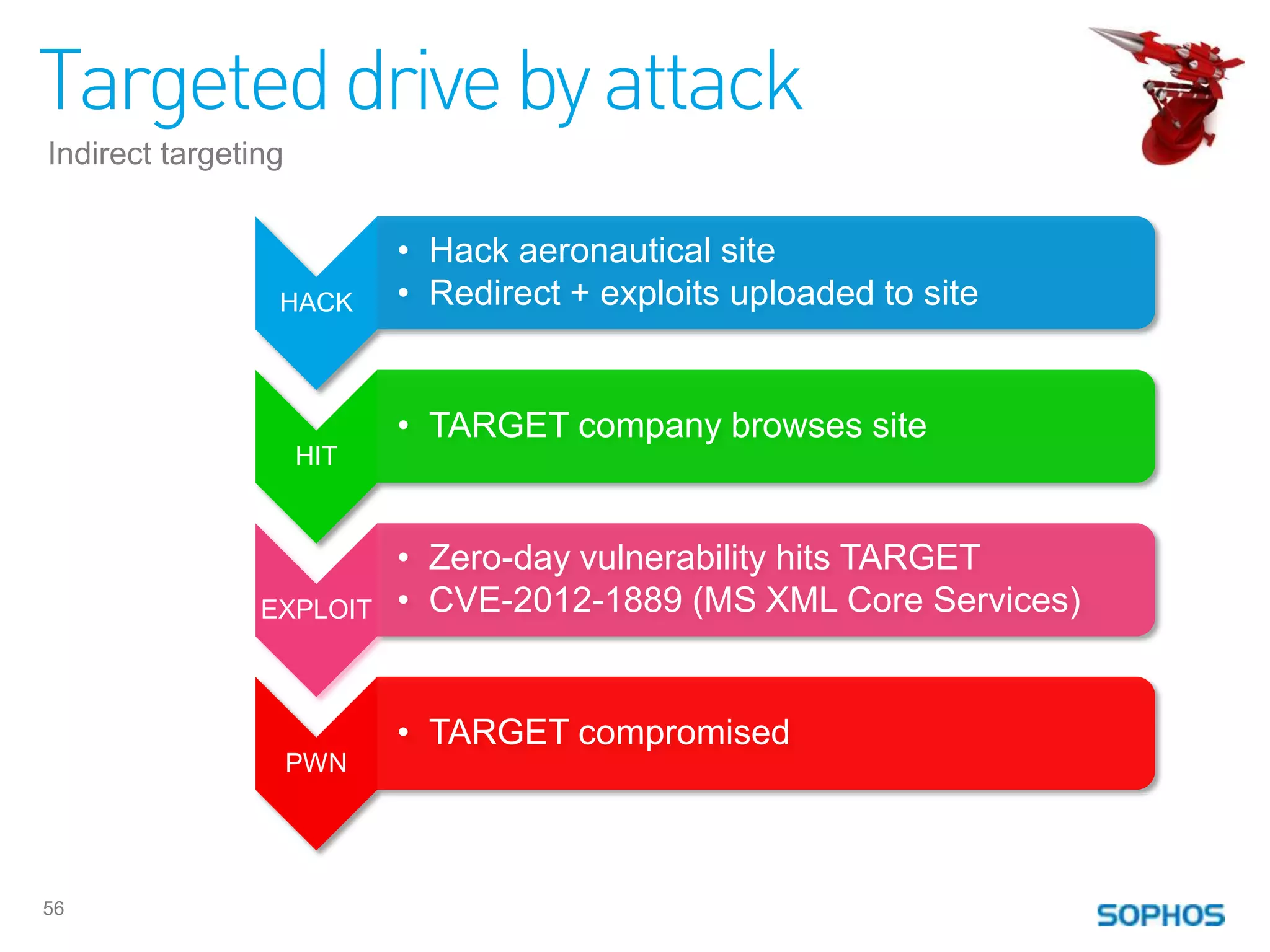
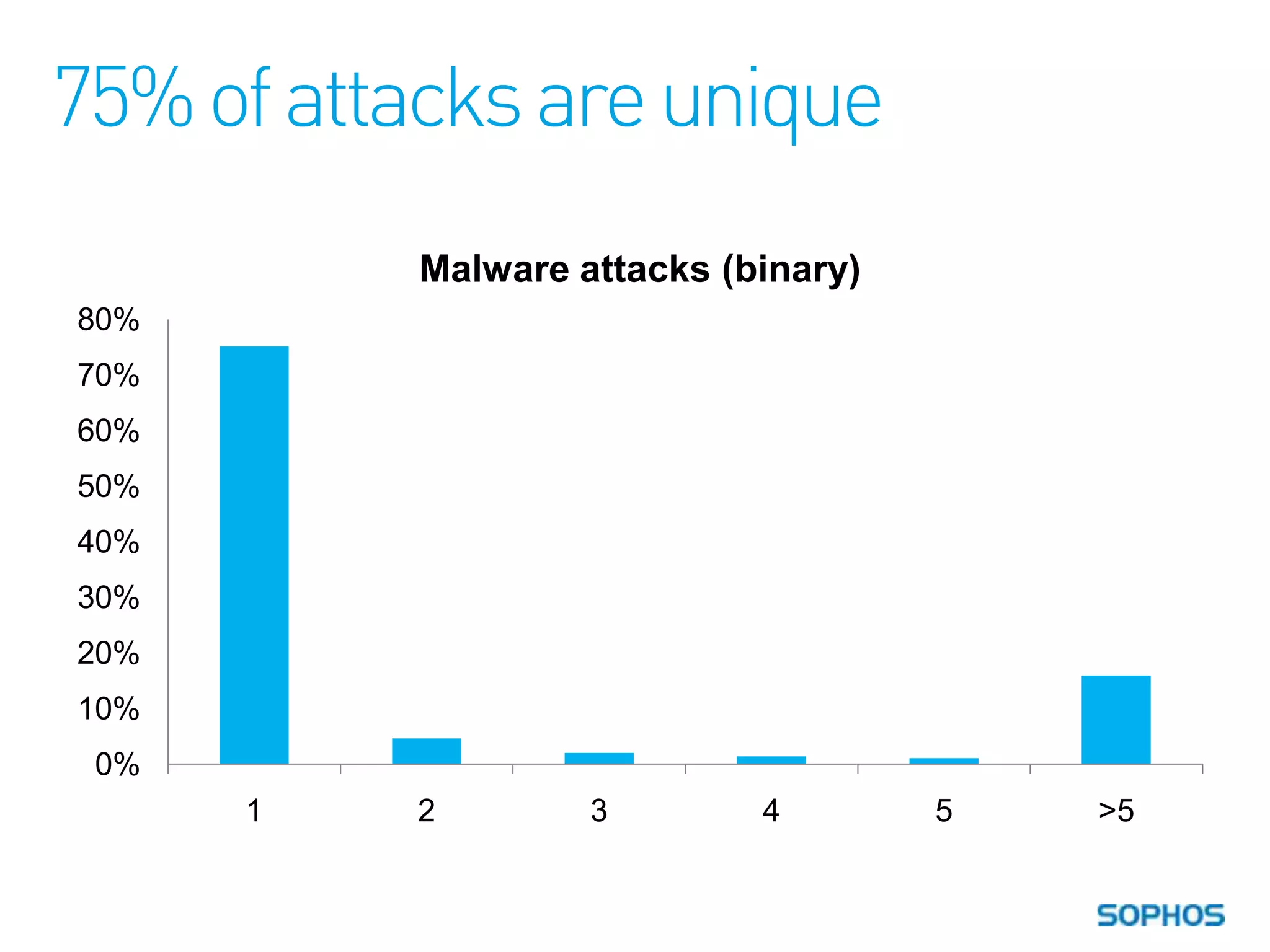
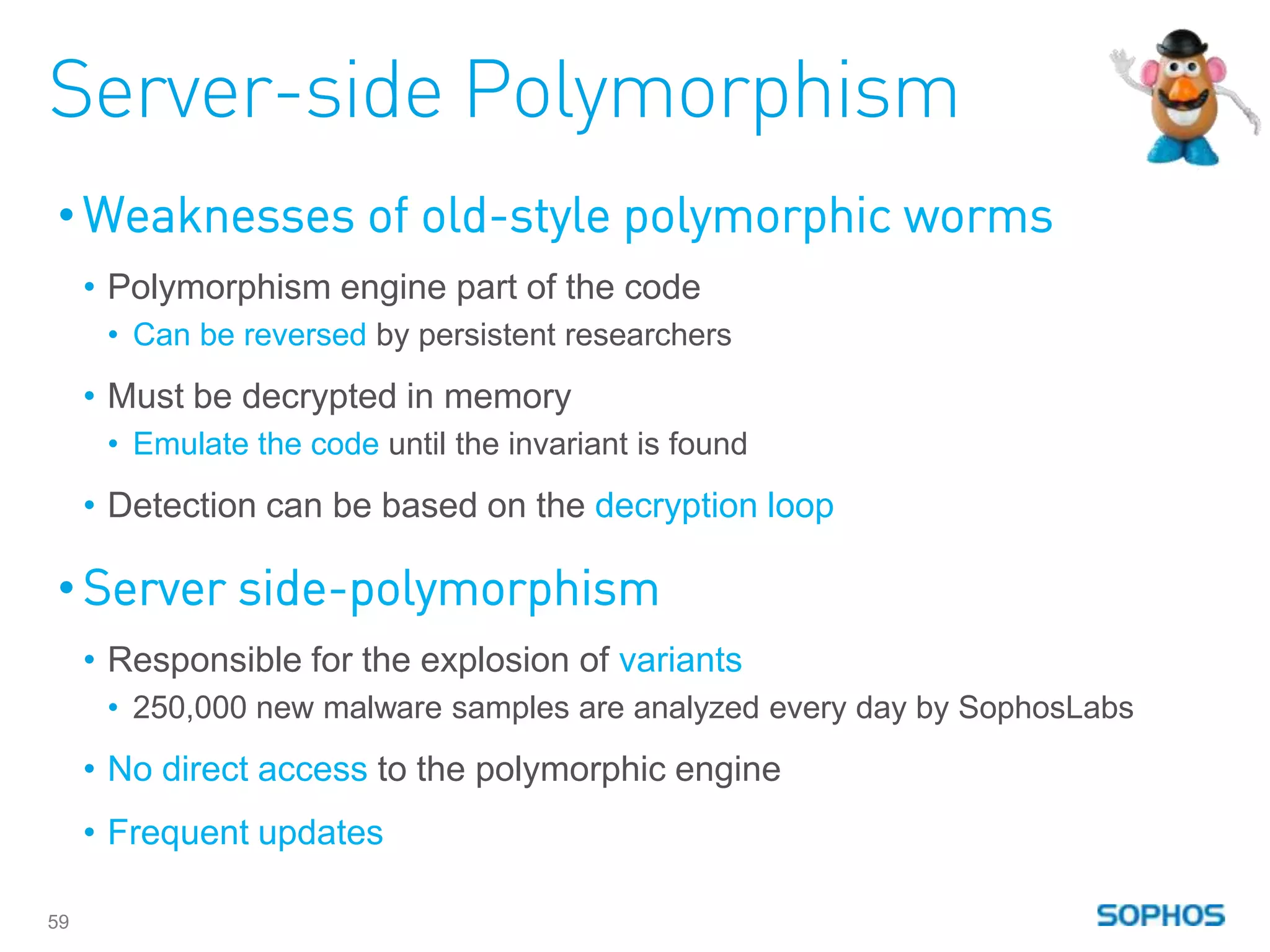
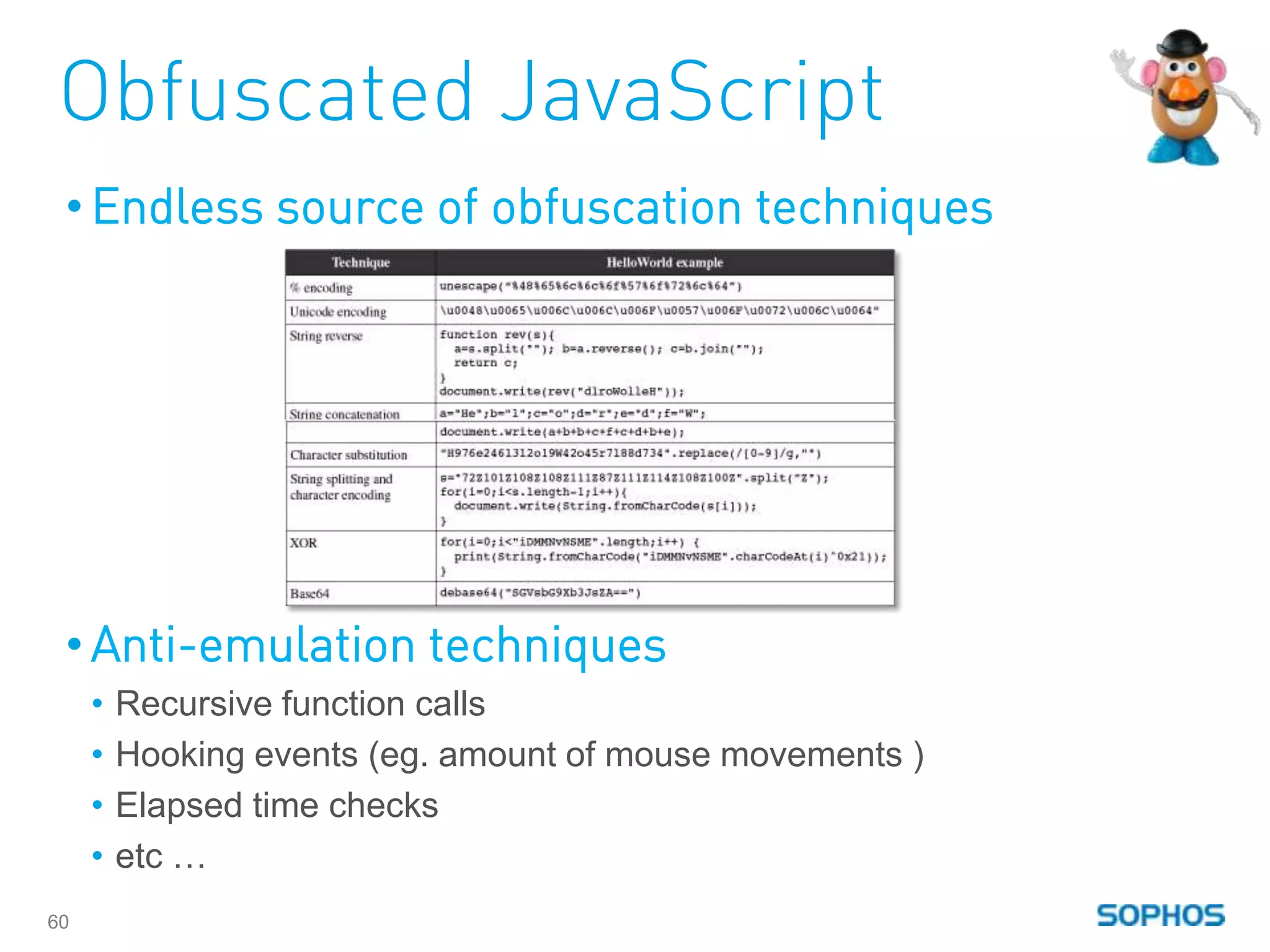
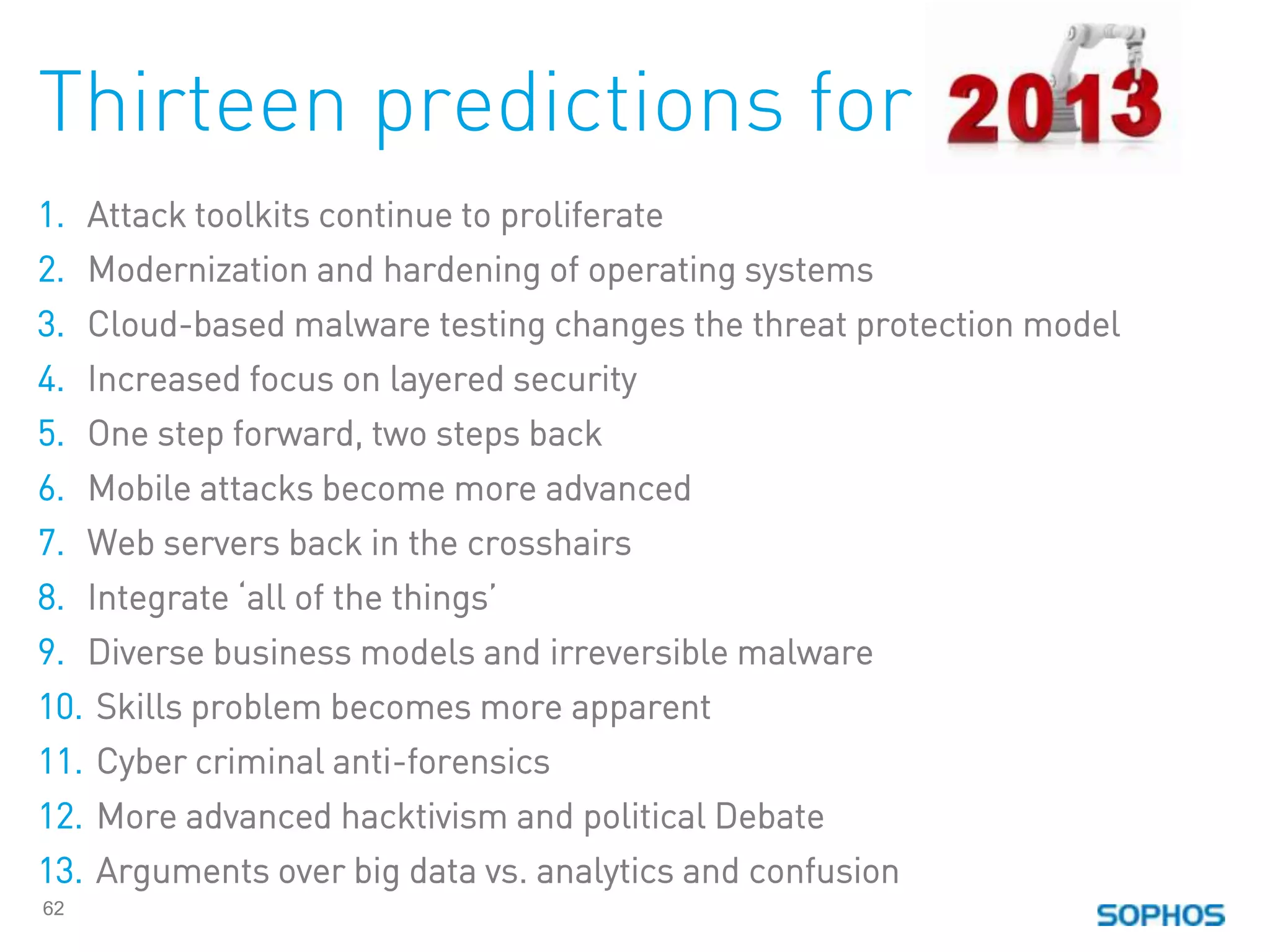
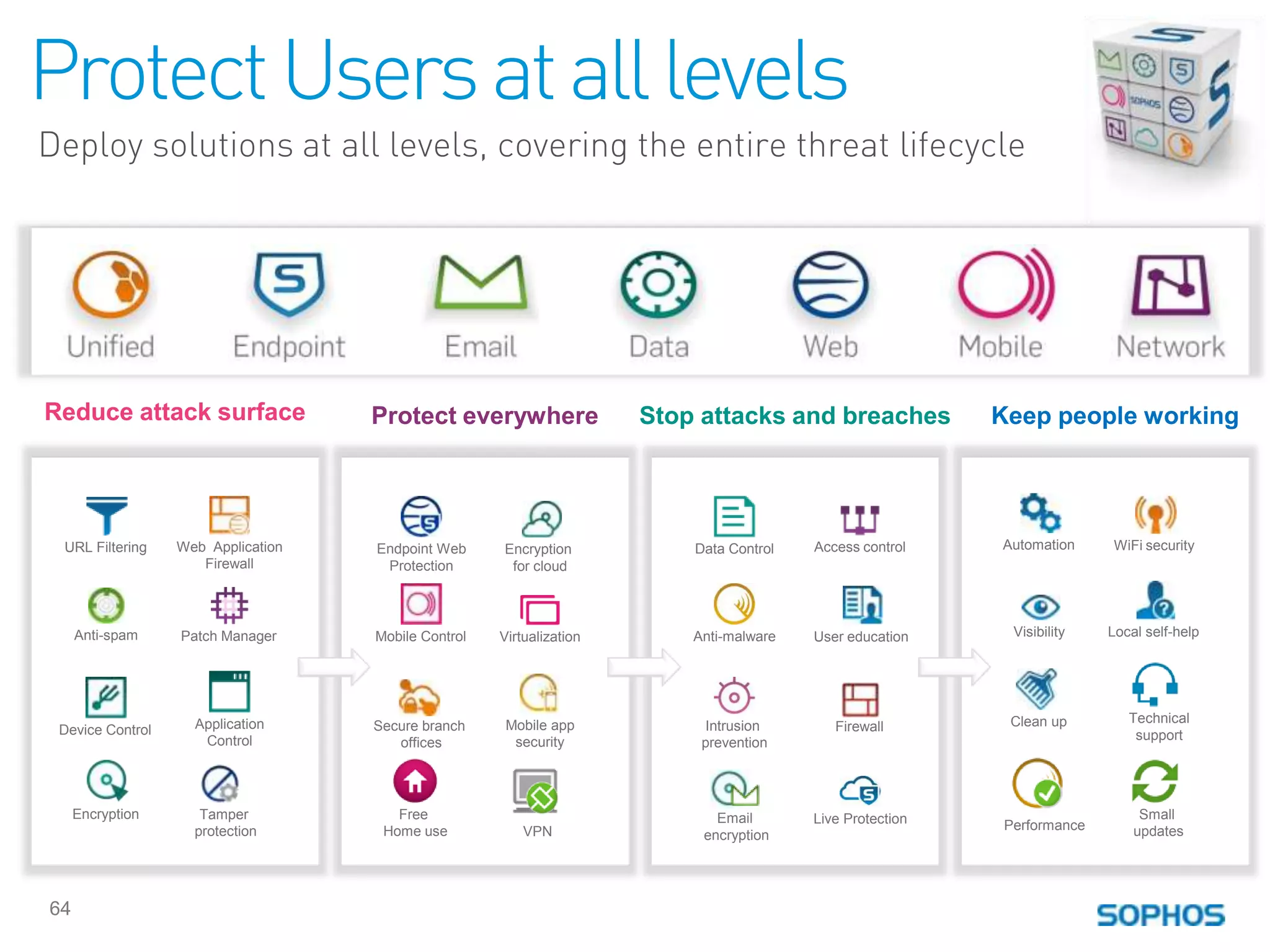
The Sophos Security Threat Report from January 2013 details the evolving landscape of cybersecurity threats, highlighting the growing sophistication of malware, particularly through techniques like drive-by downloads and social engineering. It notes the emergence of ransomware and the use of exploit kits, such as Blackhole, in targeted attacks, emphasizing the importance of layered security and proactive defenses. The report also addresses specific malware trends across various platforms, including Windows and Mac OS X, alongside predictions for future threats.